Abstract
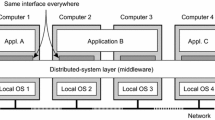
Taking into account the intrinsic heterogeneity of communication latency of grid environments, we propose in this article a composition approach that enables to build mutual exclusion services for grids. By using our approach, different intra and inter cluster token-based mutual exclusion algorithms can be combined easily. Performance evaluation tests were conducted on the French national grid testbed called Grid’5000, whose results show that our approach is effective and that the choice of the most suitable inter cluster algorithm depends on the behavior of the application.
Similar content being viewed by others
References
Antoniu G, Bouge L, Lacour S (2003) Making a DSM consistency protocol hierarchy-aware: an efficient synchronization scheme. In: Proceedings of the workshop on distributed shared memory on clusters, May 2003, pp 516–521
Arantes L, Sens P, Folliot B (2002) An effective logical cache for a clustered LRC-based DSM system. Clust Comput 5(1):19–31
Bertier M, Arantes L, Sens P (2006) Distributed mutual exclusion algorithms for grid applications: a hierarchical approach. J Parallel Distrib Comput 66:128–144
Cappello F, Desprez F, Dayde M, Jeannot E, Jegou Y, Lanteri S, Melab N, Namyst R, Vicat-Blanc Primet P, Richard O, Caron E, Leduc J, Mornet G (2006) Grid5000: a nation wide experimental grid testbed. High Perform Comput Appl 20(4):481–494
Chang I, Singhal M, Liu M (1990) A hybrid approach to mutual exclusion for distributed system. In: IEEE international computer software and applications conference, 1990, pp 289–294
Erciyes K (2004) Distributed mutual exclusion algorithms on a ring of clusters. In: International conference on computational science and its applications. LNCS, vol 3045, pp 518–527
Housni A, Tréhel M (2001) Distributed mutual exclusion by groups based on token and permission. In: International conference on computational science and its applications, June 2001, pp 26– 29
Lamport L (1978) Time, clocks, and the ordering of events in a distributed system. CACM 21(7):558–564
Madhuram X, Kumar X (1994) A hybrid approach for mutual exclusion in distributed computing systems. In: IEEE symposium on parallel and distributed processing, 1994
Maekawa M (1985) A \(\sqrt{N}\) algorithm for mutual exclusion in decentralized systems. ACM Trans Comput Syst 3(2):145–159
Martin AJ (1985) Distributed mutual exclusion on a ring of processes. Sci Comput Program 5(3):265–276
Mueller F (1998) Prioritized token-based mutual exclusion for distributed systems. In: International parallel processing symposium, March 1998, pp 791–795
Naimi M, Trehel M, Arnold A (1996) A log (N) distributed mutual exclusion algorithm based on path reversal. J Parallel Distributed Comput 34(1):1–13
Omara F, Nabil M (2002) A new hybrid algorithm for the mutual exclusion problem in the distributed systems. Int J Intell Comput Inf Sci 2(2):94–105
Raymond K (1989) A tree-based algorithm for distributed mutual exclusion. ACM Trans Comput Syst 7(1):61–77
Ricart G, Agrawala A (1981) An optimal algorithm for mutual exclusion in computer networks. Commun ACM, 24, 1981
Rizzo L (1997) Dummynet: a simple approach to the evaluation of network protocols. ACM Comput Commun Rev 27(1):31–41
Singhal M (1992) A dynamic information structure for mutual exclusion algorithm for distributed systems. IEEE Trans Parallel Distrib Syst 3(1):121–125
Sopena J, Arantes L, Legond F, Sens P (2008) The impact of clustering on token-based mutual exclusion algorithms. In: Euro-Par 2008 processing, Las Palmas, Spain. Springer, Berlin
Sopena J, Legond F, Arantes L, Sens P (2007) A composition approach to mutual exclusion algorithms for grid applications. In: The 36th international conference on parallel processing, September 2007, pp 65–75
Suzuki I, Kasami T (1985) A distributed mutual exclusion algorithm. ACM Trans Comput Syst 3(4):344–349
Author information
Authors and Affiliations
Corresponding author
Rights and permissions
About this article
Cite this article
Sopena, J., Arantes, L., Legond-Aubry, F. et al. Building effective mutual exclusion services for grids. J Supercomput 49, 84–107 (2009). https://doi.org/10.1007/s11227-008-0235-8
Received:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11227-008-0235-8