Abstract
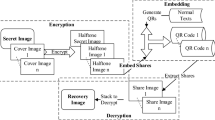
In conventional Visual Cryptography, the generated transparency is either meaningless or meaningful. However, even if the generated transparencies are meaningful, they are just with rough look of a meaningful picture. In this paper, the encoded transparencies are also QR-codes that can be decoded by common QR-code scanner that can be ained in mobile phone. Therefore, people can get more information of this transparencies by scanning the QR-code transparencies.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Similar content being viewed by others
References
Naor, M., Shamir, A.: Visual cryptography. In: Advances in Cryptology—Eurocrypt’94, pp. 1–12. Springer, Berlin (1995)
Chang, C.C., Hwang, R.J.: Hiding a picture in two pictures. Opt. Eng. 40(3), 342–351 (2001)
Ateniese, G., Blundo, C., De Santis, A., Stinson, D.R.: Extended schemes for visual cryptography. Theoret. Comput. Sci. 250, 143–161 (2001)
Hou, Y.C., Wu, J.H.: An extended visual cryptography scheme for concealing color images. In: Proc. The 5th Conference on Information Management and Police Administrative Practice, Taoyuan, Taiwan, pp. 62–69 (2001)
Chen, S.-K.: Friendly progressive visual secret sharing using generalized random grids. Opt. Eng. 48(11), 117001.1–117001.7 (2009)
Fang, W.P.: Friendly progressive visual secret sharing. Pattern Recogn. 41(4), 1410–1414 (2008)
Tan, J.S.: QR code. Synth. J., Sec. 3, pp. 59–78 (2008)
Huang, H.C., Chang, F.C., Fang, W.C.: Reversible data hiding with histogram-based difference expansion for QR code applications. IEEE Trans. Consum. Electron. 57(2), 779–787 (2011)
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2019 Springer Nature Switzerland AG
About this paper
Cite this paper
Chen, SK., Ti, YW. (2019). Visual Cryptography with QR-Code Transparencies. In: Pan, JS., Ito, A., Tsai, PW., Jain, L. (eds) Recent Advances in Intelligent Information Hiding and Multimedia Signal Processing. IIH-MSP 2018. Smart Innovation, Systems and Technologies, vol 110. Springer, Cham. https://doi.org/10.1007/978-3-030-03748-2_3
Download citation
DOI: https://doi.org/10.1007/978-3-030-03748-2_3
Published:
Publisher Name: Springer, Cham
Print ISBN: 978-3-030-03747-5
Online ISBN: 978-3-030-03748-2
eBook Packages: Intelligent Technologies and RoboticsIntelligent Technologies and Robotics (R0)