Abstract
Attribute-based conditional proxy re-encryption (AB-CPRE) allows delegators to carry out attribute-based control on the delegation of decryption by setting policies and attribute vectors. The fine-grained control of AB-CPRE makes it suitable for a variety of applications, such as cloud storage and distributed file systems. However, all existing AB-CPRE schemes are constructed under classical number-theoretic assumptions, which are vulnerable to quantum cryptoanalysis. Therefore, we propose the first AB-CPRE scheme based on the learning with errors (LWE) assumption. Constructed from fully key-homomorphic encryption (FKHE) and key-switching techniques, our scheme is unidirectional, single-hop, and enables a polynomial-depth boolean circuit as its policy. Furthermore, we split the ciphertext into two independent parts to avoid two-level or multi-level encryption/decryption mechanisms. Taking advantage of it, we then extend our single-hop AB-CPRE into an efficient and concise multi-hop one. No matter how many transformations are performed, the re-encrypted ciphertext is in constant size, and only one encryption/decryption algorithm is needed. Both of our schemes are proved to be selective secure against chosen-plaintext attacks (CPA) in the standard model.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
References
Agrawal, S., Boneh, D., Boyen, X.: Efficient lattice (h)ibe in the standard model. In: Gilbert, H. (ed.) EUROCRYPT 2010. LNCS, vol. 6110, pp. 553–572. Springer, Heidelberg (2010). https://doi.org/10.1007/978-3-642-13190-5_28
Alwen, J., Peikert, C.: Generating shorter bases for hard random lattices. In: 26th International Symposium on Theoretical Aspects of Computer Science STACS 2009, pp. 75–86. IBFI Schloss Dagstuhl (2009)
Aono, Y., Boyen, X., Phong, L.T., Wang, L.: Key-private proxy re-encryption under LWE. In: Paul, G., Vaudenay, S. (eds.) INDOCRYPT 2013. LNCS, vol. 8250, pp. 1–18. Springer, Cham (2013). https://doi.org/10.1007/978-3-319-03515-4_1
Applebaum, B., Cash, D., Peikert, C., Sahai, A.: Fast cryptographic primitives and circular-secure encryption based on hard learning problems. In: Halevi, S. (ed.) CRYPTO 2009. LNCS, vol. 5677, pp. 595–618. Springer, Heidelberg (2009). https://doi.org/10.1007/978-3-642-03356-8_35
Blaze, M., Bleumer, G., Strauss, M.: Divertible protocols and atomic proxy cryptography. In: Nyberg, K. (ed.) EUROCRYPT 1998. LNCS, vol. 1403, pp. 127–144. Springer, Heidelberg (1998). https://doi.org/10.1007/BFb0054122
Boneh, D., et al.: Fully key-homomorphic encryption, arithmetic circuit ABE and compact garbled circuits. In: Nguyen, P.Q., Oswald, E. (eds.) EUROCRYPT 2014. LNCS, vol. 8441, pp. 533–556. Springer, Heidelberg (2014). https://doi.org/10.1007/978-3-642-55220-5_30
Brakerski, Z.: Fully homomorphic encryption without modulus switching from classical GapSVP. In: Safavi-Naini, R., Canetti, R. (eds.) CRYPTO 2012. LNCS, vol. 7417, pp. 868–886. Springer, Heidelberg (2012). https://doi.org/10.1007/978-3-642-32009-5_50
Brakerski, Z., Langlois, A., Peikert, C., Regev, O., Stehlé, D.: Classical hardness of learning with errors. In: Proceedings of the Forty-Fifth Annual ACM Symposium on Theory of Computing, STOC ’13, pp. 575–584. Association for Computing Machinery, New York (2013)
Canetti, R., Hohenberger, S.: Chosen-ciphertext secure proxy re-encryption. In: Proceedings of the 14th ACM Conference on Computer and Communications Security, pp. 185–194 (2007)
Canetti, R., Krawczyk, H., Nielsen, J.B.: Relaxing chosen-ciphertext security. In: Boneh, D. (ed.) CRYPTO 2003. LNCS, vol. 2729, pp. 565–582. Springer, Heidelberg (2003). https://doi.org/10.1007/978-3-540-45146-4_33
Cash, D., Hofheinz, D., Kiltz, E., Peikert, C.: Bonsai trees, or how to delegate a lattice basis. In: Gilbert, H. (ed.) EUROCRYPT 2010. LNCS, vol. 6110, pp. 523–552. Springer, Heidelberg (2010). https://doi.org/10.1007/978-3-642-13190-5_27
Fang, L., Wang, J., Ge, C., Ren, Y.: Fuzzy conditional proxy re-encryption. Sci. China Inf. Sci. 56(5), 1–13 (2013). https://doi.org/10.1007/s11432-012-4623-6
Ge, C., Susilo, W., Wang, J., Fang, L.: Identity-based conditional proxy re-encryption with fine grain policy. Comput. Stand. Interfaces 52, 1–9 (2017)
Gentry, C., Peikert, C., Vaikuntanathan, V.: Trapdoors for hard lattices and new cryptographic constructions. In: Proceedings of the Fortieth Annual ACM Symposium on Theory of Computing, pp. 197–206 (2008)
Green, M., Ateniese, G.: Identity-based proxy re-encryption. In: Katz, J., Yung, M. (eds.) ACNS 2007. LNCS, vol. 4521, pp. 288–306. Springer, Heidelberg (2007). https://doi.org/10.1007/978-3-540-72738-5_19
Lai, J., Huang, Z., Au, M.H., Mao, X.: Constant-size CCA-secure multi-hop unidirectional proxy re-encryption from indistinguishability obfuscation. Theoret. Comput. Sci. 847, 1–16 (2020)
Li, B., Xu, J., Liu, Y.: Lattice-based fuzzy conditional proxy re-encryption. J. Internet Technol. 20(5), 1379–1385 (2019)
Liang, K., Chu, C.K., Tan, X., Wong, D.S., Tang, C., Zhou, J.: Chosen-ciphertext secure multi-hop identity-based conditional proxy re-encryption with constant-size ciphertexts. Theoret. Comput. Sci. 539, 87–105 (2014)
Liang, K., Susilo, W., Liu, J.K., Wong, D.S.: Efficient and fully CCA secure conditional proxy re-encryption from hierarchical identity-based encryption. Comput. J. 58(10), 2778–2792 (2015)
Liang, X., Weng, J., Yang, A., Yao, L., Jiang, Z., Wu, Z.: Attribute-based conditional proxy re-encryption in the standard model under LWE. Cryptology ePrint Archive, Report 2021/613 (2021). https://ia.cr/2021/613
Lindner, R., Peikert, C.: Better key sizes (and attacks) for LWE-based encryption. In: Kiayias, A. (ed.) CT-RSA 2011. LNCS, vol. 6558, pp. 319–339. Springer, Heidelberg (2011). https://doi.org/10.1007/978-3-642-19074-2_21
Luo, F., Al-Kuwari, S., Wang, F., Chen, K.: Attribute-based proxy re-encryption from standard lattices. Theoret. Comput. Sci. 865, 52–62 (2021)
Ma, C., Li, J., Ouyang, W.: Lattice-based identity-based homomorphic conditional proxy re-encryption for secure big data computing in cloud environment. Int. J. Found. Comput. Sci. 28(06), 645–660 (2017)
Mao, X., Li, X., Wu, X., Wang, C., Lai, J.: Anonymous attribute-based conditional proxy re-encryption. In: Au, M.H., et al. (eds.) NSS 2018. LNCS, vol. 11058, pp. 95–110. Springer, Cham (2018). https://doi.org/10.1007/978-3-030-02744-5_7
Micciancio, D., Peikert, C.: Trapdoors for lattices: simpler, tighter, faster, smaller. In: Pointcheval, D., Johansson, T. (eds.) EUROCRYPT 2012. LNCS, vol. 7237, pp. 700–718. Springer, Heidelberg (2012). https://doi.org/10.1007/978-3-642-29011-4_41
Mo, L., Yao, G.: Multi-use conditional proxy re-encryption. In: 2013 International Conference on Information Science and Cloud Computing Companion, pp. 246–251. IEEE (2013)
Peikert, C.: Public-key cryptosystems from the worst-case shortest vector problem: extended abstract. In: Proceedings of the Forty-First Annual ACM Symposium on Theory of Computing, STOC 2009, pp. 333–342. Association for Computing Machinery, New York (2009)
Regev, O.: On lattices, learning with errors, random linear codes, and cryptography. J. ACM 56(6), 1–40 (2009)
Shao, J., Cao, Z.: Multi-use unidirectional identity-based proxy re-encryption from hierarchical identity-based encryption. Inf. Sci. 206, 83–95 (2012)
Shao, J., Wei, G., Ling, Y., Xie, M.: Identity-based conditional proxy re-encryption. In: 2011 IEEE International Conference on Communications (ICC), pp. 1–5. IEEE (2011)
Wang, H., Cao, Z., Wang, L.: Multi-use and unidirectional identity-based proxy re-encryption schemes. Inf. Sci. 180(20), 4042–4059 (2010)
Weng, J., Deng, R.H., Ding, X., Chu, C.K., Lai, J.: Conditional proxy re-encryption secure against chosen-ciphertext attack. In: Proceedings of the 4th International Symposium on Information, Computer, and Communications Security, pp. 322–332 (2009)
Yang, Y., Lu, H., Weng, J., Zhang, Y., Sakurai, K.: Fine-grained conditional proxy re-encryption and application. In: Chow, S.S.M., Liu, J.K., Hui, L.C.K., Yiu, S.M. (eds.) ProvSec 2014. LNCS, vol. 8782, pp. 206–222. Springer, Cham (2014). https://doi.org/10.1007/978-3-319-12475-9_15
Zhao, J., Feng, D., Zhang, Z.: Attribute-based conditional proxy re-encryption with chosen-ciphertext security. In: 2010 IEEE Global Telecommunications Conference GLOBECOM 2010, pp. 1–6. IEEE (2010)
Acknowledgements
We all thank the anonymous reviewers for their valuable comments and suggestions which improve the content and presentation of this work a lot. Jian Weng was supported by Major Program of Guangdong Basic and Applied Research Project under Grant No. 2019B030302008, National Key Research and Development Plan of China under Grant Nos. 2020YFB1005600, National Natural Science Foundation of China under Grant Nos. 61825203, U1736203 and 61732021, and Guangdong Provincial Science and Technology Project under Grant No. 2017B010111005. Anjia Yang was partially supported by Key-Area Research and Development Program of Guangdong Province (Grant No. 2020B0101360001), National Natural Science Foundation of China (Grant No. 62072215, 61702222). Xiaojian Liang, Zhenghao Wu, and Zike Jiang were supported by Special Funds for the Cultivation of Guangdong College Students’ Scientific and Technological Innovation. (“Climbing Program” Special Funds.) (No. pdjh2021a0050).
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Appendices
A Proof for Single-hop AB-CPRE
All details of proof can be found in full version [20]. Due to space limitations, we only present the simulator algorithms used in our proof.
-
\(\mathbf { Setup }_{SIM}(n , \mathbf{x}^* )\): Let \(\mathbf{x}^* = \lbrace x_i^* \rbrace _{i \in [\ell ]}\) to be the attribute vector selected by adversary \(\mathcal {A}\). Sample a uniform matrix \(\mathbf{D}_{\theta } \leftarrow \mathbb {Z}_q^{n \times m} \) and generate a random identity’s public key \(\mathbf{A}_{\theta } \leftarrow \mathbb {Z}_q^{n \times m}\) , then choose \(\ell \) random matrices \(\mathbf{S}_1^* , ... , \mathbf{S}_\ell ^* \leftarrow \lbrace -1 , 1 \rbrace ^{m \times m}\). Set \(\mathbf{B}_i = \mathbf{A}_{\theta } \mathbf{S}_i^* - x_i^* \mathbf{G}\) for all \(i \in [\ell ]\). Select an error sampling algorithm \(\chi \), which is a \(B-\)bounded distribution. Keep matrices \(\lbrace \mathbf{S}_i^* \rbrace _{ i \in [\ell ] }\) as secret and output public parameters \(pp := ( \lbrace \mathbf{B}_i \rbrace _{i \in [\ell ]}, \chi )\) and specific public key \(pk_{\theta } := ( \mathbf{A}_{\theta } , \mathbf{D}_{\theta } )\).
-
\(\mathbf { Enc }_{SIM}(pp , pk_\theta ,\boldsymbol{\mu }_b , \mathbf{x}^* )\): Let \(pp = ( \lbrace \mathbf{B}_i \rbrace _{i \in [\ell ]}, \chi )\), \(pk_\theta = \mathbf ( \mathbf{A}_{\theta } , \mathbf{D}_{\theta } )\), a challenge message \(\boldsymbol{\mu }_b \in \lbrace 0 , 1 \rbrace ^{m}\), and a selected attribute vector \(\mathbf{x}^* = ( \lbrace x_i^* \rbrace _{ i \in [\ell ] } )\). Choose a random vector \(\mathbf{s} \leftarrow \mathbb {Z}_q^n\) and two error vectors \(\mathbf{e}_{in} , \mathbf{e}_{out} \leftarrow \chi ^{m}\). Compute \(ct = ( \mathbf{c}_{in} , \mathbf{c}_{out} )\) as
$$\mathbf{c}_{in} = ( \mathbf { A_{\theta } } )^T \mathbf{s} + \mathbf{e}_{in} , \mathbf{c}_{out} = ( \mathbf { D_{\theta } } )^T \mathbf{s} + \mathbf{e}_{out} + \lfloor q/2 \rfloor \boldsymbol{\mu }_b.$$Use \(\lbrace \mathbf{S}_i^* \rbrace _{ i \in [\ell ] }\) chosen in \(Setup_{SIM}\) instead of uniform matrices in \(\lbrace -1 , 1 \rbrace ^{m \times m}\) and then assemble \(cc^* = ( \lbrace \mathbf{c}_i = (x_i^* \mathbf{G} + \mathbf{B}_i )^T \mathbf{s} + (\mathbf{S}_i^*)^T \mathbf{e}_{in} \rbrace _{ i \in [ \ell ] } ) \in \mathbb {Z}_q^{ \ell m }\). Output a challenge ciphertext \(CT^* = (ct^* , cc^* )\).
-
\(\mathbf { ReKeyGen }_{SIM}( pp , pk_{\beta } , f )\): Parse \(pp = (\lbrace \mathbf{B}_i \rbrace _{i \in [\ell ]}, \chi )\) , \(pk_{\beta } = ( \mathbf{A}_{\beta } , \mathbf{D}_{\beta } )\), and a policy \(f \in \mathcal {F}_{\ell , d}\). Let \(\mathbf{S}_f^* = \mathbf {Eval}_{ \mathrm {sim} }( f , (x_i^* , \mathbf{S}_i^*)_{i \in [\ell ] } , \mathbf{A}_{\theta })\).
-
1)
In the case that \(f( \mathbf{x}^* ) \ne 0\), let \(\mathbf{B}_f = \mathbf{A}_{\theta } \mathbf{S}_f^* - f( \mathbf{x}^* ) \mathbf{G}\) and set \(\mathbf{F} = [ \mathbf{A}_{\theta } | \mathbf{B}_f - f( \mathbf{x}^* ) \mathbf{G} ] \in \mathbb {Z}^{n \times 2m}\). Compute the basis \(\mathbf{T}_{ \theta , f}\) for \(\mathbf{F}\) as \(\mathbf{T}_{ \theta , f} \leftarrow \mathbf {ExtendLeft}( \mathbf{A}_{\theta } , \mathbf{G} , \mathbf{T}_{\mathbf{G}}, \mathbf{S}_f )\). Then generate a matrix \(\mathbf{R}_{ \theta , f } \in \mathbb {Z}^{2m \times m}\) such that \(\mathbf{F} \mathbf{R}_{ \theta , f } = - \mathbf{D}_{\theta }\) by executing \(\mathbf {SamplePre}( \mathbf{F} , \mathbf{T}_{ \theta , f} , - \mathbf{D}_{\theta } , \sigma )\), set \(\overline{\mathbf{R}}_{\alpha ,f } = \mathbf {Power2}_q( \mathbf{R}_{ \alpha , f } )\), sample \(\mathbf{E}_1 \leftarrow \chi ^{2km \times n} , \mathbf{E}_2 , \mathbf{E}_3 \leftarrow \chi ^{2 km \times m}\) and compute
$$\mathbf{Q} = \begin{bmatrix} \mathbf{E}_1 \mathbf{A}_{\beta } + \mathbf{E}_2 &{} \mathbf{E}_1 \mathbf{D}_{\beta } + \mathbf{E}_3 + \overline{ \mathbf{R} }_{ \theta , f } \\ \mathbf{0}_{m \times m} &{} \mathbf{I}_{m \times m} \end{bmatrix} \in \mathbb {Z}_q^{ (2km + m ) \times 2m}.$$ -
2)
In the case that \(f( \mathbf{x}^* ) = 0\), sample two matrices \(\mathbf{E}_1 \leftarrow \chi ^{2km \times n} , \mathbf{E}_2 \leftarrow \chi ^{2 km \times m}\), choose a matrices \(\mathbf{M}' \leftarrow \mathbb {Z}^{ 2km \times m }\) uniformly at random, and compute
$$\mathbf{Q} = \begin{bmatrix} \mathbf{E}_1 \mathbf{A}_{\beta } + \mathbf{E}_2 &{} \mathbf{M}' \\ \mathbf{0}_{m \times m} &{} \mathbf{I}_{m \times m} \end{bmatrix} \in \mathbb {Z}_q^{ (2km + m ) \times 2m}.$$
Output \(rk_{ \theta , f \rightarrow \beta } = \mathbf{Q}\) as re-encryption key.
-
1)
B Correctness for Multi-hop AB-CPRE
The correctness of original ciphertext is the same as the correctness in Sect. 4. Then the correctness of transformed ciphertext is presented as follows.
Transformed Ciphertext. \((ct^{(t-1)} = (\mathbf{c}_{in}^{(t-1)} , \mathbf{c}_{out}^{(t-1)} ) , cc^{(t-1)} = \lbrace \mathbf{c}_i^{(t-1)} \rbrace _{i \in [\ell ] } )\) is the ciphertext which has been transformed \(t-1\) times and associated with attribute vector \(\mathbf{x}\) under \(pk_\alpha \). For convenience, \(rk_{\alpha , f \rightarrow \beta , \mathbf{y}} = (\mathbf{Q} , \mathbf{P})\) is the re-encryption key, where \(f( \mathbf{x} ) = 0\). Set \( \widetilde{ \mathbf{c} }_{in,f}^{(t-1)} = \mathbf {Bits}_q( [\mathbf{c}_{in}^{(t-1)} ; \mathbf{c}_f^{(t-1)} ] )\) and \(\overline{ \mathbf{R} }_{\alpha ,f } =\mathbf {Power2}_q( \mathbf{R}_{\alpha , f } )\). Then the t times transformed ciphertext \(( ct^{(t)} , cc^{(t)} )\) is showed as following;
For any \(t > 0\), we can learn that, \(\Vert \mathbf {e}_{in}^{(t)} \Vert \le 2 k m \sqrt{m} B\) and \(\Vert \mathbf {e}_i^{(t)} \Vert \le 2 k m \sqrt{m} B\). Because \(\Vert \mathbf{e}_{out}^{(0)} \Vert \le \sqrt{m}B\) and \(\Vert \mathbf{e}_f^{(t)} \Vert \le \sqrt{2} m k B (m+1)^d\), we have,
Therefore, for the t times transformed ciphertext \(( ct^{(t)} , cc^{(t)} )\),
where \(\Vert ( \mathbf {e}_{in}^{(t)} )^T \mathbf{R}_{\alpha } + ( \mathbf {e}_{out}^{(t)} )^T \Vert \le \Vert ( \mathbf {e}_{in}^{(t)} )^T \Vert \cdot \Vert \mathbf{R}_{\alpha } \Vert + \Vert ( \mathbf {e}_{out}^{(t)} )^T \Vert \le 2 k m^2 \sqrt{m} \sigma B + \sqrt{m} B + 2 k m \sqrt{m} B t + 2 \sqrt{2} k m^2(m + 1)^d \sigma B t \le B \cdot (m+1)^{O(d)} \le q/4\) with overwhelming probability, which ensures the correctness.
C Simulator Algorithms for Multi-hop AB-CPRE
We only present \(\mathbf { ReKeyGen }_{SIM}\) for multi-hop scheme and the other simulator algorithms can be found in the full version [20].
-
\(\mathbf { ReKeyGen }_{SIM}( pp , pk_{\beta } , f ,\mathbf{y} )\): Parse \(pp = (\lbrace \mathbf{B}_i \rbrace _{i \in [\ell ]}, \chi )\), \(pk_{\beta } = ( \mathbf{A}_{\beta } , \mathbf{D}_{\beta } )\), a policy \(f \in \mathcal {F}_{\ell , d}\) and an attribute vector \(\mathbf{y} = \lbrace y_i \rbrace _{i \in [\ell ]}\). Compute \(\mathbf{S}_f^*\) by executing \(\mathbf {Eval}_{ \mathrm {sim} }( f , (x_i^* , \mathbf{S}_i^*)_{i \in [\ell ] } , \mathbf{A}_{\theta })\), sample matrices \(\mathbf{E}_1 \leftarrow \chi ^{2km \times n}\), \(\mathbf{E}_2 , \mathbf{E}_3 \leftarrow \chi ^{2 km \times m}\).
-
1)
In the case that \(f( \mathbf{x}^* ) \ne 0\), let \(\mathbf{B}_f = \mathbf{A}_{\theta } \mathbf{S}_f^* - f( \mathbf{x}^* ) \mathbf{G}\) and set \(\mathbf{F} = [ \mathbf{A}_{\theta } | \mathbf{B}_f - f( \mathbf{x}^* ) \mathbf{G} ] \in \mathbb {Z}^{n \times 2m}\). Compute the basis \(\mathbf{T}_{ \theta , f}\) for \(\mathbf{F}\) as \(\mathbf{T}_{ \theta , f} \leftarrow \mathbf {ExtendLeft}( \mathbf{A}_{\theta } , \mathbf{G} , \mathbf{T}_{\mathbf{G}}, \mathbf{S}_f )\). Then generate a matrix \(\mathbf{R}_{ \theta , f } \in \mathbb {Z}^{2m \times m}\) such that \(\mathbf{F} \mathbf{R}_{ \theta , f } = - \mathbf{D}_{\theta }\) by executing \(\mathbf {SamplePre}( \mathbf{F} , \mathbf{T}_{ \theta , f} , - \mathbf{D}_{\theta } , \sigma )\), set \(\overline{\mathbf{R}}_{\alpha ,f } = \mathbf {Power2}_q( \mathbf{R}_{ \alpha , f } )\), and compute
$$\mathbf{Q} = \begin{bmatrix} \mathbf{E}_1 \mathbf{A}_{\beta } + \mathbf{E}_2 &{} \mathbf{E}_1 \mathbf{D}_{\beta } + \mathbf{E}_3 + \overline{ \mathbf{R} }_{ \theta , f } \\ \mathbf{0}_{m \times m} &{} \mathbf{I}_{m \times m} \end{bmatrix} \in \mathbb {Z}_q^{ (2km + m ) \times 2m}.$$ -
2)
In the case that \(f( \mathbf{x}^* ) = 0\), choose a matrices \(\mathbf{M} \leftarrow \mathbb {Z}^{ 2km \times m }\) uniformly at random, and compute
$$\mathbf{Q} = \begin{bmatrix} \mathbf{E}_1 \mathbf{A}_{\beta } + \mathbf{E}_2 &{} \mathbf{M} \\ \mathbf{0}_{m \times m} &{} \mathbf{I}_{m \times m} \end{bmatrix} \in \mathbb {Z}_q^{ (2km + m ) \times 2m}.$$
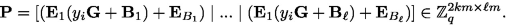
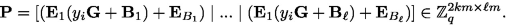
If \(\mathbf{y}\) is none or null, then set \(\mathbf{P}\) as a null matrix. Otherwise, samples \(\ell \) matrices \(\mathbf{E}_{B_i}\) from error distribution \(\chi ^{2km \times m}\) and compute,
Output \(rk_{ \theta ,f \rightarrow \beta , \mathbf{y} } = ( \mathbf{Q} , \mathbf{P} )\) as re-encryption key.
-
1)
Rights and permissions
Copyright information
© 2021 Springer Nature Switzerland AG
About this paper
Cite this paper
Liang, X., Weng, J., Yang, A., Yao, L., Jiang, Z., Wu, Z. (2021). Attribute-Based Conditional Proxy Re-encryption in the Standard Model Under LWE. In: Bertino, E., Shulman, H., Waidner, M. (eds) Computer Security – ESORICS 2021. ESORICS 2021. Lecture Notes in Computer Science(), vol 12973. Springer, Cham. https://doi.org/10.1007/978-3-030-88428-4_8
Download citation
DOI: https://doi.org/10.1007/978-3-030-88428-4_8
Published:
Publisher Name: Springer, Cham
Print ISBN: 978-3-030-88427-7
Online ISBN: 978-3-030-88428-4
eBook Packages: Computer ScienceComputer Science (R0)