Abstract
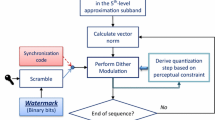
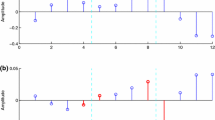
Rational Dither Modulation has been proposed as an effective QIM watermarking algorithm which is robust against value-metric scaling. Invariance is obtained by quantizing a rational function of the host features instead of the features themselves. In this paper we propose a vector extension of the basic RDM scheme. Specifically, a sequence of feature ratios is quantized vectorially with the aid of a properly designed dirty trellis code. A fast sub-optimum embedding algorithm is proposed ensuring fast watermark insertion and good distortion properties. Preliminary results show that a significant advantage is obtained with respect to conventional RDM.
Preview
Unable to display preview. Download preview PDF.
Similar content being viewed by others
References
Chen, B., Wornell, G.: Quantization index modulation: a class of provably good methods for digital watermarking and information embedding. IEEE Trans. on Information Theory 47, 1423–1443 (2001)
Eggers, J.J., Bäuml, R., Tzschoppe, R., Girod, B.: Scalar Costa scheme for information embedding. IEEE Trans. on Signal Processing 4 (2003)
Bartolini, F., Barni, M., Piva, A.: Performance analysis of st-dm watermarking in presence of non-additive attacks. IEEE Trans. on Signal Processing 52, 2965–2974 (2004)
Eggers, J.J., Bäuml, R., Girod, B.: Estimation of amplitude modifications before SCS watermark detection. In: Wong, P.W., Delp, E.J. (eds.) Security and Watermarking of Multimedia Contents IV, San Jose, CA. Proc. SPIE, vol. 4675, pp. 387–398 (2002)
Miller, M.L., Doerr, G.J., Cox, I.J.: Applying informed coding and embedding to design a robust, high capacity, watermark. IEEE Trans. on Image Processing 13, 792–807 (2004)
Abrardo, A., Barni, M.: Informed watermarking by means of orthogonal and pseudo-random dirty paper coding. IEEE Trans. on Signal Processing 53, 824–833 (2005)
Oostven, J., Kalker, T., Staring, M.: Adaptive quantization watermarking. In: Wong, P.W., Delp, E.J. (eds.) Security, Steganography, and Watermarking of Multimedia Contents VI, San Jose, CA, USA. Proc. SPIE, vol. 5306, pp. 296–303 (2004)
Perez-Gonzalez, F., Mosquera, C., Barni, M., Abrardo, A.: Rational dither modulation: a novel data-hiding method robust to value-metric scaling attacks. In: MMSP 2004, IEEE Workshop on Multimedia Signal Processing, Siena, Italy (2004)
Perez-Gonzalez, F., Mosquera, C., Barni, M., Abrardo, A.: Ensuring gain invariance in high-rate data-hiding. In: Wong, P.W., Delp, E.J. (eds.) Security, Steganography, and Watermarking of Multimedia Contents VII, San Jose, CA, USA. Proc. SPIE, vol. 5681 (2005)
Liu, T., Venkatesan, R., Mihcak, M.K.: Scale-invariant image watermarking via optimization algorithms for quantizing randomized statistics. In: Proceedings of the ACM Multimedia and Security Workshop, Magdeburg, Germany (2004)
Cox, I.J., Kilian, J., Leighton, T., Shamoon, T.: Secure spread spectrum watermarking for multimedia. IEEE Trans. on Image Processing 6, 1673–1687 (1997)
Malvar, H.S., Florencio, D.A.F.: Improved spread spectrum: a new modulation technique for robust watermarking. IEEE Trans. on Image Processing 51, 898–905 (2003)
Miller, M.L., Doerr, G.J., Cox, I.J.: Dirty-paper trellis codes for watermarking. In: Proc. 9th IEEE Int. Conf. on Image Processing, ICIP 2002, Rochester, NY, vol. II, pp. 129–132 (2002)
Proakis, J.G.: Digital Communications, 2nd edn. McGraw-Hill, New York (1989)
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2005 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Abrardo, A., Barni, M., Pérez-González, F., Mosquera, C. (2005). Trellis-Coded Rational Dither Modulation for Digital Watermarking. In: Barni, M., Cox, I., Kalker, T., Kim, HJ. (eds) Digital Watermarking. IWDW 2005. Lecture Notes in Computer Science, vol 3710. Springer, Berlin, Heidelberg. https://doi.org/10.1007/11551492_27
Download citation
DOI: https://doi.org/10.1007/11551492_27
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-540-28768-1
Online ISBN: 978-3-540-32052-4
eBook Packages: Computer ScienceComputer Science (R0)