Abstract
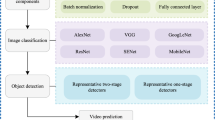
With the increasing availability of internet access, the number of malware is growing dramatically. So, defence against malware is an important issue in the security of computers and networks. Hence, malware detection systems are important. The most common method for malware detection is a signature-based technique. Nowadays, malware attempt to deceive all kinds of anti-malware, using obfuscation mechanisms and polymorphic behaviours, thus this method is not able to detect such malware and is not very effective. One way to deal with these types of malware is through dynamic malware analysis that requires executing the malware and monitoring its behaviour. In this paper, a novel dynamic malware detection method is presented which utilizes hardware events during file execution such as hardware port status, CPU internal status, main memory status, etc., as features of the classification model. Then, two Deep Neural Network (DNN) based algorithms, Convolutional Neural Network (CNN) and Long Short-Term Memory (LSTM), are used to construct the machine learning model. Finally, the voting network is used between the outputs of CNNs and the LSTM network, and the label of the suspicious sample is determined. The results show that the combination of hardware events as feature inputs, with LSTM and voting network can be effective in detecting new malware.









Similar content being viewed by others
References
Nash, T.: An Undirected Attack Against Critical Infrastructure. 1.2, 1–10 (2005)
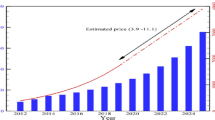
The AV-Test Institute. current malware statistics. https://www.av-test.org/en/statistics/malware (2019), Accessed 22 Jan 2020
Idika, N., Mathur, A.P.: A Survey of Malware Detection Techniques. SERC Tech, Reports (2007)
Farrokhmanesh, M., Hamzeh, A.: Music classification as a new approach for malware detection. J. Comput. Virol. Hacking Tech. 15, 77–96 (2019)
Rhode, M., Burnap, P., Jones, K.: Early-stage malware prediction using recurrent neural networks. Comput. Secur. 77, 578–594 (2018)
Saleh, M., Li, T., Xu, S.: Multi-context features for detecting malicious programs. J. Comput. Virol. Hacking Tech. 14, 181–193 (2018)
Bazrafshan, Z., Hashemi, H., Fard, S.M.H., Hamzeh, A.: A survey on heuristic malware detection techniques. In: IKT 2013–2013 5th Conference on Information and Knowledge Technology, pp. 113–120 (2013)
Das, S., Xiao, H., Liu, Y., & Zhang, W.: Online malware defense using attack behavior model. In 2016 IEEE International Symposium on Circuits and Systems (ISCAS), 1322–1325 (2016)
Mosli, R., Li, R., Yuan, B., Pan, Y.: Automated malware detection using artifacts in forensic memory images. 2016 IEEE Symp. Technol. Homel. Secur. HST 2016. (2016).
Intel VTune Amplifier 2019. https://software.intel.com/en-us/intel-vtune-amplifier-xe (2019), Accessed 31 Dec 2019
Nataraj, L., Karthikeyan, S., Jacob, G., Manjunath, B.S.: Malware images: Visualization and automatic classification. ACM Int. Conf. Proceeding Ser. (2011)
Manavi, F., Hamzeh, A.: A new approach for malware detection based on evolutionary algorithm. GECCO 2019 Companion - Proc. 2019 Genet. Evol. Comput. Conf. Companion. 1619–1624 (2019)
Cui, Z., Xue, F., Cai, X., Cao, Y., Wang, G.G., Chen, J.: Detection of malicious code variants based on deep learning. IEEE Trans. Ind. Informatics. 14, 3187–3196 (2018)
Bakhshinejad, N., Hamzeh, A.: Parallel-CNN network for malware detection. IET Inf. Secur. 14, 210–219 (2020)
Ghiasi, M., Sami, A., Salehi, Z.: Dynamic vsa: a framework for malware detection based on register contents. Eng. Appl. Artif. Intell. 44, 111–122 (2015)
Guo, W., Wang, T., Wei, J.: Malware detection with convolutional neural network using hardware events. Commun. Comput. Inf. Sci. 600, 104–115 (2018)
Dictionary of Hardware. https://www.techopedia.com, Accessed 7 July 2019
Intel Processor Events Reference. https://software.intel.com/en-us/vtune-help-intel-processor-events-reference, Accessed 23 July 2019
Intel VTune Amplifier: Intel Processor Events Reference. https://scc.ustc.edu.cn/zlsc/tc4600/intel/2017.0.098/vtune_amplifier_xe/help/GUID-ECB96402-717C-4DAA-B127-85972AF4CB4F.html, Accessed 23 July 2019
CS231n Convolutional Neural Networks for Visual Recognition. https://cs231n.github.io, Accessed 7 Dec 2019
Camacho, C.: Convolutional Neural Networks. https://sezannec.github.io, Accessed 7 Dec 2019
Haridas, R., Jyothi, R.L.: Convolutional neural networks: A comprehensive survey. Int. J. Appl. Eng. Res. 14, 780–789 (2019)
Fully Connected Layers in Convolutional Neural Networks. https://missinglink.ai, Accessed 22 Nov 2019
Ororbia, A., Mali, A., Giles, C. L., & Kifer, D.: Continual learning of recurrent neural networks by locally aligning distributed representations. IEEE Transactions on Neural Networks and Learning Systems. 1–13 (2018)
Olah, C. Understanding LSTM Networks. http://colah.github.io (2018), Accessed by 8 Dec 2019
Nguyen, M.: Illustrated Guide to LSTM's and GRU's: A step by step explanation. https://towardsdatascience.com (2018), Accessed 7 Dec 2019
Cho, K., van Merrienboer, B., Gulcehre, C., Bahdanau, D., Bougares, F., Schwenk, H., Bengio, Y.: Supplementary Material Learning Phrase Representations using RNN Encoder–Decoder for Statistical Machine Translation. In: Proceedings of the 2014 conference on empirical methods in natural language processing (EMNLP). 1724–1734 (2014)
Schmidhuber, J.: Deep Learning in neural networks: An overview. Neural Netw. 61, 85–117 (2015). https://doi.org/10.1016/j.neunet.2014.09.003
Zhao, Z., Chen, W., Wu, X., Chen, P.C.V., Liu, J.: LSTM network: A deep learning approach for short-term traffic forecast. IET Image Process. 11, 68–75 (2017)
PortableApps.com. https://portableapps.com/2019, Accessed 13 Jan 2019
SnapFiles.com. https://snapfiles.com/2019, Accessed 17 Jan 2019
VirusShare.com. https://virusshare.com/2019, Accessed 19 Jan 2019
VMware's Vix in python. https://pypi.org, Accessed 22 Feb 2019
Keras Documentation. https://keras.io, Accessed 20 Feb 2019
Pedregosa, F., Varoquaux, G., Gramfort, A., Michel, V., Thirion, B., Grisel, O., Blondel, M., Prettenhofer, P., Weiss, R., Dubourg, V., Vanderplas, J., Passos, A., Cournapeau, D., Brucher, M., Perrot, M., Duchesnay, É.: Scikit-learn: Machine learning in Python. J. Mach. Learn. Res. 12, 2825–2830 (2011)
kohavi, R.: A study of cross-validation and bootstrap for accuracy estimation and model selection. In Ijacai, Stanford, CA. 14, 1137–1145 (1995)
Powers, D.M.: Evaluation: from precision, recall and F-measure to ROC, informedness, markedness and correlation. J. Mach. Learn. Technol. 2(1), 37–39 (2011)
Hashemi, H., Hamzeh, A.: Visual malware detection using local malicious pattern. J. Comput. Virol. Hacking Tech. 15, (2019)
Author information
Authors and Affiliations
Corresponding author
Additional information
Publisher's Note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Rights and permissions
About this article
Cite this article
Ghanei, H., Manavi, F. & Hamzeh, A. A novel method for malware detection based on hardware events using deep neural networks. J Comput Virol Hack Tech 17, 319–331 (2021). https://doi.org/10.1007/s11416-021-00386-y
Received:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11416-021-00386-y