Abstract
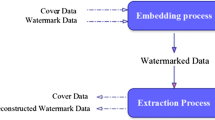
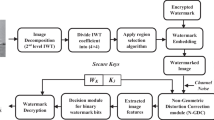
In this paper, we propose a secure semi-fragile watermarking technique based on integer wavelet transform with a choice of two watermarks to be embedded. A self-recovering algorithm is employed, that hides the image digest into some wavelet subbands for detecting possible illicit object manipulation undergone in the image. The semi-fragility makes the scheme tolerant against JPEG lossy compression with the quality factor as low as 70%, and locates the tampered area accurately. In addition, the system ensures more security because the embedded watermarks are protected with private keys. The computational complexity is reduced by using parameterized integer wavelet transform. Experimental results show that the proposed scheme guarantees safety of a watermark, recovery of image and localization of tampered area.
Similar content being viewed by others
References
Alessandro Piva, Franco Bartolini, Roberto Caldelliy. Self-recovery authentication of images in the DWT domain. International Journal of Image and Graphics, 2005, 5(1): 149–166.
Fei C, Kundur D, Kwong R H. Analysis and design of secure watermark-based authentication systems. IEEE Transactions on Information Forensics and Security, 2006, 1(1): 43–55.
Ingemar J Cox, Gwenaë Doërr, Teddy Furon. Watermarking is not cryptography. LNCS 4283, Springer, 2006, pp.1–15.
Fei C, Kundur D, Kwong R H. Achieving computational and unconditional security in authentication watermarking: Analysis, insights, and algorithm. In Proc. SPIE: Security and Watermarking of Multimedia Contents VII, Vol. 5681, San Jose, California, 2005, pp.697–708.
Luis Perez-Freire, Pedro Comesana, Juan Ramon Troncoso-Pastoriza, Fernando Perez-Gonzalez. Watermarking security: A survey. Transactions on Data Hiding and Multimedia Security 1, 4300, 2006, pp.41–72.
Hartung F, Kutter M. Multimedia watermarking techniques. In Proc. IEEE, USA, 1999, 87(7): 1079–1107.
Friedman G L. The trustworthy digital camera: Restoring credibility to the photographic image. IEEE Transaction on Consumer Electronics, Rosemont, IL, USA, 1993, 39(4): 905–910.
Xiang Zhou, Xiaohui Duan, Daoxian Wang. A semi-fragile watermark scheme for image authentication. In Proc. IEEE, 10th International Multimedia Modeling Conference (MMM’04), Brisbane, Australia, 2004, pp.374–377.
Hua Fiun, Xiuo-Ping Zhang. Fragile watermark based on the Gaussian mixture model in the wavelet domain for image authentication. IEEE International Conference on Image Processing, Barcelona, Spain, Vol. 1, 2003, pp.505–508.
Kurato Maeno, Qibin Sun, Shih-Fu Chang, Masayuki Suto. New semi-fragile image authentication watermarking techniques using random bias and non-uniform quantization. IEEE Transactions on Multimedia, 2006, 8(1): 32–45.
Xiaoyun Wu, Junquan Hu, Zhixiong Gu, Jiwu Huang. A secure semi-fragile watermarking for image authentication based on integer wavelet transform with parameters. In Proc. the Australasian Workshop on Grid Computing and E-Research, Newcastle, New South Wales, Australia, Vol. 44, 2005, pp.75–80.
Ching-Yang Lin, Shi Fu-Chang. Semi-fragile watermarking for authenticating JPEG visual content. SPIE Security and Watermarking of Multimedia Contents II, Vol. 3971, 2000, pp.140–151.
Liu H M, Liu J F, Huang J W, Huang D R, Shi Y Q. A robust DWT-based blind data hiding algorithm. In Proc. IEEE on Circuits and Systems, Phoenix-Scottsdale, AZ, USA, Vol. 2, 2002, pp.672–675.
Dima Pröfrock, Mathias Schlauweg, Erika Müller Richard Wagner. A new uncompressed-domain video watermarking approach robust to h.264/AVC compression. In Proc. the 24th IASTED International Conference on Signal Processing, Pattern Recognition, and Applications, Innsburk, Austria, 2006, pp.99–104.
http://www.math.cuhk.edu.hk/–rchan/paper/impulse/de-finitions.html
Meerwald, Uhl A. Watermark security via wavelet filter parameterization. In Proc. IEEE International Conference on Image Processing, Thessaloniki, Greece, Vol. 3, 2001, pp.1027–1030.
Khan A. A novel approach to decoding: Exploiting anticipated attack information using genetic programming. International Journal of Knowledge-Based Intelligent Engineering Systems, 2006, 10(5): 337–347.
A Khan, Anwar M Mirza, A Majid. Intelligent perceptual shaping of a digital watermark: Exploiting characteristics of human visual system. International Journal of Knowledge-Based Intelligent Engineering Systems, 2006, 10(3): 213–223.
A Khan, Anwar M Mirza. Genetic perceptual shaping: Utilizing cover image and conceivable attack information using genetic programming. Information Fusion, Elsevier Science, 2007, 8(4): 354–365.
Author information
Authors and Affiliations
Corresponding author
Additional information
This work was supported by the Higher Education Commission of the Government of Pakistan under the Indigenous Ph.D. Scholarship Program (Grant No. 17- 5-I (Cu - 180) HEC/Sch/2004/4343).
Rights and permissions
About this article
Cite this article
Chamlawi, R., Khan, A. & Idris, A. Wavelet Based Image Authentication and Recovery. J. Comput. Sci. Technol. 22, 795–804 (2007). https://doi.org/10.1007/s11390-007-9103-x
Received:
Revised:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11390-007-9103-x