Abstract
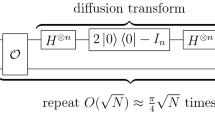
The impacts that quantum computers will have on cryptography have become more and more important to study for not only public key cryptography but also symmetric key cryptography. For example, at ISITA 2012, Kuwakado and Morii showed that an adversary with a quantum computer can recover keys of the Even-Mansour construction in polynomial time by applying Simon’s algorithm. In addition, at CRYPTO 2016, Kaplan et al. showed that Simon’s algorithm can also be used to perform forgery attacks against MACs and exponentially speed-up a slide attack. This paper introduces a tool for finding the period of a function that is periodic up to constant addition and shows that a quantum adversary can use the tool to perform a related-key attack in polynomial time. Our quantum related-key attack is an extension of the quantum slide attack by Kaplan et al. against iterated Even-Mansour ciphers that are implemented on quantum circuits. Although the relationships among keys are strong, our algorithm can recover all the keys of a two-round iterated Even-Mansour cipher in polynomial time.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Similar content being viewed by others
References
Chen, S., Steinberger, J.P.: Tight security bounds for key-alternating ciphers. IACR Cryptology ePrint Archive 2013, 222 (2013). http://eprint.iacr.org/2013/222
Even, S., Mansour, Y.: A construction of a cipher from a single pseudorandom permutation. J. Cryptology 10(3), 151–162 (1997). https://doi.org/10.1007/s001459900025
Grover, L.K.: A fast quantum mechanical algorithm for database search. In: Proceedings of the Twenty-Eighth Annual ACM Symposium on Theory of Computing. STOC 1996, NY, USA, pp. 212–219 (1996). http://doi.acm.org/10.1145/237814.237866
Kaplan, M.: Quantum attacks against iterated block ciphers. CoRR abs/1410.1434 (2014). http://arxiv.org/abs/1410.1434
Kaplan, M., Leurent, G., Leverrier, A., Naya-Plasencia, M.: Breaking symmetric cryptosystems using quantum period finding. In: Proceedings of the Advances in Cryptology - CRYPTO 2016–36th Annual International Cryptology Conference, Part II, Santa Barbara, CA, USA, August 14–18, 2016, pp. 207–237 (2016). http://dx.doi.org/10.1007/978-3-662-53008-5_8
Kaplan, M., Leurent, G., Leverrier, A., Naya-Plasencia, M.: Quantum differential and linear cryptanalysis. IACR Trans. Symmetric Cryptol. 2016(1), 71–94 (2016). http://tosc.iacr.org/index.php/ToSC/article/view/536
Kuwakado, H., Morii, M.: Quantum distinguisher between the 3-round Feistel cipher and the random permutation. In: Proceedings of the IEEE International Symposium on Information Theory, ISIT 13–18, 2010, Austin, Texas, USA, pp. 2682–2685 (2010). http://dx.doi.org/10.1109/ISIT.2010.5513654
Kuwakado, H., Morii, M.: Security on the quantum-type Even-Mansour cipher. In: Proceedings of the International Symposium on Information Theory and its Applications, ISITA 2012, Honolulu, HI, USA, October 28–31, 2012. pp. 312–316 (2012). http://ieeexplore.ieee.org/document/6400943/
Luby, M., Rackoff, C.: How to construct pseudo-random permutations from pseudo-random functions (abstract). In: Proceedings of the Advances in Cryptology - CRYPTO 1985, Santa Barbara, California, USA, August 18–22, 1985, p. 447 (1985). https://doi.org/10.1007/3-540-39799-X_34
NIST: Advanced encryption standard (AES) FIPS 197 (2001)
NIST: Submission requirements and evaluation criteria for the post-quantum cryptography standardization process (2016)
Rötteler, M., Steinwandt, R.: A note on quantum related-key attacks. Inf. Process. Lett. 115(1), 40–44 (2015). http://dx.doi.org/10.1016/j.ipl.2014.08.009
Santoli, T., Schaffner, C.: Using Simon’s algorithm to attack symmetric-key cryptographic primitives. Quantum Inf. Comput. 17(1&2), 65–78 (2017). http://www.rintonpress.com/xxqic17/qic-17-12/0065-0078.pdf
Shor, P.W.: Polynomial-time algorithms for prime factorization and discrete logarithms on a quantum computer. SIAM J. Comput. 26(5), 1484–1509 (1997). http://dx.doi.org/10.1137/S0097539795293172
Simon, D.R.: On the power of quantum computation. SIAM J. Comput. 26(5), 1474–1483 (1997). http://dx.doi.org/10.1137/S0097539796298637
Treger, J., Patarin, J.: Generic attacks on Feistel networks with internal permutations. In: Proceedings of the Progress in Cryptology - AFRICACRYPT 2009, Second International Conference on Cryptology in Africa, Gammarth, Tunisia, June 21–25, 2009, pp. 41–59 (2009). http://dx.doi.org/10.1007/978-3-642-02384-2_4
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2017 Springer International Publishing AG
About this paper
Cite this paper
Hosoyamada, A., Aoki, K. (2017). On Quantum Related-Key Attacks on Iterated Even-Mansour Ciphers. In: Obana, S., Chida, K. (eds) Advances in Information and Computer Security. IWSEC 2017. Lecture Notes in Computer Science(), vol 10418. Springer, Cham. https://doi.org/10.1007/978-3-319-64200-0_1
Download citation
DOI: https://doi.org/10.1007/978-3-319-64200-0_1
Published:
Publisher Name: Springer, Cham
Print ISBN: 978-3-319-64199-7
Online ISBN: 978-3-319-64200-0
eBook Packages: Computer ScienceComputer Science (R0)