Abstract
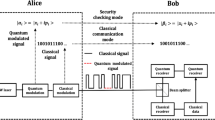
In order to enhance the transmission security in quantum communications via coherent states, we propose a quantum optical firewall device to protect a quantum cryptosystem against eavesdropping through optical attack strategies. Similar to the classical model of the firewall, the proposed device gives legitimate users the possibility of filtering, controlling (input/output states) and making a decision (access or deny) concerning the traveling states. To prove the security and efficiency of the suggested optical firewall, we analyze its performances against the family of intercept and resend attacks, especially against one of the most prominent attack schemes known as “Faked State Attack.”







Similar content being viewed by others
References
Dirac, P.A.M.: The Principles of Quantum Mechanics, 3rd edn. Clarendon Press, Oxford (1947)
Wootters, W.K., Zurek, W.H.: A single quantum cannot be cloned. Nature 299, 802–803 (1982). doi:10.1038/299802a0
Dieks, D.: Communication by EPR devices. Phys. Lett. A 92(6), 271–272 (1982)
Linares, L.-A., Kurtsiefer, C.: Breaking a quantum key distribution system through a timing side channel. Opt. Express 15, 9388–9393 (2007)
Nauerth, S., Fürst, M., Schmitt-Manderbach, T., Weier, H., Weinfurter, H.: Information leakage via side channels in freespace BB84 quantum cryptography. New J. Phys. 11, 065001 (2009)
Lütkenhaus, N.: Security against individual attacks for realistic quantum key distribution. Phys. Rev. A 61, 052304 (2000)
Hwang, W.Y.: Quantum key distribution with high loss: toward global secure communication. Phys. Rev. Lett. 91, 057901 (2003)
Scarani, V., Acin, A., Ribordy, G., Gisin, N.: Quantum cryptography protocols robust against photon number splitting attacks for weak laser pulse implementations. Phys. Rev. Lett. 92, 057901 (2004)
Qi, B., Fung, C.-H.F., Lo, H.-K., Ma, X.: Time-shift attack in practical quantum cryptosystems. Quant. Inf. Comp. 7, 73,2 (2007)
Makarov, V., Hjelme, D.R.: Faked states attack on quantum cryptosystems. J. Mod. Opt. 52, 691–705 (2005)
Makarov, V., Anisimov, A., Skaar, J.: Effects of detector efficiency mismatch on security of quantum cryptosystems. Phys. Rev. A 74, 022313 (2006)
Makarov, V.: Controlling passively quenched single photon detectors by bright light. New J. Phys. 11, 065003 (2009)
Zhao, Y., Fung, C.-H.F., Qi, B., Chen, C., Lo, H.-K.: Quantum hacking: experimental demonstration of time-shift attack against practical quantum-key- distribution systems. Phys. Rev. A 78, 042333 (2008)
Liu, A.X., Gouda, M.G.: Diverse firewall design. Parallel Distrib. Syst. IEEE Trans. 19(9), 1237–1251 (2008). doi:10.1109/TPDS.2007.70802
Jou, Y.F., Gong, F., Sargor, C., Wu, X.: Design and implementation of a scalable intrusion detection system for the protection of network infrastructure. DARPA Information Survivability Conference and Exposition, 2000. DISCEX ’00. Proceedings (IEEE Transactions), 2, 69–83 (2000). doi:10.1109/DISCEX.2000.821510
Kollmitzer, C., Pivk, M. (eds.): Applied Quantum Cryptography, Lecture Notes in Physics, vol. 797. Springer, Berlin, Heidelberg (2010)
Bennett, C.H., Brassard, G.: Quantum cryptography: public key distribution and coin tossing. In: Proceedings of IEEE International Conference on Computers, Systems and Signal Processing, Bangalore, India, pp. 175–179. IEEE, New York (1984)
Bennett, C.H., Brassard, G., Mermin, N.D.: Quantum cryptography without Bell’s theorem. Phys. Rev. Lett. 68(5), 557–559 (1992)
Shor, P.W., Preskill, J.: Simple proof of security of the BB84 quantum key distribution protocol. Phys. Rev. Lett. 85, 441 (2000)
Lo, H.L., Preskill, J.: Security of quantum key distribution using weak coherent states with nonrandom phases. Quant. Inf. Comp. 7, 431, 58 (2007)
Andersson, E., Curty, M., Jex, I.: Experimentally realizable quantum comparison of coherent states and its applications. Phys. Rev. A 74, 022304 (2007). 2006
Ivanovic, I.D.: Phys. Lett. A 123, 257 (1987)
El Allati, A., El Baz, M.: Opt. Quant. Electron. doi:10.1007/s11082-014-9959-2
Allati, A., Hassouni, Y., Metwally, N.: Phys. Scr. 83, 065002 (2011)
Meslouhi, A., Amellal, H., Hassouni, Y., El Allati, A.: J. Russian Laser Res. doi:10.1007/s10946-014-9438-z
Allati, A., Baz, M., Hassouni, Y.: Quant. Inf. Process. 10, 589 (2011)
Author information
Authors and Affiliations
Corresponding author
Rights and permissions
About this article
Cite this article
Amellal, H., Meslouhi, A., Hassouni, Y. et al. A quantum optical firewall based on simple quantum devices. Quantum Inf Process 14, 2617–2633 (2015). https://doi.org/10.1007/s11128-015-1002-4
Received:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11128-015-1002-4