Abstract
Domain extender for the ideal cipher was firstly studied by Coron et al. (TCC 2010). The construction given by them doubles the domain. To extend the domain by a factor of t > 2, recursively applying their extender requires using the cipher exponential times, i.e. \(\mathcal {O}(t^{log_{2}3})\). In this paper, we describe an improved extender which extends the domain by a factor of t with \(\mathcal {O}(t)\) calls to underlying small-block blockciphers. This extender is based on a (2t − 1)-round generalized Feistel structure, and is actually a generalization of the proposal of Coron et al. We show it to be indifferentiable from an ideal cipher with tn-bit blocks. Additionally, for expansion factor t we give an attack to show that indifferentiability cannot be achieved in (2t − 2)-round case. Compared with the recursively applying strategy, the time complexity of this extender is competitive in some practical applications.





Similar content being viewed by others
Notes
References
Andreeva, E., Bogdanov, A., Dodis, Y., Mennink, B., Steinberger, J.: On the indifferentiability of key-alternating ciphers. In: Canetti, R., Garay, J. (eds.) Advances in Cryptology – CRYPTO 2013, Lecture Notes in Computer Science, vol. 8042, pp. 531–550. Springer, Berlin Heidelberg (2013)
Bellare, M., Kohno, T.: A theoretical treatment of related-key attacks: Rka-prps, rka-prfs, and applications. In: Biham, E. (ed.) Advances in Cryptology – EUROCRYPT 2003, Lecture Notes in Computer Science, vol. 2656, pp. 491–506. Springer, Berlin Heidelberg (2003)
Bertoni, G., Daemen, J., Peeters, M., Van Assche, G.: On the indifferentiability of the sponge construction. In: Smart, N. (ed.) Advances in Cryptology – EUROCRYPT 2008, Lecture Notes in Computer Science, vol. 4965, pp. 181–197. Springer, Berlin Heidelberg (2008)
Black, J.: The ideal-cipher model, revisited: An uninstantiable blockcipher-based hash function. In: Robshaw, M. (ed.) Fast Software Encryption, Lecture Notes in Computer Science, vol. 4047, pp. 328–340. Springer, Berlin Heidelberg (2006)
Black, J., Rogaway, P., Shrimpton, T.: Black-box analysis of the block-cipher-based hash-function constructions from pgv. In: Yung, M. (ed.) Advances in Cryptology – CRYPTO 2002, Lecture Notes in Computer Science, vol. 2442, pp. 320–335. Springer, Berlin Heidelberg (2002)
Cogliati, B., Seurin, Y.: On the provable security of the iterated even-mansour cipher against related-key and chosen-key attacks. In: EUROCRYPT 2015. Lecture Notes in Computer Science. (2015, to appear), full version: http://eprint.iacr.org/2015/069.pdf. Springer, Berlin Heidelberg
Coron, J.S., Dodis, Y., Mandal, A., Seurin, Y.: A domain extender for the ideal cipher. In: Micciancio, D. (ed.) Theory of Cryptography, Lecture Notes in Computer Science, vol. 5978, pp. 273–289. Springer, Berlin Heidelberg (2010)
Coron, J.S., Dodis, Y., Malinaud, C., Puniya, P.: Merkle-damgård revisited: How to construct a hash function. In: Shoup, V. (ed.) Advances in Cryptology – CRYPTO 2005, Lecture Notes in Computer Science, vol. 3621, pp. 430–448. Springer, Berlin Heidelberg (2005)
Coron, J.S., Dodis, Y., Mandal, A., Seurin, Y.: A domain extender for the ideal cipher. Cryptology ePrint Archive, Report 2009/356. http://eprint.iacr.org/ (2009)
Coron, J.S., Patarin, J., Seurin, Y.: The random oracle model and the ideal cipher model are equivalent. In: Wagner, D. (ed.) Advances in Cryptology – CRYPTO 2008, Lecture Notes in Computer Science, vol. 5157, pp. 1–20. Springer, Berlin Heidelberg (2008)
Dai, Y., Lee, J., Mennink, B., Steinberger, J.: The security of multiple encryption in the ideal cipher model. In: Garay, J., Gennaro, R. (eds.) Advances in Cryptology – CRYPTO 2014, Lecture Notes in Computer Science, vol. 8616, pp. 20–38. Springer, Berlin Heidelberg (2014)
Demay, G., Gaži, P., Hirt, M., Maurer, U.: Resource-restricted indifferentiability. In: Johansson, T., Nguyen, P. (eds.) Advances in Cryptology – EUROCRYPT 2013, Lecture Notes in Computer Science, vol. 7881, pp. 664–683. Springer, Berlin Heidelberg (2013)
Guo, C., Lin, D.: On the indifferentiability of key-alternating feistel ciphers with no key derivation. In: TCC 2015. Lecture Notes in Computer Science. (2015, to appear), full version: http://eprint.iacr.org/. Springer, Berlin Heidelberg
Holenstein, T., Künzler, R., Tessaro, S.: The equivalence of the random oracle model and the ideal cipher model, revisited. In: Proceedings of the Forty-third Annual ACM Symposium on Theory of Computing. pp. 89–98. STOC ’11. ACM, New York (2011)
Lampe, R., Seurin, Y.: How to construct an ideal cipher from a small set of public permutations. In: Sako, K., Sarkar, P. (eds.) Advances in Cryptology – ASIACRYPT 2013, Lecture Notes in Computer Science, vol. 8269, pp. 444–463. Springer, Berlin Heidelberg (2013)
Maurer, U., Renner, R., Holenstein, C.: Indifferentiability, impossibility results on reductions, and applications to the random oracle methodology. In: Naor, M. (ed.) Theory of Cryptography, Lecture Notes in Computer Science, vol. 2951, pp. 21–39. Springer, Berlin Heidelberg (2004)
Minematsu, K.: Beyond-birthday-bound security based on tweakable block cipher. In: Dunkelman, O. (ed.) Fast Software Encryption, Lecture Notes in Computer Science, vol. 5665, pp. 308–326. Springer, Berlin Heidelberg (2009)
Minematsu, K.: Building blockcipher from small-block tweakable blockcipher. Des. Codes Crypt., 1–19 (2013)
Ristenpart, T., Shacham, H., Shrimpton, T.: Careful with composition: Limitations of the indifferentiability framework. In: Paterson, K. (ed.) Advances in Cryptology – EUROCRYPT 2011, Lecture Notes in Computer Science, vol. 6632, pp. 487–506. Springer, Berlin Heidelberg (2011)
Acknowledgments
We deeply thank the anonymous reviewers for their useful comments and corrections. We also thank the editors, for their efforts and helpful suggestions. We are also grateful to Jianghua Zhong, mostly for her vital reminder.
This work is partially supported by National Key Basic Research Project of China (2011CB302400), National Science Foundation of China (61379139) and the “Strategic Priority Research Program” of the Chinese Academy of Sciences-Grant No. XDA06010701.
Author information
Authors and Affiliations
Corresponding author
Appendices
Appendix A: Deferred Pseudocode
We formally describe the other two approaches in this section.
1.1 A.1 Pseudocode for the recursive approach
Denote the construction obtained through recursively calling Ψ3 by \({\Psi }_{3}^{t,E[n,n]}\) where t is the expansion factor. For simplicity, we assume t = 2h where h is an integer,Footnote 4 assume the key length of \({\Psi }_{3}^{t,E[n,n]}\) to be 0 (the case discussed in Introduction), and only present the code for the forward computation. The code is as follows. Note that in the code, the ideal ciphers built from E[n, n] are written as private procedures. Moreover, the strings 〈0〉 and 〈1〉 are 1-bit encodings of 0 and 1, the string 〈i n d e x〉 is a \(\lceil log_{2}(t^{log_{2} 3})\rceil \)-bit encoding of the integer index, while 〈i〉 is a ⌈l o g 2(2t − 1)⌉-bit encoding of i.

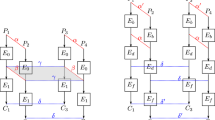
1.2 A.2 the 2-step approach, and the Pseudocode
Denote the construction built through the 2-step approach by \(LR_{14}^{E[n,n]}\). We also assume that the key length is 0. For t = 2l, we first build 14 length-preserving random oracles H : {0, 1}ln → {0, 1}ln. According to Section 5 of [8], for a fixed expansion factor t = 2l and 0 ≤ j ≤ 13, the constructions depicted in Fig. 6 give 14 such random oracles. Then the code is as follows (only include the code for the forward computation). In the code, the string 〈j⋅l + i〉 is n-bit encoding.

Appendix B: Some deferred proofs
1.1 B.1 Proof for lemma 5
Wlog we consider the case of a query E[κ, t n].E n c, and the case of E[κ, t n].D e c is similar by symmetry. If E[κ, t n].E n c was made by S[t], then this was while executing the procedure F i l l i n g C h a i n, and clearly the equality holds right after the end of this procedure. Since S[t] never overwrites entries in E T, the equality holds at the end of the execution. On the other hand, if E[κ, t n].E n c(k,(x 1,…, x t )) was first made by \(\overline {D}\), then since \(\overline {D}\) is forced to call E(1,+,(x 2,…, x t , k), x 1), S[t] will be triggered to call F i l l i n g C h a i n and add all the corresponding entries to E T, and the equality also holds.
1.2 B.2 Proof for Lemma 8
First, by Lemma 6 we know if \(\overline {D}^{{\Sigma }_{2}(\tau (u))} = 1\), then for any \(\overline {D}^{{\Sigma }_{1}(E[2n,n],S[t])}\) s.t. \(ETFunc(\overline {D},{\Sigma }_{1}(E[2n,n],S[t]))=u\), \(\overline {D}^{{\Sigma }_{1}(E[2n,n],S[t])}=\overline {D}^{{\Sigma }_{2}(\tau (u))} = 1\).
On the other hand, since \(ETFunc(\overline {D},{\Sigma }_{1}(E[2n,n],S[t]))\) has a unique value for a fixed Σ1-execution \(\overline {D}^{{\Sigma }_{1}(E[2n,n],S[t])}\), we can partition the set of all good Σ1 executions such that each subset corresponds to a unique \(u=\mathbf {ET}\in \mathcal {T}\). Hence
1.3 B.3 Proof for Lemma 9
To show the claim, we show that for any π ∈ R 2:
-
1.
there exists \(u\in \tau (\mathcal {T})\) such that π ≅ u;
-
2.
there exists at most one \(u\in \tau (\mathcal {T})\) such that π ≅ u;
For the first claim, consider the Σ1-execution \(\overline {D}^{{\Sigma }_{1}}\) during which:
-
1.
each time S[t] samples a random value, the value equals the corresponding value in π;
-
2.
each time E[κ, n] samples a random value, the values equals the corresponding input/output value of G F S[t]E[(t − 1)n + κ, n](π);
Clearly such random values are consistent, so that such a Σ1-execution is good, and \(\tau (ETFunc(\overline {D},{\Sigma }_{1}))\cong \pi \). Hence the first claim holds.
For the second claim, assume otherwise, i.e. \(\exists u^{\prime }\in \tau (\mathcal {T})\) s.t. u ≠ u ′, v ≅ u, and v ≅ u ′. Let \(v=({\pi ^{v}_{1}},\ldots ,\pi ^{v}_{2t-1})\), u = (π 1,…, π 2t − 1), \(u^{\prime }=(\pi ^{\prime }_{1},\ldots ,\pi ^{\prime }_{2t-1})\), and let the preimages of u and u ′ be \(\mathbf {ET}\in \mathcal {T}\) and \(\mathbf {ET}^{\prime }\in \mathcal {T}\). Consider any two executions \(\overline {D}^{{\Sigma }_{1}(E[\kappa ,tn],S[t])}\) and \(\overline {D}^{{\Sigma }_{1}(E[\kappa ,tn],S[t])'}\) such that:
-
1.
\(ETFunc(\overline {D}, {\Sigma }_{1}(E[\kappa ,tn],S[t]))=\mathbf {ET}=(ET_{1},\ldots ,ET_{2t-1})\),
-
2.
\(ETFunc(\overline {D}, {\Sigma }_{1}(E[\kappa ,tn],S[t])')=\mathbf {ET}^{\prime }=(ET^{\prime }_{1},\ldots ,ET^{\prime }_{2t-1})\).
We show \(Transcript(\overline {D},{\Sigma }_{1}(E[\kappa ,tn],S[t]))=Transcript(\overline {D},{\Sigma }_{1}(E[\kappa ,tn],S[t])')\) to show that the query-answer pairs generated in the two executions are exactly the same, so that E T = E T ′ and u = u ′. Assume that in the two executions, the answers for the first j − 1 queries equal correspondingly, and consider the j-th query-answer tuple q a j and \(qa_{j}^{\prime }\) in the two transcripts. Since both \(\overline {D}\) and S[t] (excluding the procedure E in) are deterministic, the procedure fields of q a j and \(qa^{\prime }_{j}\) are equal. We argue that the answer fields of them are the same. For the following cases:
-
If the procedure field is E in and the query is (i, δ, k, z), then the answers in the two executions are equal since they equal the corresponding values in E T and E T ′, and \(ET_{i}(\delta ,K,z)=\pi _{i}(\delta ,K,z)={\pi ^{v}_{i}}(\delta ,K,z)=\pi _{i}^{\prime }(\delta ,K,z)=ET_{i}^{\prime }(\delta ,K,z)\).
-
If the procedure field is E n c or D e c, following the same line as in the proof of Lemma 6 we can show that the answers are the same.
Hence \(Transcript(\overline {D},{\Sigma }_{1}(E[\kappa ,tn],S[t]))=Transcript(\overline {D},{\Sigma }_{1}(E[\kappa ,tn],S[t])')\), and u = E T = E T ′ = u ′, contradicting the assumption.
Then, with the two claims at hand, we have:
Rights and permissions
About this article
Cite this article
Guo, C., Lin, D. Improved domain extender for the ideal cipher. Cryptogr. Commun. 7, 509–533 (2015). https://doi.org/10.1007/s12095-015-0128-7
Received:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s12095-015-0128-7