Abstract
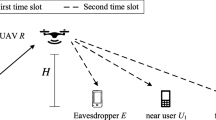
Unmanned aerial vehicles (UAVs) have become increasingly popular for wireless communication due to their mobility, versatility in deployment, and economic advantages, particularly in catastrophic weather event scenarios and vital military operations. The utilization of Non-Orthogonal Multiple Access(NOMA) has been efficiently done to enhance channel utilization. Multiple users transmit information using similar frequency bands. This technique is helpful in enhancing the performance of UAV communication. It helps in enhancing achievable rate and robustness. Non Orthogonal as compared to the orthogonal multiple access technique provides improved spectral efficiency, reduced latency, expanded coverage, enhanced connectivity, and improved fairness. However, non-orthogonal techniques are less secure. An interceptor can intercept a transmission and can access information of multiple users that are accessing the same resources. To circumvent such issues much emphasis has been given to the physical layer. The popular matrices that are used for such a system are the probability of a link going down and the likelihood of a communication interception. This study examines the practicality of pairing trustworthy and untrustworthy users, as well as the impact of optimal power allocation coefficients using tabulation and belief MDP methods. The findings of the simulation research suggest that belief MDP is a feasible approach for enabling user pairings that are attainable while adhering to the Secrecy Outage Probability (SecOP) constraint of trusted users, thereby optimizing resource allocation efficiency.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Similar content being viewed by others
References
Dai, L., Wang, B., Ding, Z., Wang, Z., Chen, S., Hanzo, L.: A survey of non-orthogonal multiple access for 5G. IEEE Commun. Surv. Tutor. 20(3), 2294–2323 (2018)
Sun, H., Duo, B., Wang, Z., Lin, X., Gao, C.: Aerial cooperative jamming for cellular-enabled UAV secure communication network: joint trajectory and power control design. Sensors 19(20) (2019). https://doi.org/10.3390/s19204440
Zhang, Y., Wang, H.-M., Yang, Q., Ding, Z.: Secrecy sum rate maximization in non-orthogonal multiple access. IEEE Commun. Lett. 20(5), 930–933 (2016). https://doi.org/10.1109/LCOMM.2016.2539162
Chen, J., Yang, L., Alouini, M.-S.: Physical layer security for cooperative NOMA systems. IEEE Trans. Veh. Technol. 67(5), 4645–4649 (2018). https://doi.org/10.1109/TVT.2017.2789223
ElHalawany, B.M., Wu, K.: Physical-layer security of NOMA systems under untrusted users, pp. 1–6. IEEE (2018). https://doi.org/10.1109/GLOCOM.2018.8647889
Nasir, A.A., Tuan, H.D., Duong, T.Q., Poor, H.V.: UAV-enabled communication using NOMA. IEEE Trans. Commun. 67, 5126–5138 (2019). https://doi.org/10.1109/TCOMM.2019.2906622
Sarfraz, M., et al.: Capacity optimization of next-generation UAV communication involving non-orthogonal multiple access. Drones 6, 234 (2022). https://doi.org/10.3390/drones6090234
Mahmood, A., Usman, M.Q., Shahzad, K., Saddique, N.: Evolution of optimal 3D placement of UAV with minimum transmit power. Int. J. Wirel. Commun. Mob. Comput. 7, 13 (2019). https://doi.org/10.11648/j.wcmc.20190701.12
Sohail, M.F., Leow, C.Y., Won, S.: A cat swarm optimization based transmission power minimization for an aerial NOMA communication system. Veh. Commun. 33, 100426 (2022). https://doi.org/10.1016/j.vehcom.2021.100426
Zeng, Y., Zhang, R.: Energy-efficient UAV communication with trajectory optimization. IEEE Trans. Wirel. Commun. 16, 3747–3760 (2017). https://doi.org/10.1109/TWC.2017.2688328
Rupasinghe, N., Yapici, Y., Guvenc, I., Dai, H., Bhuyan, A.: Enhancing physical layer security for NOMA transmission in mmwave drone networks, pp. 729–733. IEEE (2018). https://doi.org/10.1109/ACSSC.2018.8645326
Ding, Z., Fan, P., Poor, H.V.: Impact of user pairing on 5G nonorthogonal multiple-access downlink transmissions. IEEE Trans. Veh. Technol. 65, 6010–6023 (2016). https://doi.org/10.1109/TVT.2015.2480766
Patel, P.: Migration from 4G LTE to advanced PHY techniques for unmanned aerial vehicle (UAV) communication. Int. J. Eng. Res. Appl. 9, 49–54 (2019)
Quintero, S.A.P., Papi, F., Klein, D.J., Chisci, L., Hespanha, J.P.: Optimal UAV coordination for target tracking using dynamic programming. In: 49th IEEE Conference on Decision and Control (CDC), pp. 4541–4546 (2010). https://doi.org/10.1109/CDC.2010.5717933
Zhang, J., Tao, X., Wu, H., Zhang, N., Zhang, X.: Deep reinforcement learning for throughput improvement of uplink grant-free NOMA system. IEEE Internet Things J. 1 (2020). https://doi.org/10.1109/JIOT.2020.2972274
Thapar, S., Mishra, D., Saini, R.: Secrecy fairness aware NOMA for untrusted users. In: 2019 IEEE Global Communications Conference (GLOBECOM), pp. 1–6 (2019). https://doi.org/10.1109/GLOBECOM38437.2019.9014034
Author information
Authors and Affiliations
Corresponding authors
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2023 The Author(s), under exclusive license to Springer Nature Switzerland AG
About this paper
Cite this paper
Prajapati, M., Tripathi, P. (2023). Physical Layer Security Optimisation for NOMA Based UAV Communication for Optimal Resource Allocation. In: Chaubey, N., Thampi, S.M., Jhanjhi, N.Z., Parikh, S., Amin, K. (eds) Computing Science, Communication and Security. COMS2 2023. Communications in Computer and Information Science, vol 1861. Springer, Cham. https://doi.org/10.1007/978-3-031-40564-8_10
Download citation
DOI: https://doi.org/10.1007/978-3-031-40564-8_10
Published:
Publisher Name: Springer, Cham
Print ISBN: 978-3-031-40563-1
Online ISBN: 978-3-031-40564-8
eBook Packages: Computer ScienceComputer Science (R0)