Abstract
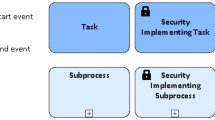
Security is a critical aspect of business processes that organisations utilise to achieve their goals. Current works on secure business process design mainly focus on annotating existing process models with security related concepts. Meanwhile, little attention is given to the rationale and the alignment of such security choices to high-level organisational security goals. To that end, a goal-to-process transformation approach, with a clear security orientation, is introduced, as part of a wider framework. This transformation process, presented through an illustrative example, uses Secure Tropos goal models as an input to create intermediate, security-annotated process skeletons. These can be then refined, through a series of manual tasks, to create secure BPMN process models.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Similar content being viewed by others
References
Mellado, D., Fernández-Medina, E., Piattini, M.: A common criteria based security requirements engineering process for the development of secure information systems. Comput. Stan. Interfaces 29(2), 244–253 (2007)
Altuhhova, O., Matulevičius, R., Ahmed, N.: Towards definition of secure business processes. In: Bajec, M., Eder, J. (eds.) CAiSE Workshops 2012. LNBIP, vol. 112, pp. 1–15. Springer, Heidelberg (2012)
Leitner, M., Miller, M., Rinderle-Ma, S.: An Analysis and evaluation of security aspects in the business process model and notation. In: 2013 IEEE International Conference on Availability, Reliability and Security. IEEE Press, pp. 262–267 (2013)
Neubauer, T., Klemen, M., Biffl, S.: Secure business process management: a roadmap. In: 1st IEEE International Conference on Availability, Reliability and Security, Vienna, Austria. IEEE Press, pp. 457–464 (2006)
Pavlovski, C.J., Zou, J.: Non-functional requirements in business process modeling. In: 5th Asia-Pacific Conference on Conceptual Modelling, vol. 79, Wollongong, Australia, pp. 103–112 (2008)
Decreus, K., Poels, G.: A goal-oriented requirements engineering method for business processes. In: Soffer, P., Proper, E. (eds.) CAiSE Forum 2010. LNBIP, vol. 72, pp. 29–43. Springer, Heidelberg (2011)
Ko, R.K., Lee, S.S., Lee, E.W.: Business process management (BPM) standards: a survey. Bus. Process Manage. 15(5), 744–791 (2009)
Lapouchnian, A., Yu, Y., Mylopoulos, J.: Requirements-driven design and configuration management of business processes. In: Alonso, G., Dadam, P., Rosemann, M. (eds.) BPM 2007. LNCS, vol. 4714, pp. 246–261. Springer, Heidelberg (2007)
Horkoff, J., Li, T., Li, F.L., Salnitri, M., Cardoso, E., Giorgini, P., Mylopoulos, J., Pimentel, J.A.: Taking goal models downstream: a systematic roadmap. In: 8th International Conference on Research Challenges in Information Science. IEEE Press, pp. 1–12 (2014)
Koliadis, G., Ghose, A.K.: Relating business process models to goal-oriented requirements models in KAOS. In: Hoffmann, A., Kang, B.-H., Richards, D., Tsumoto, S. (eds.) PKAW 2006. LNCS (LNAI), vol. 4303, pp. 25–39. Springer, Heidelberg (2006)
Ghose, A.K., Narendra, N.C., Ponnalagu, K., Panda, A., Gohad, A.: Goal-driven business process derivation. In: Kappel, G., Maamar, Z., Motahari-Nezhad, H.R. (eds.) Service Oriented Computing. LNCS, vol. 7084, pp. 467–476. Springer, Heidelberg (2011)
Pistore, M., Roveri, M., Busetta, P.: Requirements-driven verification of Web services. Electr. Notes Theo. Comput. Sci. 105, 95–108 (2004)
Guizzardi, R.S., Guizzardi, G., Almeida, J.A.P.A., Cardoso, E.: Bridging the gap between goals, agents and business processes. In: 4th International i* Workshop, CEUR, pp. 46–51 (2010)
Bleistein, S.J., Cox, K., Verner, J., Phalp, K.T.: Requirements engineering for e-business advantage. Require. Eng. 11, 4–16 (2006)
Lo, A., Yu, E.: From business models to service-oriented design: a reference catalog approach. In: Parent, C., Schewe, K.-D., Storey, V.C., Thalheim, B. (eds.) ER 2007. LNCS, vol. 4801, pp. 87–101. Springer, Heidelberg (2007)
Ruiz, M., Costal, D., España, S., Franch, X., Pastor, Ó.: Integrating the goal and business process perspectives in information system analysis. In: Jarke, M., Mylopoulos, J., Quix, C., Rolland, C., Manolopoulos, Y., Mouratidis, H., Horkoff, J. (eds.) CAiSE 2014. LNCS, vol. 8484, pp. 332–346. Springer, Heidelberg (2014)
Séguran, M., Hébert, C., Frankova, G.: Secure workflow development from early requirements analysis. In: The 6th European Conference on Web Services. IEEE, pp. 125–134 (2008)
Paja, E., Giorgini, P., Paul, S., Meland, P.H.: Security requirements engineering for secure business processes. In: Niedrite, L., Strazdina, R., Wangler, B. (eds.) BIR Workshops 2011. LNBIP, vol. 106, pp. 77–89. Springer, Heidelberg (2012)
Salnitri, M., Giorgini, P.: Transforming socio-technical security requirements in SecBPMN security policies. In: 7th International i* Workshop, Thessaloniki, Greece, CEUR (2014)
Decreus, K., Snoeck, M., Poels, G.: Practical challenges for methods transforming i* goal models into business process models. In: IEEE International Conference on Requirements Engineering. IEEE Press, pp. 15–23 (2009)
Leitner, M., Schefer-Wenzl, S., Rinderle-Ma, S., Strembeck, M.: An experimental study on the design and modeling of security concepts in business processes. In: Grabis, J., Kirikova, M., Zdravkovic, J., Stirna, J. (eds.) PoEM 2013. LNBIP, vol. 165, pp. 236–250. Springer, Heidelberg (2013)
Ahmed, N., Matulevicius, R.: A taxonomy for assessing security in business process modelling. In: 7th IEEE International Conference on Research Challenges in Information Science. IEEE Press, pp. 1–10 (2013)
OMG: Business Process Model and Notation (BPMN) Version 2.0. Technical report, January 2011
Rodríguez, A., Fernández-Medina, E., Piattini, M.: A BPMN extension for the modeling of security requirements in business processes. IEICE Trans. Inf. Syst. E90–D(4), 745–752 (2007)
Salnitri, M., Dalpiaz, F., Giorgini, P.: Modeling and verifying security policies in business processes. In: Bider, I., Gaaloul, K., Krogstie, J., Nurcan, S., Proper, H.A., Schmidt, R., Soffer, P. (eds.) BPMDS 2014 and EMMSAD 2014. LNBIP, vol. 175, pp. 200–214. Springer, Heidelberg (2014)
Brucker, A.D., Hang, I., Lückemeyer, G., Ruparel, R.: SecureBPMN: modeling and enforcing access control requirements in business processes. In: The 17th ACM symposium on Access Control Models and Technologies. ACM, pp. 123–126 (2012)
Wolter, C., Schaad, A.: Modeling of task-based authorization constraints in BPMN. In: Alonso, G., Dadam, P., Rosemann, M. (eds.) BPM 2007. LNCS, vol. 4714, pp. 64–79. Springer, Heidelberg (2007)
Braun, R., Esswein, W.: Classification of domain-specific BPMN extensions. In: Frank, U., Loucopoulos, P., Pastor, Ó., Petrounias, I. (eds.) PoEM 2014. LNBIP, vol. 197, pp. 42–57. Springer, Heidelberg (2014)
van der Aalst, W.M.: Business process management : a comprehensive survey. ISRN Softw. Eng. 2013, 1–37 (2013)
Indulska, M., Recker, J., Rosemann, M., Green, P.: Business process modeling: current issues and future challenges. In: van Eck, P., Gordijn, J., Wieringa, R. (eds.) CAiSE 2009. LNCS, vol. 5565, pp. 501–514. Springer, Heidelberg (2009)
Leitner, M., Rinderle-Ma, S.: A systematic review on security in process-aware information systems - constitution, challenges, and future directions. Inf. Softw. Technol. 56(3), 273–293 (2014)
Mouratidis, H., Giorgini, P.: Secure tropos: a security-oriented extension of the tropos methodology. Int. J. Softw. Eng. Knowl. Eng. 17(2), 285–309 (2007)
Pavlidis, M., Islam, S., Mouratidis, H.: A CASE tool to support automated modelling and analysis of security requirements. In: Nurcan, S. (ed.) IS Olympics: Information Systems in a Diverse World, pp. 95–109. Springer, Heidelberg (2012)
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2015 Springer International Publishing Switzerland
About this paper
Cite this paper
Argyropoulos, N., Mouratidis, H., Fish, A. (2015). Towards the Derivation of Secure Business Process Designs. In: Jeusfeld, M., Karlapalem, K. (eds) Advances in Conceptual Modeling. ER 2015. Lecture Notes in Computer Science(), vol 9382. Springer, Cham. https://doi.org/10.1007/978-3-319-25747-1_25
Download citation
DOI: https://doi.org/10.1007/978-3-319-25747-1_25
Published:
Publisher Name: Springer, Cham
Print ISBN: 978-3-319-25746-4
Online ISBN: 978-3-319-25747-1
eBook Packages: Computer ScienceComputer Science (R0)