Abstract
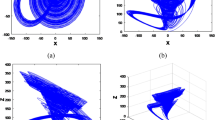
We present a fast and efficient hash algorithm based on a generalized chaotic mapping with variable parameters in this paper. We first define a generalized chaotic mapping by utilizing piecewise linear chaotic map and trigonometric functions. Then, we convert the arbitrary length of message into the corresponding ASCII values and perform 6-unit iterations with variable parameters and message values based on the generalized chaotic mapping. The final hash value is obtained by cascading extracted bits from iteration state values. We excessively evaluate the proposed algorithm in terms of distribution of hash value, sensitivity of hash value to the message and secret keys, statistical analysis of diffusion and confusion, analysis of birthday attacks and collision resistance, analysis of secret keys, analysis of speed, and comparison with other algorithms, and the results illustrate that the suggested algorithm is fast, efficient, and enough simple and has good confusion and diffusion capabilities, strong collision resistance, and a high level of security.





Similar content being viewed by others
References
Rompel J (1990) One-way functions are necessary and sufficient for secure signatures. In: Proceedings of the 22th annual ACM symposium on theory of computing, pp 387–394
Sklavos N, Alexopoulos E, Koufopavlou O (2003) Networking data integrity: high speed architectures and hardware implementations. Int Arab J Inf Technol 1:54–59
Tsudik G (1992) Message authentication with one-way hash functions. ACM SIGCOMM Comput Commun Rev 22:29–38
Pieprzyk J, Sadeghiyan B (1993) Design of hashing algorithms, Lecture Notes in Computer Science. Springer, Berlin
Knudsen L, Preneel B (2002) Construction of secure and fast hash functions using nonbinary error-correcting codes. IEEE Trans Inf Theory 48:2524–2539
Amin M, Faragallah OS, El-Latif AAA (2009) Chaos based hash function (CBHF) for cryptographic applications. Chaos Solitons Fractals 42(2):767–772
Li Y, Xiao D, Deng S (2012) Secure hash function based on chaotic tent map with changeable parameter. High Technol Lett 18(1):7–12
Liu J, Wang X, Yang K, Zhao C (2012) A fast new cryptographic hash function based on integer tent mapping system. J Comput 7(7):1671–1680
Wang Y, Yang D, Du M, Yang H (2007) One-way hash function construction based on iterating a chaotic map. In: Proceedings-CIS Workshops 2007, 2007 international conference on computational intelligence and security workshops, pp 791–794
Maqableh M, Samsudin AB, Alia MA (2008) New hash function based on chaos theory (CHA-1). Int J Comput Sci Netw Secur 8(2):20–26
Jiteurtragool N, Ketthong P, Wannaboon C, San-Um W (2013) A topologically simple keyed hash function based on circular chaotic sinusoidal map network. In: International conference on advanced communication technology, ICACT, pp 1089–1094 (2013)
Zhang Q, Zhang H, Li Z (2009) One-way hash function construction based on conservative chaotic systems. In: 5th international conference on information assurance and security, IAS 2009, vol 2, pp 402–405
Akhavan A, Samsudin A, Akhshani A (2009) Hash function based on piecewise nonlinear chaotic map. Chaos Solitons Fractals 42:1046–1053
Li Y, Xiao D, Deng S, Han Q, Zhou G (2011) Parallel hash function construction based on chaotic maps with changeable parameters. Neural Comput Appl 20(8):1305–1312
Xiao D, Liao X, Deng S (2008) Parallel keyed hash function construction based on chaotic maps. Phys Lett A 372:4682–4688
Xiao D, Liao X, Wang Y (2009) Improving the security of a parallel keyed hash function based on chaotic maps. Phys Lett A 373:4346–4353
Kanso A, Ghebleh M (2013) A fast and efficient chaos-based keyed hash function. Commun Nonlinear Sci Numer Simul 18:109–123
Nouri M, Khezeli A, Ramezani A, Ebrahimi A (2012) A dynamic chaotic hash function based upon circle chord methods. In: 2012 6th international symposium on telecommunications, IST 2012, pp 1044–1049
Akhavan A, Samsudin A, Akshani A (2013) A novel parallel hash function based on 3D chaotic map. EURASIP J Adv Signal Process 2013(1):1–12
Deng S, Li Y, Xiao D (2010) Analysis and improvement of a chaos-based hash function construction. Commun Nonlinear Sci Numer Simul 15(5):1338–1347
Alvarez G, Montoya F, Romera M, Pastor G (2004) Cryptanalysis of dynamic look-up table based chaotic cryptosystems. Phys Lett A 326(3):211–218
Arumugam G, Lakshmi Praba V, Radhakrishnan S (2007) Study of chaos functions for their suitability in generating message authentication codes. Appl Soft Comput 7(3):1064–1071
Li C, Wang S (2007) A new one-time signature scheme based on improved chaos hash function. Comput Eng Appl 43(35):133–136
Guo W, Wang X, He D, Cao Y (2009) Cryptanalysis on a parallel keyed hash function based on chaotic maps. Phys Lett A 373(36):3201–3206
Xiao D, Peng W, Liao X, Xiang T (2010) Collision analysis of one kind of chaos-based hash function. Phys Lett A 374(10):1228–1231
Wang S, Shan P (2011) Security analysis of a one-way hash function based on spatiotemporal chaos. Chin Phys B 20(9):090504–090507
Wang S, Li D, Zhou H (2012) Collision analysis of a chaos-based hash function with both modification detection and localization capability. Commun Nonlinear Sci Numer Simul 17(2):780–784
Bellare M, Ristenpart T, Multi-property-preserving hash domain extension: the EMD transform. In: Proceedings of 2nd NIST cryptographic hash workshop, Corwin Pavilion, UCSB Santa Barbara, CA
Zhang J, Xian X (2001) Nonlinear adaptive predictive targeting control of the continuous chaotic system. Acta Phys Sin 50(11):2092–2096
Zhang J, Wang X, Zhang W (2007) Chaotic keyed hash function based on feedforward–feedback nonlinear digital filter. Phys Lett A 362:439–448
Kanso A, Yahyaoui H, Almulla M (2012) Keyed hash function based on a chaotic map. Inf Sci 186:249–264
Wong KW (2003) A combined chaotic cryptographic and hashing scheme. Phys Lett A 307:292–298
Yearly Report on Algorithms and Keysizes, D.SPA.17 Rev. 1.0, ICT-2007-216676 ECRYPT II (2011)
Rivest R (1992) The MD5 message-digest algorithm. IETF Network Working Group, RFC 1321
Kanso A, Ghebleh M (2015) A structure-based chaotic hashing scheme. Nonlinear Dyn 81:27–40
Li Y, Deng S, Xiao D (2011) A novel Hash algorithm construction based on chaotic neural network. Neural Comput Appl 20:133–141
Li Y, Xiao D, Deng S (2012) Keyed hash function based on a dynamic lookup table of functions. Inf Sci 214:56–75
Ren H, Wang Y, Xie Q, Yang H (2009) A novel method for one-way hash function construction based on spatiotemporal chaos. Chaos Solitons Fractals 42(4):2014–2022
Teh JS, Samsudin A, Akhavan A (2015) Parallel chaotic hash function based on the shuffle-exchange network. Nonlinear Dyn 81:1067–1079
Wang Y, Liao X, Xiao D, Wong K (2008) One-way hash function construction based on 2D coupled map lattices. Inf Sci 178(5):1391–1406
Wang Y, Wong KW, Xiao D (2011) Parallel hash function construction based on coupled map lattices. Commun Nonlinear Sci Number Simul 16:2810–2821
Xiao D, Liao X, Wang Y (2009) Parallel keyed hash function construction based on chaotic neural network. Neurocomputing 72:2288–2296
Xiao D, Shih FY, Liao XF (2010) A chaos-based hash function with both modification detection and localization capabilities. Commun Nonlinear Sci Numer Simul 15:2254–2261
Zhang J, Wang X, Zhang W (2007) Chaotic keyed hash function based on feedforward–feedback nonlinear digital filter. Phys Lett A 362:439–448
Zhang H, Wang X, Li Z, Liu D (2005) One way hash function construction based on spatiotemporal chaos. Acta Phys Sin 54:4006–4011
Luo Y, Du M (2012) One-way hash function construction based on the spatiotemporal chaotic system. Chin Phys B 21(6):060503
Li Y, Qi X, Ren Z, Zhou G, Xiao D, Deng S (2011) Energy modeling and optimization through joint packet size analysis of BSN and WiFi networks. IEEE IPCCC, Orlando
Qi X, Zhou G, Li Y, Peng G (2012) Radiosense: Exploiting wireless communication patterns for body sensor network activity recognition. IEEE RTSS, San Juan, Puerto Rico
Nguyen DT, Zhou G, Qi X, Peng G, Zhao J, Nguyen T, Le D (2013) Storage-aware smartphone energy savings. ACM Ubicomp, Zurich
Norouzi B, Seyedzadeh SM, Mirzakuchaki S, Mosavi MR (2014) A novel image encryption based on hash function with only two-round diffusion process. Multimedia Syst 20:45–64
Lo NW, Chiang MC, Hsu CY (2015) Hash-based anonymous secure routing protocol in mobile ad hoc networks. IEEE Asia JCIS
Kanguzhin BE, Nurakhmetov DB, Tokmagambetov NE (2014) Laplace operator with δ-like potentials. Russ Math 58:6–12
Li Y, Xiao D, Deng S (2011) Hash function construction based on the chaotic look-up table with changeable parameter. Int J Mod Phys B 25:3835–3851
Acknowledgments
Our sincere thanks go to the anonymous reviewers for their valuable comments. This work is supported in part by the National Natural Science Foundation of China (Grant Nos. 61402380 and 61528206), the Natural Science Foundation of CQ CSTC (Grant No. cstc2015jcyjA40044), and the Fundamental Research Funds for the Central Universities (Grant No. XDJK2015B030).
Author information
Authors and Affiliations
Corresponding author
Rights and permissions
About this article
Cite this article
Li, Y., Li, X. & Liu, X. A fast and efficient hash function based on generalized chaotic mapping with variable parameters. Neural Comput & Applic 28, 1405–1415 (2017). https://doi.org/10.1007/s00521-015-2158-7
Received:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s00521-015-2158-7