Abstract
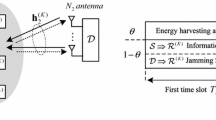
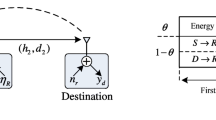
This paper studies the secure communication of an energy-harvesting system in which a source communicates with a destination via an amplify-and-forward (AF) untrusted relay. The relay uses the power-splitting policy to harvest energy from wireless signals. The source is equipped with multiple antennas and uses transmit antenna selection (TAS) and maximum ratio transmission (MRT) to enhance the harvested energy at the relay; for performance comparison, random antenna selection (RAS) is examined. The relay and destination are single-antenna nodes. To create a positive secrecy capacity, destination-assisted jamming is deployed. Because the use of multiple antennas can cause the imperfect channel state information (CSI), the channel between the source and the relay is examined in two cases: perfect CSI and imperfect CSI. To evaluate the secrecy performance, analytical expressions for the secrecy outage probability (SOP) and the average secrecy capacity (ASC) for the TAS, MRT, and RAS schemes are derived. Moreover, a high-power approximation for the SOP is presented. The accuracy of the analytical results is verified by Monte Carlo simulations. The results show the benefit of using multiple antennas in improving the secrecy performance. Specifically, MRT performs better than TAS, and both of them outperform RAS. Moreover, the results provide valuable insight into the effects of various system parameters, such as the channel correlation coefficient, energy-harvesting efficiency, secrecy rate threshold, power-splitting ratio, transmit powers, and locations of the relay, on the secrecy performance.







Similar content being viewed by others
References
Valenta CR, Durgin GD (2014) Harvesting wireless power: survey of energy-harvester conversion efficiency in far-field, wireless power transfer systems. IEEE Microw Mag 15(4):108–120
Ding Z, Perlaza SM, Esnaola I, Poor HV (2014) Power allocation strategies in energy harvesting wireless cooperative networks. IEEE Trans Wireless Commun 13(2):846–860
Zhou X, Zhang R, Ho CK (2013) Wireless information and power transfer: architecture design and rate-energy tradeoff. IEEE Trans Commun 61:4754–4767
Nasir A, Zhou X, Durrani S, Kennedy R (2013) Relaying protocols for wireless energy harvesting and information processing. IEEE Trans Wireless Commun 12:3622–3636
Son PN, Kong HY (2015) Cooperative communication with energy-harvesting relays under physical layer security. IET Commun 9(17):2131–2139
Zhong C, Suraweera H, Zheng G, Krikidis I, Zhang Z (2014) Wireless information and power transfer with full duplex relaying. IEEE Trans Commun 62:3447–3461
Gu Y, Aïssa S (2015) RF-based energy harvesting in decode-and-forward relaying systems: ergodic and outage capacities. IEEE Trans Commun 14(11):6425–6434
Zhu G, Zhong C, Suraweera H, Karagiannidis G, Zhang Z, Tsiftsis T (2015) Wireless information and power transfer in relay systems with multiple antennas and interference. IEEE Trans Commun 63:1400–1418
Liu L, Zhang R, Chua KC (2014) Secrecy wireless information and power transfer with MISO beamforming. IEEE Trans Signal Process 62(7):1850–1863
Zhang H, Li C, Huang Y, Yang L (2016) Secure beamforming for SWIPT in multiuser MISO broadcast channel with confidential messages. IEEE Commun Lett 19(8):1347–1350
Kalamkar SS, Banerjee A (2016) Secure communication via a wireless energy harvesting untrusted relay. IEEE Trans. Veh. Technol. (Accepted)
Gucluoglu T, Panayirci E (2008) Performance of transmit and receive antenna selection in the presence of channel estimation errors. IEEE Commun Lett 12(5):371–373
Chalise BK, Zhang YD, Amin MG (2013) Local CSI based full diversity achieving relay selection for amplify-and-forward cooperative systems. IEEE Trans Signal Process 61(21):5165–5180
Pan G, Lei H, Deng Y, Fan L, Yang J, Chen Y, Ding Z (2016) On secrecy performance of MISO SWIPT systems with TAS and imperfect CSI. IEEE Trans Commun 64(9):3831–3843
Gradshteyn IS, Ryzhik IM, Jeffrey A, Zwillinger D (2007) Table of integral, series and products, 7th edn. Elsevier, Amsterdam
Lv L, Chen J, Yang L, Kuo Y (2017) Improving physical layer security in untrusted relay networks: cooperative jamming and power allocation. IET Commun 11(3):393–399
Zhu G, Zhong C, Suraweera HA, Zhang Z, Yuen C, Yin R (2014) Ergodic capacity comparison of different relay precoding schemes in dual-hop AF systems with co-Channel interferer. IEEE Trans Commun 62 (7):2314–2328
David HA, Nagaraja HN (2003) Order Statistics, 3rd edn. Wiley, Hoboken
Author information
Authors and Affiliations
Corresponding author
Appendices
Appendix A: Proof of Proposition 1
Let x 1,…,x N be N exponential RVs with a rate parameter λ, and the PDF and CDF of x n , 1 ≤ n ≤ N, are respectively given by
Let us define Y = max{x 1,…,x N } and \(Z={\sum }_{n=1}^{N} x_{n}\). The CDFs of Y and Z are respectively given by
Next, we rewrite Eq. 12 as
where \({F_{{X_{1}}}}\left ({{\lambda _{1}},N;x} \right )\) and \({f_{{X_{2}}}}\left ({{\lambda _{2}};x} \right )\) are the cumulative distribution function (CDF) of X 1 and the probability density function (PDF) of X 2, respectively.
1.1 A.1 Calculation for SOPRAS
Replacing \({F_{{X_{1}}}}\left ({{\lambda _{1}},N;x} \right )\) and \({f_{{X_{2}}}}\left ({{\lambda _{2}};x} \right )\) in Eq. 37 with F(λ 1; x) and f(λ 2; x), respectively, we obtain Eq. 13.
1.2 A.2 Calculation for SOPTAS
Replacing \({F_{{X_{1}}}}\left ({{\lambda _{1}},N;x} \right )\) and \({f_{{X_{2}}}}\left ({{\lambda _{2}};x} \right )\) in Eq. 37 with F Y (λ 1,N; x) and f(λ 2; x), respectively, we obtain Eq. 14.
1.3 A.3 Calculation for SOPMRT
Replacing \({F_{{X_{1}}}}\left ({{\lambda _{1}},N;x} \right )\) and \({f_{{X_{2}}}}\left ({{\lambda _{2}};x} \right )\) in Eq. 37 with F Z (λ 1,N; x) and f(λ 2; x), respectively, we obtain Eq. 15.
Finally, Proposition 1 is proved.
Appendix B: Proof of Proposition 2
1.1 B.1 Calculation for case of perfect CSI (ζ = 1)
In this case, we have \(\mu =1, {\Xi } \left ({x;\beta } \right ) \approx \frac {x}{{x + \kappa } }\), and \({\bar x_{1}} \approx \sqrt {\frac {{\beta } }{{\eta \theta {\rho _{d}}}}}\). Therefore, Eq. 12 can be approximated as
where \({\bar x_{3}} = \frac {{\left ({\beta - 1} \right )}}{{\left ({1 - \theta } \right ){\rho _{s}}}}\left ({1 + \frac {\kappa } {{{X_{2}}}}} \right )\), and the approximation in Eq. (38) is obtained due to the fact that \(\mathop {\lim } \limits _{\left ({{\rho _{s}},{\rho _{d}}} \right ) \to \left ({\infty ,\infty } \right )} \frac {{{{\bar x}_{3}}}}{{{{\bar x}_{1}}}} = 0\).
Using the series representation of the exponential function given in [15, Eq. (1.211.1)], we can prove (16).
1.2 B.2 Calculation for case of perfect CSI (0 < ζ < 1)
In this case, we have \(\mu \approx {\mu _{0}}: = \left ({1 - \zeta } \right )\left ({1 - \theta } \right )\tfrac {{{\rho _{s}}}}{{{\lambda _{1}}}}\) and \({\Xi } \left ({x;\beta } \right ) \approx \frac {1}{\mu } - \frac {\beta } {{\left ({1 - \theta } \right ){\rho _{d}}{X_{2}} + \mu } }\). Therefore, \(\frac {1}{{\Xi \left ({x;\beta } \right )}}\) can be approximated by
Then, the asymptotic functions for the SOP are calculated by
Let us define \(t=x-\bar x_{2}\), Eq. 40 can be rewritten as
1.2.1 B.2.1 Calculation for \(\textup {SOP}_{\textup {RAS}}^{\infty }\)
Replacing \({F_{{X_{1}}}}\left ({{\lambda _{1}},N;x} \right )\) and \(f_{{X_{2}}}\left ({{\lambda _{2}};x} \right )\) in Eq. 41 with F(λ 1; x) and f(λ 2; x), respectively, we have
With the help of [15, Eq. (3.471.9)], Eq. 42 can be expressed as Eq. 17.
1.2.2 B.2.2 Calculation for \(\textup {SOP}_{\textup {TAS}}^{\infty }\)
Replacing \({F_{{X_{1}}}}\left ({{\lambda _{1}},N;x} \right )\) and \({f_{{X_{2}}}}\left ({{\lambda _{2}};x} \right )\) in Eq. 41 with F Y (λ 1,N; x) and f(λ 2; x), respectively, and using the same step in the calculation for SOPRAS∞, we obtain Eq. 18.
1.2.3 B.2.3 Calculation for \(\textup {SOP}_{\textup {MRT}}^{\infty }\)
Replacing \({F_{{X_{1}}}}\left ({{\lambda _{1}},N;x} \right )\) and \({f_{{X_{2}}}}\left ({{\lambda _{2}};x} \right )\) in Eq. 41 with F Z (λ 1,N; x) and f(λ 2; x), respectively, and using the same step in the calculation for SOPRAS∞, we obtain Eq. 19.
Finally, Proposition 2 is proved.
Appendix C: Proof of Proposition 3
1.1 C.1 Calculation for the RAS scheme
Using the PDFs of X 1 and X 2 for the RAS scheme given by f(λ 1; x) and f(λ 2; x), respectively, and [15, Eq.(4.352.1)], \(\mathcal {J}_{1}\) and \(\mathcal {J}_{2}\) for the RAS scheme are calculated as
Moreover, using the PDFs of X2 and [15, Eq.(4.337.1)], \(\mathcal {J}_{3}\) for the RAS scheme is calculated as
Substituting Eqs. 43, 44, and 45 into Eq. 22 yields (23).
1.2 C.2 Calculation for the TAS scheme
According to [18], the PDF of Y defined in Appendix A is given by
Using the PDF of X 1 for the TAS scheme given by f Y (λ 1,N; x) and [15, Eq.(4.352.1)], \(\mathcal {J}_{1}\) for the TAS scheme is calculated as
Using the fact that \(N\sum \limits _{n = 0}^{N - 1} \binom {N-1}{n} \frac {{{{\left ({ - 1} \right )}^{n}}}}{{\left ({n + 1} \right )}} = 1\), we can rewrite Eq. 47 as
Because \(\mathcal {J}_{2}\) and \(\mathcal {J}_{3}\) for the TAS scheme are the same as for the RAS scheme, Eq. 24 is obtained by substituting Eqs. 44, 45 and 48 into Eq. 22.
1.3 C.3 Calculation for the MRT scheme
According to [8], the PDF of Z defined in Appendix A is given by
Using the PDF of X 1 for the MRT scheme given by f Z (λ 1,N; x) and [15, Eq.(4.352.1)], \(\mathcal {J}_{1}\) for the MRT scheme is calculated as
Because \(\mathcal {J}_{2}\) and \(\mathcal {J}_{3}\) for the MRT scheme are the same as for the RAS scheme, Eq. 25 is obtained by substituting Eqs. 44, 45, and 50 into Eq. 22.
Appendix D: Proof of Proposition 4
From Eq. 7, the PDF of γ r is calculated as
1.1 D.1 Calculation for the RAS scheme
Replacing \({F_{{X_{1}}}}\left ({{\lambda _{1}},N;x} \right )\) and \({f_{{X_{2}}}}\left ({{\lambda _{2}};x} \right )\) in Eq. 50 with F(λ 1; x) and f(λ 2; x), respectively, Eq. 50 can be expressed as
Substituting Eqs. 50 into Eq. 26, we have the following:
In the case of λ 1 ≠ λ 2 ζ ω, \(\left ({\tfrac {{{\lambda _{1} \gamma }}}{{{\lambda _{2}}\zeta \omega } } \,+\, 1} \right )^{-1} ({1 \,+\, \gamma } )^{-1} \) can be expressed as \({\left ({1 \,-\, \tfrac {{{\lambda _{1}}}}{{{\lambda _{2}}\zeta \omega } }} \right )^{- 1}}\left ({{{\left ({\gamma \,+\, 1} \right )}^{- 1}} \,-\, {{\left ({\gamma \,+\, {} \tfrac {{{\lambda _{2}}\zeta \omega } }{{{\lambda _{1}}}}} \right )}^{- 1}}} \right )\). Then, using [15, Eq.(3.383.10)], we obtain Eq. 27. In the case of λ 1 = λ 2 ζ ω, we obtain Eq. 28 with the help of [15, Eq. (3.353.2)].
1.2 D.2 Calculation for the TAS scheme
The result for the TAS scheme can be obtained by replacing \({F_{{X_{1}}}}\left ({{\lambda _{1}},N;x} \right )\) and \({f_{{X_{2}}}}\left ({{\lambda _{2}};x} \right )\) in Eq. 50 with F Y (λ 1,N; x) and f(λ 2; x), respectively, and using the same step as in Appendix D.1.
1.3 D.3 Calculation for the MRT scheme
Replacing \({F_{{X_{1}}}}\left ({{\lambda _{1}},N;x} \right )\) and \({f_{{X_{2}}}}\left ({{\lambda _{2}};x} \right )\) in Eq. 50 with F Z (λ 1,N; x) and f(λ 2; x), respectively, and using [15, Eq.(8.350.2)], Eq. 50 can be expressed as
Substituting Eq. 53 into Eq. 26, we have the following:
where \(\mathcal {I}\left (\gamma \right ) = {\left ({1 + \gamma } \right )^{- 1}}{\left ({\tfrac {{{\lambda _{1}}}}{{\zeta \omega } }\gamma + {\lambda _{2}}} \right )^{- k - 1}}\).
In the case of λ 1≠λ 2 ζ ω, \(\mathcal {I}\left (\gamma \right )\) can be decomposed using partial fraction decomposition as follows.
Substituting Eq. 55 into Eq. 54 and using [15, Eq.(3.383.10) and Eq.(9.211.4)], we obtain Eq. 31.
In the case of λ 1 = λ 2 ζ ω, \(\mathcal {I}\left (\gamma \right ) = {\left ({\tfrac {{\zeta \omega } }{{{\lambda _{1}}}}} \right )^{k + 1}}{({\gamma + 1})^{- k - 2}}\). Then, with the help of [15, Eq. (9.211.4)], we obtain Eq. 32.
Rights and permissions
About this article
Cite this article
Tuan, V., Kong, H. Secure communication via an energy-harvesting untrusted relay with imperfect CSI. Ann. Telecommun. 73, 341–352 (2018). https://doi.org/10.1007/s12243-017-0604-5
Received:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s12243-017-0604-5