Abstract
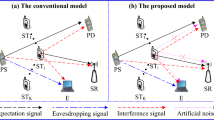
Physical Layer Security (PLS) is becoming a hot topic in wireless communications research. The application of artificial noise can reduce the eavesdropping ability of illegal eavesdroppers without affecting legitimate users. Most current PLS schemes only consider static scenarios without taking mobility into account. Some Cooperative Jamming (CJ) schemes analyse the security performance in mobile scenarios, but do not exploit the handoff and cooperation of friendly jammers. To address the above challenge, we propose a CJ scheme for soft-handoff-based cooperative jamming (CJSH) in mobility scenarios. We first consider a common scenario where a base station communicates with a mobile legitimate user alongside a mobile passive eavesdropper. Some friendly jammers with multiple antennas are chosen to emit artificial noise. Next, we design two corresponding thresholds for jammer entry and exit and measure the values based on the Secrecy Outage Probability (SOP). We then define the Power Average Security Gain (PASG) as the system performance to balance security and energy consumption. Finally, numerical simulation results are provided to verify the rationality of the proposed handoff scheme and demonstrate that it effectively improves the system security performance and jamming power consumption.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Similar content being viewed by others
References
Huo, Y., Tian, Y., Ma, L., Cheng, X., Jing, T.: Jamming strategies for physical layer security. IEEE Wirel. Commun. 25(1), 148–153 (2018)
Gao, Q., Huo, Y., Jing, T., Ma, L., Wen, Y., Xing, X.: An intermittent cooperative jamming strategy for securing energy-constrained networks. IEEE Trans. Commun. 67(11), 7715–7726 (2019)
Wen, Y., et al.: A covert jamming scheme against an intelligent eavesdropper in cooperative cognitive radio networks. IEEE Trans. Veh. Technol. 72(10), 13243–13254 (2023)
Huo, Y., Fan, X., Ma, L., Cheng, X., Tian, Z., Chen, D.: Secure communications in tiered 5G wireless networks with cooperative jamming. IEEE Trans. Wireless Commun. 18(6), 3265–3280 (2019)
Tang, J., et al.: Cross-layer optimization for industrial internet of things in NOMA-based C-RANS. IEEE Int. Things J. 9(18), 16962–16975 (2022)
Zhang, H., Zou, Y., Yu, D., Yu, J., Cheng, X.: Covert communications with friendly jamming in internet of vehicles. Veh. Commun. 35, 100472 (2022)
Cai, Z., Chen, Q.: Latency-and-coverage aware data aggregation scheduling for multihop battery-free wireless networks. IEEE Trans. Wireless Commun. 20(3), 1770–1784 (2021)
Zou, Y., Xu, M., Yu, D., Chen, L., Guo, S., Xing, X.: Implementation of abstract MAC layer under jamming. Tsinghua Sci. Technol. 27(2), 257–269 (2021)
Zhang, H., Zou, Y., Yin, H., Yu, D., Cheng, X.: CCM-FL: covert communication mechanisms for federated learning in crowd sensing IoT. Digit. Commun. Netw. (2023)
Tang, J., Dabaghchian, M., Zeng, K., Wen, H.: Impact of mobility on physical layer security over wireless fading channels. IEEE Trans. Wireless Commun. 17, 7849–7864 (2018)
Tang, J., Wen, H., Song, H., Zhang, T., Qin, K.: On the security-reliability and secrecy throughput of random mobile user in internet of things. IEEE Internet Things J. 7(10), 10635–10649 (2020)
Zhou, X., et al.: Digital twin enhanced federated reinforcement learning with lightweight knowledge distillation in mobile networks. IEEE J. Sel. Areas Commun. 41(10), 3191 - 3211 (2023)
Cao, N., Chen, Y., Yang, Z.: Secrecy outage probability with randomly moving interferers in nakagami-\( m \) fading. IEEE Commun. Lett. 23(1), 76–79 (2018)
Wu, H., Li, H., Wei, Z., Zhang, N., Tao, X.: Secrecy performance analysis of air-to-ground communication with UAV jitter and multiple random walking eavesdroppers. IEEE Trans. Veh. Technol. 70(1), 572–584 (2021)
Xiong, Z., Cai, Z., Hu, C., Takabi, D., Li, W.: Towards neural network-based communication system: attack and defense. IEEE Trans. Dependable Secure Comput. 20(4), 3238–3250 (2023)
Zhang, T., Wen, H., Tang, J., Song, H., Xie, F.: Cooperative jamming secure scheme for IWNs random mobile users aided by edge computing intelligent node selection. IEEE Trans. Industr. Inf. 17(7), 4999–5009 (2021)
Yu, K., Yu, J., Dong, A.: Cooperative communication and mobility for securing uRLLC of future wireless networks. IEEE Trans. Veh. Technol. 71(5), 5331–5342 (2022)
Zhou, X., et al.: Spatial-temporal federated transfer learning with multi-sensor data fusion for cooperative positioning. Inf. Fusion 105, 102182 (2024)
Shen, D., Huo, Y. and Gao, Q.: A friendly jamming handover scheme for a conscious mobile eavesdropper in IoT systems. Procedia Comput. Sci. 202, 15–20 (2022)
Narrainen, R.P., Takawira, F.: Performance analysis of soft handoff in CDMA cellular networks. IEEE Trans. Veh. Technol. 50(6), 1507–1517 (2001)
Hu, L., et al.: Cooperative jamming for physical layer security enhancement in internet of things. IEEE Internet Things J. 5(1), 219–228 (2018)
Acknowledgement.
This work was supported in part by the Fundamental Research Funds for the Central Universities under Grant 2023JBZX001 and the National Natural Science Foundation of China under Grant 62202035 and Grant 61931001.
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2025 The Author(s), under exclusive license to Springer Nature Switzerland AG
About this paper
Cite this paper
Huang, H., Huo, Y., Gao, Q., Jing, T., Yang, Z. (2025). An Effective Cooperative Jamming-Based Secure Transmission Scheme for a Mobile Scenario. In: Cai, Z., Takabi, D., Guo, S., Zou, Y. (eds) Wireless Artificial Intelligent Computing Systems and Applications. WASA 2024. Lecture Notes in Computer Science, vol 14997. Springer, Cham. https://doi.org/10.1007/978-3-031-71464-1_5
Download citation
DOI: https://doi.org/10.1007/978-3-031-71464-1_5
Published:
Publisher Name: Springer, Cham
Print ISBN: 978-3-031-71463-4
Online ISBN: 978-3-031-71464-1
eBook Packages: Computer ScienceComputer Science (R0)