Abstract
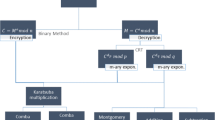
This paper proposes an optimal method for large integer multiplication when implementing modern cryptographic applications on Peer-to-Peer ubiquitous networks. P2P ubiquitous networks are usually composed of smart low-end devices, which operate on the limited battery power. To maximize the lifetime of P2P networks, the power consumption rate of each node must be quite careful, and an efficient and energy-saving large integer multiplication makes the cryptographic protocols possible to be executed on such nodes. The proposed method first recursively bisections multiplier and multiplicand in threshold times. Subsequently, classical multiplication calculates the products of the split multiplier and multiplicand blocks. Finally, the products of the blocks are gradually integrated to obtain the product of the large integers. This study demonstrates that the n-times recursive-balanced-2-way split method, where n is the floor of log2(0.13515 × s), obtains the optimal performance in multiplying two s-words based on classical multiplication. The experiment results show that modular exponentiation combined with other modular multiplication methods uses 1.28×–2.10× the computational cost required in the proposed method. The energy consumption of software is closely related to the execution time. The proposed scheme is an energy-saving method to maximize the lifetime of P2P ubiquitous networks when implementing security protocols in smart low-end devices on P2P networks. It is suitable for realizing robust security protocol on smart low-end devices, in which the framework is based on modular exponentiation and modular multiplication. Smart low-end devices based on the proposed method perform security protocols in satisfying the security recommendations of NIST.



Similar content being viewed by others
References
RSA Laboratories, RSA challenges. Available from URL: http://www.rsasecurity.com/rsalabs/
NIST Recommendation for Key Management: Part 1: General (Revision 3). NIST Special Publication 800-57, July 2012, Available from URL: http://csrc.nist.gov/publications/nistpubs/800-57/sp800-57_part1_rev3_general.pdf
NIST: “Recommendation for Key Management, Part 3 Application-Specific Key Management Guidance,” NIST Special Publication 800-57, December 2009. Available from URL: http://csrc.nist.gov/publications/nistpubs/800-57/sp800-57_PART3_key-management_Dec2009.pdf
Silas S, Ezra K, Rajsingh EB (2012) A novel fault tolerant service selection framework for pervasive computing. Human-centric Comput Inf Sci 2:5
Luo H, Shyu M (2011) Quality of service provision in mobile multimedia—a survey. Human-centric Comput Inf Sci 1:5
Kettani MD, En-Nasry B (2011) MidM: an open architecture for mobile identity. J Converg 2(2):25–32
Li Y, Xiao L, Chen S, Tian H, Ruan L, Yu B (2011) Parallel point-multiplication based on the extended basic operations on conic curves over ring Z n . J Converg 2(1):69–78
Rivest R, Shamir A, Adleman L (1978) A method for obtaining digital signatures and public-key cryptosystems. Commun ACM 21:120–126
Koblitz N (1987) Elliptic curve cryptosystems. Math Comp 48:203–209
NIST, FIPS PUB 186-3, Digital Signature Standard (DSS). NIST Publication FIPS 186-3, June 2009, Available from URL: http://csrc.nist.gov/publications/fips/fips186-3/.pdf
Diffie W, Hellman ME (1976) New directions in cryptography. IEEE Trans Inf Theory IT-22(6):638–654
Hankerson D, Menezes A, Vanstone S (2004) Guide to elliptic curve cryptography. Springer
Eberle H, Shantz S, Gupta V, Gura N, Rarick L, Spracklen L (2005) Accelerating next-generation public-key cryptosystems on general-purpose CPUs. IEEE Macro 25(2):52–59
Karatsuba A, Ofman Y (1963) Multiplication of multidigit numbers on automata. Sov Phys Doklagy 7(7):595–596
Lederer C, Mader R, Koschuch M, Grobschadl J, Szekely A, Tillich S (2009) Energy-efficient implementation of ECDH key exchange for wireless sensor networks. WISTP 2009, LNCS 5746, pp 112–127
Menezes AJ, van Oorschot PC, Vanstone SA (1997) Handbook of applied cryptography. CRC Press
Knuth DE, The art of computer programming, 1969, 2nd edition, 3rd edition, 1998. Addison-Wesley
Groβschädl J, Avanzi RM, Savas E, Tillich S (2005) Energy-efficient software implementation of large integer modular arithmetic. CHES 2005, LNCS 3659, pp 75–90
Texas Instruments, C5000 DSPs: Architecture & Peripheral Features, Available: http://www.ti.com
Koc CK, Acar T, Kaliski BS (1996) Analyzing and computing montgomery algorithms. IEEE Macro 16(3):26–33
Author information
Authors and Affiliations
Corresponding author
Appendices
Appendix 1. Proof of Theorem 1
From Fig. 1, balanced-t-way split can be shown as following:
According to Eq. (1), every cross term in Eq. (4) can be shown as below:
Therefore, the number of base instruction is estimated according to Tables 1 and 2.
-
(a)
the number of base instructions for the classical multiplication:
-
the number of classical multiplications
$$ \begin{array}{*{20}c} {=t\times Mul{t_{CM }}\left( {s/t} \right)+C_2^t\times Mul{t_{CM }}\left( {s/t} \right)} \\ {=\frac{{{t^2}+t}}{2}\times Mul{t_{CM }}\left( {s/t} \right)} \\ \end{array} $$ -
⇒the number of base instructions
$$ \begin{array}{*{20}c} {=\frac{{{t^2}+t}}{2}\times Mul{t_{CM }}\left( {s/t} \right)\left| {_{{Mul{t_{CM }}(s)=8{s^2}+2s}}} \right.} \\ {=\frac{{{t^2}+t}}{2}\left( {8\frac{{{s^2}}}{{{t^2}}}+2\frac{s}{t}} \right)} \\ {=\frac{4t+4 }{t}{s^2}+\left( {t+1} \right)s} \\ \end{array} $$
-
-
(b)
the number of base instructions for the large integer additions/subtractions:
-
the number of additions/subtractions
$$ =\frac{{t\left( {t-1} \right)}}{2}\times AddSub\left( {2\times \frac{s}{t}} \right)+2\times C_2^t\times AddSub\left( {2\times \frac{s}{t}} \right)+2\times C_2^t\times AddSub\left( {\frac{s}{t}} \right) $$ -
⇒ the number of base instructions
$$ \begin{array}{*{20}c} {=\frac{{t\left( {t-1} \right)}}{2}\times AddSub\left( {2\times \frac{s}{t}} \right)+2\times C_2^t\times AddSub\left( {2\times \frac{s}{t}} \right)+2\times C_2^t\times AddSub\left( {\frac{s}{t}} \right)\left| {_{AddSub(s)=5s }} \right.} \\ {=3\frac{{{t^2}-t}}{2}\left( {2\times 4\times \frac{s}{t}} \right)+2\frac{{{t^2}-t}}{2}\left( {5\times \frac{s}{t}} \right)} \\ {=20\left( {t-1} \right)s} \\ \end{array} $$
-
By (a) and (b), the number of base instructions for balanced-t-way split is \( \frac{4t+4 }{t}{s^2}+\left( {t+1} \right)s+20\left( {t-1} \right)s=\frac{4t+4 }{t}{s^2}+\left( {21t-19} \right)s \)
Appendix 2. Proof of Theorem 2
From Fig. 2, this work estimates the number of base instructions for unbalanced-t-way split. For convenience, we define every block length as following:
-
(a)
the number of base instructions for the classical multiplication:
-
the number of classical multiplications
$$ \begin{array}{*{20}c} {\left[ {Mul{t_{CM }}\left( {{s_1}} \right)+Mul{t_{CM }}\left( {{s_2}} \right)+\cdots +Mul{t_{CM }}\left( {{s_t}} \right)} \right]+\left[ {Mul{t_{CM }}\left( {{s_2}} \right)+\cdots +Mul{t_{CM }}\left( {{s_t}} \right)} \right]+\left[ {Mul{t_{CM }}\left( {{s_3}} \right)+\cdots +Mul{t_{CM }}\left( {{s_t}} \right)} \right]+\cdots +\left[ {Mul{t_{CM }}\left( {{s_{t-1 }}} \right)+Mul{t_{CM }}\left( {{s_t}} \right)} \right]+\left[ {Mul{t_{CM }}\left( {{s_t}} \right)} \right]} \hfill \\ {=Mul{t_{CM }}\left( {{s_1}} \right)+2\times Mul{t_{CM }}\left( {{s_2}} \right)+\cdots +\left( {t-1} \right)\times Mul{t_{CM }}\left( {{s_{t-1 }}} \right)+t\times Mul{t_{CM }}\left( {{s_t}} \right)} \hfill \\ \end{array} $$ -
⇒the number of base instructions
$$ \begin{array}{*{20}c} {=Mul{t_{CM }}\left( {{s_1}} \right)+2\times Mul{t_{CM }}\left( {{s_2}} \right)+\cdots +\left( {t-1} \right)\times Mul{t_{CM }}\left( {{s_{t-1 }}} \right)+t\times Mul{t_{CM }}\left( {{s_t}} \right)\left| {_{{Mul{t_{CM }}(s)=8{s^2}+2s}}} \right.} \\ {=\frac{4t+4 }{t}{s^2}+\left\{ {\left( {t+1} \right)+\frac{16 }{t}\left[ {\left( {t-1} \right){d_1}+\left( {t-2} \right){d_2}+\cdots +{d_{t-1 }}} \right]} \right\}s+\left\{ {2\left[ {\left( {t-1} \right){d_1}+\left( {t-2} \right){d_2}+\cdots +{d_{t-1 }}} \right]+8\left[ {d_1^2+2d_2^2+\cdots +t{{{\left( {{d_1}+{d_2}+\cdots +{d_{t-1 }}} \right)}}^2}} \right]} \right\}} \\ \end{array} $$(5)
-
-
(b)
the number of base instructions for the large integer additions/subtractions:
-
the number of additions/subtractions
$$ \begin{array}{*{20}c} {=3\left[ {AddSub\left( {2{s_2}} \right)+2AddSub\left( {2{s_3}} \right)+\cdots +\left( {t-1} \right)AddSub\left( {2{s_t}} \right)} \right]+2\left[ {AddSub\left( {{s_2}} \right)+2AddSub\left( {{s_3}} \right)+\cdots +\left( {t-1} \right)AddSub\left( {{s_t}} \right)} \right]} \\ {=3\left[ {AddSub\left( {2{s_2}} \right)+2AddSub\left( {2{s_3}} \right)+\cdots +\left( {t-1} \right)AddSub\left( {2{s_t}} \right)} \right]+2\left[ {AddSub\left( {{s_2}} \right)+2AddSub\left( {{s_3}} \right)+\cdots +\left( {t-1} \right)AddSub\left( {{s_t}} \right)} \right]} \\ \end{array} $$ -
⇒the number of base instructions
$$ \begin{array}{*{20}c} {=3\left[ {AddSub\left( {2{s_2}} \right)+2AddSub\left( {2{s_3}} \right)+\cdots +\left( {t-1} \right)AddSub\left( {2{s_t}} \right)} \right]+2\left[ {AddSub\left( {{s_2}} \right)+2AddSub\left( {{s_3}} \right)+\cdots +\left( {t-1} \right)AddSub\left( {{s_t}} \right)} \right]\left| {_{AddSub(s)=5s }} \right.} \\ {=20\left( {t-1} \right)s+40\left[ {\left( {t-1} \right){d_1}+\left( {t-2} \right){d_2}+\cdots +{d_{t-1 }}} \right]} \\ \end{array} $$(6)
-
We get the number of base instructions for unbalanced-t-way split = (5) + (6)
Appendix 3. Proof of Corollary 1
Without any loss of generality, assuming that there are (k − 1) different d i in total and that each d i < 0. By Conditions 3 & 4 in Theorem 2, two relations can be deduced:
By Relation (Ι),
By condition (2) of Theorem 2, Relation (ΙΙ), and (ΙΙΙ), \( \left( {t-1} \right){d_1}+\left( {t-2} \right){d_2}+\cdots +{d_{t-1 }}>0 \)
Appendix 4. Proof of Theorem 3
By the proof of Theorem 1, the number of base instructions of balanced-t-way split to multiply two s-word integers by classical multiplication is \( \frac{{{t^2}+t}}{2}Mul{t_{CM }}\left( {s/t} \right)+20\left( {t-1} \right)s \).
The number of base instructions of 2-times recursive-balanced-t-way split to multiply two s-word integers by classical multiplication is \( \frac{{{t^2}+t}}{2}\left[ {\frac{{{t^2}+t}}{2}Mul{t_{CM }}\left( {s/{t^2}} \right)+20\left( {t-1} \right)\left( {s/t} \right)} \right]+20\left( {t-1} \right)s \).
The number of base instructions of n-times recursive-balanced-t-way split to multiply two s-word integers by classical multiplication is \( {{\left( {\frac{{{t^2}+t}}{2}} \right)}^n}Mul{t_{CM }}\left( {s/{t^n}} \right)+\left[ {20\left( {t-1} \right)(s)+\frac{{{t^2}+t}}{2}20\left( {t-1} \right)\left( {s/t} \right)+{{{\left( {\frac{{{t^2}+t}}{2}} \right)}}^n}20\left( {t-1} \right)\left( {s/{t^2}} \right)+\cdots +{{{\left( {\frac{{{t^2}+t}}{2}} \right)}}^{n-1 }}20\left( {t-1} \right)\left( {s/{t^{{\left( {n-1} \right)}}}} \right)} \right]\left| {_{{Mul{t_{CM }}(s)=8{s^2}+2s}}} \right.=8{{\left( {\frac{t+1 }{2t }} \right)}^n}{s^2}+42{{\left( {\frac{t+1 }{2}} \right)}^n}s-40s \).
Theorem 4 finds the n that results in optimal performance of n-times recursive-balanced-t-way split.
Appendix 5. Proof of Theorem 4
From Theorem 3, the number of base instructions of n-times recursive balanced-t-way split is \( 8{{\left( {\frac{t+1 }{2t }} \right)}^n}{s^2}+42{{\left( {\frac{t+1 }{2}} \right)}^n}s-40s,t\geqslant 2,n\geqslant 1 \).
Let \( f(n)=8{{\left( {\frac{t+1 }{2t }} \right)}^n}{s^2}+42{{\left( {\frac{t+1 }{2}} \right)}^n}s-40s \).
In order to find the minimum value of f (n), we set f ′(n) = 0 and solve for n.
we get \( n={\log_t}\frac{{4s\left[ {\ln \left( {2t} \right)-\ln \left( {t+1} \right)} \right]}}{{21\left[ {\ln \left( {t+1} \right)-\ln 2} \right]}} \).
f (n) has the minimum value when \( n={\log_t}\frac{{4s\left[ {\ln \left( {2t} \right)-\ln \left( {t+1} \right)} \right]}}{{21\left[ {\ln \left( {t+1} \right)-\ln 2} \right]}} \).
The n-times recursive-balanced-t-way split performs the minimum number of base instructions as \( n=\left\lfloor {{\log_t}\frac{{4s\left[ {\ln \left( {2t} \right)-\ln \left( {t+1} \right)} \right]}}{{21\left[ {\ln \left( {t+1} \right)-\ln 2} \right]}}} \right\rfloor \).
Appendix 6. Proof of Theorem 5
By Theorem 3, the number of base instructions of n-times recursive-balanced-t-way split is \( 8{{\left( {\frac{t+1 }{2t }} \right)}^n}{s^2}+42{{\left( {\frac{t+1 }{2}} \right)}^n}s-40s \).
By Theorem 4, n-times recursive-balanced-t-way split performs the minimum number of base instructions as \( n={\log_t}\frac{{4s\left[ {\ln \left( {2t} \right)-\ln \left( {t+1} \right)} \right]}}{{21\left[ {\ln \left( {t+1} \right)-\ln 2} \right]}} \).
Define that g(t, s) is the number of base instructions of using n-times recursive-balanced-t-way split to multiply two s-word integers when \( n={\log_t}\frac{{4s\left[ {\ln \left( {2t} \right)-\ln \left( {t+1} \right)} \right]}}{{21\left[ {\ln \left( {t+1} \right)-\ln 2} \right]}} \).
We get \( g\left( {t,\,s} \right)=8{{\left( {\frac{t+1 }{2t }} \right)}^{{{\log_t}\frac{{4s\left[ {\ln \left( {2t} \right)-\ln \left( {t+1} \right)} \right]}}{{21\left[ {\ln \left( {t+1} \right)-n2} \right]}}}}}{s^2}+42{{\left( {\frac{t+1 }{2}} \right)}^{{{\log_t}\frac{{4s\left[ {\ln \left( {2t} \right)-\ln \left( {t+1} \right)} \right]}}{{21\left[ {\ln \left( {t+1} \right)-\ln 2} \right]}}}}}s-40s \)3
Then we find the partial derivative of g(t, s) with respect to t.
It is clear that \( \frac{{\partial g\left( {t,s} \right)}}{{\partial t}}\geqslant 0 \) because s and t are two positive integers. Therefore, g(t, s) is a non-decreasing function. By this result, the smallest value of t is 2 for the n-times recursive-balanced-t-way split. Consequently, using n-times recursive-balanced-2-way split to multiply two s-word integers is more efficient than using n-times recursive-balanced-t-way split for t > 2.
Appendix 7. Proof of Lemma 1
From the results of Theorem 1, 2 and Corollary 1, there exists the relation below:
We get the balanced-t-way split performs better than unbalanced-t-way split.
Rights and permissions
About this article
Cite this article
Hwang, RJ., Huang, LS. The optimal split method of large integer multiplication for smart low-end devices on P2P ubiquitous networks. Peer-to-Peer Netw. Appl. 7, 655–664 (2014). https://doi.org/10.1007/s12083-012-0189-8
Received:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s12083-012-0189-8