Abstract
Commit-and-prove is a building block that allows a party to commit to a secret input and then later prove something about it. This is a pillar of many cryptographic protocols and especially the ones underlying anonymous systems. In anonymous systems, often there is a set of public commitments, and a prover wants to prove a property about one of the inputs committed in the set, while hiding which one. This latter property gives the prover anonymity within the set.
Currently, there are numerous commit-and-prove protocols in the anonymous setting from various computational and setup assumptions. However, all such approaches are non-black-box in the cryptographic primitive. In fact, there exists no anonymous black-box construction of commit-and-prove protocols, under any computational or setup assumption. This is despite the fact that, when anonymity is not required, black-box commit-and-prove protocols are well known.
Is this inherent in the anonymous setting?
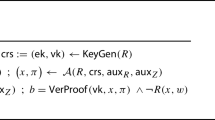
In this paper we provide a partial answer to the above question by constructing the first (one-time) black-box commit-and-prove protocol in the anonymous setting. We do so by first introducing a new primitive that we call Partially Openable Commitment (POC), and instantiating it in a black-box way from a Random Oracle. Next we show a black-box commit-and-prove protocol based on POC. From a theoretical standpoint, our result reduces the gap between known black-box feasibility results in the non-anonymous setting and the anonymous setting. From a practical standpoint, we show that our protocol can be very efficient for certain relations of interest.
Supported by NSF grants #1718074, #1764025.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Similar content being viewed by others
Notes
- 1.
We remark that partially openable commitment are different from trapdoor or UC-secure [7] commitments. In the latter, the commitments can be opened by anyone who has a trapdoor, and the equivocation property is used in the security proof, not the protocol. They are also different from Mercurial Commitments [8] where the prover has the ability to “tease” only commitments she created.
References
Ames, S., Hazay, C., Ishai, Y., Venkitasubramaniam, M.: Ligero: lightweight sublinear arguments without a trusted setup. In: Proceedings of the 2017 ACM SIGSAC, pp. 2087–2104 (2017)
Bellare, M., Rogaway, P.: Random oracles are practical: a paradigm for designing efficient protocols. In: Denning, D.E., Pyle, R., Ganesan, R., Sandhu, R.S., Ashby, V. (ed.) ACM CCS 93, pp. 62–73. ACM Press, November 1993
Ben-Sasson, E., Bentov, I., Horesh, Y., Riabzev, M.: Scalable, transparent, and post-quantum secure computational integrity. IACR Cryptology ePrint Archive 2018, 46 (2018)
Ben-Sasson, E.: Zerocash: decentralized anonymous payments from bitcoin. In: 2014 IEEE Symposium on Security and Privacy, pp. 459–474 (2014)
Bünz, B., Bootle, J., Boneh, D., Poelstra, A., Wuille, P., Maxwell, G.: Bulletproofs: short proofs for confidential transactions and more. In: 2018 IEEE Symposium on Security and Privacy, SP, pp. 315–334 (2018)
Camenisch, J., Lysyanskaya, A.: Dynamic accumulators and application to efficient revocation of anonymous credentials. In: Yung, M. (ed.) CRYPTO 2002. LNCS, vol. 2442, pp. 61–76. Springer, Heidelberg (2002). https://doi.org/10.1007/3-540-45708-9_5
Canetti, R., Fischlin, M.: Universally composable commitments. In: Kilian, J. (ed.) CRYPTO 2001. LNCS, vol. 2139, pp. 19–40. Springer, Heidelberg (2001). https://doi.org/10.1007/3-540-44647-8_2
Chase, M., Healy, A., Lysyanskaya, A., Malkin, T., Reyzin, L.: Mercurial commitments with applications to zero-knowledge sets. In: Cramer, R. (ed.) EUROCRYPT 2005. LNCS, vol. 3494, pp. 422–439. Springer, Heidelberg (2005). https://doi.org/10.1007/11426639_25
Giacomelli, I., Madsen, J., Orlandi, C.: ZKBoo: faster zero-knowledge for Boolean circuits. In: 25th USENIX Security Symposium, USENIX Security 16, Austin, TX, USA, 10–12 August 2016, pp. 1069–1083 (2016)
Goyal, V., Lee, C.-K., Ostrovsky, R., Visconti, I.: Constructing non-malleable commitments: a black-box approach. In: 53rd FOCS, pp. 51–60. IEEE Computer Society Press, October 2012
Ishai, Y., Kushilevitz, E., Ostrovsky, R., Sahai, A.: Zero-knowledge from secure multiparty computation. In: Johnson, D.S., Feige, U. (eds.) 39th ACM STOC, pp. 21–30. ACM Press, June 2007
Ishai, Y., Weiss, M.: Probabilistically checkable proofs of proximity with zero-knowledge. In: Lindell, Y. (ed.) TCC 2014. LNCS, vol. 8349, pp. 121–145. Springer, Heidelberg (2014). https://doi.org/10.1007/978-3-642-54242-8_6
Kilian, J.: A general completeness theorem for two-party games. In: 23rd ACM STOC, pp. 553–560. ACM Press, May 1991
Kiyoshima, S.: Round-optimal black-box commit-and-prove with succinct communication. In: Micciancio, D., Ristenpart, T. (eds.) CRYPTO 2020. LNCS, vol. 12171, pp. 533–561. Springer, Cham (2020). https://doi.org/10.1007/978-3-030-56880-1_19
Kosba, A.E., Miller, A., Shi, E., Wen, Z., Papamanthou, C.: Hawk: the blockchain model of cryptography and privacy-preserving smart contracts. In: IEEE Symposium on Security and Privacy, pp. 839–858 (2016)
Miers, I., Garman, C., Green, M., Rubin, A.D.: Zerocoin: anonymous distributed e-cash from bitcoin. In: 2013 IEEE Symposium on Security and Privacy, pp. 397–411 (2013)
Ostrovsky, R., Richelson, S., Scafuro, A.: Round-optimal black-box two-party computation. In: Gennaro, R., Robshaw, M. (eds.) CRYPTO 2015. LNCS, vol. 9216, pp. 339–358. Springer, Heidelberg (2015). https://doi.org/10.1007/978-3-662-48000-7_17
Pass, R., Wee, H.: Black-box constructions of two-party protocols from one-way functions. In: Reingold, O. (ed.) TCC 2009. LNCS, vol. 5444, pp. 403–418. Springer, Heidelberg (2009). https://doi.org/10.1007/978-3-642-00457-5_24
Pedersen, T.P.: Non-interactive and information-theoretic secure verifiable secret sharing. In: Feigenbaum, J. (ed.) CRYPTO 1991. LNCS, vol. 576, pp. 129–140. Springer, Heidelberg (1992). https://doi.org/10.1007/3-540-46766-1_9
Shamir, A.: How to share a secret. Commun. ACM 22(11), 612–613 (1979)
Z. Zcash project (2013). https://z.cash/
Zhang, B., Oliynykov, R., Balogun, H.: A treasury system for cryptocurrencies: enabling better collaborative intelligence. In: Network and Distributed System Security Symposium, NDSS (2019)
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2022 The Author(s), under exclusive license to Springer Nature Switzerland AG
About this paper
Cite this paper
Scafuro, A. (2022). Black-Box Anonymous Commit-and-Prove. In: Galdi, C., Jarecki, S. (eds) Security and Cryptography for Networks. SCN 2022. Lecture Notes in Computer Science, vol 13409. Springer, Cham. https://doi.org/10.1007/978-3-031-14791-3_26
Download citation
DOI: https://doi.org/10.1007/978-3-031-14791-3_26
Published:
Publisher Name: Springer, Cham
Print ISBN: 978-3-031-14790-6
Online ISBN: 978-3-031-14791-3
eBook Packages: Computer ScienceComputer Science (R0)