Abstract
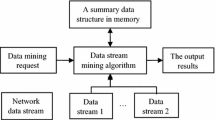
Intrusion detection provides important protection for network security and anomaly detection as a type of intrusion detection, which can recognize the pattern of normal behaviors and label the behaviors which departure from normal pattern as anomaly behaviors. The updating of network equipment and broadband speed makes the data mining object change from static data sets to dynamic data streams. We think that the traditional methods based on data set do not satisfy the needs of dynamic network environment. The network data stream is temporal and cannot be treated as static data set. The concept and distribution of data objects is variety in different time stamps and the changing is unpredictable. Therefore, we propose an improved data stream clustering algorithm and design the anomaly detection model according to the improved algorithm. The established model can be modified with the changing of data stream and detect anomaly behaviors in time.






Similar content being viewed by others
References
Lee, W., Stolfo, S., Mok, K.: Mining audit data to build intrusion detection models. In: International Conference on Knowledge Discovery & Data Mining, pp. 66–72 (1998)
Keegan, N., Ji, S.Y., Chaudhary, A., Concolato, C., Yu, B., Jeong, D.: A survey of cloud-based network intrusion detection analysis. Hum. Cent. Comput. Inf. Sci. 6(1), 19–35 (2016)
Gu, B., Sheng, V.S., Tay, K.Y., Romano, W., Li, S.: Incremental support vector learning for ordinal regression. IEEE Trans. Neural Netw. Learn. Syst. 26(7), 1403–1416 (2014)
Gu, B., Sheng, V.S., Wang, Z., Ho, D., Osman, S., Li, S.: Incremental learning for \(\nu \)-support vector regression. Neural Netw. 67, 140–150 (2015)
Li, W., Li, X., Yao, M., Jiang, J., Jin, Q.: Personalized fitting recommendation based on support vector regression. Hum. Cent. Comput. Inf. Sci. 5(1), 21–32 (2015)
Gaur, M., Pant, B.: Trusted and secure clustering in mobile pervasive environment. Hum.-Cent. Comput. Inf. Sci. 5(1), 1–17 (2015)
Li, L., Ye, J., Deng, F., Xiong, S., Zhong, L.: A comparison study of clustering algorithms for microblog posts. Clust. Comput. 19(3), 1333–1345 (2016)
Chen, C.-C., Fu, X., Chang, C.-Y.: A terms mining and clustering technique for surveying network and content analysis of academic groups exploration. Clust. Comput. 20(1), 43–52 (2017)
Jang, J., Lee, Y., Lee, S., Shin, D., Kim, D., Rim, H.: A novel density-based clustering method using word embedding features for dialogue intention recognition. Clust. Comput. 19(4), 2315–2326 (2016)
Yin, C., Zhang, S.: Parallel implementing improved k-means applied for image retrieval and anomaly detection. Multimed. Tools Appl. 2016, 1–17 (2016)
Yin, C., Zhang, S., Kim, K.: Mobile anomaly detection based on improved self-organizing maps. Mob. Inf. Syst. 2017, 1–9 (2017)
Yin, C., Zhang, S., Xi, J., Wang, J.: An improved anonymity model for big data security based on clustering algorithm. Concurr. Comput.-Pract. Exp. 29(7), 1–13 (2016)
Silva, J., Faria, E., Barros, R., Hruschka, E.: Data stream clustering: a survey. ACM. Comput. Surv. 46(1), 125–134 (2013)
Oh, S., Kang, S., Byun, Y., Jeong, T., Lee, W.: Anomaly intrusion detection based on clustering a data stream. In: ACIS International Conference on Software Engineering Research, Management and Applications, vol. 4176, pp. 220–227 (2005)
Guha, S., Meyerson, A., Mishra, N., Motwani, R.: Clustering data streams: theory and practice. IEEE Trans. Knowl. Data Eng. 15(3), 515–528 (2003)
Aggarwal, C., Yu, P., Han, J., Wang, J.: A framework for clustering evolving data streams. In: International Conference on Very Large Data Bases, vol. 29, pp. 81–92 (2003)
Cao, F., Ester, M., Qian, W., Zhou, A.: Density-based clustering over an evolving data stream with noise. In: SIAM International Conference on dData Mining, pp. 328–339 (2006)
Udommanetanakit, K., Rakthanmanon, T., Waiyamai, K.: E-Stream: evolution-based technique for stream clustering. In: Third International Conference on Advanced Data Mining and Applications, pp. 605–615 (2007)
Chen, Y., Tu, L.: Density-based clustering for real-time stream data. In: ACM SIGKDD International Conference on Knowledge Discovery and Data Mining, pp. 133–142 (2007)
Axelsson, S.: The base-rate fallacy and the difficulty of intrusion detection. ACM Trans. Inf. Syst. Sec. 3(3), 186–205 (2000)
Acknowledgements
This work was funded by the National Natural Science Foundation of China (61373134, 61402234). It was also supported by the Priority Academic Program Development of Jiangsu Higher Education Institutions (PAPD), Jiangsu Key Laboratory of Meteorological Observation and Information Processing (KDXS1105) and Jiangsu Collaborative Innovation Center on Atmospheric Environment and Equipment Technology (CICAEET). Prof. Jin Wang is the corresponding author. We declare that we do not have any conflicts of interest to this work.
Funding This study was funded by the National Natural Science Foundation of China (Grant Number 61373134, 61402234).
Author information
Authors and Affiliations
Corresponding author
Ethics declarations
Conflict of interest
Chunyong Yin, Sun Zhang, Zhichao Yin and Jin Wang declares that they have no conflict of interest. Ethical approval This article does not contain any studies with human participants or animals performed by any of the authors.
Rights and permissions
About this article
Cite this article
Yin, C., Zhang, S., Yin, Z. et al. Anomaly detection model based on data stream clustering. Cluster Comput 22 (Suppl 1), 1729–1738 (2019). https://doi.org/10.1007/s10586-017-1066-2
Received:
Revised:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s10586-017-1066-2