Abstract
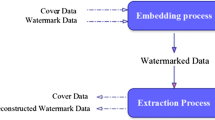
This paper proposes a novel fragile watermarking approach for digital image tamper localization (TL) along with the self-recovery (SR) capability. The host image is first divided into blocks of size 4 × 4 and then, singular value decomposition is performed on each block. The trace of singular matrix is used to compute the TL bits for each block. These 4 × 4 blocks are further divided into blocks of size 2 × 2 to compute the SR information. This SR information is also used for 2nd level of tamper detection in order to enhance the resolution of TL. Proposed scheme implements a self-embedding of TL bits and mapped embedding of SR bits and for that, block mapping is performed. The encrypted combination of both the codes (TL of parent block + SR of mapped block) is inserted in the 1st and 2nd least significant bits of the parent block. Encryption of watermark bits (unique for each watermarked image) helps it to sustain the block based attacks (vector quantization, collage and four scanning attack). Whereas; two level of authentication helps it to sustain content only and constant average attack. The scheme provides an average detection rate of more than 99.5 % and average recovery of 28 dB for a 50 % tampering. The proposed scheme shows a superior performance, when it is compared with the earlier proposed schemes.

















Similar content being viewed by others
References
Matsuo T, Kurosawa K (2004) On parallel hash functions based on block-ciphers. IEICE Trans Fundam Electron Commun Comput Sci 87(1):67–74
Li N, Wenliang D, Boneh D (2005) Oblivious signature based envelope. Distrib Comput 17(4):293–302
Yeung MM, Mintzer F (1997) An invisible watermarking technique for image verification. Proc IEEE Int Conf Image Process 2:680–683
Wong PW, Memon N (2001) Secret and public key image watermarking schemes for image authentication and ownership verification. IEEE Trans Image Process 10(10):1593–1601
Suthaharan S (2004) Fragile image watermarking using a gradient image for improved localization and security. Pattern Recogn Lett 25(16):1893–1903
Chun-Shien Lu and H-YM Liao (2003) Structural digital signature for image authentication: an incidental distortion resistant scheme. IEEE Trans Multimed 5(2):161–173
Walton S (1995) Information authentication for a slippery new age. Dr Dobbs J 20:18–26
Liu S-H, Yao H-X, Gao W, Liu Y-L (2007) An image fragile watermark scheme based on chaotic image pattern and pixel-pairs. Appl Math Comput 185(2):869–882
Memon N, Shende S, Wong PW (1999) On the security of the Yeung-Mintzer authentication watermark. In: Is and TS Pics conference. Society for imaging science & technology, pp 301–306
Li C-T, Yuan Y (2006) Digital watermarking scheme exploiting nondeterministic dependence for image authentication. Opt Eng 45(12):127001
Chang CC, Hu YS, Lu TC (2006) A watermarking-based image ownership and tampering authentication scheme. Pattern Recogn Lett 27(5):439–446
Chen WC, Wang MS (2009) A fuzzy c-means clustering-based fragile watermarking scheme for image authentication. Expert Syst Appl 36:1300–1307
Holliman M, Memon N (2000) Counterfeiting attacks on oblivious block-wise independent invisible watermarking schemes. IEEE Trans Image Process 9(3):432–441
Rawat S, Raman B (2011) A chaotic system based fragile watermarking scheme for image tamper detection. AEU Int J Electron Commun 65:840–847
Zhang X, Wang S (2007) Statistical fragile watermarking capable of locating individual tampered pixels. IEEE Signal Process Lett 14:727–730
Rosales-Roldan L, Cedillo-Hernandez M, Nakano-Miyatake M, Perez-Meana H, Kurkoski B (2013) Watermarking based image authentication with recovery capability using halftoning technique. Signal Process Image Commun 28(1):69–83
Wang L-J, Syue M-Y (2013) A wavelet based multipurpose watermarking for image authentication and recovery. Int J Commun 2(4)
Qian Z, Zhao L (2012) A flexible scheme of self-recovery for digital image protection. Int J Comput Sci 9:6
Wang M-S, Chen W-C (2007) A majority-voting based watermarking scheme for color image tamper detection and recovery. Comput Stand Interfaces 29(5):561–570
Yuan H, Zhang X-P (2006) Multiscale fragile watermarking based on the Gaussian mixture model. IEEE Trans Image Process 15(10):3189–3200
Lin PL, Hsieh C-K, Huang P-W (2005) A hierarchical digital watermarking method for image tamper detection and recovery. Pattern Recogn 38(12):2519–2529
Wu H-C, Chang C-C (2002) Detection and restoration of tampered JPEG compressed images. J Syst Softw 64(2):151–161
Lee T-Y, Lin SD (2008) Dual watermark for image tamper detection and recovery. Pattern Recogn 41(11):3497–3506
Huang S-C, Jiang C-F (2012) A color image authentication and recovery method using block truncation code embedding [J]. J Mar Sci Technol 20(1):49–55
Patra B, Patra JC (2012) Crt-based fragile self-recovery watermarking scheme for image authentication and recovery. In: IEEE international symposium on intelligent signal processing and communication systems (ISPACS2012), pp 430–435
Bravo-Solorio S, Nandi AK (2011) Secure fragile watermarking method for image authentication with improved tampering localisation and self-recovery capabilities. Signal Process 91(4):728–739
Tong X, Liu Y, Zhang M, Chen Y (2013) A novel chaos based fragile watermarking for image tampering detection and self-recovery. Signal Process Image Commun 28(3):301–308
Holliman M, Memon N (2000) Counterfeiting attacks on oblivious block- wise independent invisible watermarking schemes. IEEE Trans Image Process 9(3):432–441
Chang C-C, Fan Y-H, Tai W-L (2008) Four-scanning attack on hierarchical digital watermarking method for image tamper detection and recovery. Pattern Recogn 41(2):654–661
Ansari IA, Pant M, Neri F (2014) Analysis of gray scale watermark in RGB host using SVD and PSO. In: IEEE symposium on computational intelligence for multimedia, signal and vision processing (CIMSIVP), pp 1–7
Ansari IA, Pant M (2015) SVD watermarking: particle swarm optimization of scaling factors to increase the quality of watermark. In: Springer India proceedings of fourth international conference on soft computing for problem solving, pp 205–214
Agoyi M, Çelebi E, Anbarjafari G (2014) A watermarking algorithm based on chirp z-transform, discrete wavelet transform, and singular value decomposition. SIViP 9(3):735–745
Sun R, Sun H, Yao T (2002) A SVD-and quantization based semi-fragile watermarking technique for image authentication. In: IEEE 6th international conference on signal processing, vol 2. pp 1592–1595
Acknowledgments
This work was supported by Ministry of Human Resource Development, India and IKRI (India Korea Research Internship) program; jointly supported by Department of Science and Technology, India and Ministry of Science, ICT and Future Planning of the Republic of Korea.
Author information
Authors and Affiliations
Corresponding author
Rights and permissions
About this article
Cite this article
Ansari, I.A., Pant, M. & Ahn, C.W. SVD based fragile watermarking scheme for tamper localization and self-recovery. Int. J. Mach. Learn. & Cyber. 7, 1225–1239 (2016). https://doi.org/10.1007/s13042-015-0455-1
Received:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s13042-015-0455-1