Abstract
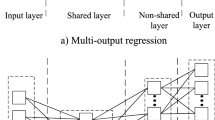
As the global IoT market increases, the importance of security in the IoT environment is growing. So, studies on lightweight cipher techniques are actively underway for limited environments. In ICISC 2020, PIPO, a bitslice lightweight cipher that can effectively apply a countermeasure considering side-channel analysis, was proposed. In this paper, we propose Deep Learning-based profiled and non-profiled Side-Channel Analysis for PIPO. In profiled attack, we use an 8-bit model instead of 1-bit model that considered the bitslice characteristic of S-Box output. Although an each bit of S-Box output is distributed across the power trace, the 8-bit model has shown high training performance with 98% accuracy, and was able to derive right key successfully. In non-profiled attack, we propose a labeling technique suitable for the bitslice characteristic and show the excellence of our proposed labeling through experiments. Also, we expect that these characteristics will apply to other bitslice block ciphers as well as PIPO.
This work was supported by Institute for Information & communications Technology Promotion (IITP) grant funded by the Korea government (MSIT) (No. 2017-0-00520, Development of SCR-Friendly Symmetric Key Cryptosystem and Its Application Modes).
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Similar content being viewed by others
References
Chari, S., Rao, J.R., Rohatgi, P.: Template attacks. In: Kaliski, B.S., Koç, K., Paar, C. (eds.) CHES 2002. LNCS, vol. 2523, pp. 13–28. Springer, Heidelberg (2003). https://doi.org/10.1007/3-540-36400-5_3
Kim, H., et al.: PIPO: a lightweight block cipher with efficient higher-order masking software implementations. In: Hong, D. (ed.) ICISC 2020. LNCS, vol. 12593, pp. 99–122. Springer, Cham (2021). https://doi.org/10.1007/978-3-030-68890-5_6
Kocher, P., Jaffe, J., Jun, B.: Differential power analysis. In: Wiener, M. (ed.) CRYPTO 1999. LNCS, vol. 1666, pp. 388–397. Springer, Heidelberg (1999). https://doi.org/10.1007/3-540-48405-1_25
Priddy, K., Keller, P.: Artificial Neural Networks: An Introduction. SPIE Tutorial Texts. SPIE Press (2005). https://books.google.co.kr/books?id=BrnHR7esWmkC
Reed, R.D., Marks, R.J.: Neural Smithing: Supervised Learning in Feedforward Artificial Neural Networks. MIT Press, Cambridge (1998)
Schaffer, C.: Selecting a classification method by cross-validation. Mach. Learn. 13, 135–143 (1993). https://doi.org/10.1007/BF00993106
Timon, B.: Non-profiled deep learning-based side-channel attacks with sensitivity analysis. IACR Trans. Cryptogr. Hardw. Embed. Syst. 2019(2), 107–131 (2019). https://doi.org/10.13154/tches.v2019.i2.107-131
TrusThingz: PIPO data set. https://trusthingz.org/index.php/pipo-data-set
Zeman, V., Martinasek, Z.: Innovative method of the power analysis. Radioengineering 22, 586–594 (2013)
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2022 The Author(s), under exclusive license to Springer Nature Switzerland AG
About this paper
Cite this paper
Woo, JE. et al. (2022). Learning-based Side-Channel Analysis on PIPO. In: Park, J.H., Seo, SH. (eds) Information Security and Cryptology – ICISC 2021. ICISC 2021. Lecture Notes in Computer Science, vol 13218. Springer, Cham. https://doi.org/10.1007/978-3-031-08896-4_16
Download citation
DOI: https://doi.org/10.1007/978-3-031-08896-4_16
Published:
Publisher Name: Springer, Cham
Print ISBN: 978-3-031-08895-7
Online ISBN: 978-3-031-08896-4
eBook Packages: Computer ScienceComputer Science (R0)