Abstract
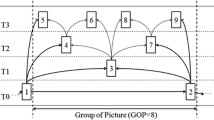
Taking advantage of the inter-layer prediction technique used in H.264/scalable video coding (H.264/SVC), in this paper we propose an efficient block-based encryption scheme (BBES) for encrypting H.264/SVC enhancement layers (ELs). BBES operates in three modes, namely, Intra-MB mode, Group-MB mode and 4Group-MB mode. All the three modes are effective in securing ELs, preserve the “adaptation-transparent” property of H.264/SVC, and are format-compliant to the H.264/SVC bitstream format specifications. Moreover, Intra-MB and Group-MB modes also possess the property we termed as “transcoding transparency”. Experimental results indicate that BBES has low computational complexity and small compression overhead. Thus, BBES is suitable for transparent encryption of H.264/SVC bitstreams in which ELs are encrypted but base layers are left in cleartext.











Similar content being viewed by others
Notes
Encoded H.264/SVC (QCIF) consists of base layer and an encrypted quality enhancement layer. Quantization parameters (QP) of base layer and enhancement layer are equal 40 and 30, respectively.
Available at http://media.xiph.org/video/derf/.
if the compared images are the same, the scores are 1.
If the compared images are the same, the score are 0.
References
Schwarz, H., Marpe, D., Wiegand, T.: Overview of the scalable video coding extension of the h.264/avc standard. IEEE Trans Circuits Syst Video Technol 17(9), 1103–1120 (2007)
Apostolopoulos, J.G., Wee, S.J.: Secure scalable streaming enabling transcoding without decryption. In: Proceedings of the IEEE International Conference on Image Processing, pp. 437–440 (2001)
Gergely, V., Fehér, G.: Enhancing progressive encryption for scalable video streams. In: Conference on Information and Communications Technologies, pp. 51–58 (2009)
Sohn, H., Neve, W.D., Ro, Y.M.: Region-of-interest scrambling for scalable surveillance video using jpeg xr. ACM Multimedia, Barcelona, pp. 861–864 (2009)
Sohn, H., Neve, W.D., Ro, Y.M.: Privacy protection in video surveillance systems: Analysis of subband-adaptive scrambling in jpeg xr. IEEE Trans Circuits Syst Video Technol 21(2), 170–177 (2011)
Yuan, C., Zhu, B.B., Wang, Y., Li, S., Zhong, Y.: Efficient and fully scalable encryption for mpeg-4 fgs. IEEE Int Symp Circuits Syst 2, 620–623 (2003)
Yuan, C., Zhu, B.B., Wang, Y., Li, S., Zhong, Y.: Scalable protection for mpeg-4 fine granularity scalability. IEEE Trans Multimed 7, 222–233 (2005)
Shahid, Z., Chaumont, M., Puech, W.: Selective and scalable encryption of enhancement layers for dyadic scalable H.264/AVC by scrambling of scan patterns. In: Proceedings of the International Conference on Image Processing, pp. 1273–1276 (2009)
Stütz, Thomas, Uhl, Andreas: A survey of h.264 avc/svc encryption. IEEE Transactions on Circuits and System for Video Technology 22(3), 325–339 (2012)
Norcen R., Uhl, A.: Encryption of wavelet-coded imagery using random permutations. In: Proceedings of the IEEE International Conference on Image Processing, pp. 3431–3434 (2004)
Zeng, W., Lei, S.: Efficient frequency domain selective scrambling of digital video. IEEE Trans Multimed 5(1), 118–129 (2003)
Reichel, J., Schwarz, H., Wien, M.: Joint Scalable Video Model JSVM-19, doc. Joint Video Team (JVT) of ISO/IEC MPEG & ITU-T VCEG (2011)
Won, Y.G., Bae, T.M., Ro, Y.M.: Scalable protection and access control in full scalable video coding. In: Proceedings of the International Workshop on Digital Watermarking, pp. 407–421 (2006)
Algin, G.B., Tunali, E.T.: Scalable video encryption of h.264 svc codec. J Visual Commun Image Represent 22(4), 353–364 (2011)
Park, S.W., Shin, S.U.: Efficient selective encryption scheme for the h.264/scalable video coding(svc). In: Proceedings of the 4th International Conference on Networked Computing and Advanced Information Management, pp. 371–376 (2008)
Li, C.H., Zhou, X.X., Zhong, Y.Z.: Nal level encryption for scalable video coding. In: Proceedings of the Pacific-Rim Conference on Multimedia, pp. 496–505 (2008)
Li, C.H., Yuan, C., Zhong, Y.Z.: Layered encryption for scalable video coding,” In: Proceedings of the 2nd International Congress on Image and Signal Processing, pp. 1–4 (2009)
Wu, C.P., Kuo, C.C.J.: Fast encryption methods for audiovisual data confidentiality. In: Proceedings of SPIE in Multimedia Systems and Applications III, pp. 284–295 (2000)
Lian, S.G.: Secure service convergence based on scalable media coding. Telecommun Syst 45(1), 21–35 (2010)
Magli, E., Grangetto, M., Olmo, G.: Transparent encryption techniques for h.264/avc and h.264/svc compressed video. Signal Process 91(5), 1103–1114 (2011)
Hellwagner, H., Stütz, T., Kuschnig, R., Uhl, A.: Efficient in-network adaptation of encrypted h.264/svc content. Signal Process Image Commun 24(9), 740–758 (2009)
Arachchi, H.K., Perramon, X., Dogan, S., Kondoz, A.M.: Adaptation-aware encryption of scalable h.264/avc video for content security. Signal Process Image Commun 24(6), 468–483 (2009)
Thomas, N., Bull, D., Redmill, D.: A novel h.264 svc encryption scheme for secure bit-rate transcoding. In: Proceedings of the Picture Coding Symposium, pp. 1–4 (2009)
ITU-T Recommendation H.264 & ISO/IEC 14496 AVC. Advanced video coding for generic audio-visual services. ITU-T and ISO/IEC JTC 1 Recommendation H.264 and ISO/IEC 14 496-10 (MPEG-4) AVC (2003)
Katz, J., Lindell, Y.: Introduction to Modern Cryptography. Chapman & Hall/CRC, London (2008)
Hofbauer, H., Uhl, A.: An effective and efficient visual quality index based on local edge gradients.In: Proceedings of the 3rd European Workshop on Visual Information Processing (EUVIP), pp. 162–167 (2011)
Wang, Z., Bovik, A.C., Sheikh, H.R., Simoncelli, E.: Image quality assessment: From error visibility to structural similarity. IEEE Trans Image Process 13(4), 600–612 (2004)
Mao Y., Wu M.: Security evaluation for communication-friendly encryption of multimedia. In: Proceedings of the IEEE International Conference on Image Processing, pp. 1522–4880 (2004)
Yao, Y., Xu, Z., Li, W.: Visual security evaluation for video encryption.In: Proceedings of the 3rd International Conference on Communications and Networking in China, pp. 1317–1322 (2008)
Tong, L., Dai, F., Zhang, Y., Li, J.: Visual security evaluation for video encryption. ACM Multimedia, Barcelona, pp. 835–838 (2010)
Hemami, S.S., Rouse, D.: Natural image utility assessment using image contours. In: Proceedings of the IEEE International Conference on Image Processing, pp. 2217–2220 (2009)
Acknowledgments
This work was supported in part by A*STAR SERC Grant No. 102 101 0027 in Singapore.
Author information
Authors and Affiliations
Corresponding author
Rights and permissions
About this article
Cite this article
Deng, R.H., Ding, X., Wu, Y. et al. Efficient block-based transparent encryption for H.264/SVC bitstreams. Multimedia Systems 20, 165–178 (2014). https://doi.org/10.1007/s00530-013-0326-0
Published:
Issue Date:
DOI: https://doi.org/10.1007/s00530-013-0326-0