Abstract
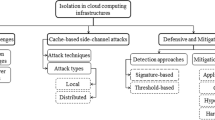
Isolation across virtual machines is one of the pillars on which the cloud computing paradigm relies on, allowing efficient use of shared resources among users who experience dedicated services. However side channel attacks have been recently demonstrated possible, showing how an adversary is enabled to recover sensible information by observing the behavior of a VM co-located on the same physical machine. In this paper we survey the current attacks, focusing on the ones targeted to extract private RSA keys, and discuss some possible countermeasures, offering a picture of the security challenges cloud providers need to address in order to provide strong guarantees to their customers.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Similar content being viewed by others
References
AlBelooshi, B., Salah, K., Martin, T., Damiani, E.: Securing cryptographic keys in the IAAS cloud model. In: Raicu, I., Rana, O.F., Buyya, R. (eds.) 8th IEEE/ACM International Conference on Utility and Cloud Computing, UCC 2015, Limassol, Cyprus, 7–10 December 2015, pp. 397–401. IEEE (2015)
Benger, N., van de Pol, J., Smart, N.P., Yarom, Y.: “Ooh Aah\(\ldots \) Just a Little Bit”: a small amount of side channel can go a long way. In: Batina, L., Robshaw, M. (eds.) CHES 2014. LNCS, vol. 8731, pp. 75–92. Springer, Heidelberg (2014)
Bernstein, D.J.: Cache-timing attacks on AES (2005)
Boneh, D., Durfee, G., Frankel, Y.: An attack on RSA given a small fraction of the private key bits. In: Ohta, K., Pei, D. (eds.) ASIACRYPT 1998. LNCS, vol. 1514, pp. 25–34. Springer, Heidelberg (1998)
Giraud, C.: An RSA implementation resistant to fault attacks and to simple power analysis. IEEE Trans. Comput. 55, 1116–1120 (2006)
Cimato, S., Mella, S., Susella, R.: New results for partial key exposure on RSA with exponent blinding. In: SECRYPT 2015 - Proceedings of 12th International Conference on Security and Cryptography, Colmar, Alsace, France, 20–22 July 2015, pp. 136–147 (2015)
Cimato, S., Mella, S., Susella, R.: Partial key exposure attacks on RSA with exponent blinding. In: International Conference on E-Business and Telecommunications, pp. 364–385. Springer (2015)
Clavier, C., Feix, B., Gagnerot, G., Roussellet, M., Verneuil, V.: Horizontal correlation analysis on exponentiation. In: Soriano, M., Qing, S., López, J. (eds.) ICICS 2010. LNCS, vol. 6476, pp. 46–61. Springer, Heidelberg (2010)
Coron, J.-S.: Resistance against differential power analysis for elliptic curve cryptosystems. In: Koç, Ç.K., Paar, C. (eds.) CHES 1999. LNCS, vol. 1717, pp. 292–302. Springer, Heidelberg (1999)
Doychev, G., Köpf, B.: Rigorous analysis of software countermeasures against cache attacks. arXiv e-prints, March 2016
Ernst, M., Jochemsz, E., May, A., de Weger, B.: Partial key exposure attacks on RSA up to full size exponents. In: Cramer, R. (ed.) EUROCRYPT 2005. LNCS, vol. 3494, pp. 371–386. Springer, Heidelberg (2005)
Fouque, P.-A., Kunz-Jacques, S., Martinet, G., Muller, F., Valette, F.: Power attack on small RSA public exponent. In: Goubin, L., Matsui, M. (eds.) CHES 2006. LNCS, vol. 4249, pp. 339–353. Springer, Heidelberg (2006)
Garner, H.L.: The residue number system. Papers presented at 3–5 March 1959, Western Joint Computer Conference, IRE-AIEE-ACM 1959 (Western), pp. 146–153. ACM, New York (1959)
Kiss, Á., Krämer, J., Rauzy, P., Seifert, J.-P.: Algorithmic countermeasures against fault attacks and power analysis for RSA-CRT. In: Standaert, F.-X., Oswald, E. (eds.) COSADE 2016. LNCS, vol. 9689, pp. 111–129. Springer, Heidelberg (2016)
Gordon, D.M.: A survey of fast exponentiation methods. J. Algorithms 27, 129–146 (1998)
Gruss, D., Maurice, C., Wagner, K.: Flush+flush: a stealthier last-level cache attack. In: 13th International Conference on Detection of Intrusions and Malware, and Vulnerability Assessment, DIMVA 2016, Proceedings (2016)
Gruss, D., Spreitzer, R., Mangard, S.: Cache template attacks: automating attacks on inclusive last-level caches. In: 24th USENIX Security Symposium (USENIX Security 15), pp. 897–912 (2015)
Gullasch, D., Bangerter, E., Krenn, S.: Cache games-bringing access-based cache attacks on AES to practice. In: 2011 IEEE Symposium on Security and Privacy (SP), pp. 490–505. IEEE (2011)
Inci, M.S., Gulmezoglu, B., Irazoqui, G., Eisenbarth, T., Sunar, B.: Seriously, get off my cloud! Cross-VM RSA key recovery in a public cloud. Technical report, IACR Cryptology ePrint Archive (2015)
Irazoqui, G., Eisenbarth, T., Sunar, B.: S$a: a shared cache attack that works across cores and defies VM sandboxing - and its application to AES. In: 2015 IEEE Symposium on Security and Privacy, pp. 591–604, May 2015
Irazoqui, G., Inci, M.S., Eisenbarth, T., Sunar, B.: Wait a minute! A fast, cross-VM attack on AES. In: Stavrou, A., Bos, H., Portokalidis, G. (eds.) RAID 2014. LNCS, vol. 8688, pp. 299–319. Springer, Heidelberg (2014)
Joye, M., Lepoint, T.: Partial key exposure on RSA with private exponents larger than N. In: Ryan, M.D., Smyth, B., Wang, G. (eds.) ISPEC 2012. LNCS, vol. 7232, pp. 369–380. Springer, Heidelberg (2012)
Kocher, P.C.: Timing attacks on implementations of Diffie-Hellman, RSA, DSS, and other systems. In: Koblitz, N. (ed.) CRYPTO 1996. LNCS, vol. 1109, pp. 104–113. Springer, Heidelberg (1996)
Liu, F., Yarom, Y., Ge, Q., Heiser, G., Lee, R.B.: Last-level cache side-channel attacks are practical. In: 2015 IEEE Symposium on Security and Privacy, pp. 605–622, May 2015
Liu, F., Ge, Q., Yarom, Y., McKeen, F., Rozas, C.V., Heiser, G., Lee, R.B.: Catalyst: defeating last-level cache side channel attacks in cloud computing. In: HPCA (2016)
Maurice, C., Le Scouarnec, N., Neumann, C., Heen, O., Francillon, A.: Reverse engineering Intel last-level cache complex addressing using performance counters. In: 18th International Symposium on Research in Attacks, Intrusions and Defenses (RAID) (2015)
Inci, M.S., Gulmezoglu, B., Eisenbarth, T., Sunar, B.: Co-location detection on the cloud. In: Standaert, F.-X., Oswald, E. (eds.) COSADE 2016. LNCS, vol. 9689, pp. 19–34. Springer, Heidelberg (2016)
Oren, Y., Kemerlis, V.P., Sethumadhavan, S., Keromytis, A.D.: The spy in the sandbox-practical cache attacks in Javascript (2015). arXiv preprint arXiv: 1502.07373
Osvik, D.A., Shamir, A., Tromer, E.: Cache attacks and countermeasures: the case of AES. In: Pointcheval, D. (ed.) CT-RSA 2006. LNCS, vol. 3860, pp. 1–20. Springer, Heidelberg (2006)
Quisquater, J.-J., Couvreur, C.: Fast decipherment algorithm for RSA Public-key cryptosystem. Electron. Lett. 18, 905–907 (1982)
Ristenpart, T., Tromer, E., Shacham, H., Savage, S.: Hey, you, get off of my cloud: exploring information leakage in third-party compute clouds. In: Proceedings of 16th ACM Conference on Computer and Communications Security, pp. 199–212. ACM (2009)
Suzaki, K., Iijima, K., Yagi, T., Artho, C.: Memory deduplication as a threat to the guest os. In: Proceedings of 4th European Workshop on System Security, EUROSEC 2011, pp. 1:1–1:6. ACM, New York (2011)
Suzaki, K., Iijima, K., Yagi, T., Artho, C.: Software side channel attack on memory deduplication. In: SOSP POSTER (2011)
Yarom, Y., Falkner, K.: Flush+reload: a high resolution, low noise, l3 cache side-channel attack. In: 23rd USENIX Security Symposium (USENIX Security 14), pp. 719–732 (2014)
Yarom, Y., Genkin, D., Heninger, N.: Cachebleed: a timing attack on OpenSSL constant time RSA. Technical report, Cryptology ePrint Archive, Report 2016/224 (2016)
Zhang, Y., Juels, A., Reiter, M.K., Ristenpart, T.: Cross-VM side channels and their use to extract private keys. In: Proceedings of 2012 ACM Conference on Computer and Communications Security, CCS 2012, pp. 305–316. ACM, New York (2012)
Zhang, Y., Juels, A., Reiter, M.K., Ristenpart, T.: Cross-tenant side-channel attacks in paas clouds. In: Proceedings of 2014 ACM SIGSAC Conference on Computer and Communications Security, pp. 990–1003. ACM (2014)
Zhou, Z., Reiter, M.K., Zhang, Y.: A Software approach to defeating side channels in last-level caches (2016). arXiv preprint arXiv: 1603.05615
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2016 Springer International Publishing AG
About this paper
Cite this paper
Cimato, S., Damiani, E., Mella, S., Yang, CN. (2016). Key Recovery in Public Clouds: A Survey on Cross-VM Side Channel Attacks. In: Sun, X., Liu, A., Chao, HC., Bertino, E. (eds) Cloud Computing and Security. ICCCS 2016. Lecture Notes in Computer Science(), vol 10039. Springer, Cham. https://doi.org/10.1007/978-3-319-48671-0_40
Download citation
DOI: https://doi.org/10.1007/978-3-319-48671-0_40
Published:
Publisher Name: Springer, Cham
Print ISBN: 978-3-319-48670-3
Online ISBN: 978-3-319-48671-0
eBook Packages: Computer ScienceComputer Science (R0)