Abstract
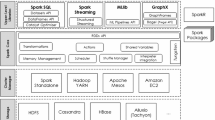
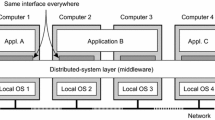
A data layout method suitable for workflow in a cloud computing environment with speech applications is designed and implemented in this research. With the continuous advancement of cloud computing, Internet of Things, wireless communications, mobile Internet and other technologies, data is growing and accumulating at an unprecedented rate. This paper provides the novel efficient speech data processing layout considering prior information and the data structure. On the basis of in-depth research on existing data layout strategies, this paper summarizes several aspects such as incompatibility with energy-saving modes based on storage area division, incompatibility with the heterogeneous HDFS clusters, inflexible data block segmentation algorithms, and randomness of general storage node selection aspects. Especially, considering that speech data related lower-case read-ahead and basic read-ahead are quite different, reflected in the purpose of read-ahead, read-ahead objects, read-ahead execution level, read-ahead trigger conditions, read-ahead feasibility, we propose the efficient robust data mining model to capture the data structure and feature. Through comparing with the other state-of-the-art models, the experiment section gives the clear analysis on the performance.







Similar content being viewed by others
Change history
13 October 2022
This article has been retracted. Please see the Retraction Notice for more detail: https://doi.org/10.1007/s10772-022-10003-y
References
Abdel-Basset, M., Mohamed, M., & Chang, V. (2018). NMCDA: A framework for evaluating cloud computing services. Future Generation Computer Systems, 86, 12–29.
Crisp, S., & Dawdy, K. (2018). Building a magnetic resonance imaging safety culture from the ground up. Journal of Medical Imaging and Radiation Sciences, 49(1), 18–22.
Fan, E., Xie, W., Pei, J., Hu, K., & Li, X. (2018). Neutrosophic hough transform-based track initiation method for multiple target tracking. IEEE Access, 6, 16068–16080.
Huang, C., Lin, W., Lai, C., Li, X., Jin, Y., & Yong, Q. (2019a). Coupling the post-extraction process to remove residual lignin and alter the recalcitrant structures for improving the enzymatic digestibility of acid-pretreated bamboo residues. Bioresource technology, 285, 121355.
Huang, C., Wang, X., Liang, C., Jiang, X., Yang, G., Xu, J., et al. (2019b). A sustainable process for procuring biologically active fractions of high-purity xylooligosaccharides and water-soluble lignin from Moso bamboo prehydrolyzate. Biotechnology for Biofuels, 12(1), 189.
Jiao, J., Venkat, K., & Weissman, T. (2018a). Mutual information, relative entropy and estimation error in semi-martingale channels. IEEE Transactions on Information Theory, 64(10), 6662–6671.
Jiao, Z., Gao, X., Wang, Y., Li, J., & Xu, H. (2018b). Deep Convolutional Neural Networks for mental load classification based on EEG data. Pattern Recognition, 76, 582–595.
Li, H., Lu, R., Misic, J., & Mahmoud, M. (2018c). Security and privacy of connected vehicular cloud computing. IEEE Network, 32(3), 4–6.
Li, J., Zhang, Y., Chen, X., & Xiang, Y. (2018b). Secure attribute-based data sharing for resource-limited users in cloud computing. Computers & Security, 72, 1–12.
Li, P., Li, J., Huang, Z., Gao, C. Z., Chen, W. B., & Chen, K. (2018a). Privacy-preserving outsourced classification in cloud computing. Cluster Computing, 21(1), 277–286.
Lu, Z. H., Zhao, W. L., Ji, L. B., Wen, R., Zhang, Y. S., Wu, J. F., et al. (2018). The histogram analysis of apparent diffusion coefficient maps with standard-or ultrahigh-b value diffusion-weighted MR imaging for differentiating the gleason grade of prostate cancer. Journal of Medical Imaging and Health Informatics, 8(3), 577–582.
Muhammad, K., Hamza, R., Ahmad, J., Lloret, J., Wang, H., & Baik, S. W. (2018). Secure surveillance framework for IoT systems using probabilistic image encryption. IEEE Transactions on Industrial Informatics, 14(8), 3679–3689.
Noor, T. H., Zeadally, S., Alfazi, A., & Sheng, Q. Z. (2018). Mobile cloud computing: Challenges and future research directions. Journal of Network and Computer Applications, 115, 70–85.
Pan, C. T., Chang, W. H., Kumar, A., Singh, S. P., Kaushik, A. C., Sharma, J., et al. (2019). Nanoparticles-mediated brain imaging and disease prognosis by conventional as well as modern modal imaging techniques: A comparison. Current Pharmaceutical Design, 25(24), 2637–2649.
Pavlichin, D. S., Jiao, J., & Weissman, T. (2019). Approximate profile maximum likelihood. Journal of Machine Learning Research, 20(122), 1–55.
Plageras, A. P., Psannis, K. E., Stergiou, C., Wang, H., & Gupta, B. B. (2018). Efficient IoT-based sensor BIG Data collection–processing and analysis in smart buildings. Future Generation Computer Systems, 82, 349–357.
Que, S., Awuah-Offei, K., Demirel, A., Wang, L., Demirel, N., & Chen, Y. (2019). Comparative study of factors affecting public acceptance of mining projects: Evidence from USA, China and Turkey. Journal of Cleaner Production, 237, 117634.
Shah-Mansouri, H., & Wong, V. W. (2018). Hierarchical fog-cloud computing for IoT systems: A computation offloading game. IEEE Internet of Things Journal, 5(4), 3246–3257.
Shao, C., Zhang, Q., Song, Y., & Zhu, D. (2020). Smart home healthcare system based on middleware and counter neural network. Journal of Medical Imaging and Health Informatics, 10(5), 1105–1112.
Thakur, S., Singh, A. K., Ghrera, S. P., & Elhoseny, M. (2019). Multi-layer security of medical data through watermarking and chaotic encryption for tele-health applications. Multimedia Tools and Applications, 78(3), 3457–3470.
Ting, D. S., Liu, Y., Burlina, P., Xu, X., Bressler, N. M., & Wong, T. Y. (2018). AI for medical imaging goes deep. Nature Medicine, 24(5), 539.
Wang, N., Gao, X., Tao, D., Yang, H., & Li, X. (2018). Facial feature point detection: A comprehensive survey. Neurocomputing, 275, 50–65.
Wang, Y., Li, J., & Wang, H. H. (2019). Cluster and cloud computing framework for scientific metrology in flow control. Cluster Computing, 22(1), 1189–1198.
Wang, S., Zhou, J., Liu, J. K., Yu, J., Chen, J., & Xie, W. (2016). An efficient file hierarchy attribute-based encryption scheme in cloud computing. IEEE Transactions on Information Forensics and Security, 11(6), 1265–1277.
Zhang, H., Yu, Y., Jiao, J., Xing, E.P., Ghaoui, L.E., Jordan, M.I. (2019). Theoretically principled trade-off between robustness and accuracy. arXiv preprint arXiv:1901.08573.
Zhang, S., Wang, H., & Huang, W. (2020). Palmprint identification combining hierarchical multi-scale complete LBP and weighted SRC. Soft Computing, 24(6), 4041–4053.
Zhang, S., Wang, H., Huang, W., & You, Z. (2018). Plant diseased leaf segmentation and recognition by fusion of superpixel, K-means and PHOG. Optik, 157, 866–872.
Zhao, G., Wu, Y., He, M., Bai, J., Cheng, J., & Lin, Y. (2019). Preprocessing and grading of glioma data acquired from multicenter. Journal of Medical Imaging and Health Informatics, 9(6), 1236–1245.
Zhou, B., & Buyya, R. (2018). Augmentation techniques for mobile cloud computing: A taxonomy, survey, and future directions. ACM Computing Surveys (CSUR), 51(1), 13.
Author information
Authors and Affiliations
Corresponding author
Additional information
Publisher's Note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
This article has been retracted. Please see the retraction notice for more detail:https://doi.org/10.1007/s10772-022-10003-y
Rights and permissions
Springer Nature or its licensor (e.g. a society or other partner) holds exclusive rights to this article under a publishing agreement with the author(s) or other rightsholder(s); author self-archiving of the accepted manuscript version of this article is solely governed by the terms of such publishing agreement and applicable law.
About this article
Cite this article
Jiang, Y., Liu, X., Li, Y. et al. RETRACTED ARTICLE: A data layout method suitable for workflow in a cloud computing environment with speech applications. Int J Speech Technol 24, 31–40 (2021). https://doi.org/10.1007/s10772-020-09705-y
Received:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s10772-020-09705-y