Abstract
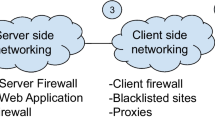
Cross-Site Scripting (XSS) attacks are at number three in the OWASP Top 10 2013 list [1] and according to a recent report by WhiteHat, 53% of the web applications are vulnerable to XSS attacks [2]. In this paper, we propose SIACHEN, a fine-grained, white-list and browser-enforced security policy language for the mitigation of XSS attacks. SIACHEN’s syntax is similar to Cascading Style Sheets (CSS) and its semantics is based on Content Security Policy (CSP) directives. CSP is a coarse-grained policy language and gives web site administrators a page-level control. Our policy language operates on per-id or per-class of web page’s HTML elements. SIACHEN also supports input validation and output encoding, which is missing in case of CSP. At the same time, SIACHEN leverages ECMAScript’s object freezing feature from the earlier work done by Heiderich et al. in [3]. SIACHEN glues together a number of disparate technologies into a single framework.
We implemented our proposal in the form of a client-side JavaScript library. Web site administrators can deliver the SIACHEN policy to the browser via a new header named “X-Siachen-Policy”. To show the applicability of our solution, we have added support of SIACHEN policy language in three open source web applications (i.e., PHPBB, PHPList & Damn Vulnerable Web App). Our evaluation shows reasonably low overhead is incurred by web applications and requires less amount of effort from developers’ side. We have tested our prototype against a large number of state-of-the-art, obfuscated and unobfuscated XSS attack vectors and found no bypass. To assist web site administrators, we present SIACHEN AiDer, an online service for the automated recommendation of policies. Further, this paper also presents results of a short survey of fifty popular desktop web applications and their mobile versions (100 in total). We have found an XSS in all surveyed sites but the main purpose of the survey is to find suitable venues for our prototype.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Preview
Unable to display preview. Download preview PDF.
Similar content being viewed by others
References
OWASP Top 10 2013, https://www.owasp.org/index.php/Top_10_2013-Top_10
WhiteHat Security’s Website Security Statistics Report (May 2013), https://www.whitehatsec.com/assets/WPstatsReport_052013.pdf
Heiderich, M., Frosch, T., Holz, T.: IceShield: Detection and Mitigation of Malicious Websites with a Frozen DOM. In: Sommer, R., Balzarotti, D., Maier, G. (eds.) RAID 2011. LNCS, vol. 6961, pp. 281–300. Springer, Heidelberg (2011)
Cross-site Scripting Overview, http://ha.ckers.org/cross-site-scripting.html
Cross-site scripting attacks up 160%, http://www.net-security.org/secworld.php?id=14320
Kirda, E., Kruegel, C., Vigna, G., Jovanovic, N.: Noxes: A client-side solution for mitigating cross-site scripting attacks. In: ACM SAC 2006 (2006)
Same Origin Policy, http://www.w3.org/Security/wiki/Same_Origin_Policy
Jayaraman, K., Du, W., Rajagopalan, B., Chapin, S.J.: ESCUDO: A Fine-grained Protection Model for Web Browsers. In: ICDCS 2010 (2010)
Inline JavaScript on Alexa top 25K sites, https://twitter.com/freddyb/status/304878658345107456
Oda, T.: Simple Security Policy for the Web, PhD Thesis (October 24, 2011), http://terri.zone12.com/doc/academic/TerriOda-PhDThesis-WebSecurity.pdf
Oda, T., Somayaji, A.: Enhancing Web Page Security with Security Style Sheets: SCS Technical Report TR-11-04, http://terri.zone12.com/doc/academic/TR-11-04-Oda.pdf
Stamm, S., Sterne, B., Markham, G.: Reining in the Web with Content Security Policy. In: WWW 2010 (2010)
Content Security Policy 1.0, http://www.w3.org/TR/CSP/
Content Security Policy Level 2.0, http://www.w3.org/TR/CSP11/
Louw, M.T., Venkatakrishnan, V.N.: BLUEPRINT: Robust Prevention of Cross-site Scripting Attacks for Existing Browsers. In: IEEE S&P 2009 (2009)
Jim, T., Swamy, N., Hicks, M.: BEEP: Browser-Enforced Embedded Policies. In: WWW 2007 (2007)
ModSecurity Core Rules, http://www.modsecurity.org/documentation/modsecurity-apache/2.1.3/html-multipage/ar01s02.html
Oda, T., Wurster, G., Van Oorschot, P., Somayaji, A.: SOMA: Mutual Approval for Included Content in Web Pages. In: CCS 2008 (2008)
Nadji, Y., Saxena, P., Song, D.: Document Structure Integrity: A Robust Basis for Cross-site Scripting Defense. In: NDSS 2009 (2009)
Javed, A., Schwenk, J.: Towards Elimination of Cross-Site Scripting on Mobile Versions of Web Applications. In: Kim, Y., Lee, H., Perrig, A. (eds.) WISA 2013. LNCS, vol. 8267, pp. 95–114. Springer, Heidelberg (2014)
Van Gundy, M., Chen, H.: Noncespaces: Using randomization to defeat cross-site scripting attacks. In: NDSS 2009 (2009)
Kc, G.S., Keromytis, A.D., Prevelakis, V.: Countering code-injection attacks with instruction-set randomization. In: CCS 2003 (2003)
ECMAScript Programming Language, http://www.ecmascript.org/
Kirda, E., Kruegel, C., Vigna, G., Jovanovic, N.: Noxes: A client-side solution for mitigating cross-site scripting attacks. In: ACM SAC 2006 (2006)
Heiderich, M., Niemietz, M., Schuster, F., Holz, T., Schwenk, J.: Scriptless Attacks—Stealing the Pie Without Touching the Sill. In: ACM CCS 2012 (2012)
Blink now has CSP 1.1 script nonce support, https://src.chromium.org/viewvc/blink?view=revision&revision=150541
PHPBB – Free and Open Source Forum Software, https://www.phpbb.com/
PHPLIST – The world’s most popular open source email campaign manager, http://www.phplist.com/
Damn Vulnerable Web App (DVWA), http://www.dvwa.co.uk/
Yahoo! UI Library, http://yuiblog.com/sandbox/yui/3.3.0pr3/api/Escape.html
There’s more to HTML escaping than &, < , > , and ”, http://wonko.com/post/html-escaping
Apple Developer Website Hacked - What Happened? http://mytechblog.com/2013/07/apple-developer-website-hacked-what-happened/
Ubuntu Forums are back up and a post mortem, http://blog.canonical.com/2013/07/30/ubuntu-forums-are-back-up-and-a-post-mortem/
Scripts, http://www.w3.org/TR/REC-html40/interact/scripts.html
Tip of the tree Blink now has CSP 1.1 script nonce support! And what the hell does that mean? http://joelweinberger.us/blog/archives/35
Weinberger, J., Barth, A., Song, D.: Towards Client-side HTML Security Policies. In: HotSec 2011 (2011)
CSP 1.1: Nonce-source (experimental), https://bugzilla.mozilla.org/show_bug.cgi?id=855326
XSS Filter Code, https://github.com/SpiderLabs/owasp-modsecurity-crs/blob/master/base_rules/modsecurity_crs_41_xss_attacks.conf#L11
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2014 Springer International Publishing Switzerland
About this paper
Cite this paper
Javed, A., Riemer, J., Schwenk, J. (2014). SIACHEN: A Fine-Grained Policy Language for the Mitigation of Cross-Site Scripting Attacks. In: Chow, S.S.M., Camenisch, J., Hui, L.C.K., Yiu, S.M. (eds) Information Security. ISC 2014. Lecture Notes in Computer Science, vol 8783. Springer, Cham. https://doi.org/10.1007/978-3-319-13257-0_33
Download citation
DOI: https://doi.org/10.1007/978-3-319-13257-0_33
Publisher Name: Springer, Cham
Print ISBN: 978-3-319-13256-3
Online ISBN: 978-3-319-13257-0
eBook Packages: Computer ScienceComputer Science (R0)