Abstract
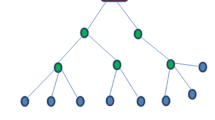
Wireless sensor networks are used in many applications in military, ecology, health, and other areas. These applications often include the monitoring of sensitive information making the security issue one of the most important aspects to consider in this field. However, most of protocols optimize for the limited capabilities of sensor nodes and the application specific nature of the networks, but they are vulnerable to serious attacks. In this paper, a Secure Energy and Reliability Aware data gathering protocol (SERA) is proposed, which provides energy efficiency and data delivery reliability as well as security. The proposed protocol’s security was confirmed by a formal verification carried out using the AVISPA tool and analysis of the most common network layer attacks such as selective forwarding, sinkhole, Sybil, wormhole, HELLO flood, and acknowledgment spoofing attacks. Additionally, a visual simulation environment was developed to evaluate the performance of the proposed protocol.



















Similar content being viewed by others
References
Al Shidhani A, Leung V (2009) Pre-authentication schemes for UMTS-WLAN interworking. EURASIP J Wireless Commun Netw. doi:10.1155/2009/806563
Braginsky D, Estrin D (2002) Rumor Routing Algorithm For Sensor Networks. Proc 1st ACM international workshop on wireless sensor networks and applications. doi: 10.1145/570738.570742
Cam H, Ozdemir S, Muthuavinashiappan D, Nair P (2003) Energy efficient security protocol for wireless sensor networks. IEEE Veh Technol Conf. doi:10.1109/VETECF.2003.1286170
Capkun S, Hubaux J (2005) Secure positioning of wireless devices with application to sensor networks. Proc IEEE INFOCOM. doi:10.1109/INFCOM.2005.1498470
Capkun S, Hubaux JP (2006) Secure positioning in wireless networks. IEEE J Selected Areas Commun. doi:10.1109/JSAC.2005.861380
Carlson J, Han R, Lao S, Narayan C, Ghani S (2003) Rapid prototyping of mobile input devices using wireless sensor nodes. Proc WMCSA’03, pp 21–29
Conti M, Di Pietro R, Mancini L, Mei A (2008) Emergent properties: detection of the node-capture attack in mobile wireless sensor networks. Proc of the first ACM conference on Wireless network security. doi: 10.1145/1352533.1352568
Douceur J (2002) The Sybil attack. In First International Workshop on Peer-to-Peer Systems, vol 2429 of LNCS
Giruka V, Singhal M, Royalty J, Varanasi S (2008) Security in wireless sensor network. Wireless Comm Mobile Comp 8(1):1–24
Heinzelman W, Chandrakasan A, Balakrishnan H (2000) Energy-efficient communication protocol for wireless microsensor networks. Proc of the 33rd Hawaii International Conference on System Sciences
Heinzelman W, Chandrakasan A, Balakrishnan H (2002) An application-specific protocol architecture for wireless microsensor networks. IEEE Trans Wireless Commun 1(4):660–670. doi:10.1109/TWC.2002.804190
Hill J et al (2000) System architecture directions for networked sensors. Architectural Support for Programming Languages and Operating Systems, pp 93–104, 2000
Hodjat A, Verbauwhede I (2002) The energy cost of secrets in ad-hoc networks. Proc IEEE Circuits and Systems Workshop on Wireless Communications and Networking, pp 4
Hu Y, Perrig A, Johnson DB (2002) Wormhole detection in wireless ad hoc networks. Technical Report TR01-384. Department of Computer Science, Rice University
Hu YC, Perrig A, Johnson DB (2003) Packet leashes: a defense against wormhole attacks in wireless networks. Proc IEEE Infocom 3:1976–1986
Hung L et al (2009) SCODE: a secure coordination-based data dissemination to mobile sinks in sensor networks. IEICE Trans Commun E92-B(1):131–142
Intanagonwiwat C, Govindan R, Estrin D, Heidemann J, Silva F (2003) Directed diffusion for wireless sensor networking. IEEE/ACM Trans Netw. doi:10.1109/TNET.2002.808417
Karlof C, Wagner D (2003) Secure routing in wireless sensor networks: attacks and countermeasures. Proc IEEE Int Workshop Sensor Netw Protoc Appl. doi:10.1109/SNPA.2003.1203362
Kim M et al (2008) An energy-aware multipath routing algorithm in wireless sensor networks. IEICE Trans Inf Syst E91-D:2419–2427
Lindsey S, Raghavendra CS (2002) PEGASIS: Power-efficient gathering in sensor information systems. IEEE Aerospace Conference Proc, pp 3-1125–3-1130. doi: 10.1109/AERO.2002.1035242
Mainwaring A, Polastre J, Szewczyk R, Culler D, Anderson J (2002) Wireless sensor networks for habitat monitoring. Proc of the 1st ACM international workshop on wireless sensor networks and applications. doi: 10.1145/570738.570751
Manjeshwar A, Agrawal DP (2001) TEEN: a routing protocol for enhanced efficiency in wireless sensor networks. IEEE International Parallel Distributed Processing Symposium, pp 2009–2015
Manjeshwar A, Agrawal DP (2002) APTEEN: A hybrid protocol for efficient routing and comprehensive information retrieval in wireless sensor networks. IEEE International Parallel Distributed Processing Symposium, pp 195–202
Otto C, Milenkovic A, Sanders C, Jovanov E (2006) System architecture of a wireless body area sensor network for ubiquitous health monitoring. J Mobile Multimed 1(4):307–326
Park T, Shin K (2004) LiSP: a lightweight security protocol for wireless sensor networks. ACM Trans Embedded Comput Syst. doi:10.1145/1015047.1015056
Perrig A et al (2002) SPINS: security protocols for sensor networks. Wireless Netw. doi:10.1023/A:1016598314198
Pura M, Patriciu V, Bica I (2009) Modeling and formal verification of implicit on-demand secure ad hoc routing protocols in HLPSL and AVISPA. Int J Comput Commun 2(3):25–32
The AVISPA project (2010) Automated Validation of Internet Security Protocols http://www.avispa-project.org. Accessed 17 December 2010
U.A.F. (2009) ARGUS advanced remote ground unattended sensor systems. Department of Defense. http://www.globalsecurity.org/ intell/systems/arguss.htm. Accessed 15 June 2010
Xu Y, Heidemann J, Estrin D (2001) Geography-informed energy conservation for ad hoc routing. Proc Seventh Annual ACM/IEEE International Conference on Mobile Computing and Networking (MobiCom 2001). doi: 10.1145/381677.381685
Ye M, Li C, Chen G, Wu J (2005) EECS: an energy efficient clustering scheme in wireless sensor networks. Proc IPCCC 2005. doi: 10.1109/PCCC.2005.1460630
Younis O, Fahmy S (2004) HEED: a hybrid, energy-efficient. Distributed clustering approach for Ad Hoc sensor networks. IEEE Trans Mob Comput. doi:10.1109/TMC.2004.41
Zhou Y, Fang Y, Zhang Y (2008) Securing wireless sensor network: a survey. IEEE Commun Surv Tutorial. doi:10.1109/COMST.2008.4625802
Acknowledgment
Sang Guun Yoo likes to take this opportunity to thank Overseas Korean Foundation (OKF) for its scholarship support. He had the privilege to be the recipient of this award from 2007 to 2010.
Author information
Authors and Affiliations
Corresponding author
Rights and permissions
About this article
Cite this article
Yoo, S.G., Kang, Sh. & Kim, J. SERA: a secure energy reliability aware data gathering for sensor networks. Multimed Tools Appl 73, 617–646 (2014). https://doi.org/10.1007/s11042-011-0735-z
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11042-011-0735-z