Abstract
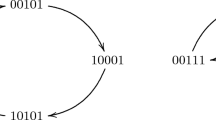
Boolean functions used in stream ciphers against algebraic attacks are required to have a necessary cryptographic property-high algebraic immunity (AI). In this paper, Boolean functions of even variables with the maximum AI are investigated. The number of independent annihilators at the lowest degree of Boolean functions of even variables with the maximum AI is determined. It is shown that when n is even, one can get an (n + 1)-variable Boolean function with the maximum AI from two n-variable Boolean functions with the maximum AI only if the Hamming weights of the two functions satisfy the given conditions. The nonlinearity of the Boolean functions obtained in this way is computed. Similarly, one can get an (n + 2)-variable Boolean function with the maximum AI from four n-variable Boolean functions with the maximum AI. The nonlinearity of a class of Boolean functions with the maximum AI is determined such that their Hamming weights are either the maximum or the minimum.
Similar content being viewed by others
References
Courtois N, Pieprzyk J. Cryptanalysis of block ciphers with overdefined systems of equations. In: Goos G, Hartmanis J, van Leeuwen J, eds. Advances in Cryptology-ASIACRYPT 2002. Lecture Notes in Computer Science, Vol. 2501. Berlin: Springer-Verlag, 2002. 267–287
Courtois N, Meier W. Algebraic attacks on stream ciphers with linear feedback. In: Goos G, Hartmanis J, van Leeuwen J, eds. Advances in Cryptology-EUROCRYPT 2003. Lecture Notes in Computer Science, Vol. 2656. Berlin: Springer-Verlag, 2003. 345–359
Armknecht F, Krause M. Algebraic attacks on combiners with memory. In: Goos G, Hartmanis J, van Leeuwen J, eds. Advances in Cryptology-CRYPTO 2003. Lecture Notes in Computer Science, Vol. 2729. Berlin: Springer-Verlag, 2003. 162–175
Courtois N. Fast algebraic attacks on stream ciphers with linear feedback. In: Goos G, Hartmanis J, van Leeuwen J, eds. Advances in Cryptology-CRYPTO 2003. Lecture Notes in Computer Science, Vol. 2729. Berlin: Springer-Verlag, 2003. 176–194
Armknecht F. Improving fast algebraic attacks. In: Goos G, Hartmanis J, van Leeuwen J, eds. Fast Software Encryption 2004. Lecture Notes in Computer Science, Vol. 3017. Berlin: Springer-Verlag, 2004. 65–82
Meier W, Pasalic E, Carlet C. Algebraic attacks and decomposition of Boolean functions. In: Goos G, Hartmanis J, van Leeuwen J, eds. Advances in Cryptology-EUROCRYPT 2004. Lecture Notes in Computer Science, Vol. 3027. Berlin: Springer-Verlag, 2004. 474–491
Carlet C, Dalai D K, Gupta K C, et al. Algebraic immunity for cryptographically significant Boolean functions: analysis and construction. IEEE Trans Inf Theory, 2006, 52: 3105–3121
Dalai D K, Gupta K C, Maitra S. Results on algebraic immunity for cryptographically significant Boolean functions. In: Goos G, Hartmanis J, van Leeuwen J, eds. Progress in Cryptology-INDOCRYPT 2004. Lecture Notes in Computer Science, Vol. 3348. Berlin: Springer-Verlag, 2004. 92–106
Dalai D K, Gupta K C, Maitra S. Cryptographically significant Boolean functions: construction and analysis in terms of algebraic immunity. In: Goos G, Hartmanis J, van Leeuwen J, eds. Fast Software Encryption 2005. Lecture Notes in Computer Science, Vol. 3557. Berlin: Springer-Verlag, 2005. 98–111
Dalai D K, Gupta K C, Maitra S. Notion of algebraic immunity and its evaluation related to fast algebraic attacks. Cryptology ePrint Archive, Report 2006/018. 2006. http://eprint.iacr.org/2006/018.pdf
Dalai D K, Maitra S, Sarkar S. Basic theory in construction of Boolean functions with maximum possible annihilator immunity. Designs, Codes and Cryptography, 2006, 40: 41–58
Braeken A, Preneel B. On the algebraic immunity of symmetric Boolean functions. In: Goos G, Hartmanis J, van Leeuwen J, eds. Progress in Cryptology-INDOCRYPT 2005. Lecture Notes in Computer Science, Vol. 3797. Berlin: Springer-Verlag, 2005. 35–48
Qu L, Li C, Feng K. A note on symmetric Boolean functions with maximum algebraic immunity in odd number of variables. IEEE Trans Inf Theory, 2007, 58: 2908–2910
Carlet C. A method of construction of balanced functions with the optimum algebraic immunity. Cryptology ePrint Archive, Report 2006/149. 2006. http://eprint.iacr.org/2006/149.pdf.
Qu L, Feng G, Li C. On the Boolean functions with maximum possible algebraic immunity: construction and a lower bound of the count. Cryptology ePrint Archive, Report 2005/449. 2005. http://eprint.iacr.org/2005/449.pdf.
Li N, Qi W. Construction and count of Boolean functions of an odd number of variables with maximum algebraic immunity. arXiv.org e-Print archive, cs>arXiv:cs/0605139. 2006. http://arxiv.org/abs/cs.CR/0605139
Li N, Qi W. Boolean functions of an odd number of variables with maximum algebraic immunity. Sci China Ser F-Inf Sci, 2007, 50: 307–317
Lobanov M. Tight bound between nonlinearity and algebraic immunity. Cryptology ePrint Archive, Report 2005/441. 2005. http://eprint.iacr.org/2005/441.pdf
Author information
Authors and Affiliations
Corresponding author
Rights and permissions
About this article
Cite this article
Du, Y., Pei, D. Construction of Boolean functions with maximum algebraic immunity and count of their annihilators at lowest degree. Sci. China Inf. Sci. 53, 780–787 (2010). https://doi.org/10.1007/s11432-010-0064-2
Received:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11432-010-0064-2