Abstract
We present a designated-verifier non-interactive zero-knowledge argument system for QMA with multi-theorem security under the Learning with Errors Assumption. All previous such protocols for QMA are only single-theorem secure. We also relax the setup assumption required in previous works. We prove security in the malicious designated-verifier (MDV-NIZK) model (Quach, Rothblum, and Wichs, EUROCRYPT 2019), where the setup consists of a mutually trusted random string and an untrusted verifier public key.
Our main technical contribution is a general compiler that given a NIZK for NP and a quantum sigma protocol for QMA generates an MDV-NIZK protocol for QMA.
O. Shmueli—Supported by ISF grants 18/484 and 19/2137, by Len Blavatnik and the Blavatnik Family Foundation, and by the European Union Horizon 2020 Research and Innovation Program via ERC Project REACT (Grant 756482).
You have full access to this open access chapter, Download conference paper PDF
Similar content being viewed by others
1 Introduction
Zero-knowledge protocols allow to prove statements without revealing anything but the mere fact that they are true. Since their introduction by Goldwasser, Micali, and Rackoff [GMR89] they have had a profound impact on modern cryptography and theoretical computer science at large. While standard zero-knowledge protocols are interactive, Blum, Feldman, and Micali [BFM19] introduced the concept of a non-interactive zero-knowledge (NIZK) protocol, which consists of a single message sent by the prover to the verifier. NIZK protocols cannot exist in the plain model (i.e. a language with such a NIZK protocol can be decided by an efficient algorithm) but can be realized with a pre-computed setup. The point of the setup is that it can be computed instance-independently and usually, the setup is executed by a trusted third party that generates and publishes a string of bits and sometimes trapdoors are handed to the prover or verifier (or both).
Although existing zero-knowledge protocols for NP cover an array of diverse tasks and in particular, under standard computational assumptions it is known how to construct NIZK protocols for NP [CCH+19, PS19, BKM20], far less is known about the class QMA, the quantum generalization of NP. This knowledge gap between NP and QMA, which is present in both interactive and non-interactive zero-knowledge protocols, stems from the fact that many of the techniques that work for constructing protocols for NP, implicitly rely on the assumption that information in the system is classical. Accordingly, these techniques fail when this assumption no longer holds.
The first gap between classical and quantum NIZK protocols is that of setup requirements, that is, how much trust and resources the setup needs. The standard setup in NIZK is called the common reference string (CRS) model, where the trusted party samples a classical string from some specified distribution and publishes it. If the reference string is simply uniformly random then the setup is in the common random string model, which is considered to require minimal trust in the NIZK setting. While NIZK arguments for NP are known to exist in the common random string model under LWE [CCH+19, PS19], in current QMA constructions the setup is comprised at least of a common reference string sampled by the trusted party, and an additional public and secret verification keys \((\mathsf {pvk}, \mathsf {svk})\) where \(\mathsf {pvk}\) is published along with the CRS and \(\mathsf {svk}\) is kept by the verifier, such that either:
-
\(\mathsf {pvk}\) is a quantum state that needs to stay coherent while waiting for the proof by the prover, or
-
The pair \((\mathsf {pvk}, \mathsf {svk})\) can be sampled only by the trusted party and not the verifier.
Aside from the above, a more elementary missing part in current NIZK protocols for QMA is multi-theorem security, which provides the main efficiency advantage to a NIZK protocol over an interactive protocol. Multi-theorem security considers the reusability of the setup, that is, once the setup is computed, any prover can send a proof by a single message repeatedly for many different statements and there is no need to re-compute the setup for every new proof sent, and in relation to the above QMA setups: once the CRS and public verification key are published, they are reusable.
Given the gap of knowledge in NIZK techniques between NP and QMA, improving the power of NIZKs for QMA and specifically constructing a reusable non-interactive zero-knowledge protocol for QMA seem as a natural cryptographic goal which we explore in this work.
1.1 Results
Under the Learning with Errors (LWE) assumption [Reg09] we resolve the above question. Specifically, we construct a multi-theorem-secure NIZK argument for QMA in the malicious designated-verifier model, which is the following:
-
1.
The trusted party samples only a common random string \(\mathsf {crs}\).
-
2.
Given \(\mathsf {crs}\), any verifier can sample a pair of classical public and secret verification keys \((\mathsf {pvk}, \mathsf {svk})\), in particular it is possible that the published \(\mathsf {pvk}\) is maliciously-generated.
Given \(\mathsf {crs}\) and \(\mathsf {pvk}\), any prover can repeatedly give a non-interactive zero-knowledge proof by a single quantum message \(|{\pi }\rangle \). The MDV-NIZK model is introduced by Quach, Rothblum, and Wichs in [QRW19] and has the same minimal trust requirements as the common random string model (but is privately verifiable).
Theorem 1 (informal)
[informal] Assuming that LWE is hard for polynomial-time quantum algorithms, there exists a reusable, non-interactive computational zero-knowledge argument system for QMA in the malicious designated-verifier model.
Main Technical Contribution: General Sigma Protocol MDV-NIZK Compilation. Technically, we deviate from previous NIZK constructions for QMA and aim for a simple and classical technique which is post-quantum (i.e. preserves security also for quantum protocols). Specifically, our main contribution is showing how given a NIZK for NP it is possible to compile a quantum sigma protocol into a reusable MDV-NIZK protocol. Further details are given in the technical overview below.
1.2 Technical Overview
We next describe our construction of a multi-theorem-secure MDV-NIZK protocol for QMA. For a discussion about the possibility of constructing a NIZK protocol for QMA in the CRS model see Subsect. 1.3, and for an overview of NIZK models and previous work on NIZK for QMA see Subsect. 1.3.
As we are aiming for a classical (quantum-secure) technique we currently restrict our attention to a purely-classical question: Given any sigma protocol \((\varSigma .\mathsf {\mathsf {P}}, \varSigma .\mathsf {\mathsf {V}})\), generically compile it into a multi-theorem-secure MDV-NIZK while assuming minimal properties of the protocolFootnote 1. We will start with considering classical sigma protocols and later see what changes should take place in order for the technique to work for quantum protocols.
From a Sigma Protocol to a Single-Theorem-Secure MDV-NIZK. A sigma protocol is a 3-message public-coin proof system (with some mild zero knowledge properties), where the 3 messages are denoted by \(\alpha \), \(\beta \) and \(\gamma \) (i.e. \(\beta \) is a random string and is called “the challenge string”). Our first step is to construct a MDV-NIZK protocol with only single-theorem security out of a sigma protocol and is very simple.
In a sigma protocol, since the verifier’s message \(\beta \) is a random string it is independent of any other information, additionally, our second need from it is that it stays hidden (until after the prover sends its first message \(\alpha \)). The verifier can compute its public verification key, which is computed instance-independently, as a function of \(\beta \): The public verification key \(\mathsf {pvk}\) is an FHE-encrypted random challenge \(\beta \) and the secret verification key \(\mathsf {svk}\) is the FHE decryption key and the challenge string,
Given the public verification key \(\mathsf {pvk}\), the 1-message proof procedure for \(x \in \mathcal {L}\) goes as follows:
-
\(\mathsf {P}\) computes the first sigma protocol message \(\alpha \leftarrow \varSigma .\mathsf {\mathsf {P}}(x, w)\), where \(w\in \mathcal {R}_{\mathcal {L}}(x)\).
-
\(\mathsf {P}\) computes \(\gamma \) the last protocol message under the encryption, that is, \(\mathsf {P}\) performs the homomorphic evaluation \(\hat{\mathsf {ct}}_\mathsf {P}\leftarrow \mathsf {FHE.Eval}(\varSigma .\mathsf {\mathsf {P}}_3, \mathsf {FHE.Enc}_{\mathsf {fhek}}(\beta ))\).
-
As the proof, \(\mathsf {P}\) sends \(\alpha \) out in the open and \(\gamma \) under the encryption, that is, the proof is \(\pi = (\alpha , \hat{\mathsf {ct}}_{\mathsf {P}})\).
In order for the proof to stay zero-knowledge, the homomorphic evaluation needs to be circuit-private. The verification algorithm is straightforward: Given \(\mathsf {svk}\), an instance x and a proof \(\pi = (\alpha , \hat{\mathsf {ct}}_{\mathsf {P}})\), the verifier decrypts \(\hat{\mathsf {ct}}_{\mathsf {P}}\) to get \(\gamma \), and accepts iff the sigma protocol verifier accepts \(\varSigma .\mathsf {\mathsf {V}}(x, \alpha , \beta , \gamma ) = 1\).
Is the Above Protocol Multi-theorem-Secure? While it is intuitively clear that the described construction is secure for a single use of the setup (that is, the above should, with some modifications, yield a single-theorem-secure MDV-NIZK) it is provably not multi-theorem-secure. Sigma protocols are usually parallel repetitions of 3-message zero-knowledge protocols, for example, consider the sigma protocol which is the parallel repetition of the zero-knowledge protocol for Graph Hamiltonicity [Blu86], which is as follows: Given a Hamiltonian cycle C in a graph \(G = (V, E)\), the prover samples a random permutation \(\varphi : V \rightarrow V\) of the vertices and commits to the permuted graph \(\varphi (G)\)Footnote 2. The verifier then sends a random bit b, and the prover answers accordingly:
-
If \(b = 0\) it is considered as a validity check, and the prover opens all commitments and sends \(\varphi \). The verifier accepts if indeed the committed graph is \(\varphi (G)\).
-
If \(b = 1\) it is considered as the cycle check, and the prover opens commitments only for the subgraph \(\varphi (C)\). The verifier accepts if the opening shows a Hamiltonian cycle.
If the sigma protocol used in the above MDV-NIZK construction is the parallel repetition of the zero-knowledge protocol for HamiltonicityFootnote 3, then there is a polynomial-time malicious prover \(\mathsf {P}^*\) that given multiple access to the verifier’s verdict function \(\mathsf {V}(\mathsf {svk}, \cdot )\) using the same public/secret verification key pair, can decode the encrypted challenge string \(\beta \) (which is polynomially-many random bits, each bit is for the i-th parallel repetition of the zero-knowledge protocol) and consequently break the soundness.
\(\mathsf {P}^*\) takes a Hamiltonian graph G and a Hamiltonian cycle C in it, and will decode the entire \(\beta = (b_1, b_2, \cdots , b_k)\) bit-by-bit: To decode \(b_i\), \(\mathsf {P}^*\) will honestly execute the zero-knowledge protocol prover’s algorithm for all indices but index i (that is, for all \(j \ne i\), it will honestly compute \(\mathsf {Com}(\varphi _j(G))\) and under the encryption, the opening of either the entire graph and the permutation of just the cycle \(\varphi _j(C)\)), for which it is going to operate as follows. \(\mathsf {P}^*\) will guess that \(b_i = 0\) and send a commitment to a permutation of the graph out in the open and under the encryption act as if \(b_i = 0\) regardless of the actual value of \(b_i\). By the verifier’s acceptance or rejection it will know whether the bit was 0 or 1. After decoding \(\beta \) the prover can now use this information to “prove” that any graph G is Hamiltonian.
From Single-Theorem to Multi-theorem Security. In the above attack the prover heavily relied on a specific operation: It uses a yes-instance (in the above case, a Hamiltonian graph G), in order to decode the random challenge \(\beta \) and then goes on to use the knowledge of \(\beta \) to give a false proof for a no-instance (again, in the above, a non Hamiltonian graph \(G^*\)).
Crucially, \(\mathsf {P}^*\) does not know how to decode \(\beta \) when the graph is not Hamiltonian. More specifically, in the above we decode \(\beta \) bit-by-bit rather than all at once, and this ability comes from the fact that G is Hamiltonian and the zero-knowledge protocol is complete, thus \(\mathsf {P}^*\) can be sure that if it honestly executes the zero-knowledge protocol for all indices but i, the only index that can make the proof get rejected is i. In this isolation, checking whether the challenge bit \(b_i\) is 0 or 1 becomes easy. However, if the graph is not Hamiltonian then the prover cannot know which index made the proof get rejected because all k indices are prone to rejection. Formally, by the soundness of the sigma protocol, we know that the answer from the verdict function of the verifier in this case will always be a rejection for any polynomial (or even sub-exponential) number of queries, with overwhelming probability. This means in particular that the prover cannot decode anything through the oracle access to the verdict function.
Our fix to the first protocol is based on the above observation: If we could make the random challenge \(\beta \) change with the instance at hand it seems that the decoding attack is neutralized, because even if the prover decodes \(\beta _G\) the challenge for a Hamiltonian graph G, it doesn’t have information about \(\beta _{G^*}\) the challenge of some non Hamiltonian \(G^*\). Since the instance x is in particular a classical string we can make the challenge change with the instance: The public verification key will not be an encrypted challenge \(\beta \) but instead will be a secret key \(\mathsf {prfk}\) of a pseudorandom function \(\mathsf {PRF}\). The prover will compute \(\alpha \) out in the open as before but the homomorphic evaluation changes: under the encryption, \(\mathsf {P}\) will compute the challenge string as the PRF’s output on the instance \(\beta _x = \mathsf {PRF}.\mathsf {F}_{\mathsf {prfk}}(x)\), and then compute \(\gamma \) for the challenge \(\beta _x\).
Extraction by Non-interactive Zero Knowledge for NP. Up to this point we only came close to constructing a provably-secure MDV-NIZK. Indeed, we didn’t even use any NIZK tools yet for NP, and in order to prove the security of our construction we need knowledge extraction from both the prover and verifier.
To prove soundness, our thought process is roughly the following: We know that the prover computes \(\gamma \) obliviously under the FHE, more precisely, it homomorphically evaluates the circuit \(C_{x, r}\) that computes \(\beta _x = \mathsf {PRF}.\mathsf {F}_{\mathsf {prfk}}(x)\) and then given \(\beta _x\) computes \(\gamma \). The part of the circuit \(C_{x, r}\) that computes \(\gamma \) from \(\beta _x\) is the “non-trivial” part of the circuit and is determined by a secret string r (which is the information that the honest sigma protocol prover uses in order to compute \(\gamma \), this information is the randomness of the prover and possibly the witness). If we could extract r from a prover (e.g. by the prover giving a proof of knowledge on the non-trivial part of the circuit \(C_{x, r}\)) that successfully cheats in the NIZK protocol then we could get a successfully cheating prover for the sigma protocol and thus prove security. To see this, note that by the hiding of the FHE and by the pseudorandomness of the PRF, even if as the public verification key we send an encryption of 0 instead of an encryption of the PRF secret key, the string r still needs to yield a circuit \(C_{x, r}\) that does well in generating a satisfying \(\gamma \) for a now-truly-random challenge \(\beta \).
On the zero knowledge side we also need extraction; we recall a basic property of a sigma protocol: if the sigma protocol simulator knows the challenge string \(\beta \) before sending the first message \(\alpha \) then it can simulate a view that is indistinguishable from the real interaction with the honest prover. This means that the information we want to extract from the malicious verifier is the secret PRF key \(\mathsf {prfk}\) that in particular holds the information for obtaining \(\beta _x\).
We solve both extraction tasks by a combination of a two-sided NP NIZK and a public-key encryption scheme with pseudorandom public keys. Given the existence of a PKE scheme \((\mathsf {PKE}.\mathsf {Gen}, \mathsf {PKE}.\mathsf {Enc}, \mathsf {PKE}.\mathsf {Dec})\) with pseudorandom public keys of length \(\ell \) we take the common random string of our protocol to be (1) the common random string of an NP NIZK \((\mathsf {NIZK.\mathsf {Setup}}, \mathsf {NIZK.\mathsf {P}}, \mathsf {NIZK.\mathsf {V}})\) protocol which we denote with \(\mathsf {crs}\), concatenated with (2) a random string of length \(\ell \) which we denote with \(\mathsf {ek}\) (for extraction key).
We will let each of the parties encrypt, using \(\mathsf {PKE}.\mathsf {Enc}_{\mathsf {ek}}(\cdot )\), the secrets that we want to extract and then use the NIZK to prove consistency between the content of the PKE encryption and the protocol computations. More precisely, as part of its 1-message proof, the prover will give a proof \(\pi _{\mathsf {P}}\) that the string r encrypted using the PKE yields the (canonical) circuit \(C_{x, r}\) that it used for the (circuit-private) homomorphic evaluation that generated \(\gamma \), and the verifier, as part of its public verification key, will give a proof \(\pi _{\mathsf {V}}\) that the PRF key \(\mathsf {prfk}\) that is encrypted using the PKE is the same key encrypted with the FHE. Note that the information that the parties encrypt using a random string instead of a real PKE key stays secure due to the fact that a real key is indistinguishable from a random string, and thus an adversary that manages to break the PKE when it uses a random string as the public key can break the pseudorandomness property of the public keys.
When wanting to extract information (either in the soundness reduction or in the zero-knowledge simulation), we will sample \(\mathsf {ek}\) using the PKE key-generation algorithm \((\mathsf {ek}, \mathsf {sk}) \leftarrow \mathsf {PKE}.\mathsf {Gen}\), and since the public keys are pseudorandom the change in key distribution won’t be felt by either of the parties. At that point the parties encrypt their secrets and prove they do so using the NIZK, and the extractor can just use the PKE decryption \(\mathsf {PKE}.\mathsf {Dec}_{\mathsf {sk}}(\cdot )\) to obtain the secrets.
Compiling Quantum Protocols. Our technique so far is entirely classical and compiles classical sigma protocols. We now ask whether it works to compile quantum sigma protocols. This can be answered in turn by answering the following question: what properties of the sigma protocol exactly did we use in order for the MDV-NIZK protocol to work?
It can be verified that even if we don’t assume nothing on the sigma protocol that we compile, every action in the MDV-NIZK protocol except the homomorphic evaluation of the circuit \(C_{x, r}\) can stay exactly the same. Regarding the homomorphic evaluation, the issue that we have is the following: In order to still be able to extract the information r of the circuit \(C_{x, r}\) from the prover, the computation that takes \(\beta _x\) and outputs \(\gamma \) needs to be a classical circuit. This is not necessarily the case in a quantum protocol. For example, in the quantum zero-knowledge protocol for QMA of [BJSW16] (which is also the basis for the quantum NIZK protocol of [CVZ19]), in order to generate \(\gamma \) given \(\alpha , \beta \), first a quantum Clifford operation that is chosen with respect to \(\beta \) needs to be executed on \(\alpha \), followed by a measurement. Then, the prover proves in ZK that the classical string obtained by the measurement satisfies some propertiesFootnote 4. With this goal in mind, we identify a different quantum protocol that in fact does satisfy the property that \(\gamma \) can be computed by an entirely classical circuit.
We consider the Consistency of Local Density Matrices (CLDM) problem [Liu06], which is a QMA problem with some special properties. In [BG19] Broadbent and Grilo show that CLDM is QMA-complete and how to construct a very simple quantum zero-knowledge protocol for it. The [BG19] zero-knowledge protocol for CLDM is as follows: Given a quantum witness \(|{w}\rangle \), the protocol starts with the prover sending a quantum one-time pad encryption of \(|{w}\rangle \) as the message \(\alpha \). More precisely, for a length-l witness it samples classical random pads \(a, b \leftarrow \{ 0, 1 \}^l\), applies
and then sends as \(\alpha \) the transformed quantum state and classical commitments to the QOTP keys a, b. For a random challenge \(\beta \), the prover response \(\gamma \) is an opening to part of the state. We find the CLDM problem and specifically the zero-knowledge protocol for it especially attractive for our purposes as \(\gamma \) is only a function of the randomness of the prover and the challenge \(\beta \), which in particular means that the circuit \(C_{x, r}\) can stay classical in our setting.
Finally, by using the sigma protocol yielded by the parallel repetition of the zero-knowledge protocol from [BG19] we obtain a clean and simple non-interactive computational zero-knowledge argument system for the class QMA in the malicious designated-verifier model:
-
1.
Common Random String: \((\mathsf {crs}, \mathsf {ek})\).
-
2.
Public and Secret Verification Keys: \(\mathsf {prfk}\leftarrow \mathsf {PRF}.\mathsf {Gen}(1^\lambda ), \mathsf {fhek}\leftarrow \mathsf {FHE.Gen}(1^\lambda )\),
$$ \mathsf {pvk}= \big (\mathsf {FHE.Enc}_{\mathsf {fhek}}(\mathsf {prfk}), \; \mathsf {PKE}.\mathsf {Enc}_{\mathsf {ek}}(\mathsf {prfk}), \;\pi _\mathsf {V}\big ), \mathsf {svk}= \big ( \mathsf {prfk}, \; \mathsf {fhek}\big ) . $$
For any prover that wishes to give a proof for an instance \(x \in \mathcal {L}_{yes}\), it executes the following:
-
Proof: If \(\pi _\mathsf {V}\) is valid, \(\mathsf {P}\) computes \(\alpha \leftarrow \varXi .\mathsf {P}(|{w}\rangle ; r)\) and sends
$$ |{\pi }\rangle = \big ( \alpha , \; \mathsf {FHE.Eval}(C_{x, r}, \mathsf {FHE.Enc}(\mathsf {prfk})), \; \mathsf {PKE}.\mathsf {Enc}_{\mathsf {ek}}(r), \; \pi _\mathsf {P}\big ) . $$
1.3 Related Work
In this section we discuss the main challenges in the construction of non-interactive zero-knowledge protocols for QMA (specifically in the CRS model) and the previous works on QMA NIZKs.
Can We Build a NIZK Protocol for QMA in the CRS Model? In short, the answer to the above question is that we don’t know, and this section does not aim to answer it. This section is intended to give some evidence to why constructing a NIZK for QMA in the CRS model seem to require a different set of techniques from what we currently have for NP. In what follows we will start with briefly recalling how NIZKs for NP are constructed and then understand why current approaches fail in the setting of quantum proofs.
NP, Fiat-Shamir and Correlation Intractability. In order to construct a non-interactive zero-knowledge protocol for NP under standard assumptions, the construction starts with a sigma protocol \((\varSigma .\mathsf {\mathsf {P}}, \varSigma .\mathsf {\mathsf {V}})\). To make the protocol non-interactive, the Fiat-Shamir transform is applied: By assuming public oracle access to a random function F, the prover applies it to \(\alpha \) and treat its (random-string) output \(F(\alpha )\) as the challenge string \(\beta \). It then computes \(\gamma \) and sends all of this information to the verifier, who makes sure that \(\beta \) was rightfully generated \(\beta = F(\alpha )\), and that the sigma protocol verifier \(\varSigma .\mathsf {\mathsf {V}}(\alpha , \beta , \gamma )\) accepts. Since we don’t know how to construct a cryptographic primitive that acts as a publicly-computable random function, the above protocol is secure only in the random oracle model, that is, only if we directly assume public access to such random function F.
In order to prove the security of the NIZK protocol in the standard model (with access to a common reference string rather than a random oracle), the final part of the construction involves swapping the random function F with a new, special hash function H - this general technique of swapping F with a special hash function H is usually called the Correlation Intractability (CI) paradigm [CGH04]. The properties of the hash function H or the meaning of correlation intractability are less relevant to this overview, but it is suffices to say that under the LWE assumption it is known how to construct a hash function H that can be swapped with F in the FS transform and where the protocol can be proven secure [CCH+19, PS19].
Can we use Known Classical NIZK Techniques for Quantum Protocols? There are two known routes for getting a quantum-secure NIZK for NP in the CRS model, the first is through the FS transform and CI (which also uses only standard assumptions, described above) and the second is through the hidden bits model and indistinguishability obfuscation. It is natural to ask whether we can use these techniques for QMA (the question of whether the FS transform can be used for quantum protocols was asked as one of the open questions in Sect. 1.4 of [BG19]).
We first review the ability to use the FS transform (and in particular correlation intractability) for QMA and explain why there is an issue with the no-cloning theorem. In the quantum setting, sigma protocols \((\varXi .\mathsf {P}, \varXi .\mathsf {V})\) [BG19, BJSW16] are quite the same but with the main difference that the first message \(\alpha \) is quantum (and of course, the prover takes as input a quantum witness \(|{w}\rangle \) rather than classical). Recall that when we use the FS transform on a sigma protocol in order to generate a NIZK, for the protocol to be complete, when the parties act honestly then the verifier needs to verify that the random function F yields the challenge, that is \(F(\alpha ) = \beta \). This means that now F needs to be a quantum transformation such that for \(x \in \mathcal {L}_{yes}\) and an honestly generated \(\alpha \leftarrow \varXi .\mathsf {P}(|{w}\rangle )\), \(F(\alpha )\) is always the same classical string (with overwhelming probability). Also, for the protocol to be sound we need that the entire output of F will be the chellenge \(\beta \) and it cannot be the case for example that the output \(F(\alpha )\) will contain one register with the classical string \(\beta \) and another register with some quantum state \(|{\psi }\rangle \). Now, denote by s the classical string s.t. \(F(\alpha ) = s\), and we have a generating circuit for the quantum witness: \(|{w}\rangle = \varXi .\mathsf {P}^{\dagger }(\cdot )\cdot F^{\dagger }\cdot |{s}\rangle \), where the inverse versions of F and \(\varXi .\mathsf {P}\) are purified. This seems to violate the no-cloning theorem in the following manner: the prover gets a copy of the witness and can generate a generating circuit for the witness state, this circuit can be used to generate arbitrarily many copies of the state. Finally, because we can always consider a trivial language with a dummy witness, and take the quantum witness to be some unclonable state (for example, a pseudorandom quantum state) we get a contradiction to the no-cloning theorem.
Even if we aim to construct a NIZK using the FS transform for QCMA, the subclass of QMA where the verification algorithm is still quantum but the witness is classical, the problem is not seemed to be solved. The reason, is that we don’t know how to construct sigma protocols for QCMA where the first message \(\alpha \) is classical, and the same contradiction to the no-cloning theorem holds.
The second known route of obtaining a quantum-secure NIZK protocol for NP in the CRS model is through the hidden bits model [FLS99] which is implementable by sub-exponentially-secure indistinguishability obfuscation [BP15]. In the hidden bits model, intuitively (and roughly), the trusted party samples as the common reference string a commitment to a string sampled from some distribution (where by using a trapdoor permutation, the prover can open the commitments efficiently), and the prover proves that the instance at hand \(x \in \mathcal {L}_{yes}\) satisfies some property related to the string underlying the commitments. Even if we are willing to assume the very strong cryptographic assumptions which are needed for the realization of this protocol (i.e. sub-exponentially-secure post-quantum indistinguishability obfuscation), it is currently unknown how to use the hidden bits model to instantiate non-interactive zero-knowledge quantum protocols.
Relaxations of the CRS Model and Previous Work. The constructions of NIZKs for NP discussed in Subsect. 1.3 are implicitly in the CRS model, where the setup consists of a string that is sampled and published by the trusted party, in particular, nor the prover or verifier hold any trapdoors over the setup. Sometimes when it is unknown how to build a NIZK in the CRS model (or unknown how to minimize the assumptions for building one) we turn to relaxations of the CRS model. For example, in the designated-verifier model (DV-NIZK) [PV+06] the trusted party samples, along with the CRS, a pair of public and secret verification keys \((\mathsf {pvk}, \mathsf {svk})\), publishes \(\mathsf {pvk}\) along with the CRS and hands \(\mathsf {svk}\) only to the verifier. Another example is the designated prover model (DP-NIZK) [KW19], which is analogous to the DV-NIZK model, only that the prover is the one who gets a secret, now-proof key.
It is a well known fact in the design of NIZKs that when the verifier holds a secret verification key (e.g. in the DV-NIZK model) then multi-theorem zero knowledge can be achieved generically by the compiler of [FLS99], but multi-theorem soundness becomes non-trivial. For example, it is possible (and is sometimes provably the case) that the prover can decode the verifier’s secret key by having access multiple times to the verifier’s verdict function, consequently breaking the soundness of the protocol. Indeed, one example is that until the works of [QRW19, LQR+19], based on [PV+06] it was only known how to get single-theorem-secure DV-NIZK for NP, and another example is that this is the current situation with QMA constructions of NIZK protocols.
The QMA NIZK protocol of Broadbent and Grilo [BG19] is in the secret parameters model (i.e. the protocol is both designated-prover and designated-verifier and both parties get secret keys from the trusted party) but is a proof system and has statistical soundness rather than the computational soundness we achieve. The protocol of Coladangelo, Vidick and Zhang [CVZ19] is in a model that is somewhat between the common reference string model and the DV-NIZK model, where the trusted party samples a common reference string and the verifier itself samples a pair \((\mathsf {pvk}, \mathsf {svk})\) where \(\mathsf {pvk}\) is a quantum state. Morimae [Mor20] shows a classical-designated-verifier NIZK proof system for QMA with a quantum trusted setup. Outside of the standard model, an additional construction by Alagic, Childs, Grilo and Hung [ACGH19] yields a QMA NIZK argument in the quantum random oracle model (with additional setup in the secret parameters model) which is classical-verifier. All of the abovementioned protocols are not reusable.
There are two main issues with letting the trusted party sample secret keys for any of the parties: First, the trust requirements of the setup now increase as the party receiving the secret key should assume that the trusted party handles its secret information securely. The second issue is that of centralization of computational resources: for example, in the DV-NIZK model, the trusted party is now responsible for sampling a fresh pair \((\mathsf {pvk}, \mathsf {svk})\) for every new verifier that wishes to use the protocol, which is very different from the CRS setting where it samples a string and from that point on can terminate.
The malicious designated-verifier (MDV-NIZK) model [QRW19, LQR+19] seeks to solve the above two problems, which is also the model of our protocol. In the MDV-NIZK model the trusted party only samples a common random string, and then, any verifier wishing to use the protocol can sample by itself a pair of classical keys \((\mathsf {pvk}, \mathsf {svk})\) and publish \(\mathsf {pvk}\). The protocol then stays secure even if the public key \(\mathsf {pvk}\) is maliciously-generated.
1.4 Subsequent Work
Subsequently to this work, several related constructions for NIZK protocols for QMA are shown. Morimae and Yamakawa construct a classically verifiable dual-mode NIZK for QMA, with quantum preprocessing [MY21]. The result is essentially in the same model of the protocol of Coladangelo, Vidick and Zhang [CVZ19], that is, the CRS is published, and then the verifier sends an instance-independent quantum message to the prover, keeping a classical trapdoor. Given the instance, witness and the verifier’s quantum message, the prover can perform an efficient quantum procedure and send a classical message to the verifier which acts as a proof. The improvement of [MY21] over [CVZ19] is that the protocol is dual-mode and has two modes: (1) a proof (with statistical soundness) and computational ZK guarantee and (2) an argument (with computational soundness guarantee) and statistical ZK, rather than only an argument mode, that [CVZ19] enables.
Bartusek, Coladangelo, Khurana and Ma also construct an MDV-NIZK protocol for QMA [BCKM20], and improve our result in two aspects. First, in order to get adaptive soundness (over standard soundness) we need to assume the subexponential (quantum) hardness of LWE, while [BCKM20] only requires assuming the polynomial (quantum) hardness of LWE. Second, our protocol requires polynomially-many copies of the quantum witness for the QMA instance x, while the protocol of [BCKM20] is a single-witness protocol.
2 Preliminaries
We rely on standard notions of classical Turing machines and Boolean circuits:
-
A PPT algorithm is a probabilistic polynomial-time Turing machine.
-
Let M be a PPT and let x denote the random variable which is the output of M. Whenever the entropy of the output of M is non-zero, we denote the random experiment of sampling x with \(x \leftarrow M(\cdot )\). If the entropy of the output of M is zero (i.e. M is deterministic), we denote \(x = M(\cdot )\).
-
We sometimes think about PPT algorithms as polynomial-size uniform families of circuits, these are equivalent models. A polynomial-size circuit family \(\mathcal {C}\) is a sequence of circuits \(\mathcal {C} = \left\{ C_\lambda \right\} _{\lambda \in \mathbb {N}}\), such that each circuit \(C_\lambda \) is of polynomial size \(\lambda ^{O(1)}\). We say that the family is uniform if there exists a deterministic polynomial-time algorithm M that on input \(1^\lambda \) outputs \(C_\lambda \).
-
For a PPT algorithm M, we denote by M(x; r) the output of M on input x and random coins r. For such an algorithm and any input x, we write \(m\in M(x)\) to denote the fact that m is in the support of \(M(x;\cdot )\).
We follow standard notions from quantum computation.
-
A QPT algorithm is a quantum polynomial-time Turing machine.
-
We sometimes think about QPT algorithms as polynomial-size uniform families of quantum circuits, these are equivalent models. A polynomial-size quantum circuit family \(\mathcal {C}\) is a sequence of quantum circuits \(\mathcal {C} = \left\{ C_\lambda \right\} _{\lambda \in \mathbb {N}}\), such that each circuit \(C_\lambda \) is of polynomial size \(\lambda ^{O(1)}\). We say that the family is uniform if there exists a deterministic polynomial-time algorithm M that on input \(1^\lambda \) outputs \(C_\lambda \).
-
An interactive algorithm M, in a two-party setting, has input divided into two registers and output divided into two registers. For the input, one register \(I_m\) is for an input message from the other party, and a second register \(I_a\) is an auxiliary input that acts as an inner state of the party. For the output, one register \(O_m\) is for a message to be sent to the other party, and another register \(O_a\) is again for auxiliary output that acts again as an inner state. For a quantum interactive algorithm M, both input and output registers are quantum.
The Adversarial Model. Throughout, efficient adversaries are modeled as quantum circuits with non-uniform quantum advice (i.e. quantum auxiliary input). Formally, a polynomial-size adversary \(\mathsf {A}^*= \left\{ \mathsf {A}^*_\lambda , \rho _\lambda \right\} _{\lambda \in \mathbb {N}}\), consists of a polynomial-size non-uniform sequence of quantum circuits \(\{ \mathsf {A}^*_\lambda \}_{\lambda \in \mathbb {N}}\), and a sequence of polynomial-size mixed quantum states \(\{ \rho _\lambda \}_{\lambda \in \mathbb {N}}\).
For an interactive quantum adversary in a classical protocol, it can be assumed without loss of generality that its output message register is always measured in the computational basis at the end of computation. This assumption is indeed without the loss of generality, because whenever a quantum state is sent through a classical channel then qubits decohere and are effectively measured in the computational basis.
Indistinguishability in the Quantum Setting
-
Let \(f:\mathbb {N}\rightarrow [0, 1]\) be a function.
-
f is negligible if for every constant \(c \in \mathbb {N}\) there exists \(N \in \mathbb {N}\) such that for all \(n > N\), \(f(n) < n^{-c}\).
-
f is noticeable if there exists \(c \in \mathbb {N}, N \in \mathbb {N}\) such that for every \(n \ge N\), \(f(n) \ge n^{-c}\).
-
f is overwhelming if it is of the form \(1 - \mu (n)\), for a negligible function \(\mu \).
-
-
We may consider random variables over bit strings or over quantum states. This will be clear from the context.
-
For two random variables X and Y supported on quantum states, quantum distinguisher circuit \(\mathsf {D}\) with, quantum auxiliary input \(\rho \), and \(\mu \in [0, 1]\), we write \(X \approx _{\mathsf {D}, \rho , \mu } Y\) if
$$\begin{aligned} \left| \Pr [\mathsf {D}(X; \rho )=1] - \Pr [\mathsf {D}(Y; \rho )=1] \right| \le \mu . \end{aligned}$$ -
Two ensembles of random variables \(\mathcal {X}=\{X_{i}\}_{\lambda \in \mathbb {N}, i \in I_\lambda }\), \(\mathcal {Y}=\{Y_{i}\}_{\lambda \in \mathbb {N}, i \in I_\lambda }\) over the same set of indices
 are said to be computationally indistinguishable, denoted by \(\mathcal {X}\approx _{c} \mathcal {Y}\), if for every polynomial-size quantum distinguisher \(\mathsf {D}=\left\{ \mathsf {D}_\lambda , \rho _\lambda \right\} _{\lambda \in \mathbb {N}}\) there exists a negligible function \(\mu (\cdot )\) such that for all \(\lambda \in \mathbb {N}, i \in I_\lambda \), $$\begin{aligned} X_i \approx _{\mathsf {D}_{\lambda }, \rho _\lambda , \mu (\lambda )} Y_i. \end{aligned}$$
are said to be computationally indistinguishable, denoted by \(\mathcal {X}\approx _{c} \mathcal {Y}\), if for every polynomial-size quantum distinguisher \(\mathsf {D}=\left\{ \mathsf {D}_\lambda , \rho _\lambda \right\} _{\lambda \in \mathbb {N}}\) there exists a negligible function \(\mu (\cdot )\) such that for all \(\lambda \in \mathbb {N}, i \in I_\lambda \), $$\begin{aligned} X_i \approx _{\mathsf {D}_{\lambda }, \rho _\lambda , \mu (\lambda )} Y_i. \end{aligned}$$ -
The trace distance between two distributions X, Y supported over quantum states, denoted \(\mathrm {TD}(X, Y)\), is a generalization of statistical distance to the quantum setting and represents the maximal distinguishing advantage between two distributions supported over quantum states, by unbounded quantum algorithms. We thus say that ensembles \(\mathcal {X}=\{X_{i}\}_{\lambda \in \mathbb {N}, i \in I_\lambda }\), \(\mathcal {Y}=\{Y_{i}\}_{\lambda \in \mathbb {N}, i \in I_\lambda }\), supported over quantum states, are statistically indistinguishable (and write \(\mathcal {X}\approx _{s} \mathcal {Y}\)), if there exists a negligible function \(\mu (\cdot )\) such that for all \(\lambda \in \mathbb {N}, i \in I_\lambda \),
$$\begin{aligned} \mathrm {TD}\left( X_i, Y_i \right) \le \mu (\lambda ) . \end{aligned}$$
In what follows, we introduce the cryptographic tools used in this work. By default, all algorithms are classical and efficient, and security holds against polynomial-size non-uniform quantum adversaries with quantum advice.
2.1 Cryptographic Tools
Interactive Proofs and Sigma Protocols. We define interactive proof systems and then proceed to describe sigma protocols, which are a special case of interactive proof systems. In what follows, we denote by \((\mathsf {P}, \mathsf {V})\) a protocol between two parties \(\mathsf {P}\) and \(\mathsf {V}\). For common input \(x\), we denote by \(\mathsf {OUT}_{\mathsf {V}}\langle \mathsf {P},\mathsf {V} \rangle (x)\) the output of \(\mathsf {V}\) in the protocol. For honest verifiers, this output will be a single bit indicating acceptance or rejection of the proof. Malicious quantum verifiers may have arbitrary quantum output.
Definition 1 (Quantum Proof Systems for QMA)
Let \((\mathsf {P}, \mathsf {V})\) be a quantum protocol with an honest QPT prover \(\mathsf {P}\) and an honest QPT verifier \(\mathsf {V}\) for a problem \(\mathcal {L}\in \text{ QMA }\), satisfying:
-
1.
Statistical Completeness: There is a polynomial \(k(\cdot )\) and a negligible function \(\mu (\cdot )\) s.t. for any \(\lambda \in \mathbb {N}\), \(x\in \mathcal {L}\cap \{0,1\}^\lambda \), \(|{w}\rangle \in \mathcal {R}_{\mathcal {L}}(x)\)Footnote 5,
$$ \Pr [ \mathsf {OUT}_{\mathsf {V}}\langle \mathsf {P}(|{w}\rangle ^{\otimes k(\lambda )}),\mathsf {V} \rangle (x) = 1 ] \ge 1 - \mu (\lambda ) . $$ -
2.
Statistical Soundness: There exists a negligible function \(\mu (\cdot )\), such that for any (unbounded) prover \(\mathsf {P}^*\), any security parameter \(\lambda \in \mathbb {N}\), and any \(x\in \{0,1\}^\lambda \setminus \mathcal {L}\),
$$\begin{aligned} \Pr \left[ \mathsf {OUT}_{\mathsf {V}}\langle \mathsf {P}^*,\mathsf {V} \rangle (x)=1 \right] \le \mu (\lambda ). \end{aligned}$$
We use the abstraction of Sigma Protocols, which are public-coin three-message proof systems with a weak zero-knowledge quarantee. We define quantum Sigma Protocols for gap problems in QMA.
Definition 2 (Quantum Sigma Protocol for QMA)
[Quantum Sigma Protocol for QMA] A quantum sigma protocol for \(\mathcal {L}\in \text{ QMA }\) is a quantum proof system \((\varXi .\mathsf {P}, \varXi .\mathsf {V})\) (as in Definition 1) with 3 messages and the following syntax.
-
\(\alpha = \varXi .\mathsf {P}(|{w}\rangle ^{\otimes k(\lambda )} ; r):\) Given \(k(\lambda )\) copies of the quantum witness \(w \in \mathcal {R}_{\mathcal {L}}(x)\) and classical randomness r, the first prover message consists of a quantum message \(\alpha \) generated by a quantum unitary computation \(\varXi .\mathsf {P}\).
-
\(\beta \leftarrow \varXi .\mathsf {V}(x):\) The verifier simply outputs a string of \(\mathrm {poly}(|x|)\) random bits.
-
\(\gamma = \varXi .\mathsf {P}_3(\beta , r):\) Given the verifier’s \(\beta \) and the randomness r, the prover outputs a response \(\gamma \) by a classical computation \(\varXi .\mathsf {P}_3\).
The protocol satisfies the following.
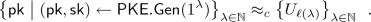
Special Zero-Knowledge: There exists a QPT simulator \(\varXi .\mathsf {Sim}\) such that,
where \(\lambda \in \mathbb {N}\), \(x\in \mathcal {L}\cap \{0,1\}^\lambda \), \(|{w}\rangle \in \mathcal {R}_{\mathcal {L}}(x)\), \(\beta \in \{ 0, 1 \}^{\mathrm {poly}(\lambda )}\) and \(\ell (\lambda )\) is the amount of randomness needed for the first prover message.
Instantiations. Quantum sigma protocols follow from the parallel repetition of the 3-message quantum zero-knowledge protocols of [BG19] for QMA.
Leveled Fully-Homomorphic Encryption with Circuit Privacy. We define a leveled fully-homomorphic encryption scheme with circuit privacy, that is, for an encryption \(\mathsf {ct}= \mathsf {FHE.Enc}(x)\) and a circuit C, a C-homomorphically-evaluated ciphertext \(\hat{\mathsf {ct}}= \mathsf {FHE.Eval}(C, \mathsf {ct})\) reveals nothing on C but C(x).
Definition 3 (Circuit-Private Fully-Homomorphic Encryption)
A circuit-private, leveled fully-homomoprhic encryption scheme \((\mathsf {FHE.Gen},\) \(\mathsf {FHE.Enc},\) \(\mathsf {FHE.Eval},\) \(\mathsf {FHE.Dec})\) has the following syntax:
-
\(\mathsf {sk}\leftarrow \mathsf {FHE.Gen}(1^\lambda , 1^{s(\lambda )}):\) a probabilistic algorithm that takes a security parameter \(1^\lambda \) and a circuit size bound \(s(\lambda )\) and outputs a secret key \(\mathsf {sk}\).
-
\(\mathsf {ct}\leftarrow \mathsf {FHE.Enc}_{\mathsf {sk}}(x):\) a probabilistic algorithm that given the secret key, takes a string \(x \in \{0,1\}^*\) and outputs a ciphertext \(\mathsf {ct}\).
-
\(\hat{\mathsf {ct}}\leftarrow \mathsf {FHE.Eval}({C},\mathsf {ct}):\) a probabilistic algorithm that takes a (classical) circuit \({C}\) and a ciphertext \(\mathsf {ct}\) and outputs an evaluated ciphertext \(\hat{\mathsf {ct}}\).
-
\(\hat{x} = \mathsf {FHE.Dec}_{\mathsf {sk}}(\hat{\mathsf {ct}}):\) a deterministic algorithm that takes a ciphertext \(\hat{\mathsf {ct}}\) and outputs a string \(\hat{x}\).
The scheme satisfies the following.
-
Perfect Correctness: For any polynomial \(s(\cdot )\), for any \(\lambda \in \mathbb {N}\), size-\(s(\lambda )\) classical circuit C and input x for C,

-
Input Privacy: For every polynomial \(\ell (\cdot )\) (and any polynomial \(s(\lambda )\)),

where \(\lambda \in \mathbb {N}\) and \(x_0, x_1 \in \{ 0, 1 \}^{\ell (\lambda )}\).
-
Statistical Circuit Privacy: There exist unbounded algorithms, probabilistic \(\mathsf {Sim}\) and deterministic \(\mathsf {Ext}\) such that:
-
For every \(x \in \{ 0, 1 \}^*\), \(\mathsf {ct}\in \mathsf {FHE.Enc}(x)\), the extractor outputs \(\mathsf {Ext}(\mathsf {ct}) = x\).
-
For any polynomial \(s(\cdot )\),
$$\begin{aligned} \{ \mathsf {FHE.Eval}({C}, \mathsf {ct}^*) \}_{\lambda , {C}, \mathsf {ct}^*} \approx _s \{ \mathsf {Sim}( \; 1^\lambda , {C}(\mathsf {Ext}(1^\lambda , \mathsf {ct}^*)) \; ) \}_{\lambda , {C}, \mathsf {ct}^*}, \end{aligned}$$where \(\lambda \in \mathbb {N}\), \({C}\) is a \(s(\lambda )\)-size circuit, and \(\mathsf {ct}^* \in \{ 0, 1 \}^{*}\).
-
The next claim follows directly from the circuit privacy property, and will be used throughout the analysis.
Claim (Evaluations of Agreeing Circuits are Statistically Close)
For any polynomial \(s(\cdot )\),
where \(\lambda \in \mathbb {N}\), \(C_0\), \(C_1\) are two \(s(\lambda )\)-size functionally-equivalent circuits, and \(\mathsf {ct}^* \in \{ 0, 1 \}^*\).
Instantiations. Circuit-private leveled FHE schemes are known based on LWE [OPCPC14, BD18].
Pseudorandom-Key Public-Key Encryption. We define a public-key encryption scheme with pseudorandom public keys.
Definition 4 (Pseudorandom-key Public-key Encryption)
A pseudorandom-key public-key encryption scheme \((\mathsf {PKE}.\mathsf {Gen},\) \(\mathsf {PKE}.\mathsf {Enc},\) \(\mathsf {PKE}.\mathsf {Dec})\) has the following syntax:
-
\((\mathsf {pk}, \mathsf {sk}) \leftarrow \mathsf {PKE}.\mathsf {Gen}(1^\lambda ):\) a probabilistic algorithm that takes a security parameter \(1^\lambda \) and outputs a pair of public and secret keys \((\mathsf {pk}, \mathsf {sk})\).
-
\(\mathsf {ct}\leftarrow \mathsf {PKE}.\mathsf {Enc}_{\mathsf {pk}}(x):\) a probabilistic algorithm that given the public key, takes a string \(x \in \{0,1\}^*\) and outputs a ciphertext \(\mathsf {ct}\).
-
\(x = \mathsf {PKE}.\mathsf {Dec}_{\mathsf {sk}}(\mathsf {ct}):\) a deterministic algorithm that given the secret key, takes a ciphertext \(\mathsf {ct}\) and outputs a string x.
The scheme satisfies the following.
-
Statistical Correctness Against Malicious Encryptors: There is a negligible function \(\mathrm {negl}(\cdot )\) such that for any \(\lambda \in \mathbb {N}\) and input \(x \in \{ 0, 1 \}^*\), the following perfect correctness holds with probability at least \(1 - \mathrm {negl}(\lambda )\) over sampling \((\mathsf {pk}, \mathsf {sk}) \leftarrow \mathsf {PKE}.\mathsf {Gen}(1^\lambda )\):

-
Public-key Pseudorandomness: For \(\lambda \in \mathbb {N}\) let \(\ell (\lambda )\) be the length of the public key generated by \(\mathsf {PKE}.\mathsf {Gen}(1^\lambda )\), then,
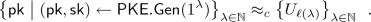
-
Encryption Security: For every polynomial \(l(\cdot )\),

where \(\lambda \in \mathbb {N}\) and \(x_0, x_1 \in \{ 0, 1 \}^{l(\lambda )}\).
Instantiations. Pseudorandom-key public-key encryption schemes are known based on LWE [Reg09].
Pseudorandom Function
Definition 5 (Pseudorandom Function (PRF))
[Pseudorandom Function (PRF)] A pseudorandom function scheme \((\mathsf {PRF}.\mathsf {Gen},\) \(\mathsf {PRF}.\mathsf {F})\) has the following syntax:
-
\(\mathsf {sk}\leftarrow \mathsf {PRF}.\mathsf {Gen}(1^\lambda , 1^{\ell (\lambda )}):\) a probabilistic algorithm that takes a security parameter \(1^\lambda \) and an output size \(\ell (\lambda )\) and outputs a secret key \(\mathsf {sk}\).
-
\(y = \mathsf {PRF}.\mathsf {F}_{\mathsf {sk}}(x):\) a deterministic algorithm that given the secret key, takes a string \(x \in \{0,1\}^*\) and outputs a string \(y \in \{ 0, 1 \}^{\ell (\lambda )}\).
The scheme satisfies the following property.
-
Pseudorandomness: For every quantum polynomial-size distinguisher \(\mathsf {D}= \{ \mathsf {D}_\lambda , \rho _\lambda \}_{\lambda \in \mathbb {N}}\) and polynomial \(\ell (\cdot )\) there is a negligible function \(\mu (\cdot )\) such that for all \(\lambda \in \mathbb {N}\),
$$ \left| \Pr _{\mathsf {sk}\leftarrow \mathsf {PRF}.\mathsf {Gen}(1^\lambda , 1^{\ell (\lambda )})} [\mathsf {D}_\lambda (\rho _\lambda )^{\mathsf {PRF}.\mathsf {F}_{\mathsf {sk}}(\cdot )} = 1] - \Pr _{f \leftarrow (\{0, 1\}^{\ell (\lambda )})^{(\{0, 1\}^*)}} [\mathsf {D}_\lambda (\rho _\lambda )^{f(\cdot )} = 1] \right| \le \mu (\lambda ) . $$
NIZK Argument for NP in the Common Random String Model. We define non-interactive computational zero-knowledge arguments for NP in the common random string model, with adaptive multi-theorem security.
Definition 6 (NICZK Argument for NP)
A non-interactive computational zero-knowledge argument system in the common random string model for a language \(\mathcal {L}\in \text{ NP } \) consists of 3 algorithms \((\mathsf {NIZK.\mathsf {Setup}}\) \(, \mathsf {NIZK.\mathsf {P}}\) \(, \mathsf {NIZK.\mathsf {V}})\) with the following syntax:
-
\(\mathsf {crs}\leftarrow \mathsf {NIZK.\mathsf {Setup}}(1^\lambda ) : \) A classical algorithm that on input security parameter \(\lambda \) simply samples a common uniformly random string \(\mathsf {crs}\).
-
\(\pi \leftarrow \mathsf {NIZK.\mathsf {P}}(\mathsf {crs}, x , w) : \) A probabilistic algorithm that on input \(\mathsf {crs}\), an instance \(x \in \mathcal {L}\) and a witness \(w\in \mathcal {R}_{\mathcal {L}}(x)\), outputs a proof \(\pi \).
-
\(\mathsf {NIZK.\mathsf {V}}(\mathsf {crs}, x, \pi ) \in \{ 0 , 1 \} : \) A deterministic algorithm that on input \(\mathsf {crs}\), an instance \(x \in \mathcal {L}\) and a proof \(\pi \), outputs a bit.
The protocol satisfies the following properties.
-
Perfect Completeness: For any \(\lambda \in \mathbb {N}\), \(x\in \mathcal {L}\cap \{0,1\}^\lambda \), \(w\in \mathcal {R}_{\mathcal {L}}(x)\),
$$ \Pr _{\begin{array}{c} \mathsf {crs}\leftarrow \mathsf {NIZK.\mathsf {Setup}}(1^\lambda ),\\ \pi \leftarrow \mathsf {NIZK.\mathsf {P}}(\mathsf {crs}, x , w) \end{array}} \Big [ \mathsf {NIZK.\mathsf {V}}(\mathsf {crs}, x, \pi ) = 1 \Big ] = 1 . $$ -
Adaptive Computational Soundness: For every quantum polynomial-size prover \(\mathsf {NIZK.\mathsf {P}}^* = \{ \mathsf {NIZK.\mathsf {P}}^*_\lambda , \rho _\lambda \}_{\lambda \in \mathbb {N}}\) there is a negligible function \(\mu (\cdot )\) such that for every security parameter \(\lambda \in \mathbb {N}\),
$$ \Pr _{\begin{array}{c} \mathsf {crs}\leftarrow \mathsf {NIZK.\mathsf {Setup}}(1^\lambda ),\\ (x, \pi ^*) \leftarrow \mathsf {NIZK.\mathsf {P}}^*_\lambda (\rho _\lambda , \mathsf {crs}) \end{array}} \Big [ (x \notin \mathcal {L}) \wedge \big ( 1 = \mathsf {NIZK.\mathsf {V}}(\mathsf {crs}, x, \pi ^*) \big ) \Big ] \le \mu (\lambda ) . $$ -
Multi-Theorem Adaptive Computational Zero Knowledge: There exists a polynomial-time simulator \(\mathsf {NIZK.\mathsf {Sim}}\) such that for every quantum polynomial-size distinguisher \(\mathsf {D}^*= \{ \mathsf {D}^*_\lambda , \rho _\lambda \}_{\lambda \in \mathbb {N}}\) there is a negligible function \(\mu (\cdot )\) such that for every security parameter \(\lambda \in \mathbb {N}\),
$$ \left| P_{\lambda , \mathsf {Real}} - P_{\lambda , \mathsf {Simulated}}\right| \le \mu (\lambda ) , $$where,
$$ P_{\lambda , \mathsf {Real}} := \Pr _{\mathsf {crs}\leftarrow \mathsf {NIZK.\mathsf {Setup}}(1^\lambda )} \Big [ \mathsf {D}^*_{\lambda }(\rho _{\lambda }, \mathsf {crs})^{\mathsf {NIZK.\mathsf {P}}(\mathsf {crs}, \cdot , \cdot )} = 1 \Big ] , $$$$ P_{\lambda , \mathsf {Simulated}} := \Pr _{(\mathsf {\tilde{crs}}, \mathsf {td}) \leftarrow \mathsf {NIZK.\mathsf {Sim}}(1^\lambda )} \Big [ \mathsf {D}^*_{\lambda }(\rho _{\lambda }, \mathsf {\tilde{crs}})^{\mathsf {NIZK.\mathsf {Sim}}(\mathsf {td}, \cdot )} = 1 \Big ] , $$where,
-
In every query that \(\mathsf {D}^*\) makes to the oracle, it sends a pair \((x, w)\) where \(x \in \mathcal {L}\cap \{0, 1\}^\lambda \) and \(w\in \mathcal {R}_{\mathcal {L}}(x)\).
-
\(\mathsf {NIZK.\mathsf {P}}(\mathsf {crs}, \cdot , \cdot )\) is the prover algorithm and \(\mathsf {NIZK.\mathsf {Sim}}(\cdot , \cdot )\) acts only on its sampled trapdoor \(\mathsf {td}\) and on x.
-
Instantiations. Non-interactive computational zero-knowledge arguments for NP in the common random string model with both adaptive soundness and zero knowledge are known based on LWE [CCH+19, PS19].
Malicious Designated-Verifier Non-interactive Zero-Knowledge for QMA. We define non-interactive zero-knowledge protocols in the malicious designated-verifier model (MDV-NIZK) for QMA, with adaptive (and non-adaptive) multi-theorem security.
Definition 7 (MDV-NICZK Argument for QMA)
A non-interactive computational zero-knowledge argument system for in the malicious designated-verifier model for a gap problem \((\mathcal {L}_{yes}, \mathcal {L}_{no}) = \mathcal {L}\in \text{ QMA }\) consists of 4 algorithms \((\mathsf {Setup}\) \(, \mathsf {VSetup}\) \(, \mathsf {P}\) \(, \mathsf {V})\) with the following syntax:
-
\(\mathsf {crs}\leftarrow \mathsf {Setup}(1^\lambda ) : \) A classical algorithm that on input security parameter \(\lambda \) simply samples a common uniformly random string \(\mathsf {crs}\).
-
\((\mathsf {pvk}, \mathsf {svk}) \leftarrow \mathsf {VSetup}(\mathsf {crs}) : \) A classical algorithm that on input \(\mathsf {crs}\) samples a pair of public and secret verification keys.
-
\(|{\pi }\rangle \leftarrow \mathsf {P}(\mathsf {crs}, \mathsf {pvk}, x , |{w}\rangle ^{\otimes k(\lambda )}) : \) A quantum algorithm that on input \(\mathsf {crs}\), the public verification key \(\mathsf {pvk}\), an instance \(x \in \mathcal {L}_{yes}\) and polynomially-many identical copies of a witness \(|{w}\rangle \in \mathcal {R}_{\mathcal {L}}(x)\) (\(k(\cdot )\) is some polynomial), outputs a quantum state \(|{\pi }\rangle \).
-
\(\mathsf {V}(\mathsf {crs}, \mathsf {svk}, x, |{\pi }\rangle ) \in \{ 0 , 1 \} : \) A quantum algorithm that on input \(\mathsf {crs}\), secret verification key \(\mathsf {svk}\), an instance \(x \in \mathcal {L}\) and a quantum proof \(|{\pi }\rangle \), outputs a bit.
The protocol satisfies the following properties.
-
Statistical Completeness: There is a polynomial \(k(\cdot )\) and a negligible function \(\mu (\cdot )\) s.t. for any \(\lambda \in \mathbb {N}\), \(x\in \mathcal {L}_{yes}\cap \{0,1\}^\lambda \), \(|{w}\rangle \in \mathcal {R}_{\mathcal {L}}(x)\), \(\mathsf {crs}\in \mathsf {Setup}(1^\lambda )\), \((\mathsf {pvk}, \mathsf {svk}) \in \mathsf {VSetup}(\mathsf {crs})\),
$$ \Pr _{|{\pi }\rangle \leftarrow \mathsf {P}(\mathsf {crs}, \mathsf {pvk}, x , |{w}\rangle ^{\otimes k(\lambda )})} \Big [ \mathsf {V}(\mathsf {crs}, \mathsf {svk}, x, |{\pi }\rangle ) = 1 \Big ] \ge 1 - \mu (\lambda ) . $$ -
Multi-Theorem Adaptive Computational Soundness: For every quantum polynomial-size prover \(\mathsf {P}^*= \{ \mathsf {P}^*_\lambda , \rho _\lambda \}_{\lambda \in \mathbb {N}}\) there is a negligible function \(\mu (\cdot )\) such that for every security parameter \(\lambda \in \mathbb {N}\),
$$ \Pr _{\begin{array}{c} \mathsf {crs}\leftarrow \mathsf {Setup}(1^\lambda ),\\ (\mathsf {pvk}, \mathsf {svk}) \leftarrow \mathsf {VSetup}(\mathsf {crs}),\\ (x, |{\pi ^*}\rangle ) \leftarrow \mathsf {P}^*_\lambda (\rho _\lambda , \mathsf {crs}, \mathsf {pvk})^{\mathsf {V}(\mathsf {crs}, \mathsf {svk}, \cdot , \cdot )} \end{array}} \Big [ (x \in \mathcal {L}_{no}) \wedge \big ( 1 = \mathsf {V}(\mathsf {crs}, \mathsf {svk}, x, |{\pi ^*}\rangle ) \big ) \Big ] \le \mu (\lambda ) . $$ -
Multi-Theorem Adaptive Computational Zero Knowledge: There exists a quantum polynomial-time simulator \(\mathsf {Sim}\) such that for every quantum polynomial-size distinguisher \(\mathsf {D}^*= \{ \mathsf {D}^*_\lambda , \rho _\lambda \}_{\lambda \in \mathbb {N}}\) there is a negligible function \(\mu (\cdot )\) such that for every security parameter \(\lambda \in \mathbb {N}\),
$$ \left| \Pr _{\mathsf {crs}\leftarrow \mathsf {Setup}(1^\lambda )} \Big [ \mathsf {D}^*_{\lambda }(\rho _{\lambda }, \mathsf {crs})^{\mathsf {P}(\mathsf {crs}, \cdot , \cdot , \cdot )} = 1 \Big ] - \Pr _{(\mathsf {\tilde{crs}}, \mathsf {td}) \leftarrow \mathsf {Sim}(1^\lambda )} \Big [ \mathsf {D}^*_{\lambda }(\rho _{\lambda }, \mathsf {\tilde{crs}})^{\mathsf {Sim}(\mathsf {td}, \cdot , \cdot )} = 1 \Big ] \right| \le \mu (\lambda ) , $$where,
-
In every query that \(\mathsf {D}^*\) makes to the oracle, it sends a triplet \((\mathsf {pvk^*}, x, |{w}\rangle ^{\otimes k(\lambda )})\) where \(\mathsf {pvk^*}\) can be arbitrary, \(x \in \mathcal {L}_{yes}\cap \{0, 1\}^\lambda \) and \(|{w}\rangle \in \mathcal {R}_{\mathcal {L}}(x)\).
-
\(\mathsf {P}(\mathsf {crs}, \cdot , \cdot , \cdot )\) is the prover algorithm and \(\mathsf {Sim}(\cdot , \cdot )\) acts only on its sampled trapdoor \(\mathsf {td}\) and on \(\mathsf {pvk^*}, x\).
-
We note that the standard (non-adaptive) soundness guarantees the following:
Definition 8 (MDV-NICZK Argument for QMA with Standard Soundness)
A non-interactive computational zero-knowledge argument system in the malicious designated-verifier model for a gap problem \((\mathcal {L}_{yes}, \mathcal {L}_{no}) = \mathcal {L}\in \text{ QMA }\) has standard non-adaptive soundness if it satisfies the same properties described in Definition 7, with the only change that instead of satisfying multi-theorem adaptive soundness, it satisfies the following guarantee:
-
Multi-Theorem Computational Soundness: For every quantum polynomial-size prover \(\mathsf {P}^*= \{ \mathsf {P}^*_\lambda , \rho _\lambda \}_{\lambda \in \mathbb {N}}\) and \(\{ x_\lambda \}_{\lambda \in \mathbb {N}}\) where \(\forall \lambda \in \mathbb {N}: x_\lambda \in \mathcal {L}_{no}\), there is a negligible function \(\mu (\cdot )\) such that for every security parameter \(\lambda \in \mathbb {N}\),
$$ \Pr _{\begin{array}{c} \mathsf {crs}\leftarrow \mathsf {Setup}(1^\lambda ),\\ (\mathsf {pvk}, \mathsf {svk}) \leftarrow \mathsf {VSetup}(\mathsf {crs}),\\ |{\pi ^*}\rangle \leftarrow \mathsf {P}^*_\lambda (\rho _\lambda , \mathsf {crs}, \mathsf {pvk})^{\mathsf {V}(\mathsf {crs}, \mathsf {svk}, \cdot , \cdot )} \end{array}} \Big [ 1 = \mathsf {V}(\mathsf {crs}, \mathsf {svk}, x, |{\pi ^*}\rangle ) \Big ] \le \mu (\lambda ) . $$
3 Non-interactive Zero-Knowledge Protocol
In this section we describe a non-interactive computational zero-knowledge argument system in the malicious designated-verifier model for an arbitrary \(\mathcal {L}\in \text{ QMA }\), according to Definition 7.
Ingredients and notation
-
A non-interactive zero-knowledge argument for NP \((\mathsf {NIZK.\mathsf {Setup}},\) \(\mathsf {NIZK.\mathsf {P}},\) \(\mathsf {NIZK.\mathsf {V}})\) in the common random string model.
-
A pseudorandom function \((\mathsf {PRF}.\mathsf {Gen}, \mathsf {PRF}.\mathsf {F})\).
-
A leveled fully-homomorphic encryption scheme \((\mathsf {FHE.Gen},\) \(\mathsf {FHE.Enc},\) \(\mathsf {FHE.Eval},\) \(\mathsf {FHE.Dec})\) with circuit privacy.
-
A public-key encryption scheme \((\mathsf {PKE}.\mathsf {Gen}, \mathsf {PKE}.\mathsf {Enc}, \mathsf {PKE}.\mathsf {Dec})\) with pseudorandom public keys.
-
A 3-message quantum sigma protocol \((\varXi .\mathsf {P}, \varXi .\mathsf {V})\) for QMA.
We describe the protocol in Fig. 1.
The (statistical) completeness of the protocol follows readily from the perfect completeness of the \(\mathsf {NIZK}\) scheme, the perfect correctness of \(\mathsf {FHE}\) and the statistical completeness of the quantum sigma protocol \((\varXi .\mathsf {P}, \varXi .\mathsf {V})\). We next prove the soundness and zero knowledge of the protocol.
3.1 Soundness
We prove that the protocol has multi-theorem computational soundness (as in Definition 8). By standard generic compilation and sub-exponential hardness of LWE we extend our soundness to be adaptive (as in Definition 7).
Proposition 1 (The Protocol has Multi-theorem Computational Soundness)
[The Protocol has Multi-theorem Computational Soundness] For every quantum polynomial-size prover \(\mathsf {P}^*= \{ \mathsf {P}^*_\lambda , \rho _\lambda \}_{\lambda \in \mathbb {N}}\) there is a negligible function \(\mu (\cdot )\) such that for every security parameter \(\lambda \in \mathbb {N}\) and \(x \in \mathcal {L}_{no}\cap \{ 0, 1 \}^\lambda \),
Proof
Let \(\mathsf {P}^*= \{ \mathsf {P}^*_\lambda , \rho _\lambda \}_{\lambda \in \mathbb {N}}\) a polynomial-size quantum prover and let \(\{ x_\lambda \}_{\lambda \in \mathbb {N}}\) s.t. \(\forall \lambda \in \mathbb {N}: x_\lambda \in \mathcal {L}_{no}\cap \{ 0, 1 \}^{\lambda }\). We prove soundness by a hybrid argument, that is, we consider a series of computationally-indistinguishable hybrid processes with output over \(\{ 0, 1 \}\), starting from the output of the verifier (for the prover’s false proof) in the real interaction, until we get to a distribution where the output of the verifier can be 1 with at most negligible probability. We define the following processes.
-
\(\mathsf {Hyb}_0:\) The output distribution of the verifier in the real interaction, that is, for
$$ (\mathsf {crs}, \mathsf {ek}) \leftarrow \mathsf {Setup}(1^\lambda ) , \big ( (\mathsf {ct}_{\mathsf {V}}, \mathsf {ct}_{r_\mathsf {V}}, \pi _\mathsf {V}), (\mathsf {prfk}, \mathsf {fhek}) \big ) \leftarrow \mathsf {VSetup}(\mathsf {crs}, \mathsf {ek}) , $$$$ |{\pi ^*}\rangle \leftarrow \mathsf {P}^*_\lambda \big ( \rho _\lambda , (\mathsf {crs}, \mathsf {ek}), (\mathsf {ct}_{\mathsf {V}}, \mathsf {ct}_{r_\mathsf {V}}, \pi _\mathsf {V}) \big )^{\mathsf {V}((\mathsf {crs}, \mathsf {ek}), (\mathsf {prfk}, \mathsf {fhek}), \cdot , \cdot )} , $$the output bit \(\mathsf {V}((\mathsf {crs}, \mathsf {ek}), (\mathsf {prfk}, \mathsf {fhek}), x, |{\pi ^*}\rangle )\).
-
\(\mathsf {Hyb}_1:\) This hybrid process is identical to \(\mathsf {Hyb}_0\), with the exception that \(\mathsf {ek}\) is sampled as a public key for the PKE scheme \((\mathsf {ek}, \mathsf {sk}) \leftarrow \mathsf {PKE}.\mathsf {Gen}(1^\lambda )\), rather than as a random string of the same length. To move to this hybrid we will use the fact that the public keys of the PKE scheme are pseudorandom.
-
\(\mathsf {Hyb}_2:\) This hybrid process is identical to \(\mathsf {Hyb}_1\), with the exception that the verification algorithm (described in step 4 of the protocol) changes. The new verifier \(\tilde{\mathsf {V}}\) still makes sure that \(\pi _\mathsf {P}\) is a valid proof for \((\hat{\mathsf {ct}}_{\mathsf {P}}, \mathsf {ct}_{r_\varXi }, \mathsf {ek})\), but the second check changes to the following: Let \(r_{\varXi } = \mathsf {PKE}.\mathsf {Dec}_{\mathsf {sk}}(\mathsf {ct}_{r_\varXi })\), and let \(\gamma = \varXi .\mathsf {P}_3(\beta _x, r_{\varXi })\). Then \(\tilde{\mathsf {V}}\) accepts if \(1 = \varXi .\mathsf {V}(x, \alpha , \beta _x, \gamma )\). To move to this hybrid we will use the (adaptive) soundness property of the NP NIZK proof that \(\mathsf {P}^*\) provides.
-
\(\mathsf {Hyb}_3:\) This hybrid process is identical to \(\mathsf {Hyb}_2\), with the exception that when generating the CRS \((\mathsf {crs}, \mathsf {ek})\) and the public verification key \(\mathsf {pvk}= (\mathsf {ct}_{\mathsf {V}}, \mathsf {ct}_{r_\mathsf {V}}, \pi _\mathsf {V})\), (1) the CRS for the NP NIZK is simulated \((\mathsf {crs}, \mathsf {td}) \leftarrow \mathsf {NIZK.\mathsf {Sim}}(1^\lambda )\), (2) the proof \(\pi _\mathsf {V}\) is simulated \(\pi _\mathsf {V}\leftarrow \mathsf {NIZK.\mathsf {Sim}}( \mathsf {td}, (\mathsf {ct}_{\mathsf {V}}, \mathsf {ct}_{r_\mathsf {V}}, \mathsf {ek}) )\) rather than generated by the NP NIZK prover. To move to this hybrid we use the zero-knowledge property of the NP NIZK proof that \(\mathsf {V}\) provides.
-
\(\mathsf {Hyb}_4:\) This hybrid process is identical to \(\mathsf {Hyb}_3\), with the exception that when generating \(\mathsf {pvk}= (\mathsf {ct}_{\mathsf {V}}, \mathsf {ct}_{r_\mathsf {V}}, \pi _\mathsf {V})\), \(\mathsf {ct}_{r_\mathsf {V}}\) is just an encryption of a string of zeros (of the same length) rather than the randomness \(r_\mathsf {V}\). To move to this hybrid we use the security of the PKE scheme.
-
\(\mathsf {Hyb}_5:\) This hybrid process is identical to \(\mathsf {Hyb}_4\), with the exception that when generating \(\mathsf {pvk}= (\mathsf {ct}_{\mathsf {V}}, \mathsf {ct}_{r_\mathsf {V}}, \pi _\mathsf {V})\), \(\mathsf {ct}_{\mathsf {V}}\) is just an encryption of a string of zeros (of the same length) rather than the FHE encryption of the secret PRF key \(\mathsf {prfk}\). To move to this hybrid we use the security of the FHE scheme.
-
\(\mathsf {Hyb}_6:\) This hybrid process is identical to \(\mathsf {Hyb}_5\), with the exception that the modified verification algorithm \(\tilde{\mathsf {V}}\) from \(\mathsf {Hyb}_2\) is now going to be a new stateful algorithm \(\tilde{\mathsf {V}}_s\). The new verifier \(\tilde{\mathsf {V}}_s\) still makes sure that \(\pi _\mathsf {P}\) is a valid proof for \((\hat{\mathsf {ct}}_{\mathsf {P}}, \mathsf {ct}_{r_\varXi }, \mathsf {ek})\), but the second check changes to the following: It is identical to that of \(\tilde{\mathsf {V}}\), except that \(\beta _x\) is now lazily sampled as a truly random string, that is, every time \(\mathsf {P}^*\) sends a query for some \(x'\), instead of computing \(\beta _{x'} = \mathsf {PRF}.\mathsf {F}_{\mathsf {prfk}}(x')\), \(\tilde{\mathsf {V}}_s\) samples \(\beta _{x'}\) a truly random string of the same length and remembers it for future queries by the prover (for the same \(x'\)). To move to this hybrid we use the pseudorandomnes guarantee of the PRF.
-
\(\mathsf {Hyb}_7:\) This hybrid process is identical to \(\mathsf {Hyb}_6\), with the exception that the behaviour of the verification algorithm \(\tilde{\mathsf {V}}_s\) changes in the following way: Consider t the first time step in the execution of \(\mathsf {P}^*\) (in \(\mathsf {Hyb}_6\)) such that with a noticeable probability, \(\mathsf {P}^*\) sends a pair \((x', |{\pi ^*}\rangle )\) such that (1) \(x' \in \mathcal {L}_{no}\) and (2) the modified verification algorithm \(\tilde{\mathsf {V}}_s\) accepts - this proof can be sent either as a query to the verification oracle, or as the final output of \(\mathsf {P}^*\) (in that case, t is the last time step of \(\mathsf {P}^*\) and \(x' = x\)). Now we define \(\mathsf {Hyb}_7\): the verification algorithm works as in \(\mathsf {Hyb}_6\) with the one change that if \(\mathsf {P}^*\) sends a query to the verification oracle before its time step t and this query is for a no-instance \(x' \in \mathcal {L}_{no}\), then we simply return 0 to \(\mathsf {P}^*\) as the verifier’s answer, without computing anything. Note that checking whether \(x' \in \mathcal {L}_{no}\) takes \(2^{O(|x'|)}\) timeFootnote 6, and thus the execution of this hybrid is inefficient. If such time step t does not exist (i.e. in each of the prover’s time steps, the probability for it to generate a false proof is only negligible), this process is identical to \(\mathsf {Hyb}_6\).
We now explain why the outputs of each two consecutive hybrids are computationally indistinguishableFootnote 7. We will then use the last hybrid process to show that soundness of the protocol follows from the soundness of the quantum sigma protocol \((\varXi .\mathsf {P}, \varXi .\mathsf {V})\).
-
\(\mathsf {Hyb}_0 \approx _{c} \mathsf {Hyb}_1:\) Follows readily from the pseudorandomness property of the public keys generated by \(\mathsf {PKE}.\mathsf {Gen}(1^\lambda )\).
-
\(\mathsf {Hyb}_1 \approx _{c} \mathsf {Hyb}_2:\) Follows from the adaptive soundness of the NIZK protocol for NP, the statistical correctness of the PKE scheme and the perfect correctness of the FHE scheme. We explain in more detail: Assume the output bits of \(\mathsf {Hyb}_1\) and \(\mathsf {Hyb}_2\) are distinguishable with some noticeable advantage, then by the perfect correctness of the FHE evaluation, it follows that with a noticeable probability, either (1) there was an error in the decryption process of the PKE scheme at least once, or (2) \(\mathsf {P}^*\) generated a false proof for the NP NIZK scheme at least once. We prove that both happen with at most negligible probability, and thus the statistical distance between the output bits of \(\mathsf {Hyb}_1\) and \(\mathsf {Hyb}_2\) is at most negligible. The correctness guarantee of the PKE scheme is that when the public key is sampled honestly, which is true in our case, then with overwhelming probability over the randomness of \(\mathsf {PKE}.\mathsf {Gen}(1^\lambda )\), the decryption is perfectly correct, regardless of the randomness used for the encryption (which in our case is possibly malicious, as it is chosen by \(\mathsf {P}^*\)). This implies that with at most negligible probability there is an error in the decryption process \(\mathsf {PKE}.\mathsf {Dec}_{\mathsf {sk}}(\cdot )\). If \(\mathsf {P}^*\) manages to give a false proof \(\pi _{\mathsf {P}}^*\) for some tuple \((\hat{\mathsf {ct}}_{\mathsf {P}}, \mathsf {ct}_{r_\varXi }, \mathsf {ek})\) with a noticeable probability \(\varepsilon \) then we can use it to break the adaptive soundness of the NP NIZK scheme: We guess the index of the query (to the verification oracle \(\tilde{\mathsf {V}}((\mathsf {crs}, \mathsf {ek}), (\mathsf {prfk}, \mathsf {fhek}), \cdot , \cdot )\)) where \(\mathsf {P}^*\) gives such false proof, and with probability at least \(\varepsilon \cdot \frac{1}{t}\), where t is the (polynomial) running time of \(\mathsf {P}^*\), we find such false proof. This implies that \(\varepsilon \) has to be at most negligible i.e. \(\mathsf {P}^*\) cannot produce a false proof for the NP NIZK with a noticeable probability.
-
\(\mathsf {Hyb}_2 \approx _{c} \mathsf {Hyb}_3:\) Assume toward contradiction that the output bits of \(\mathsf {Hyb}_2\) and \(\mathsf {Hyb}_3\) are distinguishable with some noticeable advantage, we use the prover \(\mathsf {P}^*\) in order to construct a distinguisher \(\mathsf {D}\) that breaks the zero-knowledge property of the NP NIZK scheme (it seems that we don’t have to use the fact that the zero knowledge property of the NP NIZK is adaptive, but we will use it for the convenience of the proof and because it does not cause an extra cost in computational assumptions). \(\mathsf {D}\) will sample \((\mathsf {ek}, \mathsf {sk}) \leftarrow \mathsf {PKE}.\mathsf {Gen}(1^\lambda )\), honestly sample \((\mathsf {ct}_{\mathsf {V}}, \mathsf {ct}_{r_\mathsf {V}})\) with randomness r, and then get a common random string \(\mathsf {crs}\) from the NIZK zero knowledge challenger. \(\mathsf {D}\) then hands \((\mathsf {ct}_{\mathsf {V}}, \mathsf {ct}_{r_\mathsf {V}}, \mathsf {ek})\) along with the NP witness r and gets back either a real proof or a simulated proof. it then proceeds to run the malicious prover \(\mathsf {P}^*\) and at the end, by the verdict of the (modified) verification algorithm \(\tilde{\mathsf {V}}\) for the prover’s proof and instance, distinguishes between whether it got a simulated proof or a real proof. This follows from the fact that whenever \(\mathsf {D}\) gets a real proof (and CRS) then the view of \(\mathsf {P}^*\) is exactly its view in \(\mathsf {Hyb}_2\) and whenever \(\mathsf {D}\) gets a simulated proof (and CRS) then the view of \(\mathsf {P}^*\) is exactly its view in \(\mathsf {Hyb}_3\).
-
\(\mathsf {Hyb}_3 \approx _{c} \mathsf {Hyb}_4:\) Follows readily from the security of the PKE scheme.
-
\(\mathsf {Hyb}_4 \approx _{c} \mathsf {Hyb}_5:\) Follows readily from the security of the FHE scheme.
-
\(\mathsf {Hyb}_5 \approx _{c} \mathsf {Hyb}_6:\) Follows readily from the security of the PRF scheme.
-
\(\mathsf {Hyb}_6 \approx _{c} \mathsf {Hyb}_7:\) Note that by how we defined the time step t it follows that the change of returning 0 on queries for no-instances before time step t (rather than actually evaluating the verification algorithm \(\tilde{\mathsf {V}}_s\)) is unnoticeable to the prover \(\mathsf {P}^*\).
Now, assume toward contradiction that \(\mathsf {P}^*\) succeeds in breaking the soundness with a noticeable probability in the original execution of the protocol (i.e. in the process \(\mathsf {Hyb}_0\)), and by the fact \(\mathsf {Hyb}_0 \approx _{c} \mathsf {Hyb}_7\) it follows that the verifier accepts the prover’s false proof with some noticeable probability in the hybrid experiment \(\mathsf {Hyb}_7\). By the fact that with some noticeable probability \(\mathsf {P}^*\) succeeds in cheating in \(\mathsf {Hyb}_7\), it follows that a time step t exists where \(\mathsf {P}^*\) sends a pair \((x', |{\pi ^*}\rangle )\) such that \(x' \in \mathcal {L}_{no}\) and \(\tilde{\mathsf {V}}_s\) accepts the proof (this follows because in the last step of \(\mathsf {P}^*\)’s execution it sends noticeably often a successful false proof for \(x \in \mathcal {L}_{no}\)).
Now we consider the execution process of \(\mathsf {Hyb}_7\) and fix by an averaging argument the snapshot \(|{\psi }\rangle \) of the execution in the exact moment where \(\mathsf {P}^*\) sends a pair \((x', |{\pi ^*}\rangle )\) in its time step t, such that the snapshot maximizes the probability that \(x' \in \mathcal {L}_{no}\) and \(\tilde{\mathsf {V}}_s\) accepts the proof \(|{\pi ^*}\rangle \) (as a side note, this snapshot includes (1) all of the randomness (including setup information) in the process \(\mathsf {Hyb}_7\) until \(\mathsf {P}^*\)’s step t, (2) the inner quantum state of \(\mathsf {P}^*\) in step t, and of course a pair \((x', |{\pi ^*}\rangle )\) such that \(x' \in \mathcal {L}_{no}\).). It follows that the part \(\alpha \) and the extracted \(\gamma \) (both obtained from \(|{\pi ^*}\rangle \), recall \(\gamma \) is obtained by the extracted randomness \(r_{\varXi }\) and the random string \(\beta _{x'}\)) make a quantum sigma protocol verifier \(\varXi .\mathsf {V}\) accept the proof for a random challenge \(\beta \) with a noticeable probability.
We now describe a malicious prover \(\varXi .\mathsf {P}^*\) that breaks the soundness of the quantum sigma protocol \((\varXi .\mathsf {P}, \varXi .\mathsf {V})\), by using \(\mathsf {P}^*\) and the quantum advice \(|{\psi }\rangle \) in order to convince \(\varXi .\mathsf {V}\) to accept the no-instance \(x' \in \mathcal {L}_{no}\). \(\varXi .\mathsf {P}^*\) uses the snapshot \(|{\psi }\rangle \) and takes \(\alpha \) from \(|{\pi ^*}\rangle \) and sends it as the first sigma protocol message to \(\varXi .\mathsf {V}\). \(\varXi .\mathsf {V}\) returns a random challenge \(\beta \), and \(\varXi .\mathsf {P}^*\) treats this random challenge as the random \(\beta _{x'}\) for the verification procedure \(\tilde{\mathsf {V}}_{s}\). \(\varXi .\mathsf {P}^*\) then derives \(\gamma \) from \(|{\pi ^*}\rangle \) (as usual in \(\tilde{\mathsf {V}}_s\)) and sends it to \(\varXi .\mathsf {V}\). Recall that we know \(\varXi .\mathsf {V}\) accepts the proof with a noticeable probability, and thus \(\varXi .\mathsf {P}^*\) breaks the soundness of the quantum sigma protocol with noticeable probability, in contradiction.
We next use standard complexity leveraging to make the soundness adaptive, that is, by assuming that the security of our cryptographic primitives is sub-exponential we prove that the prover cannot choose the no-instance \(x \in \mathcal {L}_{no}\) adaptively. As mentioned in the preliminaries, the security of all of our primitives can be based on the hardness of LWE, and thus based on the sub-exponential hardness of LWE we can get adaptive soundness.
Proposition 2 (The Protocol has Multi-theorem Adaptive Computational Soundness)
[The Protocol has Multi-theorem Adaptive Computational Soundness] Assume there is a constant \(\varepsilon \in (0, 1)\) such that the cryptographic ingredients we use are secure against \(O(2^{\lambda ^{\varepsilon }})\)-time quantum algorithms for security parameter \(\lambda \). Then, by executing the protocol with security parameter \(\lambda := |x|^{\frac{2}{\varepsilon }}\) rather than \(\lambda = |x|\), for every quantum polynomial-size prover \(\mathsf {P}^*= \{ \mathsf {P}^*_{\lambda } , \rho _{\lambda } \}_{\lambda \in \mathbb {N}}\) there is a negligible function \(\mu (\cdot )\) such that for every security parameter \(\lambda \in \mathbb {N}\),
where the probability is above the following experiment:
Proof
The proof is almost identical to the proof of Proposition 1, with minor technical changes. Let \(\mathsf {P}^*= \{ \mathsf {P}^*_\lambda , \rho _\lambda \}_{\lambda \in \mathbb {N}}\) a polynomial-size quantum prover in Protocol 1 and as before, we prove soundness by a hybrid argument by considering almost the same series of hybrids processes, and the reductions that show the outputs of each consecutive pair of hybrids are indistinguishable, are also going to be slightly different.
More precisely, consider the exact same hybrids \(\mathsf {Hyb}_0, \cdots , \mathsf {Hyb}_7\) from the proof of Proposition 1, with only the following differences:
-
With accordance to the fact that we consider adaptive provers, in each hybrid process, the output of the malicious prover at the end of the execution is a pair \((x, |{\pi ^*}\rangle )\) rather than only a proof \(|{\pi ^*}\rangle \).
-
The output of each hybrid process is still a bit, but going to be the logical AND of (1) the verifier accepting the prover’s proof and instance x, and (2) the instance x is indeed a no-instance \(x \in \mathcal {L}_{no}\) (note that in the proof for Proposition 1 the output bit of the hybrids only considers the verdict of the verifier, as the no-instance \(x \in \mathcal {L}_{no}\) is already fixed).
We will next claim that the outputs of each pair of consecutive hybrids are computationally indistinguishable. For this, we will use the fact that given \(x \in \mathcal {L}= \mathcal {L}_{yes}\cup \mathcal {L}_{no}\), we can decide whether \(x \in \mathcal {L}_{no}\) or not in \(2^{O(|x|)}\) time.Footnote 8 We also use the fact that our primitives are assumed to be secure against sub-exponential time algorithms and we run the protocol with increased security parameter, more specifically, we assume that our primitives are secure against \(O(2^{\lambda ^{\varepsilon }})\)-time algorithms and we use security parameter \(\lambda = |x|^{\frac{2}{\varepsilon }}\), thus it follows that no \(O(2^{\lambda ^{\varepsilon }}) = O(2^{|x|^2})\)-time algorithm can break the security of the primitives.
In continuance to the above, by the exact same reductions from the proof of Proposition 1 with a single change, we have
The single change that we refer to is the check that the reduction makes when getting the final output of the prover. In the proof of Proposition 1, the final output of \(\mathsf {P}^*\) is a false proof \(|{\pi ^*}\rangle \) for a specific and pre-chosen x, while in our case (the adaptive case) it is a pair \((x, |{\pi ^*}\rangle )\) for an adaptively-chosen x. Instead of checking only the verdict of \(\mathsf {V}\), which can be done in polynomial time, the reduction in our case will also check that \(x \in \mathcal {L}_{no}\), which can be done in time \(2^{O(|x|)}\). This implies that our security reductions take \(2^{O(|x|)}\) time to execute, but they break primitives with security against \(O(2^{|x|^2})\)-time algorithms, which constitutes the needed contradiction. Finally, the algorithm \(\varXi .\mathsf {P}^*\) that uses \(\mathsf {P}^*\) in the process \(\mathsf {Hyb}_7\) in order to break the soundness of the quantum sigma protocol is exactly the same as before, and our proof is finished.
As mentioned before, by the fact that the security of the cryptographic ingredients in our protocol can be based on the hardness of LWE and the security reductions for the primitives are polynomial-time, we get the following corollary.
Corollary 1
Assume there is a constant \(\varepsilon \in (0, 1)\) such that LWE is hard for \(O(2^{n^{\varepsilon }})\)-time quantum algorithms (for LWE secret of n bits). Then, for every quantum polynomial-size prover \(\mathsf {P}^*= \{ \mathsf {P}^*_{\lambda } , \rho _{\lambda } \}_{\lambda \in \mathbb {N}}\) there is a negligible function \(\mu (\cdot )\) such that for every security parameter \(\lambda \in \mathbb {N}\),
where the probability is above the following experiment:
3.2 Zero Knowledge
We show that the protocol is multi-theorem adaptive computational zero-knowledgeFootnote 9, which holds even when the trusted setup samples only a common uniformly random string, and an adversarial polynomial-time (quantum) verifier samples its public verification key maliciously.
We next describe the simulator and then prove that the view that it generates is indistinguishable from the real one, against adaptive distinguishers that choose the statement to be proven only after seeing the common random string.
\(\mathsf {Sim}(1^\lambda ):\)
-
1.
CRS Simulation: Given a security parameter \(\lambda \), the first simulator output is the simulation of the CRS for the NP NIZK protocol and swapping \(\mathsf {ek}\) with a public key for the PKE scheme, that is, \(\mathsf {Sim}\) samples:
$$ (\mathsf {crs}, \mathsf {td}) \leftarrow \mathsf {NIZK.\mathsf {Sim}}(1^\lambda ) , (\mathsf {ek}, \mathsf {sk}) \leftarrow \mathsf {PKE}.\mathsf {Gen}(1^\lambda ) , $$outputs \((\mathsf {crs}, \mathsf {ek})\) as the simulated CRS and \((\mathsf {td}, \mathsf {sk})\) as the simulator trapdoor.
-
2.
Proof Simulation: Given the trapdoor \((\mathsf {td}, \mathsf {sk})\), a (possibly malicious) public verification key \(\mathsf {pvk}= (\mathsf {ct}_{\mathsf {V}}, \mathsf {ct}_{r_\mathsf {V}}, \pi _{\mathsf {V}})\) and a yes-instance \(x \in \mathcal {L}_{yes}\), the simulator does the following:
-
(a)
\(\mathsf {Sim}\) checks that \(\pi _\mathsf {V}\) is a valid proof for the tuple \((\mathsf {ct}_{\mathsf {V}}, \mathsf {ct}_{r_\mathsf {V}}, \mathsf {ek})\) and also actually verifies some of the statement itself: It decrypts \(r_\mathsf {V}= \mathsf {PKE}.\mathsf {Dec}_{\mathsf {sk}}(\mathsf {ct}_{r_\mathsf {V}})\) and checks that \(\mathsf {ct}_{\mathsf {V}}\) is obtained by running \(\mathsf {PRF}.\mathsf {Gen}, \mathsf {fhek}\leftarrow \mathsf {FHE.Gen}, \mathsf {FHE.Enc}_{\mathsf {fhek}}\) with randomness \(r_\mathsf {V}\). If the check is not accepted, \(\mathsf {Sim}\) returns \(\bot \).
-
(b)
\(\mathsf {Sim}\) derives \(\mathsf {prfk}\) from \(r_\mathsf {V}\), computes \(\beta _x = \mathsf {PRF}.\mathsf {F}_{\mathsf {prfk}}(x)\) and then executes \((\alpha , \gamma ) \leftarrow \varXi .\mathsf {Sim}(x, \beta _x)\).
-
(c)
\(\mathsf {Sim}\) performs a circuit-private homomorphic evaluation \(\hat{\mathsf {ct}}_\mathsf {P}\leftarrow \mathsf {FHE.Eval}(C_{\gamma }, \mathsf {ct}_\mathsf {V})\), where \(C_\gamma \) is the circuit that always outputs \(\gamma \).
-
(d)
\(\mathsf {Sim}\) encrypts \(\mathsf {ct}_{r_{\varXi }} \leftarrow \mathsf {PKE}.\mathsf {Enc}_{\mathsf {ek}}(0^{\ell })\), where \(\ell \) is the length of the randomness for the prover in the quantum sigma protocol.
-
(e)
Finally, \(\mathsf {Sim}\) simulates the non-interactive zero-knowledge proof \(\pi _\mathsf {P}\), by executing \(\pi _{\mathsf {P}} \leftarrow \mathsf {NIZK.\mathsf {Sim}}(\mathsf {td}, (\hat{\mathsf {ct}}_{\mathsf {P}}, \mathsf {ct}_{r_\varXi }, \mathsf {ek}))\).
\(\mathsf {Sim}\) outputs \((\alpha , \hat{\mathsf {ct}}_{\mathsf {P}}, \mathsf {ct}_{r_{\varXi }}, \pi _{\mathsf {P}})\).
-
(a)
We now prove that the simulated proofs that the simulator generates are computationally indistinguishable from the real proofs that the prover generates.
Proposition 3 (The Protocol is Multi-theorem Adaptive Computational Zero-knowledge)
[The Protocol is Multi-theorem Adaptive Computational Zero-knowledge] For every quantum polynomial-size distinguisher \(\mathsf {D}^*= \{ \mathsf {D}^*_\lambda , \rho _\lambda \}_{\lambda \in \mathbb {N}}\) there is a negligible function \(\mu (\cdot )\) such that for every security parameter \(\lambda \in \mathbb {N}\),
where,
where in every query that \(\mathsf {D}^*\) makes to the oracle, it sends a triplet \((\mathsf {pvk^*}, x, |{w}\rangle ^{\otimes k(\lambda )})\) such that \(\mathsf {pvk^*}\) can be arbitrary, \(x \in \mathcal {L}_{yes}\cap \{0, 1\}^\lambda \) and \(|{w}\rangle \in \mathcal {R}_{\mathcal {L}}(x)\).
Proof
Let \(\mathsf {D}^*= \{ \mathsf {D}^*_\lambda , \rho _\lambda \}_{\lambda \in \mathbb {N}}\) a polynomial-size quantum distinguisher. We prove zero knowledge by a hybrid argument, that is, we consider a series of computationally-indistinguishable hybrid processes with 1-bit outputs, starting from the output of \(\mathsf {D}^*\) when getting real proofs, until we get to the output of \(\mathsf {D}^*\) when getting simulated proofs. We define the following processes.
-
\(\mathsf {Hyb}_0:\) The output of \(\mathsf {D}^*\) when getting honestly-generated proofs, that is, it gets the CRS from \((\mathsf {crs}, \mathsf {ek}) \leftarrow \mathsf {Setup}(1^\lambda )\) and the proofs from \(\mathsf {P}^*((\mathsf {crs}, \mathsf {ek}), \cdot , \cdot , \cdot )\), as described in the experiment of \(P_{\mathsf {Real}}\).
-
\(\mathsf {Hyb}_1:\) This hybrid process is identical to \(\mathsf {Hyb}_0\), with the exception that \(\mathsf {ek}\) is sampled as a public key for the PKE scheme \((\mathsf {ek}, \mathsf {sk}) \leftarrow \mathsf {PKE}.\mathsf {Gen}(1^\lambda )\), rather than as a random string of the same length. To move to this hybrid we will use the fact that the public keys of the PKE scheme are pseudorandom.
-
\(\mathsf {Hyb}_2:\) This hybrid process is identical to \(\mathsf {Hyb}_1\), with the exception that the prover adds another validity check, over the one checking the validity of the proof \(\pi _{\mathsf {V}}\): It decrypts \(r_\mathsf {V}= \mathsf {PKE}.\mathsf {Dec}_{\mathsf {sk}}(\mathsf {ct}_{r_\mathsf {V}})\) and checks that \(\mathsf {ct}_{\mathsf {V}}\) is obtained by running \(\mathsf {PRF}.\mathsf {Gen}, \mathsf {fhek}\leftarrow \mathsf {FHE.Gen}, \mathsf {FHE.Enc}_{\mathsf {fhek}}\) with randomness \(r_\mathsf {V}\). To move to this hybrid we will use the adaptive soundness of the NP NIZK.
-
\(\mathsf {Hyb}_3:\) This hybrid process is identical to \(\mathsf {Hyb}_2\), with the exception that we simulate the NP NIZK proofs, that is, (1) when sampling the NP NIZK common random string \(\mathsf {crs}\) from the total CRS \((\mathsf {crs}, \mathsf {ek})\), we sample a simulated CRS \((\mathsf {crs}, \mathsf {td}) \leftarrow \mathsf {NIZK.\mathsf {Sim}}(1^\lambda )\) instead of \(\mathsf {crs}\leftarrow \mathsf {NIZK.\mathsf {Setup}}(1^\lambda )\), and (2) every time we compute an NP NIZK proof \(\pi _\mathsf {P}\) as part of the QMA NIZK proof \(|{\pi }\rangle \), we use the NP NIZK simulator \(\pi _\mathsf {P}\leftarrow \mathsf {NIZK.\mathsf {Sim}}(\mathsf {td}, (\hat{\mathsf {ct}}_{\mathsf {P}}, \mathsf {ct}_{r_{\varXi }}, \mathsf {ek}))\) rather than \(\pi _\mathsf {P}\leftarrow \mathsf {NIZK.\mathsf {P}}(\mathsf {crs}, (\hat{\mathsf {ct}}_{\mathsf {P}}, \mathsf {ct}_{r_{\varXi }}, \mathsf {ek}))\) (where we execute \(\mathsf {NIZK.\mathsf {P}}\) along with a witness for the statement). To move to this hybrid we will use the adaptive zero knowledge property of the NP NIZK.
-
\(\mathsf {Hyb}_4:\) This hybrid process is identical to \(\mathsf {Hyb}_3\), with the exception that \(\mathsf {ct}_{r_{\varXi }}\) is an encryption of zeros rather than the randomness for the circuit \(C_{x, r_\varXi }\), which is homomorphically evaluated. To move to this hybrid we will use the security of the PKE scheme.
-
\(\mathsf {Hyb}_5:\) This hybrid process is identical to \(\mathsf {Hyb}_4\), with the exception that when computing the evaluated ciphertext \(\hat{\mathsf {ct}}_{\mathsf {P}}\), instead of homomorphically evaluating the circuit \(C_{x, r_\varXi }\), we compute \(C_{x, r_\varXi }\) in the clear and inject the result by circuit-private evaluation. More precisely, the prover does the following: First, it regularly computes \(\alpha = \varXi .\mathsf {P}(|{w}\rangle ^{\otimes k(\lambda )} ; r_\varXi )\), for randomness \(r_\varXi \). It derives \(\mathsf {prfk}\) from the decrypted randomness \(r_\mathsf {V}\), computes \(\beta _x = \mathsf {PRF}.\mathsf {F}_{\mathsf {prfk}}(x)\), \(\gamma = \varXi .\mathsf {P}_3(\beta _x, r_\varXi )\), and then \(\hat{\mathsf {ct}}_{\mathsf {P}} \leftarrow \mathsf {FHE.Eval}(C_{\gamma }, \mathsf {ct}_{\mathsf {V}})\), where \(C_{\gamma }\) is the circuit that always outputs \(\gamma \). To move to this hybrid we will use the circuit-privacy property of the FHE’s evaluation algorithm.
-
\(\mathsf {Hyb}_6:\) This hybrid process is identical to \(\mathsf {Hyb}_5\), with the exception that when computing \((\alpha , \gamma )\) we use the quantum sigma protocol (special zero-knowledge) simulator, that is, the prover first computes \(\beta _x\) (from \(\mathsf {prfk}\) which is derived from \(r_\mathsf {V}\)) and then computes \((\alpha , \gamma ) \leftarrow \varXi .\mathsf {Sim}(x, \beta _x)\) and as before, \(\alpha \) is sent in the clear and \(\gamma \) is sent through homomorphically evaluating the circuit \(C_{\gamma }\) on \(\mathsf {ct}_\mathsf {V}\). To move to this hybrid we will use the special zero knowledge property of the quantum sigma protocol. Note that the actions of the prover in this hybrid process are exactly the ones of the QMA NIZK simulator \(\mathsf {Sim}\) and thus \(\mathsf {Hyb}_6\) is exactly the process described in the experiment of \(P_{\mathsf {Simulated}}\).
We now claim that the outputs of each two consecutive hybrids are computationally indistinguishable, which will finish our proof.
-
\(\mathsf {Hyb}_0 \approx _{s} \mathsf {Hyb}_1:\) Follows readily from the pseudorandomness property of the public keys generated by \(\mathsf {PKE}.\mathsf {Gen}(1^\lambda )\).
-
\(\mathsf {Hyb}_1 \approx _{s} \mathsf {Hyb}_2:\) Follows from the adaptive soundness of the NIZK protocol for NP and the statistical correctness of the PKE scheme. We explain in more detail: First, note that whenever the NP statement that \(\mathsf {D}^*\) proves in \(\pi _\mathsf {V}\) is correct and the decryption of the PKE is correct, then the output distribution of the proof oracle is identical between the two hybrid processes, as the additional check that is made in \(\mathsf {Hyb}_2\) passes successfully. Also note that whenever the proof \(\pi _{\mathsf {V}}\) is invalid, then both processes output \(\bot \) and are identical. It follows that the only times that the output distributions of the proof oracles are not identical is whenever there is an error in the decryption of the PKE, or the proof \(\pi _{\mathsf {V}}\) checks successfully but the statement is false i.e. whenever \(\mathsf {D}^*\) breaks the adaptive soundness of the NP NIZK protocol. Since both of the above happen with at most negligible probability, it follows that only with negligible probability the outputs of \(\mathsf {Hyb}_1\) and \(\mathsf {Hyb}_2\) can be distinguished, and the statistical closeness between them follows.
-
\(\mathsf {Hyb}_2 \approx _{c} \mathsf {Hyb}_3:\) Follows readily from the adaptive zero-knowledge property of the NP NIZK protocol.
-
\(\mathsf {Hyb}_3 \approx _{c} \mathsf {Hyb}_4:\) Follows from the security of the PKE scheme. Specifically, the encrypted randomness \(r_\varXi \) for every query is simply a random string (independent of all other operations in the process) and thus all of these random strings can be chosen at the beginning of the execution of the process, and thus we fix by an averaging argument the strings \(r^1_\varXi , \cdots , r^q_\varXi \) that maximize the distinguishability of \(\mathsf {D}^*\), where the q is the (polynomial) number of queries that \(\mathsf {D}^*\) makes to the proof oracle. It then follows that if \(\mathsf {D}^*\) distinguishes between \(\mathsf {Hyb}_3\) and \(\mathsf {Hyb}_4\) then it distinguishes between encryptions of \(r^1_\varXi , \cdots , r^q_\varXi \) and encryptions of zeros, and since the single-message security of public-key encryption schemes implies many-message security the indistinguishability \(\mathsf {Hyb}_3 \approx _{c} \mathsf {Hyb}_4\) follow.
-
\(\mathsf {Hyb}_4 \approx _{s} \mathsf {Hyb}_5:\) Follows by a hybrid argument, by the circuit-privacy property of the FHE scheme and from the fact that the prover makes the additional check on the public verification key, which checks that \(\mathsf {ct}_{\mathsf {V}}\) is obtained by running \(\mathsf {PRF}.\mathsf {Gen}, \mathsf {fhek}\leftarrow \mathsf {FHE.Gen}, \mathsf {FHE.Enc}_{\mathsf {fhek}}\) with the extracted randomness \(r_\mathsf {V}\). More precisely, let q be the number of queries that \(\mathsf {D}^*\) makes to the proof oracle, and for \(i \in \{ 0, 1, \cdots , q \}\) we define \(\mathsf {Hyb}^{i}_4\) as the process that performs the homomorphic evaluation of \(C_{x, r_\varXi }\) (rather than computing it in the clear and then injecting the result, as done in \(\mathsf {Hyb}_5\)) starting from query number \(i+1\) that \(\mathsf {D}^*\) makes, thus \(\mathsf {Hyb}^{0}_4 = \mathsf {Hyb}_4\), \(\mathsf {Hyb}^{q}_4 = \mathsf {Hyb}_5\). If \(\mathsf {Hyb}_4\) and \(\mathsf {Hyb}_5\) are distinguishable then for some \(i \in \{ 0, 1, \cdots , q-1 \}\), \(\mathsf {Hyb}^{i}_4\) and \(\mathsf {Hyb}^{i+1}_4\) are distinguishable. We fix by an averaging argument a snapshot of the execution until after the point that \(\mathsf {D}^*\) sends the \((i+1)\)-th query to the proof oracle. If the check that the prover makes in the beginning, which includes both checking the validity of the NP proof \(\pi _{\mathsf {V}}\) and also checking the validity of creating \(\mathsf {ct}_{\mathsf {V}}\) from the extracted randomness \(r_\mathsf {V}\), fails, then the hybrid processes are the same as the answer of the proof oracle will be \(\bot \). In case the check is successful, it follows that the outputs of the circuits \(C_{x, r_\varXi }\) and \(C_\gamma \) on the input \(\mathsf {prfk}\) (which is encrypted inside \(\mathsf {ct}_{\mathsf {V}}\)) are the same, and thus it follows that the distinguisher between the hybrids \(\mathsf {Hyb}^{i}_4\) and \(\mathsf {Hyb}^{i+1}_4\) can be used to break the (even statistical) circuit privacy of the FHE evaluation.
-
\(\mathsf {Hyb}_5 \approx _{c} \mathsf {Hyb}_6:\) The proof is very similar to the proof for the indistinguishability \(\mathsf {Hyb}_4 \approx _{c} \mathsf {Hyb}_5\), as the indistinguishability follows by a hybrid argument and from the special zero knowledge property of the quantum sigma protocol. More precisely, for \(i \in \{ 0, 1, \cdots , q \}\) we define \(\mathsf {Hyb}^{i}_5\) as the process that uses \(\varXi .\mathsf {P}\) (and the polynomially-many copies of the quantum witness) in order to generate \((\alpha , \gamma )\) (rather than computing it using the simulator) starting from query number \(i+1\) that \(\mathsf {D}^*\) makes, thus \(\mathsf {Hyb}^{0}_5 = \mathsf {Hyb}_5\), \(\mathsf {Hyb}^{q}_5 = \mathsf {Hyb}_6\). If \(\mathsf {Hyb}_5\) and \(\mathsf {Hyb}_6\) are distinguishable then for some \(i \in \{ 0, 1, \cdots , q-1 \}\), \(\mathsf {Hyb}^{i}_5\) and \(\mathsf {Hyb}^{i+1}_5\) are distinguishable. We fix by an averaging argument a snapshot of the execution until after the point that \(\mathsf {D}^*\) sends the \((i+1)\)-th query to the proof oracle, this in particular fixes the yes instance \(x \in \mathcal {L}_{yes}\), the quantum witness \(|{w}\rangle \) and the pseudorandomness \(\beta _x\). It follows that the distinguisher between the hybrids \(\mathsf {Hyb}^{i}_5\) and \(\mathsf {Hyb}^{i+1}_5\) can be used to tell the difference between a tuple \((\alpha , \gamma )\) that was generated by \(\varXi .\mathsf {P}\) and a tuple that was generated by \(\varXi .\mathsf {Sim}\), in contradiction the special zero knowledge property of the protocol \((\varXi .\mathsf {P}, \varXi .\mathsf {V})\).
Notes
- 1.
In particular, we do not assume that the message \(\alpha \) is classical.
- 2.
That is, the prover commits to all of the cells in the adjacency matrix that represents the graph \(\varphi (G)\).
- 3.
We take the Hamiltonicity protocol only as a concrete easy example and in fact any other sigma protocol can take the role of this protocol in our context of attacking the soundness.
- 4.
in that protocol it is also needed that the verifier itself makes the Clifford operation and measurement, which makes the protocol more challenging to use for a NIZK protocol.
- 5.
For a problem \(\mathcal {L}= (\mathcal {L}_{yes}, \mathcal {L}_{no})\) in QMA, for an instance \(x \in \mathcal {L}_{yes}\), the set \(\mathcal {R}_{\mathcal {L}}(x)\) is the (possibly infinite) set of quantum witnesses that make the BQP verification machine accept with some overwhelming probability \(1 - \mathrm {negl}(\lambda )\).
- 6.
We assume that our gap problem \(\mathcal {L}\in \text{ QMA }\) has exponential-time algorithms that solve it, that is, for \(x \in \mathcal {L}\) we can decide whether \(x \in \mathcal {L}_{yes}\) or \(x \in \mathcal {L}_{no}\) in \(2^{O(|x|)}\) time. It is also enough for our proof to assume that \(\mathcal {L}\) is solvable in general exponential time i.e. \(O(2^{|x|^c})\) time for some constant \(c \in \mathbb {N}\).
- 7.
the output bits of the hybrids are in fact statistically indistinguishable, because any two distributions over a bit are statistically indistinguishable if they are computationally indistinguishable, but we won’t care about this in our analysis.
- 8.
As noted before, the proof is not sensitive to the fact that the time complexity is \(2^{O(|x|)}\) and not \(O(2^{|x|^c})\) time for some constant \(c \in \mathbb {N}\).
- 9.
It would have been enough to show that the protocol is single-theorem adaptive computational zero-knowledge, and then by the single-to-multi-theorem compiler for NIZKs of [FLS99] get a MDV-NICZK argument with adaptive multi-theorem security, but for the sake of completeness, because our construction can be shown to be multi-theorem zero-knowledge without the FLS compilation and because it does not change the main ideas in the proof, we prove the multi-theorem case directly.
References
Alagic, G., Childs, A.M., Grilo, A.B., Hung, S.H.: Non-interactive classical verification of quantum computation. arXiv, pages arXiv-1911 2019)
Bartusek, J., Coladangelo, A., Khurana, D., Ma, F.: On the round complexity of two-party quantum computation. arXiv preprint arXiv:2011.11212 (2020)
Brakerski, Z., Döttling, N.: Two-message statistically sender-private OT from LWE. In: Beimel, A., Dziembowski, S. (eds.) TCC 2018. LNCS, vol. 11240, pp. 370–390. Springer, Cham (2018). https://doi.org/10.1007/978-3-030-03810-6_14
Blum, M., Feldman, P., Micali, S.: Non-interactive zero-knowledge and its applications. In: Providing Sound Foundations for Cryptography: On the Work of Shafi Goldwasser and Silvio Micali, pP. 329–349 (2019)
Broadbent, A., Grilo, A.B.: Zero-knowledge for qma from locally simulatable proofs. arXiv preprint arXiv:1911.07782 (2019)
Broadbent, A., Ji, Z., Song, F., Watrous, J.: Zero-knowledge proof systems for qma. In: 2016 IEEE 57th Annual Symposium on Foundations of Computer Science (FOCS), pp. 31–40. IEEE (2016)
Brakerski, Z., Koppula, V., Mour, T.: Nizk from lpn and trapdoor hash via correlation intractability for approximable relations. IACR Cryptol. ePrint Arch. 2020, 258 (2020)
Blum, M.: How to prove a theorem so no one else can claim it. In: Proceedings of the International Congress of Mathematicians, vol. 1, p. 2. Citeseer (1986)
Bitansky, N., Paneth, O.: ZAPs and non-interactive witness indistinguishability from indistinguishability obfuscation. In: Dodis, Y., Nielsen, J.B. (eds.) TCC 2015. LNCS, vol. 9015, pp. 401–427. Springer, Heidelberg (2015). https://doi.org/10.1007/978-3-662-46497-7_16
Canetti, R., et al.: Fiat-shamir: from practice to theory. In: Proceedings of the 51st Annual ACM SIGACT Symposium on Theory of Computing, pp. 1082–1090 (2019)
Canetti, R., Goldreich, O., Halevi, S.: The random oracle methodology, revisited. J. ACM (JACM) 51(4), 557–594 (2004)
Coladangelo, A., Vidick, A., Zhang, T.: Non-interactive zero-knowledge arguments for qma, with preprocessing. arXiv preprint arXiv:1911.07546 (2019)
Feige, U., Lapidot, D., Shamir, A.: Multiple noninteractive zero knowledge proofs under general assumptions. SIAM J. Comput. 29(1), 1–28 (1999)
Goldwasser, S., Micali, S., Rackoff, C.: The knowledge complexity of interactive proof systems. SIAM J. Comput. 18(1), 186–208 (1989)
Kim, S., Wu, D.J.: Multi-theorem preprocessing nizks from lattices. J. Cryptol., pp. 1–84 (2019)
Liu, Y.-K.: Consistency of local density matrices is QMA-complete. In: Díaz, J., Jansen, K., Rolim, J.D.P., Zwick, U. (eds.) APPROX/RANDOM -2006. LNCS, vol. 4110, pp. 438–449. Springer, Heidelberg (2006). https://doi.org/10.1007/11830924_40
Lombardi, A., Quach, W., Rothblum, R.D., Wichs, D., Wu, D.J.: New constructions of reusable designated-verifier NIZKs. In: Boldyreva, A., Micciancio, D. (eds.) CRYPTO 2019. LNCS, vol. 11694, pp. 670–700. Springer, Cham (2019). https://doi.org/10.1007/978-3-030-26954-8_22
Morimae, T.: Information-theoretically-sound non-interactive classical verification of quantum computing with trusted center. arXiv preprint arXiv:2003.10712 (2020)
Morimae, T., Yamakawa, T.: Classically verifiable (dual-mode) nizk for qma with preprocessing. arXiv preprint arXiv:2102.09149, 2021
Ostrovsky, R., Paskin-Cherniavsky, A., Paskin-Cherniavsky, B.: Maliciously circuit-private FHE. In: Garay, J.A., Gennaro, R. (eds.) CRYPTO 2014. LNCS, vol. 8616, pp. 536–553. Springer, Heidelberg (2014). https://doi.org/10.1007/978-3-662-44371-2_30
Peikert, C., Shiehian, S.: Noninteractive zero knowledge for NP from (plain) learning with errors. In: Boldyreva, A., Micciancio, D. (eds.) CRYPTO 2019. LNCS, vol. 11692, pp. 89–114. Springer, Cham (2019). https://doi.org/10.1007/978-3-030-26948-7_4
Pass, R., Vaikuntanathan, V., et al.: Construction of a non-malleable encryption scheme from any semantically secure one. In: Dwork, C. (ed.) CRYPTO 2006. LNCS, vol. 4117, pp. 271–289. Springer, Heidelberg (2006). https://doi.org/10.1007/11818175_16
Quach, W., Rothblum, R.D., Wichs, D.: Reusable designated-verifier NIZKs for all NP from CDH. In: Ishai, Y., Rijmen, V. (eds.) EUROCRYPT 2019. LNCS, vol. 11477, pp. 593–621. Springer, Cham (2019). https://doi.org/10.1007/978-3-030-17656-3_21
Regev, O.: On lattices, learning with errors, random linear codes, and cryptography. J. ACM 56(6), 34:1–34:40 (2009)
Acknowledgments
We thank Nir Bitansky and Zvika Brakerski for helpful discussions during the preparation of this work.
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2021 International Association for Cryptologic Research
About this paper
Cite this paper
Shmueli, O. (2021). Multi-theorem Designated-Verifier NIZK for QMA. In: Malkin, T., Peikert, C. (eds) Advances in Cryptology – CRYPTO 2021. CRYPTO 2021. Lecture Notes in Computer Science(), vol 12825. Springer, Cham. https://doi.org/10.1007/978-3-030-84242-0_14
Download citation
DOI: https://doi.org/10.1007/978-3-030-84242-0_14
Published:
Publisher Name: Springer, Cham
Print ISBN: 978-3-030-84241-3
Online ISBN: 978-3-030-84242-0
eBook Packages: Computer ScienceComputer Science (R0)





 are said to be computationally indistinguishable, denoted by
are said to be computationally indistinguishable, denoted by