Abstract
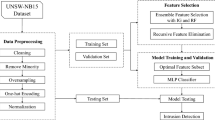
This paper introduces an approach to anomaly-based intrusion detection, which searches the system activity data for deviations from preliminarily described profiles of normal activity. The normal system activity in the proposed methodology is described using data mining techniques, namely classification trees. The intrusion detection is performed using some similarity coefficients with a purpose to measure the similarity between the normal activity and the current one. The evaluation of the represented simulation results indicates the proposed methodology produces reliable and steady results.
Similar content being viewed by others
References
Anderberg, M. (1973). Cluster analysis for applications. New York: Academic Press.
Ashby, F. G., & Perrin, N. A. (1988). Toward a unified theory of similarity and recognition. Psychological Review, 95, 124–150.
Baldi, P., Brunak, S., Chauvin, Y., Andersen, C. A., & Nielsen, H. (2000). Assessing the accuracy of prediction algorithms for classification: An overview. Bioinformatics, 16, 412–424.
Brieman, L., Friedman, J. H., Olshen, R. A., & Stone, C. J. (1984). Classification and regression trees. Belmont: Wadsworth International Group.
Chen, R. C., Cheng, K. F., & Hsieh, C. C. (2008). Using Fuzzy Neural Networks and rule heuristics for anomaly intrusion detection on database connection. In Proceedings of international conference on machine learning and cybernetics (Vol. 6, pp. 3607–3612).
Dal, D., Abraham, S., Abraham, A., Sanyal, S., & Sanglikar, M. (2008). Evolution induced secondary immunity: An artificial immune system based intrusion detection system. In Proceedings of 7th computer information systems and industrial management applications (pp. 65–70).
Ferri, C., Lachinche, N., Macskassy, S. A., & Rakotomamonjy, A. (Eds.) (2005). Second Workshop on ROC Analysis in ML.
Forrest, S., Hofmeyr, S. A., Somayaji, A., & Longtaff, T. A. (1996). A sense of self for unix processes. In Proceedings of the 1996 IEEE symposium on security and privacy (pp. 120–128). Los Alamitos: IEEE Computer Society Press.
Forrest, S., Hofmeyr, S. A., & Somayaji, A. (1998). Intrusion detection using sequences of system calls. Journal of Computer Security, 6, 151–180.
Guo, G.-D., Jain, A. K., Ma, W.-Y., & Zhang, H.-J. (2002). Learning similarity measure for natural image retrieval with relevance feedback. IEEE Transactions on Neural Networks, 13, 811–820.
Huang, B., Li, W., Chen, D., & Shi, L. (2009). An intrusion detection method based on outlier ensemble detection. In Proceedings of international conference on networks security wireless communications and trusted computing (Vol. 2, pp. 600–603).
Jiang, Z., Luosheng, W., Yong, F., & Xiao, Y. C. (2008). Intrusion detection based on density level sets estimation. In Proceedings of international conference on networking, architecture, and storage (pp. 173–174).
Kemmerer, R. A., & Vigna, G. (2002). Intrusion detection: a brief history and overview. Computer, 35(4), 27–30.
Kokotos, D. X., & Smirlis, Y. G. (2005). A classification tree application to predict total ship loss. Journal of Transportation and Statistics, 8(2), 31–42.
Kruegel, C., Vigna, G., & Robertson, W. (2005). A multi-model approach to the detection of web-based attacks. Computer Networks, 48(5), 717–738.
Lauria, E. J. M., & Tayi, G. K. (2008). Statistical machine learning for network intrusion detection: a data quality perspective. International Journal of Services Sciences, 1(2), 179–195.
Liao, Y., Vemuri, V. R., & Pasos, A. (2007). Adaptive anomaly detection with evolving connectionist systems. Journal of Network and Computer Applications, 30(1), 60–80.
Liu, Y., Cai, J., Huang, Z., Yu, J., & Yin, J. (2007). Fast detection of database system abuse behaviors based on data mining approach. In ACM international conference proceeding series: Vol. 304. Proceedings of the 2nd international conference on scalable information systems: InfoScale ’07 (pp. 1–7).
Masri, W., & Podgurski, A. (2008). Application-based anomaly intrusion detection with dynamic information flow analysis. Computers & Security, 27(5–6), 176–187.
Matthews, B. W. (1975). Comparison of the predicted and observed secondary structure of T4 phage lysozyme. Biochimica Biophysica Acta, 405, 442–451.
M’e, L., Michel, C. (2001). Intrusion detection: A bibliography (Technical Report No. SSIR-2001-01).
Prasad, G., Dhanalakshmi, Y., & Kumar, V. (2008). Modeling an intrusion detection system using data mining and genetic algorithms based on fuzzy logic. IJCSNS International Journal of Computer Science and Network Security, 8(7), 319–325.
Prashanth, G., Prashanth, V., Jayashree, P., & Srinivasan, N. (2008). Using random forests for network-based anomaly detection at active routers. In Proceedings of international conference on signal processing communications and networking, ICSCN ’08 (pp. 93–96).
Rieck, K., & Laskov, P. (2008). Linear-time computation of similarity measures for sequential data. The Journal of Machine Learning Research, 9, 23–48.
Rieck, K., Laskov, P., & Sonnenburg, S. (2007). Computation of similarity measures for sequential data using generalized suffix trees. In Advances in neural information processing systems 19 (pp. 1177–1184). Cambridge: MIT Press.
Saniee Abadeh, M., Habibi, J., Barzegar, Z., & Sergi, M. (2007). A parallel genetic local search algorithm for intrusion detection in computer networks. Engineering Applications of Artificial Intelligence, 20(8), 1058–1069.
Tan, K., Killourhy, K., & Maxion, R. (2002). Undermining an anomaly-based intrusion detection system using common exploits. In LNCS: Vol. 2516. Proceedings of 5th international symposium on recent advances in intrusion detection (RAID 2002) (pp. 54–73).
Tian, D., Liu, Y., & Li, B. (2007). A distributed hebb neural network for network anomaly detection. In Lecture notes in computer science: Vol. 4742. Parallel and distributed processing and applications (pp. 314–325). (Including subseries Lecture Notes in Artificial Intelligence and Lecture Notes in Bioinformatics).
University of New Mexico’s Computer Immune Systems Project, http://www.cs.unm.edu/~immsec/systemcalls.htm. Accessed 14 August 2009.
Webb, A. (2002). Statistical pattern recognition. New York: Wiley.
Yao, L., & Yao, K. (2007). A low complexity intrusion detection algorithm. In LNCS: Vol. 4489. Computational science–ICCS 2007 (pp. 461–464).
Author information
Authors and Affiliations
Corresponding author
Rights and permissions
About this article
Cite this article
Nikolova, E., Jecheva, V. Some similarity coefficients and application of data mining techniques to the anomaly-based IDS. Telecommun Syst 50, 127–135 (2012). https://doi.org/10.1007/s11235-010-9390-3
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11235-010-9390-3