Abstract
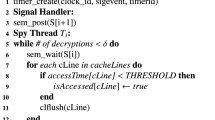
Several successful cache-based attacks have provided strong impetus for developing side channel resistant software implementations of AES. One of the best-known countermeasures—use of a “minimalist” 256-byte look-up table—has been employed in the latest (assembly language) versions. Software and hardware pre-fetching and out-of-order execution in modern processors have served to further shrink the attack surface. Despite these odds, we devise and implement two strategies to retrieve the complete AES key. The first uses adaptively chosen plaintext and random plaintext in a 2-round attack. The second strategy employs only about 50 blocks of random plaintext in a novel single round attack. The attack can be extended to spying on table accesses during decryption in a ciphertext-only attack. We also present an analytical model to explain the effect of false positives and false negatives and capture various practical tradeoffs involving number of blocks of plaintext, offline computation time for key retrieval and success probability.



Similar content being viewed by others
Notes
When we targeted lines 0, 1, or 2, we observed that lines 1, 2, or 3 respectively would be pre-fetched by the hardware causing ambiguity. But, when we targeted line 3, we noticed that line 4 was pre-fetched. That, however, did not affect our results since line 4 is not part of the lookup table.
References
Biryukov A, Dunkelman O, Keller N, Khovratovich D, Shamir A (2009) Key recovery attacks of practical complexity on AES variants with up to 10 rounds., https://eprint.iacr.org/2009/374
Bogdanov A, Khovratovich D, Rechberger C (2011) Biclique cryptanalysis of the full AES. In: International conference on the theory and application of cryptology and information security. Springer, pp 344–371
Gilbert H, Peyrin T (2009) Super-Sbox cryptanalysis: improved attacks for AES-like permutations. https://eprint.iacr.org/2009/531
Tao B, Wu H (2015) Improving the biclique cryptanalysis of AES. In: Australasian conference on information security and privacy. Springer, pp 39–56
OpenSSL Software Foundation OpenSSL Project, https://www.openssl.org/
Ashokkumar C, Giri RP, Menezes B (2016) Highly efficient algorithms for AES key retrieval in cache access attacks. In: 2016 IEEE European symposium on security and privacy (EuroS P), pp 261–275
RedHat (2014) It’s all a question of time - AES timing attacks on OpenSSL., https://access.redhat.com/blogs/766093/posts/1976303
Irazoqui G, Inci MS, Eisenbarth T, Sunar B (2014) Wait a minute! A fast, Cross-VM attack on AES. In: Research in attacks, intrusions and defenses. Springer, pp 299–319
Tromer E, Osvik D, Shamir A (2010) Efficient cache attacks on AES and countermeasures. J Cryptol 23(1):37–71
Gullasch D, Bangerter E, Krenn S (2011) Cache games – bringing access-based cache attacks on AES to practice. In: Proceedings of the 2011 IEEE symposium on security and privacy, Washington, DC, USA: IEEE Computer Society SP ’11, pp 490–505
Apecechea GI, Inci MS, Eisenbarth T, Sunar B (2014) Fine grain cross-VM attacks on Xen and VMware are possible!. IACR Cryptology ePrint Archive, 248
Osvik D, Shamir A, Tromer E (2006) Cache attacks and countermeasures: the case of AES. In: Pointcheval D (ed) Topics in cryptology CT-RSA 2006. Vol. 3860 of Lecture notes in computer science, Springer, pp 1–20
Bernstein DJ (2005) Cache-timing attacks on AES
Acıiçmez O, Brumley BB, Grabher P (2010) New results on instruction cache attacks. In: Cryptographic hardware and embedded systems, CHES 2010. Springer, pp 110–124
Neve M, Seifert JP, Wang Z (2006) A refined look at Bernstein’s AES side-channel analysis. In: Proceedings of the ACM symposium on information, computer and communications security. ACM, pp 369–369
Page D (2002) Theoretical use of cache memory as a cryptanalytic side-channel. IACR Cryptology ePrint Archive, 169
Yarom Y, Falkner KE (2013) Flush+ reload: a high resolution, low noise, L3 cache side-channel attack. IACR cryptology ePrint Archive, 448
Bhattacharya S, Rebeiro C, Mukhopadhyay D (2016) A formal security analysis of even-odd sequential prefetching in profiled cache-timing attacks. In: Proceedings of the hardware and architectural support for security and privacy 2016, ACM, p 6
Intel Corporation (2016) Intel® 64 and IA-32 architectures optimization reference manual. , number 248966-033, 2016
Hu WM (1992) Lattice scheduling and covert channels. In: Proceedings of the IEEE symposium on security and privacy, Washington, DC, USA: IEEE Computer Society SP ’92, pp 52– 61
Kocher PC (1996) Timing attacks on implementations of Diffie-Hellman, RSA, DSS, and other systems. In: Proceedings of the 16th annual international cryptology conference on advances in cryptology, London, UK: Springer CRYPTO ’96, pp 104– 113
Kelsey J, Schneier B, Wagner D, Hall C (2000) Side channel cryptanalysis of product ciphers. J. Comput. Secur. 8:141–158
Neve M, Seifert JP (2006) Advances on access-driven cache attacks on AES. In: International workshop on selected areas in cryptography. Springer, pp 147–162
Irazoqui G, Eisenbarth T, Sunar B (2015) S$A: a shared cache attack that works across cores and defies VM Sandboxing–and its application to AES. In: IEEE symposium on security and privacy. IEEE, pp 591–604
Liu F, Yarom Y, Ge Q, Heiser G, Lee RB (2015) Last-level cache side-channel attacks are practical. In: IEEE symposium on security and privacy, pp 605–622
Kayaalp M, Abu-Ghazaleh N, Ponomarev D, Jaleel A (2016) A high-resolution side-channel attack on last-level cache. In: Proceedings of the 53rd annual design automation conference. ACM, p 72
Götzfried J, Eckert M, Schinzel S, Müller T (2017) Cache attacks on Intel SGX. In: Proceedings of the 10th European workshop on systems security. ACM, p 2
Moghimi A, Irazoqui G, Eisenbarth T (2017) CacheZoom: How SGX amplifies the power of cache attacks. In: International conference on cryptographic hardware and embedded systems. Springer, pp 69–90
Author information
Authors and Affiliations
Corresponding author
Additional information
Publisher’s Note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Rights and permissions
About this article
Cite this article
C., A., Roy, B., Venkatesh, M.B.S. et al. “S-Box” Implementation of AES Is Not Side Channel Resistant. J Hardw Syst Secur 4, 86–97 (2020). https://doi.org/10.1007/s41635-019-00082-w
Received:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s41635-019-00082-w