Abstract
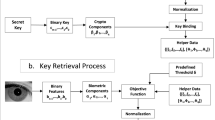
We propose a new biometric identity based encryption scheme (Bio-IBE), in which user biometric information is used to generate the public key with a fuzzy extractor. This is the first Bio-IBE scheme that achieves constant size ciphertext. This is also a scheme that is secure against the adaptive chosen ciphertext attack (CCA2). Details are presented along with a discussion of Shamir’s threshold secret sharing and fuzzy extraction of biometrics, which is based on error correction codes. We also define a security model and prove that the security of the proposed scheme is reduced to the decisional bilinear Diffie-Hellman (DBDH) assumption. The comparison shows that the proposed scheme has better efficiency and stronger security compared with the available Bio-IBE schemes.
Similar content being viewed by others
References
Baek, J., Susilo, W., Zhou, J.Y., 2007. New Constructions of Fuzzy Identity-Based Encryption. Proc. 2nd ACM Symp. on Information Computer and Communications Security, p.368–370. [doi:10.1145/1229285.1229330]
Boneh, D., Boyen, X., 2004. Efficient Selective-ID Secure Identity-Based Encryption without Random Oracles. Proc. EUROCRYPT, p.223–238.
Boneh, D., Franklin, M.K., 2001. Identity-Based Encryption from the Weil Pairing. Proc. CRYPTO, p.213–229.
Burnett, A., Byrne, F., Dowling, T., Duffy, A., 2007. A biometric identity based signature scheme. Int. J. Network Secur., 5(3):317–326.
Cha, J.C, Cheon, J.H., 2003. An Identity-Based Signature from Gap Diffie-Hellman Groups. Proc. Public Key Cryptography, p.18–30.
Cheon, J.H., 2006. Security Analysis of the Strong Diffie-Hellman Problem. Proc. EUROCRYPT, p.1–11.
Dodis, Y., Ostrovsky, R., Reyzin, L., Smith, A., 2008. Fuzzy extractors: how to generate strong keys from biometrics and other noisy data. SIAM J. Comput., 38(1):97–139. [doi:10.1137/060651380]
Fang, L., Wang, J., Ren, Y., Xia, J., Bian, S., 2008. Chosen ciphertext secure fuzzy identity based encryption without ROM. J. Shanghai Jiao Tong Univ. (Sci.), 13(6):646–650. [doi:10.1007/s12204-008-0646-y]
Juels, A., Wattenberg, M., 1999. A Fuzzy Commitment Scheme. ACM Conf. on Computer and Communications Security, p.28–36.
Li, X.M., Yang, B., Guo, Y.B., 2009. Fuzzy Identity Based Encryption Scheme with Some Assigned Attributes. Proc. 5th Int. Conf. on Information Assurance and Security, p.133–136. [doi:10.1109/IAS.2009.145]
Ren, Y.L., Gu, D.W., Wang, S.Z., Zhang, X.P., 2010. New fuzzy identity-based encryption in the standard model. Informatica, 21(3):393–407.
Sahai, A., Waters, B., 2005. Fuzzy Identity-Based Encryption. Proc. EUROCRYPT, p.457–473.
Sarier, N.D., 2008. A New Biometric Identity Based Encryption Scheme. Proc. ICYCS, p.2061–2066.
Sarier, N.D., 2010. Generic Constructions of Biometric Identity Based Encryption Systems. Proc. WISTP, p.90–105.
Sarier, N.D., 2011. A new biometric identity based encryption scheme secure against DoS attacks. Secur. Commun. Networks, 4(1):23–32. [doi:10.1002/sec.162]
Shamir, A., 1984. Identity-Based Cryptosystems and Signature Schemes. Proc. Crypto, p.47–53.
Author information
Authors and Affiliations
Corresponding author
Additional information
Project supported by the National Basic Research Program (973) of China (No. 2007CB311201) and the National Natural Science Foundation of China (Nos. 60970119, 60803149, 60833008, and 61072067)
Rights and permissions
About this article
Cite this article
Yang, Y., Hu, Yp., Zhang, Ly. et al. CCA2 secure biometric identity based encryption with constant-size ciphertext. J. Zhejiang Univ. - Sci. C 12, 819–827 (2011). https://doi.org/10.1631/jzus.C1000429
Received:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1631/jzus.C1000429