Abstract
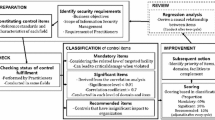
Initially, the field only dealt with sensitive security information. However, as operations on cyber space increases, the need for security in internet also increased. Thus, areas that requires security assessment also increased. But, to date, a security evaluation for each area is performed partially. Since security assessment does not reflect the characteristics of each area, the correct security level is difficult to determine. Therefore, new security indicator is required for the effective and efficient management. In this paper, we provide an advanced security assessment using edited indicators and common indicators.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Similar content being viewed by others
Notes
- 1.
C.B.I: Classification by Business Impact.
- 2.
N/A: Not Applicable.
References
International Organization for Standardization, ISO 27001 (2013)
National Institute of Standards and Technology, NIST Special Publication 800-53 (2009)
National Institute of Standards and Technology, NIST Special Publication 800-55 (2007)
Weiss, J.: Industrial control system (ICS) cyber security for water and wastewater systems. In: Clark, R.M., Hakim, S. (eds.) Securing Water and Wastewater Systems. Protecting Critical Infrastructure, vol. 2, pp. 87–105. Springer, New York (2014)
Chang, S.E., Ho, C.B.: Organizational factors to the effectiveness of implementing information security management. Ind. Manage. Data Syst. 106(3), 345–361 (2006)
Kankanhalli, A., et al.: An integrative study of information systems security effectiveness. Int. J. Inf. Manage. 23(2), 139–154 (2003)
Acknowledgement
This research was supported by the MSIP(Ministry of Science, ICT and Future Planning), Korea, under the ITRC(Information Technology Research Center) support program (NIPA-2014-H0301-14-1004) supervised by the NIPA(National IT Industry Promotion Agency).
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2015 Springer International Publishing Switzerland
About this paper
Cite this paper
You, Y., Oh, S., Lee, K. (2015). Advanced Security Assessment for Control Effectiveness. In: Rhee, KH., Yi, J. (eds) Information Security Applications. WISA 2014. Lecture Notes in Computer Science(), vol 8909. Springer, Cham. https://doi.org/10.1007/978-3-319-15087-1_30
Download citation
DOI: https://doi.org/10.1007/978-3-319-15087-1_30
Published:
Publisher Name: Springer, Cham
Print ISBN: 978-3-319-15086-4
Online ISBN: 978-3-319-15087-1
eBook Packages: Computer ScienceComputer Science (R0)