Abstract
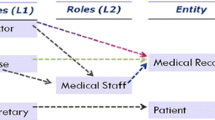
In this paper, we present a rule-based approach to fine-grained data-dependent access control for database systems. Authorization rules in this framework are described in a logical language that allows us to specify policies systematically and easily. The language expresses authorization rules based on the values, types, and semantics of data elements common to the relational data model. We demonstrate the applicability of our approach by describing several data-dependent policies using an example drawn from a medical information system.
Preview
Unable to display preview. Download preview PDF.
Similar content being viewed by others
References
Anderson, R.J.: A Security Policy Model for Clinical Information Systems. In: Proc. IEEE Symp. on Security and Privacy, pp. 30–45 (1996)
Bertino, E., Jajodia, S., Samarati, P.: Supporting Multiple Access Control Policies in Data-base Systems. In: Proc. IEEE Symp. on Security and Privacy, pp. 94–108 (1996)
Griffiths, P.P., Wade, B.W.: An Authorization Mechanism for a Relational Database System. ACM Transactions on Database Systems 1(3), 242–255 (1976)
Jajodia, S., Samarati, P., Subrahmanian, V.S., Bertino, E.: A Unified Framework for Enforcing Multiple Access Control Policies. In: Proc. ACM SIGMOD, pp. 474–485 (1997)
Rizvi, S., Mendelzon, A.O., Sudarshan, S., Roy, P.: Extending Query Rewriting Techniques for Fine-Grained Access Control. In: Proc. ACM SIGMOD, Paris, France, pp. 551–562 (2004)
Rosenthal, A., Winslett, M.: Security of Shared Data in Large Systems: State of the Art and Research Directions. In: Proc. of ACM SIGMOD, pp. 962–964 (2004)
Ullman, J.: Principles of Database and Knowledge-Base Systems, vol. 1&2. Computer Science Press (1988)
Yu, T.: Fine-grained Access Control. In: Fall Privacy Place Workshop Proceedings, http://theprivacyplace.org/Workshops/fall_2004.html
Zhang, L., Ahn, G., Chu, B.: A Role-Based Delegation Framework for Healthcare Information Systems. In: Proc. ACM SACMAT, pp. 125–134 (2002)
The Virtual Private Database in Oracle9ir2: An Oracle Technical White Paper (2002), http://www.oracle.com/technology/deploy/security/oracle9ir2/pdf/VPD9ir2twp.pdf
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2005 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Purevjii, BO., Aritsugi, M., Imai, S., Kanamori, Y., Pancake, C.M. (2005). Protecting Personal Data with Various Granularities: A Logic-Based Access Control Approach. In: Hao, Y., et al. Computational Intelligence and Security. CIS 2005. Lecture Notes in Computer Science(), vol 3802. Springer, Berlin, Heidelberg. https://doi.org/10.1007/11596981_81
Download citation
DOI: https://doi.org/10.1007/11596981_81
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-540-30819-5
Online ISBN: 978-3-540-31598-8
eBook Packages: Computer ScienceComputer Science (R0)