Abstract
The Internet of Things is expanding and since IoT devices and IoT networks are used in many crucial areas in modern societies, ranging from security and military applications to healthcare monitoring and production efficiency, the need to secure these devices is of great importance. Intrusion detection systems (IDS) play a significant role in securing IoT networks as their goal is to detect intruders that have gained access to one or several IoT nodes. While most IDS have been designed to detect a specific or at most a few attacks, the DETONAR framework detects multiple attacks. However, it is run on a designated sniffer network which adds additional cost in terms of hardware and maintenance. In this paper, we propose DETONAR-Light, adapting DETONAR to run using data collected at a border router rather than on sniffer logs. Our experiments show that this is possible almost without any decrease of detection and attack classification rate for many attacks.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Similar content being viewed by others
Notes
- 1.
DETONAR-Light is available at https://github.com/STACK-ITEA-Project/DETONAR-Light.
References
Tetcos netsim iot/wsn library documentation. https://tetcos.com/help/v13.2/Technology-Libraries/IoT-WSN.html. Accessed 02 Dec 2022
Agiollo, A., Conti, M., Kaliyar, P., Lin, T., Pajola, L.: Detonar: detection of routing attacks in RPL-based IoT. IEEE Trans. Network Serv. Manage. 18, 1178–1190 (2021)
Airehrour, D., Gutierrez, J.A., Ray, S.K.: Sectrust-RPL: a secure trust-aware RPL routing protocol for internet of things. Futur. Gener. Comput. Syst. 93, 860–876 (2019)
Alabsi, B.A., Anbar, M., Anickam, S.: A comprehensive review on security attacks in dynamic wireless sensor networks based on RPL protocol. Int. J. Pure Appl. Math. 119(12), 12481–12495 (2018)
Arış, A., Oktuğ, S.F., Voigt, T.: Security of Internet of Things for a reliable internet of services. In: Ganchev, I., van der Mei, R.D., van den Berg, H. (eds.) Autonomous Control for a Reliable Internet of Services. LNCS, vol. 10768, pp. 337–370. Springer, Cham (2018). https://doi.org/10.1007/978-3-319-90415-3_13
Bang, A.O., Rao, U.P., Kaliyar, P., Conti, M.: Assessment of routing attacks and mitigation techniques with RPL control messages: a survey. ACM Comput. Surv. 55(2), 44:1-44:36 (2023)
Boo, E., Raza, S., Hoglund, J., Ko, J.: FDTLS: supporting DTLS-based combined storage and communication security for IoT devices. In: 2019 IEEE 16th International Conference on Mobile Ad Hoc and Sensor Systems (MASS), pp. 127–135 (2019)
Box, G.E., Jenkins, G.M., Reinsel, G.C., Ljung, G.M.: Time Series Analysis: Forecasting and Control. Wiley, Hoboken (2015)
Dunkels, A., Grönvall, B., Voigt, T.: Contiki - a lightweight and flexible operating system for tiny networked sensors. In: Proceedings of the IEEE Workshop on Embedded Networked Sensor Systems (IEEE Emnets), Tampa, Florida, USA (2004)
Essop, I., Ribeiro, J.C., Papaioannou, M., Zachos, G., Mantas, G., Rodriguez, J.: Generating datasets for anomaly-based intrusion detection systems in IoT and industrial IoT networks. Sensors 21(4), 1528 (2021)
Finne, N., et al.: Multi-trace: multi-level data trace generation with the COOJA simulator. In: DCOSS (2021)
Ioulianou, P.P., Vassilakis, V.G., Shahandashti, S.F.: A trust-based intrusion detection system for RPL networks: detecting a combination of rank and blackhole attacks. J. Cybersecur. Privacy 2(1), 124–153 (2022)
Iyer, V., Hermans, F., Voigt, T.: Detecting and avoiding multiple sources of interference in the 2.4 GHz spectrum. In: Abdelzaher, T., Pereira, N., Tovar, E. (eds.) EWSN 2015. LNCS, vol. 8965, pp. 35–51. Springer, Cham (2015). https://doi.org/10.1007/978-3-319-15582-1_3
Kanwar, J., et al.: Jamsense: interference and jamming classification for low-power wireless networks. In: 13th IFIP Wireless and Mobile Networking Conference (WMNC) (2021)
Keipour, H., Hazra, S., Finne, N., Voigt, T.: Generalizing supervised learning for intrusion detection in IoT mesh networks. In: Wang, G., Choo, K.K.R., Ko, R.K.L., Xu, Y., Crispo, B. (eds.) UbiSec 2021. LNCS, vol. 1557, pp. 214–228. Springer, Cham (2022)
Kwon, H., Ahn, J., Ko, J.: Lightcert: on designing a lighter certificate for resource-limited internet-of-things devices. Trans. Emerg. Telecommun. Technol. 30(10), e3740 (2019)
Nadeem, A., et al.: SOK: explainable machine learning for computer security applications. In: 2023 IEEE 8th European Symposium on Security and Privacy (EuroS &P), pp. 221–240. IEEE (2023)
Napiah, M.N., Idris, M.Y.I.B., Ramli, R., Ahmedy, I.: Compression header analyzer intrusion detection system (cha-ids) for 6lowpan communication protocol. IEEE Access 6, 16623–16638 (2018)
Oikonomou, G., Duquennoy, S., Elsts, A., Eriksson, J., Tanaka, Y., Tsiftes, N.: The Contiki-NG open source operating system for next generation IoT devices. SoftwareX 18, 101089 (2022)
Osterlind, F., Dunkels, A., Eriksson, J., Finne, N., Voigt, T.: Cross-level sensor network simulation with COOJA. In: IEEE Conference on Local Computer Networks (2006)
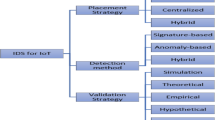
Pasikhani, A.M., Clark, J.A., Gope, P., Alshahrani, A.: Intrusion detection systems in RPL-based 6LoWPAN: a systematic literature review. IEEE Sens. J. 21(11), 12940–12968 (2021)
Pongle, P., Chavan, G.: Real time intrusion and wormhole attack detection in internet of things. Int. J. Comput. Appl. 121(9), 1–9 (2015)
Raoof, A., Matrawy, A., Lung, C.: Routing attacks and mitigation methods for RPL-based internet of things. IEEE Commun. Surv. Tutorials 21(2), 1582–1606 (2019)
Raza, S., Wallgren, L., Voigt, T.: Svelte: real-time intrusion detection in the internet of things. Ad Hoc Netw. 11(8), 2661–2674 (2013)
Sharma, M., Elmiligi, H., Gebali, F.: A novel intrusion detection system for RPL-based cyber-physical systems. IEEE Can. J. Electrical Comput. Eng. 44, 246–252 (2021)
Wang, L., Wyglinski, A.M.: A combined approach for distinguishing different types of jamming attacks against wireless networks. In: Proceedings of 2011 IEEE Pacific Rim Conference on Communications, Computers and Signal Processing, pp. 809–814. IEEE (2011)
Winter, T., et al.: RPL: Ipv6 routing protocol for low-power and lossy networks. Technical report (2012)
Wolsing, K., Thiemt, L., Sloun, C.V., Wagner, E., Wehrle, K., Henze, M.: Can industrial intrusion detection be simple? In: Atluri, V., Di Pietro, R., Jensen, C.D., Meng, W. (eds.) Computer Security-ESORICS 2022, Part III. LNCS, vol. 13556, pp. 574–594. Springer, Cham (2022)
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2024 The Author(s), under exclusive license to Springer Nature Switzerland AG
About this paper
Cite this paper
Bull, V. et al. (2024). DETONAR-Light: An IoT Network Intrusion Detection Using DETONAR without a Sniffer Network. In: Katsikas, S., et al. Computer Security. ESORICS 2023 International Workshops. ESORICS 2023. Lecture Notes in Computer Science, vol 14399. Springer, Cham. https://doi.org/10.1007/978-3-031-54129-2_12
Download citation
DOI: https://doi.org/10.1007/978-3-031-54129-2_12
Published:
Publisher Name: Springer, Cham
Print ISBN: 978-3-031-54128-5
Online ISBN: 978-3-031-54129-2
eBook Packages: Computer ScienceComputer Science (R0)