Abstract
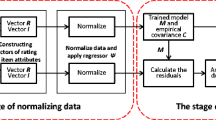
The recommendation systems have become an important tool to solve the problem of information overload. However, the recommendation system is greatly fragile as it relies heavily on behavior data of users. It is very easy for a host of malicious merchants to inject shilling attacks in order to control the recommendation results. Some papers on shilling attack have proposed the detection methods, but they ignored experimental performance of injecting a small number of attacks and time overhead. To solve above issues, we propose a novel detection method of shilling attack based on T-distribution over dynamic time intervals. Firstly, we proposed Dynamic Time Intervals to divide the rating history of items into multiple time windows; secondly, the T-distribution is employed to calculate the similarity between windows, and the feature of T-distribution is obvious to detect small samples; thirdly, abnormal windows are identified by analyzing the T value, time difference and rating actions quantity of each window; fourthly, abnormal rating actions are detected by analyzing rating mean of abnormal windows. Extensive experiments are conducted. Comparing with similar shilling detection approaches, the experimental results demonstrate the effectiveness of the proposed method.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Similar content being viewed by others
References
Yuan, J., Jin, Y., Liu, W., Wang, X.: Attention-based neural tag recommendation. In: Li, G., Yang, J., Gama, J., Natwichai, J., Tong, Y. (eds.) DASFAA 2019. LNCS, vol. 11447, pp. 350–365. Springer, Cham (2019). https://doi.org/10.1007/978-3-030-18579-4_21
Xu, K., Cai, Y., Min, H., Chen, J.: Top-N trustee recommendation with binary user trust feedback. In: Liu, C., Zou, L., Li, J. (eds.) DASFAA 2018. LNCS, vol. 10829, pp. 269–279. Springer, Cham (2018). https://doi.org/10.1007/978-3-319-91455-8_23
Yi, H., Niu, Z., Zhang, F., Li, X., Wang, Y.: Robust recommendation algorithm based on kernel principal component analysis and fuzzy C-means clustering. Wuhan Univ. J. Nat. Sci. 23(2), 111–119 (2018). https://doi.org/10.1007/s11859-018-1301-6
Kaur, P., Goel, S.: Shilling attack models in recommender system. In: 2016 International Conference on Inventive Computation Technologies. IEEE (2016)
Oh, H., Kim, S., Park, S., Zhou, M.: Can you trust online ratings? A mutual reinforcement model for trustworthy online rating systems. IEEE Trans. Syst. Man Cybern.: Syst. 45(12), 1564–1576 (2015)
Cheng, Z., Hurley, N.: Effective diverse and obfuscated attacks on model-based recommender systems. In: RecSys, New York, NY, USA, pp. 141–148 (2009)
Yu, J., Gao, M., Rong, W., Li, W., Xiong, Q., Wen, J.: Hybrid attacks on model-based social recommender systems. Physica A 483(2017), 171–181 (2017)
Zhang, S., Chakrabarti, A., Ford, J., Makedon, F.: Attack detection in time series for recommender systems. In: ACM SIGKDD International Conference on Knowledge Discovery and Data Mining, Philadelphia, Pennsylvania, USA, pp. 809–814, August 2006
Gao, M., Yuan, Q., Ling, B., Xiong, Q.: Detection of abnormal item based on time intervals for recommender systems. Sci. World J. 2014, 845–897 (2014)
Gao, M., Tian, R., Wen, J., Xiong, Q., Ling, B., Yang, L.: Item anomaly detection based on dynamic partition for time series in recommender systems. PLoS ONE 10(8), 135–155 (2015)
Chirita, P., Nejdl, W., Zamfir, C.: Preventing shilling attacks in online recommender systems. In: Seventh ACM International Workshop on Web Information and Data Management, Bremen, Germany, pp. 67–74 (2005)
Burke, R., Mobasher, B., Williams, C., Bhaumik, R.: Classification features for attack detection in collaborative recommender systems. In: ACM SIGKDD International Conference on Knowledge Discovery and Data Mining, Philadelphia, Pennsylvania, USA, pp. 542–547 (2006)
Gao, M., Li, X., Rong, W., Wen, J., Xiong, Q.: The performance of location aware shilling attacks in web service recommendation. Int. J. Web Serv. Res. 14(3), 53–66 (2017)
Wang, Y., Qian, L., Li, F., Zhang, L.: A comparative study on Shilling detection methods for trustworthy recommendations. J. Syst. Sci. Syst. Eng. 27(4), 458–478 (2018). https://doi.org/10.1007/s11518-018-5374-8
Li, W., Gao, M., Li, H., Zeng, J., Xiong, Q.: Shilling attack detection in recommender systems via selecting patterns analysis. IEICE Trans. Inf. Syst. E99.D(10), 2600–2611 (2016)
Fan, Y., Gao, M., Yu, J., Song, Y., Wang, X.: Detection of Shilling attack based on bayesian model and user embedding. In: International Conference on Tools with Artificial Intelligence, pp. 639–646. IEEE (2018)
Yang, Z., Cai, Z., Guan, X.: Estimating user behavior toward detecting anomalous ratings in rating systems. Knowl.-Based Syst. 111(2016), 144–158 (2016)
Zhang, F., Zhang, Z., Zhang, P., Wang, S.: UD-HMM: an unsupervised method for shilling attack detection based on hidden Markov model and hierarchical clustering. Knowl.-Based Syst. 148(2018), 146–166 (2018)
Wu, Z., Wu, J., Cao, J., Tao, D.: Hysad: a semi-supervised hybrid shilling attack detector for trustworthy product recommendation. In: Proceedings of the 18th International Conference on Knowledge Discovery and Data Mining, Beijing, China, pp. 985–993 (2012)
Zhang, L., Wu, Z., Cao, J.: Detecting spammer groups from product reviews: a partially supervised learning model. IEEE Access 6(2018), 2559–2567 (2018)
Shen, X., Wu, R.: Discussion on t-distribution and its application. Stat. Appl. 4(4), 319–334 (2015)
Acknowledgment
This work is supported by the National Nature Science Foundation of China (91646117, 61702368) and Natural Science Foundation of Tianjin (17JCYBJC15200, 18JCQNJC00700).
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2020 Springer Nature Switzerland AG
About this paper
Cite this paper
Yuan, W., Xiao, Y., Jiao, X., Sun, C., Zheng, W., Wang, H. (2020). A Novel Shilling Attack Detection Method Based on T-Distribution over the Dynamic Time Intervals. In: Nah, Y., Kim, C., Kim, SY., Moon, YS., Whang, S.E. (eds) Database Systems for Advanced Applications. DASFAA 2020 International Workshops. DASFAA 2020. Lecture Notes in Computer Science(), vol 12115. Springer, Cham. https://doi.org/10.1007/978-3-030-59413-8_19
Download citation
DOI: https://doi.org/10.1007/978-3-030-59413-8_19
Published:
Publisher Name: Springer, Cham
Print ISBN: 978-3-030-59412-1
Online ISBN: 978-3-030-59413-8
eBook Packages: Computer ScienceComputer Science (R0)