Abstract
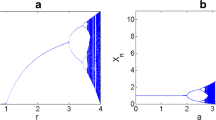
In this communication, we have presented a technique to synthesize resilient nonlinear mechanisms for the construction of substitution box for image encryption that utilizes a multiplicative group of nonzero elements of Galois field of order 256. The proposed nonlinear component assists in transforming the intelligible message or plaintext into an enciphered format by the use of exponential and Tinkerbell chaotic maps. The proposed substitution box is sensitive to the initial conditions provided to the chaotic system, which are subsequently used as parameters in creating an instance. The simulation results show that the use of the proposed substitution box to image encryption scheme provides an efficient and secure way for real-time communications.














Similar content being viewed by others
References
Alvarez G, Li S (2006) Some basic cryptographic requirements for chaos-based cryptosystems. Int J Bifurc Chaos Appl Sci Eng 16(8):2129–2153
Jakimoski G, Kocarev L (2001) Chaos and cryptography: block encryption ciphers. IEEE Trans Circuits Syst I Fundam Theory Appl 48(2):163–169
Tang G, Liao X, Chen Y (2005) A novel method for designing S-boxes based on chaotic maps. Chaos, Solitons Fractals 23:413–419
Khan M, Shah T (2014) A novel construction of substitution box with Zaslavskii chaotic map and symmetric group. J Intell Fuzzy Syst. doi:10.3233/IFS-141434
Khan M, Shah T (2014) A novel image encryption technique based on Hénon chaotic map and S8 symmetric group. Neural Comput Appl 25:1717–1722
Khan M, Shah T (2014) A literature reviews on image encryption. 3D Res 5(4):29–1722. doi:10.1007/s13319-014-0029-0
Khan M, Shah T, Batool SI (2014) Texture analysis of chaotic coupled map lattices based image encryption algorithm. 3D Res 5:19. doi:10.1007/s13319-014-0019-2
Khan M, Shah T (2014) A novel statistical analysis of chaotic s-box in image encryption. 3D Res 5:16. doi:10.1007/s13319-014-0016-5
Khan M, Shah T, Mahmood H, Gondal MA (2013) An efficient method for the construction of block cipher with multi-chaotic systems. Nonlinear Dyn 71(3):489–492
Khan M, Shah T, Mahmood H, Gondal MA (2013) An efficient technique for the construction of substitution box with chaotic partial differential equation. Nonlinear Dyn 73(2013):1795–1801
Khan M, Shah T (2013) An efficient construction of substitution box with fractional chaotic system. Signal Image Video Process. doi:10.1007/s11760-013-0577-4
Khan M, Shah T (2014) A construction of novel chaos base nonlinear component of block cipher. Nonlinear Dyn 76:377–382
Khan M, Shah T, Mahmood H et al (2012) A novel technique for the construction of strong S-boxes based on chaotic Lorenz systems. Nonlinear Dyn 70:2303–2311
Zhang Qiang, Guo Ling, Wei Xiaopeng (2010) Image encryption using DNA addition combining with chaotic maps. Math Comput Model 52:2028–2035
Saha LM, Tehri R (2010) Applications of recent indicators of regularity and chaos to discrete maps. Int J Appl Math Mech 6(1):86–93
Prokhorow MD, Ponomarenko VI (2008) Encryption and decryption of information in chaotic communication systems governed by delay-differential equations. Chaos, Solitons Fractals 35:871–877
Tang Y, Wang Z, Fang J (2010) Image encryption using chaotic coupled map lattices with time-varying delays. Commun Nonlinear Sci Numer Simul 15:2456–2468
Wang Y, Xie Q, Wu Y et al (2009) A software for S-box performance analysis and test. In: 2009 international conference on electronic commerce and business intelligence. Beijing, China, p 125–128
Webster A, Tavares S (1986) On the design of S-boxes. In: Advances in Cryptology: Proceedings of Crypto’85, Santa Barbara, USA. Lecture notes in computer science. 218: 523–534
Adams C, Tavares S (1989) Good S-boxes are easy to find. In: Advances in Cryptology: Proceedings of Crypto’89, Santa Barbara, USA. Lecture notes in computer science. 435: 612–615
Biham E, Shamir A (1991) Differential cryptanalysis of DES-like cryptosystems. J. Cryptol 4(1):3–72
Cusick TW, Stanica P (2009) Cryptographic boolean functions and applications. Elsevier, Amsterdam
Youssef AM, Tavares SE, Gong G (2006) On some probabilistic approximations for AES-like S-boxes. Discrete Math 306(16):2016–2020
Youssef AM, Tavares SE (2005) Affine equivalence in the AES round function. Discrete Appl Math 148(2):161–170
Jing-mei L, Bao-dian W, Xiang-guo C et al (2005) Cryptanalysis of Rijndael S-box and improvement. Appl Math Comput 170(2):958–975
Borujeni SE, Eshghi M (2011) Chaotic image encryption system using phase-magnitude transformation and pixel substitution. J Telecommun Syst. doi:10.1007/s11235-011-9458-8
Faraoun Kamel (2010) Chaos-based key stream generator based on multiple maps combinations and its application to images encryption. Int Arab J Inf Technol 7:231–240
Zhu C (2012) A novel image encryption scheme based on improved hyperchaotic sequences. J Opt Commun 285:29–37
Zhang G, Liu Q (2011) A novel image encryption method based on total shuffling scheme. J Opt Commun 284:2775–2780
Mazloom S, Eftekhari-Moghadam AM (2009) Color image encryption based on coupled nonlinear chaotic map. J Chaos Solitons Fractals 42:1745–1754
Kwok HS, Tang WKS (2007) A fast image encryption system based on chaotic maps with finite precision representation. J Chaos Solitons Fractals 32:1518–1529
Rhouma R, Belghith S (2008) Cryptanalysis of a new image encryption algorithm based on hyper-chaos. J Phys Lett A 372:5973–5978
Zhang Q, Guo L, Wei X (2010) Image encryption using DNA addition combining with chaotic maps. J Math Comput Model 52:2028–2035
Ferguson N, Schroeppel R, Whiting D (2001) A simple algebraic representation of Rijndael. In: Selected areas in cryptography SAC01, LNCS. 2259:103–111
Mentens N, Batina L, Preneel B, Verbauwhede I (2005) A systematic evaluation of compact hardware implementations for the Rijndael S-box. CT RSA LNCS 3376:323–333
Lidl R, Niederreiter H (1994) Introduction to finite fields and their applications. Cambridge University Press, Cambridge
Khanzadi H, Omam MA, Lotfifar F, Eshghi M (2010) Image encryption based on gyrator transform using chaotic maps. IEEE Conference signal process 2608–2612
Baigèneres T, Lu Y, Vaudenay S, Junod P, Monnerat J (2005) A classical introduction to cryptography exercise book. Springer, US
Author information
Authors and Affiliations
Corresponding author
Rights and permissions
About this article
Cite this article
Khan, M., Shah, T. An efficient chaotic image encryption scheme. Neural Comput & Applic 26, 1137–1148 (2015). https://doi.org/10.1007/s00521-014-1800-0
Received:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s00521-014-1800-0