Abstract
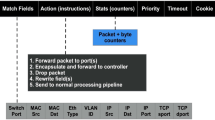
Provider-provisioned virtual private networks are nowadays well-established networking concepts. They are envisaged as an extension of the basic VPN concept to securely network low-capacity nodes in large-scale personal networks, with the help of network providers. This article presents an adaptation of the Internet Key Exchange (IKEv2) protocol to the context of dynamic tunneling in personal networks. It relies on the providers’ infrastructure to build identity-based security associations. Results of a preliminary security analysis are also provided.
Similar content being viewed by others
References
IST-MAGNET deliverable D4.3.3. Implementation and evaluation of the network-level security architecture.
Kent, S., & Seo, K. (2005). Security architecture for the Internet protocol (RFC 4301).
Kaufman (Ed.). (2005). Internet key exchange (IKEv2) protocol (RFC 4306).
Louati, W., & Zeghlache, D. (2005). Network-based virtual personal overlay networks using programmable virtual routers. IEEE Communications Magazine, 43(8), 86–94.
Semeria, C. (2001). RFC 2547bis: BGP/MPLS VPN fundamentals. Juniper Networks, White paper 200012-001, March 2001.
Hussain, M., Hajjeh, I., Afifi, H., & Seret, D. Extending IKEv2 for multi-vendor home network environment. In proceedings of the 7th international conference on advanced communication technology, ICACT 2005, 21–23 Feb. 2005 (Vol. 1, pp. 63–68).
Schiller, J. (2005). Cryptographic algorithms for use in the Internet key exchange version 2 (IKEv2) (RFC 4307).
Harkins, D., Kaufman, C., Kivinen, T., Kent, S., & Perlman, R. (2002). Design rationale for IKEv2 (Internet draft), available from http://tools.ietf.org/html/draft-ietf-ipsec-ikev2-rationale-00.txt, expired Aug. 2002.
Eronen, P., & Hoffman, P. (2006). IKEv2 clarifications and implementation guidelines. Internet informational RFC 4718, October 2006.
Paterson, K. G. (2006). A cryptographic tour of the IPsec standards (Information Security Technical Report) (Vol. 11(2), pp. 72-81).
McCullagh, N., & Barreto, P. S. L. M. (2005). A new two-party identity-based authenticated key agreement. In Cryptographers’ track at RSA conference—CT-RSA 2005 track, San Francisco, USA, February 14–18, 2005.
Menezes (1993). Elliptic curve public key cryptosystems. Dordrecht: Kluwer Academic.
Gehrmann, Mitchell, C., & Nyberg, K. (2004). Manual authentication for wireless devices. RSA Cryptobytes, 7, 29–37.
Zhang, F., Safavi-Naini, R., & Susilo, W. (2004). An efficient signature scheme from bilinear pairings and its applications. In Lecture notes in computer science. International workshop on practice and theory in public key cryptography—PKC’2004 (pp. 277–290). New York: Springer.
Chen, L., & Kudla, C. (2003). Identity based authenticated key agreement from pairings. In Proceedings of the IEEE computer security foundations workshop (pp. 219–233).
Smart, P. (2002). An identity based authenticated key agreement protocol based on the Weil pairing. Electronics Letters, 38, 630–632.
Scott, M. (2002). Authenticated ID-based key exchange and remote log-in with insecure token and PIN number (Cryptology ePrint Archive, Report 2002/164). Available at http://eprint.iacr.org/2002/164/.
Hussain, M., Masmoudi, K., Afifi, H., & Seret, D. (2005). Trust sharing using IKEv2 in multi-vendor home networks. In Proceedings of sécurité des architectures et réseaux (SAR) 2005. Batz-sur-Mer, France, June 2005.
Niemegeers, I. G., & Heemstra de Groot, S. M. (2005). FEDNETS: Context-aware ad-hoc network federations. Wireless Personal Communications, 33(3–4), 305–318.
Author information
Authors and Affiliations
Corresponding author
Rights and permissions
About this article
Cite this article
Masmoudi, K., Afifi, H. Building identity-based security associations for provider-provisioned virtual private networks. Telecommun Syst 39, 215–222 (2008). https://doi.org/10.1007/s11235-008-9123-z
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11235-008-9123-z