Abstract
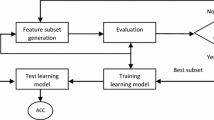
One of the essential tasks for building a network intrusion detection system might be to differentiate a salient feature subset from noisy and/or redundant features. Especially, in real-time environment too many features to be monitored deteriorate the system performance. In this paper, we focus on extracting robust feature subsets that maximizes inter-classes seperability with minimized subset size based on a genetic algorithm-based optimization, reducing both false positive and false negative errors by learning class-specific feature subsets. Experimental results show that the proposed approach is especially effective in detecting totally unknown attack patterns compared with single feature-subset model.
Preview
Unable to display preview. Download preview PDF.
Similar content being viewed by others
References
Chebrolu, S., Abraham, A., Thomas, J.: Feature deduction and ensemble design of intrusion detection systems. Computers & Security 24, 295–307 (2005)
Fayyad, U.M., Irani, K.B.: Multi-interval discretization of continuous-valued attributes for classification learning. In: Proc. of 13th International Joint Conf. on Artificial Intelligence, pp. 1022–1027 (1993)
Giacinto, G., Roli, F., Didaci, L.: Fusion of multiple classifiers for intrusion detection in computer networks. Pattern Recognition Letters 24, 1795–1803 (2003)
Han, S.J., Cho, S.-B.: Detecting intrusion with rule-based integration of multiple models. Computers & Security 22, 613–623 (2003)
Hansman, S., Hunt, R.: A Taxonomy of network and computer attacks. Computers & Security 24, 31–43 (2005)
Kim, S.H., Shin, S.W.: Identifying the impact of decision variables for nonlinear classification. Expert Systems With Applications 18, 201–214 (2000)
Langley, P., Sage, S.: Induction of Selective Bayesian classifiers. In: Proc. of the 10th Conference on Uncertainty in Artificial Intelligence, pp. 399–406 (1994)
Mahoney, M.V., Chan, P.K.: An analysis of the 1999 DARPA/Lincoln Laboratory evaluation data for network anomaly detection. In: Vigna, G., Krügel, C., Jonsson, E. (eds.) RAID 2003. LNCS, vol. 2820, pp. 220–237. Springer, Heidelberg (2003)
McHugh, J.: Testing intrusion detection systems: A critique of the 1998 and 1999 DARPA intrusion detection system evaluations as performed by Lincoln Laboratory. ACM Trans. Information System Security 3(4), 262–294 (2000)
Mukkamala, S., Sunga, A.H., Abraham, A.: Intrusion detection using an ensemble of intelligent paradigms. Journal of Network and Computer Applications 28, 167–182 (2005)
Punch, W.F., Goodman, E.D., et al.: Further research on feature selection and classification using genetic algorithms. In: Int. Conf. on Genetic Algorithms, pp. 557–564 (1993)
Stolfo, S., Fan, W., Lee, W., Prodromidis, A., Chan, P.K.: Cost-based Modeling for Fraud and Intrusion Dectection: Results from the JAM Project. In: DARPA Information Survivability Conference (2000)
Stolfo, S., Lee, W., Chan, P.K., Fan, W., Eskin, E.: Data mining-based intrusion detectors: An overview of the Columbia IDS project. ACM SIGMOD Record 30(4), 5–14 (2001)
Zhang, C., Jiang, J., Kamel, M.: A Intrusion detection using hierarchical neural networks. Pattern Recognition Letters, 779–791 (2005)
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2006 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Shin, S.W., Lee, C.H. (2006). Using Attack-Specific Feature Subsets for Network Intrusion Detection. In: Sattar, A., Kang, Bh. (eds) AI 2006: Advances in Artificial Intelligence. AI 2006. Lecture Notes in Computer Science(), vol 4304. Springer, Berlin, Heidelberg. https://doi.org/10.1007/11941439_34
Download citation
DOI: https://doi.org/10.1007/11941439_34
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-540-49787-5
Online ISBN: 978-3-540-49788-2
eBook Packages: Computer ScienceComputer Science (R0)