Abstract
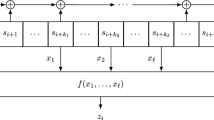
We present an algebraic attack approach to a family of irregularly clock-controlled bit-based linear feedback shift register systems. In the general set-up, we assume that the output bit of one shift register controls the clocking of other registers in the system and produces a family of equations relating the output bits to the internal state bits. We then apply this general theory to four specific stream ciphers: the (strengthened) stop-and-go generator, the alternating step generator, the self-decimated generator and the step1/step2 generator. In the case of the strengthened stop-and-go generator and of the self-decimated generator, we obtain the initial state of the registers in a significantly faster time than any other known attack. In the other two situations, we do better than or as well as all attacks but the correlation attack. In all cases, we demonstrate that the degree of a functional relationship between the registers can be bounded by two. Finally, we determine the effective key length of all four systems.
Preview
Unable to display preview. Download preview PDF.
Similar content being viewed by others
References
Armknecht, F.: Improving Fast Algebraic Attacks. In: Roy, B., Meier, W. (eds.) FSE 2004. LNCS, vol. 3017, pp. 65–82. Springer, Heidelberg (2004)
Armknecht, F., Krause, M.: Algebraic attacks on combiners with memory. In: Boneh, D. (ed.) CRYPTO 2003. LNCS, vol. 2729, pp. 162–175. Springer, Heidelberg (2003)
Beth, T., Piper, F.: The stop-and-go generator. In: Beth, T., Cot, N., Ingemarsson, I. (eds.) EUROCRYPT 1984. LNCS, vol. 209, pp. 88–92. Springer, Heidelberg (1985)
Chambers, W.G., Gollmann, D.: Embedding attacks on step[1..D] clock controlled generators. Electronics Letters 36, 1771–1773 (2000)
Chambers, W.G., Gollmann, D.: Lock-in Effect in Cascades of Clock-Controlled Shift-Registers. In: Günther, C.G. (ed.) EUROCRYPT 1988. LNCS, vol. 330, pp. 331–343. Springer, Heidelberg (1988)
Cho, J.Y., Pieprzyk, J.: Algebraic Attacks on SOBER-t32 and SOBER-t16 without Stuttering. In: Roy, B., Meier, W. (eds.) FSE 2004. LNCS, vol. 3017, pp. 49–64. Springer, Heidelberg (2004)
Coppersmith, D.: Fast evaluation of logarithms in fields of characteristic two. IEEE Transactions on Information Theory 30(4), 587–593 (1984)
Courtois, N.T.: The security of hidden field equations (HFE). In: Naccache, D. (ed.) CT-RSA 2001. LNCS, vol. 2020, pp. 266–281. Springer, Heidelberg (2001)
Courtois, N.T.: Higher order correlation attacks, XL algorithm and cryptanalysis of toyocrypt. In: Lee, P.J., Lim, C.H. (eds.) ICISC 2002. LNCS, vol. 2587, pp. 182–199. Springer, Heidelberg (2003)
Courtois, N.: Algebraic attacks on combiners with memory and several outputs. Cryptology ePrint Archive, Report 2003/125 (2003)
Courtois, N.T.: Fast algebraic attacks on stream ciphers with linear feedback. In: Boneh, D. (ed.) CRYPTO 2003. LNCS, vol. 2729, pp. 176–194. Springer, Heidelberg (2003)
Courtois, N., Meier, W.: Algebraic attacks on stream cipher with linear feedback. In: Biham, E. (ed.) EUROCRYPT 2003. LNCS, vol. 2656, pp. 346–359. Springer, Heidelberg (2003)
Courtois, N.T., Pieprzyk, J.: Cryptanalysis of block ciphers with overdefined systems of equations. In: Zheng, Y. (ed.) ASIACRYPT 2002. LNCS, vol. 2501, pp. 267–287. Springer, Heidelberg (2002)
Golić, J.D., Menicocci, R.: Edit distance correlation attack on the alternating step generator. In: Kaliski Jr., B.S. (ed.) CRYPTO 1997. LNCS, vol. 1294, pp. 499–512. Springer, Heidelberg (1997)
Golić, J.Dj., Menicocci, R.: Correlation analysis of the alternating step generator. Des. Codes Cryptography 31(1), 51–74 (2004)
Gollmann, D., Chambers, W.G.: Clock-controlled shift registers: a review. IEEE Journal on Selected Areas in Communications 7, 525–533 (1989)
Günther, C.G.: Alternating step generators controlled by de Bruijn sequences. In: Price, W.L., Chaum, D. (eds.) EUROCRYPT 1987. LNCS, vol. 304, pp. 5–14. Springer, Heidelberg (1988)
Kanso, A.A.: Clock-Controlled Generators. PhD thesis, Royal Holloway and Bedford New College, University of London, Egham, London (1999)
Molland, H.: Improved Linear Consistency Attack on Irregular Clocked Keystream Generators. In: Roy, B., Meier, W. (eds.) FSE 2004. LNCS, vol. 3017, pp. 109–126. Springer, Heidelberg (2004)
Rueppel, R.A.: When shift registers clock themselves. In: Price, W.L., Chaum, D. (eds.) EUROCRYPT 1987. LNCS, vol. 304, pp. 53–64. Springer, Heidelberg (1988)
Rueppel, R.A.: Stream ciphers. In: Simmons, G.J. (ed.) Contemporary Cryptology: The Science of Information Integrity, IEEE Press, Los Alamitos (1992)
Rueppel, R.A. (ed.): Analysis and Design of Stream Ciphers. Springer, Berlin (1986)
Thomé, E.: Computation of discrete logarithms in \( \mathbb {F}_{2^{607}}\). In: Boyd, C. (ed.) ASIACRYPT 2001. LNCS, vol. 2248, pp. 107–124. Springer, Heidelberg (2001)
Wiedemann, D.H.: Solving sparse linear equations over finite fields. IEEE Transactions on Information Theory 32(1), 54–62 (1986)
Zeng, K., Yang, C.H., Rao, T.R.N.: An Improved Linear Syndrome Algorithm in Cryptanalysis with Applications. In: Menezes, A., Vanstone, S.A. (eds.) CRYPTO 1990. LNCS, vol. 537, pp. 34–47. Springer, Heidelberg (1991)
Zenner, E.: On the Efficiency of the Clock Control Guessing Attack. In: Lee, P.J., Lim, C.H. (eds.) ICISC 2002. LNCS, vol. 2587, pp. 200–212. Springer, Heidelberg (2003)
Zivkovic, M.V.: An algorithm for the initial state reconstruction of the clock-controlled shift register. IEEE Transactions on Information Theory 37(5), 1488 (1991)
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2006 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Al-Hinai, S., Batten, L., Colbert, B., Wong, K. (2006). Algebraic Attacks on Clock-Controlled Stream Ciphers. In: Batten, L.M., Safavi-Naini, R. (eds) Information Security and Privacy. ACISP 2006. Lecture Notes in Computer Science, vol 4058. Springer, Berlin, Heidelberg. https://doi.org/10.1007/11780656_1
Download citation
DOI: https://doi.org/10.1007/11780656_1
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-540-35458-1
Online ISBN: 978-3-540-35459-8
eBook Packages: Computer ScienceComputer Science (R0)