Abstract
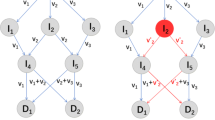
Network coding can save wireless network resources and is very fast in comparison with traditional routing. In real application scenarios, network coding is vulnerable to pollution attacks and forgery attacks. To solve these problems, the certificateless broadcast multi-signature for network coding (NC-CLBMS) method is devised, where each source node user generates a multi-signature about the message vector, and the intermediate node linearly combines the received data. NC-CLBMS is a multi-source multi-signature method with anti-pollution and anti-forgery advantages; moreover, it has a fixed signature length and its computation efficiency is very high. NC-CLBMS has extensive application prospects in unmanned aerial vehicle (UAV) communication networks, fifth-generation wireless networks, wireless sensor networks, mobile wireless networks, and Internet of Vehicles.
摘要
比起具有转储功能的传统路由技术, 网络编码能节省网络资源且速度快. 但在实际应用场景中, 网络编码容易受到污染攻击和伪造攻击. 本文针对这些问题提出面向网络编码的无证书广播多重签名 (NC-CLBMS) 方法, 每个源节点用户生成对消息向量的多重签名, 中间节点将接收到的数据线性组合. NC-CLBMS 是一种多源的多重签名方法, 具有抗污染和防止伪造攻击的功能; 此外, 它还具有固定的签名长度和较高的计算效率. 本文设计的 NC-CLBMS 在无人机通信网络、 5G 无线网络、 无线传感器网络、 移动无线网络和车联网等方面具有广泛应用前景.
Similar content being viewed by others
References
Ahlswede R, Cai N, Li SYR, et al., 2000. Network information flow. IEEE Trans Inform Theory, 46(4):1204–1216. https://doi.org/10.1109/18.850663
Al-Kofahi OM, Kamal AE, 2009. Network coding-based protection of many-to-one wireless flows. IEEE J Sel Areas Commun, 27(5):797–813. https://doi.org/10.1109/JSAC.2009.090619
Li P, Guo S, Yu S, et al., 2012. CodePipe: an opportunistic feeding and routing protocol for reliable multicast with pipelined network coding. Proc IEEE INFOCOM, p. 100–108. https://doi.org/10.1109/INFCOM.2012.6195456
Li SH, Mei ZH, 2016. Homomorphic signature scheme for network coding against inter-generation pollution attacks. Comput Technol Dev, 26(10):73–76 (in Chinese). https://doi.org/10.3969/j.issn.1673-629X.2016.10.016
Li ZP, Li BC, Lau LC, 2009. A constant bound on throughput improvement of multicast network coding in undirected networks. IEEE Trans Inform Theory, 55(3): 1016–1026. https://doi.org/10.1109/TIT.2008.2011516
Niu SF, Li WT, Wang CF, 2020. New efficient certificateless broadcast multi-signature scheme. Appl Res Comput, 37(8): 2464–2467 (in Chinese). https://doi.org/10.19734/j.issn.1001-3695.2019.02.0070
Papailiopoulos DS, Luo JQ, Dimakis AG, et al., 2012. Simple regenerating codes: network coding for cloud storage. Proc IEEE INFOCOM, p.2801–2805. https://doi.org/10.1109/INFCOM.2012.6195703
Peng TL, Shang T, Liu JW, 2015. Signature scheme for network coding against inter-generation pollution attacks. J Beijing Univ Aeronaut Astronaut, 41(4):721–726 (in Chinese). https://doi.org/10.13700/j.bh.1001-5965.2014.0478
Wang HP, Mei ZH, 2016. A scheme against pollution attacks based on secure network coding. Comput Technol Dev, 26(7):94–99 (in Chinese). https://doi.org/10.3969/j.issn.1673-629x.2016.07.020
Wang L, Zhang Z, Zhang H, et al., 2019. A RSA-based secure network coding scheme against multiple attacks. Comput Eng, 45(11):166–171 (in Chinese). https://doi.org/10.19678/j.issn.1000-3428.0052845
Xu CD, Wang HQ, 2021. Sequential multi-signature scheme based on blockchain. J Nanjing Univ Posts Telecommun (Nat Sci Ed), 41(2):85–94 (in Chinese). https://doi.org/10.14132/j.cnki.1673-5439.2021.02.010
Xu J, Liu YT, Xia GY, et al., 2016. Network coding based topology inference: a survey. Comput Sci, 43(S1): 242–248, 264 (in Chinese).
Yu HF, Gao XZ, 2019. Homomorphic ring signature scheme technology for multi-source network coding. Netinfo Secur, (2):36–42 (in Chinese). https://doi.org/10.3969/j.issn.1671-1122.2019.02.005
Yu HF, Li W, 2019. Homomorphic signature schemes for single-source and multi-source network coding. J Commun, 40(11):112–121 (in Chinese). https://doi.org/10.11959/j.issn.1000-436x.2019219
Yu HF, Li W, 2020. A certificateless signature for multi-source network coding. J Inform Secur Appl, 55:102655. https://doi.org/10.1016/j.jisa.2020.102655
Yu HF, Wang WK, 2021. Certificateless network coding ring signature scheme. Secur Commun Netw, 2021:8029644. https://doi.org/10.1155/2021/8029644
Zhou ZB, Xu L, 2016. Pollution-resistant network coding scheme based on digital signature. Comput Syst Appl, 25(6):185–190 (in Chinese). https://doi.org/10.15888/j.cnki.csa.005192
Author information
Authors and Affiliations
Contributions
Huifang YU devised the NC-CLBMS method and analyzed its security. Zhewei QI processed the data and analyzed the efficiency. Huifang YU drafted the paper. Huifang YU and Zhewei QI revised and finalized this paper.
Corresponding author
Ethics declarations
Huifang YU and Zhewei QI declare that they have no conflict of interest.
Additional information
Project supported by the Key Project of Natural Science Basis Research Plan of Shaanxi Province, China (No. 2020JZ-54)
Rights and permissions
About this article
Cite this article
Yu, H., Qi, Z. Certificateless broadcast multi-signature for network coding. Front Inform Technol Electron Eng 23, 1369–1377 (2022). https://doi.org/10.1631/FITEE.2200271
Received:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1631/FITEE.2200271