Abstract
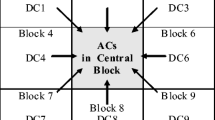
As the most commonly used entropy coding method of H.264, CAVLC (context-based adaptive variable length coding) has been widely utilized for information hiding. Various information hiding methods directly manipulate CAVLC coefficients, which are reported to be of high payload and low computational complexity. However, things are quite different in real applications. This paper addresses two misconceptions about them: (1) The CAVLC coefficients can be modified without re-encoding process. In fact, direct modifications of the number of non-zero coefficients will change the corresponding code tables for adjacent blocks and result in decoding errors. (2) CAVLC codewords can be indiscriminately substituted. Actually, it will cause serious distortion drifts. In addition, considering steganographic security, a detection strategy is proposed based on statistical analysis of some CAVLC-based methods.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Similar content being viewed by others
References
Abd, M., Zekry, A.: Implementing entropy codec for H.264 video compression standard. Int. J. Comput. Appl. 129(2), 45–53 (2015)
Cao, Y., Zhao, X., Feng, D.: Video steganalysis exploiting motion vector reversion-based features. IEEE Sig. Process. Lett. 19(1), 35–38 (2012)
Fridrich, J.: Steganography in Digital Media: Principles, Algorithms, and Applications. Cambridge University Press, Cambridge (2009)
Jafari, M., Kasaei, S.: Fast intra- and inter-prediction mode decision in H.264 advanced video coding. In: IEEE Singapore International Conference on Communication Systems, pp. 1–6 (2006)
Kim, S., Kim, S., Hong, Y., Won, C.: Data hiding on H.264/AVC compressed video. In: Image Analysis and Recognition, pp. 698–707 (2007)
Li, X., Chen, H., Wang, D., Liu, T., Hou, G.: Data hiding in encoded video sequences based on H.264. In: IEEE International Conference on Computer Science and Information Technology. vol. 6, pp. 121–125. IEEE (2010)
Liao, K., Lian, S., Guo, Z., Wang, J.: Efficient information hiding in H.264/AVC video coding. Telecommun. Syst. 49(2), 261–269 (2012)
Lin, S.D., Chuang, C.Y., Chen, M.J.: A cavlc-based video watermarking scheme for H.264/AVC codec. Int. J. Innov. Comput. Inf. Control 7(11), 6359–6367 (2011)
Lin, Y.C., Hsu, I.F.: Cavlc codewords substitution for H.264/AVC video data hiding. In: IEEE International Conference on Consumer Electronics, pp. 492–493. IEEE (2014)
Liu, Y., Ju, L., Hu, M., Ma, X., Zhao, H.: A robust reversible data hiding scheme for H.264 without distortion drift. Neurocomputing 151, 1053–1062 (2015)
Lu, C.S., Chen, J.R., Fan, K.C.: Real-time frame-dependent video watermarking in VLC domain. Sig. Process. Image Commun. 20(7), 624–642 (2005)
Ma, X., Li, Z., Tu, H., Zhang, B.: A data hiding algorithm for H.264/AVC video streams without intra-frame distortion drift. IEEE Trans. Circ. Syst. Video Technol. 20(10), 1320–1330 (2010)
Mobasseri, B.G., Marcinak, M.P.: Watermarking of MPEG-2 video in compressed domain using VLC mapping. In: ACM Workshop on Multimedia and Security, pp. 91–94. ACM (2005)
Niu, K., Zhong, W.: A video steganography scheme based on H.264 bitstreams replaced. In: IEEE International Conference on Software Engineering and Service Science, pp. 447–450. IEEE (2013)
Ozer, J.: Encoding for Multiple Screen Delivery. Udemy (2016)
Richardson, I.E.: H.264/Mpeg-4 part 10 white paper (2003)
Seo, Y.H., Lee, C.Y., Kim, D.W.: Low-complexity watermarking based on entropy coding in H.264/AVC. IEICE Trans. Fundam. Electron. Commun. Comput. Sci. 91(8), 2130–2137 (2008)
Shobitha, G.: Implementation of cavld architecture using binary tree structures and data hiding for H.264/AVC using cavlc & exp-golomb codeword substitution. Int. J. Comput. Sci. Mob. Comput. 5, 540–549 (2016)
Tew, Y., Wong, K.: An overview of information hiding in H.264/AVC compressed video. IEEE Trans. Circ. Syst. Video Technol. 24(2), 305–319 (2014)
Tian, X., Le, T.M., Lian, Y.: Entropy Coders of the H.264/AVC Standard: Algorithms and VLSI Architectures. Springer, New York (2010)
Wang, R., Hu, L., Xu, D.: A watermarking algorithm based on the CABAC entropy coding for H.264/AVC. J. Comput. Inf. Syst. 7(6), 2132–2141 (2011)
Xu, D., Wang, R.: Watermarking in H.264/AVC compressed domain using exp-golomb code words mapping. Opt. Eng. 50(9), 097402 (2011)
Yao, Y., Zhang, W., Yu, N.: Inter-frame distortion drift analysis for reversible data hiding in encrypted H.264/AVC video bitstreams. Sig. Process. 128, 531–545 (2016)
Acknowledgments
This work was supported by the NSFC under U1636102 and U1536105, and National Key Technology R&D Program under 2014BAH41B01, 2016YFB0801003 and 2016QY15Z2500.
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2017 Springer International Publishing AG
About this paper
Cite this paper
You, W., Cao, Y., Zhao, X. (2017). Information Hiding Using CAVLC: Misconceptions and a Detection Strategy. In: Kraetzer, C., Shi, YQ., Dittmann, J., Kim, H. (eds) Digital Forensics and Watermarking. IWDW 2017. Lecture Notes in Computer Science(), vol 10431. Springer, Cham. https://doi.org/10.1007/978-3-319-64185-0_15
Download citation
DOI: https://doi.org/10.1007/978-3-319-64185-0_15
Published:
Publisher Name: Springer, Cham
Print ISBN: 978-3-319-64184-3
Online ISBN: 978-3-319-64185-0
eBook Packages: Computer ScienceComputer Science (R0)