Abstract
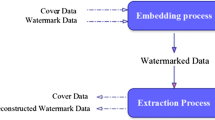
Many steganography schemes seek to improve the transmission of important and sensitive information through insecure channels. Audio steganography exploits audio files to transfer that information over public communication channels. This paper proposes a new audio steganography scheme to secure transmission of speech messages using contourlet transform and duffing oscillator. Improvement in the security, hiding capacity, and maintenance of the transparency of the audio signals are contributed by this scheme. Contourlet transform produces a wider spread data coefficient than its input samples. Secret speech samples are hidden into some of these coefficients. The duffing oscillator is used to scramble the cover samples before embedding secret speech and then it is exploited to give the embedding process more immunization against piracy. So, the enhancement in the security level is paralleled with the employing of a duffing oscillator in the proposed scheme. The performance results of the proposed scheme indicate that high hiding capacity up to 80% from the size of covered audio can be achieved and it is corresponding to good quality, secure and transparency for both transmitted audio and retrieved secret speech.









Similar content being viewed by others
References
Wu, J., Chen, B., Luo, W., & Fang, Y. (2020). Audio steganography based on iterative adversarial attacks against convolutional neural networks. IEEE Transactions on Information Forensics and Security, 15, 2282–2294
Alsabhany, A. A., Mohd Ridzuan, F. H., & Ab Halim, A. H. (2018). An adaptive multi amplitude thresholds embedding algorithm for audio steganography. Malaysian Journal of Science, Health & Technology. https://doi.org/10.33102/mjosht.v2i.43
Gong, C., Zhang, J., Yang, Y., Yi, X., Zhao, X., & Ma, Y. (2020). Detecting fingerprints of audio steganography software. Forensic Science International: Reports, 2, 100075
Rahim, L. B. A., Bhattacharjee, S., & Aziz, I. B. (2014). An audio steganography technique to maximize data hiding capacity along with least modification of host. In Proceedings of the first international conference on advanced data and information engineering (DaEng-2013) (pp. 277–289). Springer, Singapore.
Sakthisudhan, K., Prabhu, P., Thangaraj, P., & Marimuthu, C. M. (2012). Dual steganography approach for secure data communication. Procedia Engineering, 38, 412–417
Alwahbani, S. M., & Elshoush, H. T. (2016). Chaos-Based Audio Steganography and Cryptography Using LSB Method and One-Time Pad. In Proceedings of sai intelligent systems conference (pp. 755–768). Springer, Cham.
Mohajon, J., Ahammed, Z., & Talukder, K. H. (2018). An improved approach in audio steganography using genetic algorithm with K-Bit symmetric security key. In 2018 21st International conference of computer and information technology (ICCIT) (pp. 1–6). IEEE.
Alsabhany, A. A., Ridzuan, F., & Azni, A. H. (2019). The adaptive multi-level phase coding method in audio steganography. IEEE Access, 7, 129291–129306
Elkandoz, M. T., & Alexan, W. (2019). Logistic Tan Map Based Audio Steganography. In 2019 international conference on electrical and computing technologies and applications (ICECTA) (pp. 1–5). IEEE.
Balgurgi, P. P., & Jagtap, S. K. (2013). Audio steganography used for secure data transmission. In Proceedings of international conference on advances in computing (pp. 699–706). Springer, New Delhi.
Anwar, M., Sarosa, M., & Rohadi, E. (2019). Audio steganography using lifting wavelet transform and dynamic key. In 2019 international conference of artificial intelligence and information technology (ICAIIT) (pp. 133–137). IEEE.
El-Khamy, S. E., Korany, N. O., & El-Sherif, M. H. (2017). A security enhanced robust audio steganography algorithm for image hiding using sample comparison in discrete wavelet transform domain and RSA encryption. Multimedia Tools and Applications, 76(22), 24091–24106
El-Khamy, S. E., Korany, N., & El-Sherif, M. H. (2017). Robust image hiding in audio based on integer wavelet transform and Chaotic maps hopping. In 2017 34th national radio science conference (NRSC) (pp. 205–212). IEEE.
Shirali-Shahreza, S., & Manzuri-Shalmani, M. T. (2008). High capacity error free wavelet domain speech steganography. In 2008 IEEE international conference on acoustics, speech and signal processing (pp. 1729–1732). IEEE.
Do, M. N., & Vetterli, M. (2005). The contourlet transform: an efficient directional multiresolution image representation. IEEE Transactions on Image Processing, 14(12), 2091–2106
Selvi, G. U. V., & Nadarajan, R. (2012). Coronary angiogram video compression using wavelet-based contourlet transform and region-of-interest technique. IET Image Processing, 6(8), 1049–1056
Lyu, Z., Zhang, C., & Han, M. (2020). A nonsubsampled countourlet transform based CNN for real image denoising. Signal Processing: Image Communication, 82, 115727
Jin, R., Yin, J., Zhou, W., & Yang, J. (2016). Improved multiscale edge detection method for polarimetric SAR images. IEEE Geoscience and Remote Sensing Letters, 13(8), 1104–1108
Subhedar, M. S., & Mankar, V. H. (2019). Image steganography using contourlet transform and matrix decomposition techniques. Multimedia Tools and Applications, 78(15), 22155–22181
Nam, S. H., Mun, S. M., Ahn, W., Kim, D., Yu, I. J., Kim, W. H., & Lee, H. K. (2020). NSCT-Based robust and perceptual watermarking for DIBR 3D images. IEEE Access, 8, 93760–93781
Do, M. N., & Vetterli, M. (2003). Framing pyramids. IEEE Transactions on Signal Processing, 51(9), 2329–2342
Yang, G., Lu, Z., Yang, J., & Wang, Y. (2019). An adaptive contourlet HMM–PCNN model of sparse representation for image denoising. IEEE Access, 7, 88243–88253
Rabizadeh, M., Amirmazlaghani, M., & Ahmadian-Attari, M. (2016). A new detector for contourlet domain multiplicative image watermarking using Bessel K form distribution. Journal of Visual Communication and Image Representation, 40, 324–334
Li, C., Luo, G., & Li, C. (2018). A parallel image encryption algorithm based on chaotic Duffing oscillators. Multimedia Tools and Applications, 77(15), 19193–19208
Chang, T. P. (2017). Chaotic motion in forced Duffing system subject to linear and nonlinear damping. Mathematical Problems in Engineering, 2017(1), 8
Sheela, S. J., Suresh, K. V., & Tandur, D. (2017). A novel audio cryptosystem using chaotic maps and DNA encoding. Journal of Computer Networks and Communications, 2017(1), 12
Roy, S., & Kapoor, V. (2020). High Data Rate Audio Steganography. In International conference on innovative computing and communications (pp. 503–515). springer, Singapore.
Chai, X., Gan, Z., Yuan, K., Chen, Y., & Liu, X. (2019). A novel image encryption scheme based on DNA sequence operations and chaotic systems. Neural Computing and Applications, 31(1), 219–237
Hua, Z., & Zhou, Y. (2017). Design of image cipher using block-based scrambling and image filtering. Information Sciences, 396, 97–113
Farsana, F. J., & Gopakumar, K. (2020). Speech encryption algorithm based on nonorthogonal quantum state with hyperchaotic keystreams. Advances in Mathematical Physics, 2020(1), 12
Tayel, M., Gamal, A., & Shawky, H. (2016). A proposed implementation method of an audio steganography technique. In 2016 18th international conference on advanced communication technology (ICACT) (pp. 180–184). IEEE.
Funding
Not Applicable.
Author information
Authors and Affiliations
Corresponding author
Ethics declarations
Conflict of interest
The Authors declare that they do not have any conflict of interest.
Additional information
Publisher's Note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Rights and permissions
About this article
Cite this article
Hameed, A.S. A High Secure Speech Transmission Using Audio Steganography and Duffing Oscillator. Wireless Pers Commun 120, 499–513 (2021). https://doi.org/10.1007/s11277-021-08470-8
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11277-021-08470-8