Abstract—
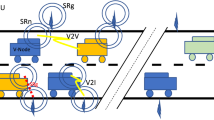
This article considers ensuring protection of Vehicular Ad-Hoc Networks (VANET) against malicious nodes. Characteristic performance features of VANETs and threats are analyzed, and current attacks identified. The proposed approach to security provision relies on radial basis neural networks and makes it possible to identify malicious nodes by indicators of behavior.


Similar content being viewed by others
REFERENCES
Sabahi, F., Impact of threats on vehicular adhoc network security, Int. J. Comput. Theory Eng., 2012, vol. 4, no. 5, p. 840.
Zahariadis, T., et al., Energy-aware secure routing for large wireless sensor networks, WSEAS Trans. Commun., 2009, vol. 8, no. 9, pp. 981–991.
Awad, M., et al., Prediction of time series using RBF neural networks: A new approach of clustering, Int. Arab J. Inf. Technol., 2009, vol. 6, no. 2, pp. 138–143.
Haykin, S., et al., Neural Networks and Learning Machines, Upper Saddle River, NJ: Pearson, 2009, vol. 3.
Jirina, M., Radial Basis Function Neural Network with Example Weights and LMS Linear Regression Weight Setting, 2001.
Kalinin, M., Krundyshev, V., Zegzhda, P., and Belenko, V., Network security architectures for VANET, Proceedings of the 10th International Conference on Security of Information and Networks, ACM, 2017, pp. 73–79.
ACKNOWLEDGMENTS
The project results are achieved using the resources of supercomputer center of Peter the Great St.Petersburg Polytechnic University – SCC “Polytechnichesky” (www.spbstu.ru).
The project is financially supported by Ministry of Science and Higher Education of the Russian Federation, Federal Program “Researching and Development in Priority Directions of Scientific and Technological Sphere in Russia within 2014–2020” (Contract no. 14.575.21.0131, September 26, 2017, unique identifier RFMEFI57517X0131).
Author information
Authors and Affiliations
Corresponding authors
Additional information
Translated by S. Kuznetsov
About this article
Cite this article
Ovasapyan, T.D., Moskvin, D.A. & Kalinin, M.O. Using Neural Networks to Detect Internal Intruders in VANETs. Aut. Control Comp. Sci. 52, 954–958 (2018). https://doi.org/10.3103/S0146411618080199
Received:
Published:
Issue Date:
DOI: https://doi.org/10.3103/S0146411618080199