Abstract
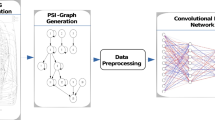
The proliferation of Internet of Things (IoT) devices has led to an increase in IoT malware, posing a significant cybersecurity threat. Detecting and mitigating this threat is challenging due to the diverse CPU architectures in IoT malware families and the limited resources of IoT devices. Specialized detection methods are needed to identify malware across different platforms, while lightweight mechanisms are required to minimize resource strain. This paper introduces a novel graph-based framework, Aggregated Weighted Graph of Hashes (AWGH), to tackle the CPU diversity challenge. The framework leverages Function Call Graphs (FCGs) and fuzzy hashing to capture the structural and code characteristics of IoT malware. By utilizing static analysis techniques, the framework can efficiently group new malware samples and identify similarities with existing families, even in the case of unknown malware to mitigate potential risks before they cause significant damage. FCGs are generated using IDA Pro [1], and fuzzy hashes are calculated using ssdeep [2]. The framework is implemented in Python and evaluated using a dataset from VirusTotal [3] through 10-fold cross-validation. The experimental results demonstrate the effectiveness of the proposed framework in accurately classifying the IoT malware into IoT malware families across various CPU architectures (MIPS, ARM, i386, PowerPC, and AMD64).
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Similar content being viewed by others
Notes
- 1.
Fuzzy hash.
References
SA, H.-R.: Ida pro. https://www.hex-rays.com. Accessed Nov 2020
ssdeep project. https://github.com/ssdeep-project/ssdeep. Accessed Nov 2020
Virustotal-free online virus, malware and URL scanner. https://www.virustotal.com. Accessed Nov 2020
Gopal, T. S., Meerolla, M., Jyostna, G., Eswari, P.R.L., Magesh, E.: Mitigating mirai malware spreading in IoT environment. In: 2018 International Conference on Advances in Computing, Communications and Informatics (ICACCI), pp. 2226–2230. IEEE (2018)
Kambourakis, G., Kolias, C., Stavrou, A.: The mirai botnet and the IoT zombie armies. In: MILCOM 2017-2017 IEEE Military Communications Conference (MILCOM), pp. 267–272. IEEE (2017)
Kumar, A., Lim, T.J.: Early detection of Mirai-like IoT bots in large-scale networks through sub-sampled packet traffic analysis. In: Arai, K., Bhatia, R. (eds.) FICC 2019. LNNS, vol. 70, pp. 847–867. Springer, Cham (2020). https://doi.org/10.1007/978-3-030-12385-7_58
Tanaka, H., Yamaguchi, S.: On modeling and simulation of the behavior of IoT malwares Mirai and Hajime. In: 2017 IEEE International Symposium on Consumer Electronics (ISCE), pp. 56–60. IEEE (2017)
Chang, K.-C., Tso, R., Tsai, M.-C.: IoT sandbox: to analysis IoT malware Zollard. In: Proceedings of the Second International Conference on Internet of things, Data and Cloud Computing, p. 4. ACM (2017)
Sivanathan, A., Sherratt, D., Gharakheili, H.H., Sivaraman, V., Vishwanath, A.: Low-cost flow-based security solutions for smart-home IoT devices. In: 2016 IEEE International Conference on Advanced Networks and Telecommunications Systems (ANTS), pp. 1–6. IEEE (2016)
Doshi, R., Apthorpe, N., Feamster, N.: Machine learning DDOS detection for consumer internet of things devices. In: 2018 IEEE Security and Privacy Workshops (SPW), pp. 29–35. IEEE (2018)
Ozawa, S., Ban, T., Hashimoto, N., Nakazato, J., Shimamura, J.: A study of IoT malware activities using association rule learning for darknet sensor data. Int. J. Inf. Secur. 19(1), 83–92 (2020)
Jamal, A., Hayat, M.F., Nasir, M.: Malware detection and classification in IoT network using ANN. Mehran Univ. Res. J. Eng. Technol. 41(1), 80–91 (2022)
Wang, B., Dou, Y., Sang, Y., Zhang, Y., Huang, J.: IoTCMAL: towards a hybrid IoT honeypot for capturing and analyzing malware. In: ICC 2020 - 2020 IEEE International Conference on Communications (ICC), pp. 1–7 (2020)
Luo, T., Xu, Z., Jin, X., Jia, Y., Ouyang, X.: IoTcandyJar: towards an intelligent-interaction honeypot for IoT devices. Black Hat (2017)
Feng, X., Li, Q., Wang, H., Sun, L.: Acquisitional rule-based engine for discovering internet-of-things devices. In: 27th \(\{\)USENIX\(\}\) Security Symposium (\(\{\)USENIX\(\}\) Security 18), pp. 327–341 (2018)
Oosterhof, M.: Cowrie SSH/Telnet honeypot (2016)
Kumar, S., Kumar, A.: Image-based malware detection based on convolution neural network with autoencoder in industrial internet of things using software defined networking honeypot. Eng. Appl. Artif. Intell. 133, 108374 (2024)
Alhanahnah, M., Lin, Q., Yan, Q., Zhang, N., Chen, Z.: Efficient signature generation for classifying cross-architecture IoT malware. In: 2018 IEEE Conference on Communications and Network Security (CNS), pp. 1–9. IEEE (2018)
Su, J., Vasconcellos, V.D., Prasad, S., Daniele, S., Feng, Y., Sakurai, K.: Lightweight classification of IoT malware based on image recognition. In: 2018 IEEE 42nd Annual Computer Software and Applications Conference (COMPSAC), vol. 2, pp. 664–669. IEEE (2018)
Naeem, H., Guo, B., Naeem, M.R.: A light-weight malware static visual analysis for IoT infrastructure. In: 2018 International Conference on Artificial Intelligence and Big Data (ICAIBD), pp. 240–244. IEEE (2018)
Isawa, R., Ban, T., Tie, Y., Yoshioka, K., Inoue, D.: Evaluating disassembly-code based similarity between IoT malware samples. In: 2018 13th Asia Joint Conference on Information Security (AsiaJCIS), pp. 89–94. IEEE (2018)
Pa, Y.M.P., Suzuki, S., Yoshioka, K., Matsumoto, T., Kasama, T., Rossow, C.: IoTpot: analysing the rise of IoT compromises. In: 9th \(\{\)USENIX\(\}\) Workshop on Offensive Technologies (\(\{\)WOOT\(\}\) 15) (2015)
Azmoodeh, A., Dehghantanha, A., Choo, K.-K.R.: Robust malware detection for internet of (battlefield) things devices using deep eigenspace learning. IEEE Trans. Sustain. Comput. (2018)
Pitolli, G., Laurenza, G., Aniello, L., Querzoni, L., Baldoni, R.: Malfamaware: automatic family identification and malware classification through online clustering. Int. J. Inf. Secur. 1–16 (2020)
Dib, M., Torabi, S., Bou-Harb, E., Assi, C.: A multi-dimensional deep learning framework for IoT malware classification and family attribution. IEEE Trans. Netw. Serv. Manag. 18(2), 1165–1177 (2021)
Chaganti, R., Ravi, V., Pham, T.D.: Deep learning based cross architecture internet of things malware detection and classification. Comput. Secur. 120, 102779 (2022)
Rahat, M.A., Banerjee, V., Bloom, G., Zhuang, Y.: Cimalir: cross-platform IoT malware clustering using intermediate representation. In: 2024 IEEE 14th Annual Computing and Communication Workshop and Conference (CCWC), pp. 0460–0466 (2024)
Sikder, A.K., Petracca, G., Aksu, H., Jaeger, T., Uluagac, A.S.: A survey on sensor-based threats to internet-of-things (IoT) devices and applications. arXiv preprint arXiv:1802.02041 (2018)
Hasan, R., Saxena, N., Haleviz, T., Zawoad, S., Rinehart, D.: Sensing-enabled channels for hard-to-detect command and control of mobile devices. In: Proceedings of the 8th ACM SIGSAC Symposium on Information, Computer and Communications Security, pp. 469–480. ACM (2013)
Azmoodeh, A., Dehghantanha, A., Conti, M., Choo, K.-K.R.: Detecting crypto-ransomware in IoT networks based on energy consumption footprint. J. Ambient Intell. Human. Comput. 1–12 (2017)
Caviglione, L., Gaggero, M., Lalande, J.-F., Mazurczyk, W., Urbański, M.: Seeing the unseen: revealing mobile malware hidden communications via energy consumption and artificial intelligence. IEEE Trans. Inf. Forensics Secur. 11(4), 799–810 (2015)
HaddadPajouh, H., Dehghantanha, A., Khayami, R., Choo, K.-K.R.: A deep recurrent neural network based approach for internet of things malware threat hunting. Futur. Gener. Comput. Syst. 85, 88–96 (2018)
Alasmary, H., Anwar, A., Park, J., Choi, J., Nyang, D., Mohaisen, A.: Graph-based comparison of IoT and android malware. In: Chen, X., Sen, A., Li, W.W., Thai, M.T. (eds.) CSoNet 2018. LNCS, vol. 11280, pp. 259–272. Springer, Cham (2018). https://doi.org/10.1007/978-3-030-04648-4_22
Pa, Y.M.P., Suzuki, S., Yoshioka, K., Matsumoto, T., Kasama, T., Rossow, C.: IoTpot: analysing the rise of IoT compromises. In: 9th USENIX Workshop on Offensive Technologies (WOOT 15), (Washington, D.C.), USENIX Association (2015)
Alasmary, H., et al.: Analyzing and detecting emerging internet of things malware: a graph-based approach. IEEE Internet Things J. 6(5), 8977–8988 (2019)
Public cyberiocs repository. https://freeiocs.cyberiocs.pro/. Accessed Nov 2020
Alasmary, H., et al.: Poster: analyzing, comparing, and detecting emerging malware: a graph-based approach (2019)
Nguyen, H.-T., Ngo, Q.-D., Le, V.-H.: A novel graph-based approach for IoT botnet detection. Int. J. Inf. Secur. 1–11 (2019)
Nguyen, H.-T., Ngo, Q.-D., Nguyen, D.-H., Le, V.-H.: Psi-rooted subgraph: A novel feature for IoT botnet detection using classifier algorithms. ICT Express (2020)
Pahl, M.-O., Aubet, F.-X., Liebald, S.: Graph-based IoT microservice security. NOMS 2018-2018 IEEE/IFIP Network Operations and Management Symposium, pp. 1–3. IEEE (2018)
Abusnaina, A, et al.: Breaking graph-based IoT malware detection systems using adversarial examples: poster. In: Proceedings of the 12th Conference on Security and Privacy in Wireless and Mobile Networks, pp. 290–291 (2019)
Nguyen, H.-T., Ngo, Q.-D., Le, V.-H.: IoT botnet detection approach based on psi graph and DGCNN classifier. In: 2018 IEEE International Conference on Information Communication and Signal Processing (ICICSP), pp. 118–122. IEEE (2018)
Darabian, H., Dehghantanha, A., Hashemi, S., Homayoun, S., Choo, K.-K.R.: An opcode-based technique for polymorphic internet of things malware detection. Concurr. Comput. Pract. Exp. 32(6), e5173 (2020)
Nguyen, H.-T., Nguyen, D.-H., Ngo, Q.-D., Tran, V.-H., Le, V.-H.: Towards a rooted subgraph classifier for IoT botnet detection. In: Proceedings of the 2019 7th International Conference on Computer and Communications Management, pp. 247–251 (2019)
Wu, C.-Y., Ban, T., Cheng, S.-M., Takahashi, T., Inoue, D.: IoT malware classification based on reinterpreted function-call graphs. Comput. Secur. 125, 103060 (2023)
Li, Y., Sundaramurthy, S.C., Bardas, A.G., Ou, X., Caragea, D., Hu, X., Jang, J.: Experimental study of fuzzy hashing in malware clustering analysis. In: 8th Workshop on Cyber Security Experimentation and Test (\(\{\)CSET\(\}\) 15) (2015)
Mirzaei, O., Suarez-Tangil, G., de Fuentes, J.M., Tapiador, J., Stringhini, G.: Andrensemble: Leveraging API ensembles to characterize android malware families. In: Proceedings of the 2019 ACM Asia Conference on Computer and Communications Security, pp. 307–314 (2019)
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2025 IFIP International Federation for Information Processing
About this paper
Cite this paper
Mahmoudyar, N., Ghorbani, A.A., Lashkari, A.H. (2025). Graph-Based Classification of IoT Malware Families Enhanced by Fuzzy Hashing. In: Rey, G., Tigli, JY., Franquet, E. (eds) Internet of Things. IFIPIoT 2024. IFIP Advances in Information and Communication Technology, vol 737. Springer, Cham. https://doi.org/10.1007/978-3-031-81900-1_8
Download citation
DOI: https://doi.org/10.1007/978-3-031-81900-1_8
Published:
Publisher Name: Springer, Cham
Print ISBN: 978-3-031-81899-8
Online ISBN: 978-3-031-81900-1
eBook Packages: Computer ScienceComputer Science (R0)