Abstract
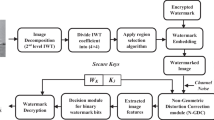
The face regions of digital pictures are some of the principal target of tampering to generate a potential scandal, causing social and economic damages to involved persons. In this paper, we propose a face region authentication and recovery system, in which the face regions are automatically protected at the moment when the picture is taken by a digital camera. When the original face of the picture is replaced by another face by malicious person, the system can detect the tampered face and recover the original one. The proposed system consists of two stages: the face region protection stage and the face region tamper detection and recovery stage. In both stages, the face detection module based on the Viola-Jones algorithm, face region encoding/decoding modules based on the Set Partitioning in Hierarchical Trees (SPIHT) algorithm and watermarking module based on Quantization Index Modulation (QIM) are used. These three algorithms, Viola-Jones detector, SPIHT and QIM, are determined as most adequate algorithms for proposed system after several evaluations. The experimental results show a high quality of the watermarked as well as the recovered images, obtaining average Peak Signals to Noise Ratios (PSNR) of more than 40 and 38 dB, respectively.



















Similar content being viewed by others
References
Chen M, Sun X (2010) A digital image watermarking of self-recovery based on the SPIHT algorithm. Int Conf Signal Process Syst 2:621–624
Chen B, Wornell GW (2001) Quantization Index Modulation: a class of provably good method for digital watermarking and information embedding. IEEE Trans Inf Theory 47:1423–1443
Crow F (1984) Summed-area tables for texture mapping. Proc SIGGRAPH 18:207–212
Cruz C, Reyes R, Nakano M, Perez H (2010) Semi-fragile watermarking based content image authentication scheme (Spanish). Rev Fac Ing 56:160–169
Hartung F, Ramme F (2000) Digital rights management and watermarking of multimedia content for m-commerce applications. IEEE Commun Mag 38(11):78–84
Jain V, Learned-Miller E (2010) FDDB: a benchmark for face detection in unconstrained setting, Technical Report UM-CS-2010-009, Dept. of Computer science, Univ. of Massachusetts, Amherst
Kanamori T, Takenouchi T, Mutara N (2007) Tutorial series en brain-inspired computing part 6: geometrical structuring of boosting algorithm. N Gener Comput 25(1):117–141
Kaur R, Kaushal N (2010) Comparative analysis of various compression methods for medical images. Poc ISCET 101:137–142
Lee T, Lin S (2008) Dual watermark for image tamper detection and recovery. Pattern Recogn 41:3497–3506
Lenarczyk P, Piotrowski Z (2013) Parallel blind digital image watermarking in spatial and frequency domain. Telecommun Syst Model Anal Des Manag. doi:10.1007/s11235-013-9734-x
Lian S, Chen X (2012) Lightweight secure multimedia distribution based on homomorphic operations. Telecommun Syst 49(2):187–197
Lin S, Lin J, Chen C (2011) A ROI-based semi-fragile watermarking for image tamper detection and recovery. Int J Innov Comput Inf Contr 7(12):6875–6888
Luo H, Chu S, Lu Z (2008) Self embedding watermarking using halftoning technique. Circ Syst Sig Process 27:155–170
Phadikar A, Maity A, Mandal M (2012) Novel wavelet-based QIM data hiding technique for tamper detection and correction of digital images. J Vis Commun Image Represent 23:608–613
Rosales L, Cedillo M, Nakano M, Perez M, Kurkoski B (2013) Watermarking-based image authentication with recovery capability using halftoning technique. Signal Process Image Commun 28:69–83
Said A, Pearlman W (1996) A new, fast and efficient image codec based on set partitioning in hierarchical trees. IEEE Trans Circ Syst Video Technol 6(3):243–250
Sang J, Zhang B, Hung D, Xiang H, Xu H, Sang N (2013) Performance analysis on a watermarking method based on double random phase encoding technique. Optik–Int J Light Electron Optics 124(24):6512–6515
Viola P, Jones M (2001) Rapid object detection using a boosting cascade of simple features. IEEE CVPR 1:511–518
Viola P, Jones M (2004) Robust real-time face detection. Int J Comput Vis 57(2):137–154
Wang J, Lian S, Wang J (2013) Hybrid additive multi-watermarking and decoding. Multimedia Systems. doi:10.1007/s00530-013-0338-9
Yang H, Yin J (2013) A secure removable visible watermarking for BTC compressed images. Multimed Tools Appl. doi:10.1007/s11042-013-1714-3
Zhang X, Qjan Z, Ren Y, Feng G (2011) Watermarking with flexible self-recovery quality based on compressive sensing and compositive reconstruction. IEEE Trans Inf Forensic Secur 6(4):1223–1232
Zhang C, Zhang Z (2010) Boosting-based face detection and adaptation. Morgan & Claypool Publishers, San Francisco
Acknowledgments
Authors thank the National Council of Science and Technology of Mexico (CONACyT) and IPN for financial support to carry out this work.
Author information
Authors and Affiliations
Corresponding author
Rights and permissions
About this article
Cite this article
Cruz-Ramos, C., Nakano-Miyatake, M., Perez-Meana, H. et al. Face region authentication and recovery system based on SPIHT and watermarking. Multimed Tools Appl 74, 7685–7709 (2015). https://doi.org/10.1007/s11042-014-2006-2
Received:
Revised:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11042-014-2006-2