Abstract
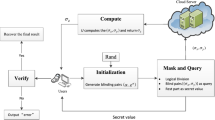
With the rapid advancements in innovative technologies like cloud computing, internet of things, and mobile computing, the paradigm to delegate the heavy computational tasks from trusted and resource-constrained devices to potentially untrusted and more powerful services has gained a lot of attention. Ensuring the verifiability of the outsourced computation along with the security and privacy requirements is an active research area. Several cryptographic protocols have been proposed by using pairing-based cryptographic techniques based on bilinear maps of suitable elliptic curves. However, the computational overhead of bilinear maps forms the most expensive part of those protocols. In this paper, we propose a new 1–checkable algorithm under the one-malicious version of a two-untrusted-program model. Our solution is approximately twice as efficient as the single comparably efficient 1–checkable solution in the literature, and requires only 4 elliptic curve point additions in the preimage and 6 field multiplications in the image of the bilinear map.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Similar content being viewed by others
References
Arabacı, O., Kiraz, M.S., Sertkaya, I., Uzunkol, O.: More efficient secure outsourcing methods for bilinear maps. Cryptology ePrint Archive, Report 2015/960 (2015). http://eprint.iacr.org/2015/960
Barbulescu, R., Duquesne, S.: Updating key size estimations for pairings. Cryptology ePrint Archive, Report 2017/334 (2017). http://eprint.iacr.org/2017/334
Barreto, P., Galbraith, S., Higeartaigh, C., Scott, M.: Efficient pairing computation on supersingular abelian varieties. Des. Codes Cryptogr. 42(3), 239–271 (2007). https://doi.org/10.1007/s10623-006-9033-6
Beuchat, J.-L., González-Díaz, J.E., Mitsunari, S., Okamoto, E., Rodríguez-Henríquez, F., Teruya, T.: High-speed software implementation of the optimal ate pairing over Barreto–Naehrig curves. In: Joye, M., Miyaji, A., Otsuka, A. (eds.) Pairing 2010. LNCS, vol. 6487, pp. 21–39. Springer, Heidelberg (2010). https://doi.org/10.1007/978-3-642-17455-1_2
Blake, I., Seroussi, G., Smart, N.: Advances in Elliptic Curve Cryptography. London Mathematical Society Lecture Note Series. Cambridge University Press, New York (2005)
Boneh, D., Franklin, M.: Identity-based encryption from the weil pairing. In: Kilian, J. (ed.) CRYPTO 2001. LNCS, vol. 2139, pp. 213–229. Springer, Heidelberg (2001). https://doi.org/10.1007/3-540-44647-8_13
Boneh, D., Lynn, B., Shacham, H.: Short signatures from the weil pairing. J. Cryptol. 17(4), 297–319 (2004). https://doi.org/10.1007/s00145-004-0314-9
Canard, S., Devigne, J., Sanders, O.: Delegating a pairing can be both secure and efficient. In: Boureanu, I., Owesarski, P., Vaudenay, S. (eds.) ACNS 2014. LNCS, vol. 8479, pp. 549–565. Springer, Cham (2014). https://doi.org/10.1007/978-3-319-07536-5_32
Chen, X.: Introduction to secure outsourcing computation. Synth. Lect. Inf. Secur. Priv. Trust 8(2), 1–93 (2016)
Chen, X., Susilo, W., Li, J., Wong, D., Ma, J., Tang, S., Tang, Q.: Efficient algorithms for secure outsourcing of bilinear pairings. Theor. Comput. Sci. 562, 112–121 (2015). http://dblp.uni-trier.de/db/journals/tcs/tcs562.html#ChenSLWMTT15
Chevallier-Mames, B., Coron, J.S., McCullagh, N., Naccache, D., Scott, M.: Secure delegation of elliptic-curve pairing. Cryptology ePrint Archive, Report 2005/150 (2005)
Galbraith, S.D., Paterson, K.G., Smart, N.P.: Pairings for cryptographers. Discrete Appl. Math. 156(16), 3113–3121 (2008)
Hess, F., Smart, N., Vercauteren, F.: The eta pairing revisited. IEEE Trans. Inf. Theory 52(10), 4595–4602 (2006)
Hohenberger, S., Lysyanskaya, A.: How to securely outsource cryptographic computations. In: Kilian, J. (ed.) TCC 2005. LNCS, vol. 3378, pp. 264–282. Springer, Heidelberg (2005). https://doi.org/10.1007/978-3-540-30576-7_15
Joux, A.: A one round protocol for tripartite Diffie-Hellman. J. Cryptol. 17(4), 263–276 (2004). https://doi.org/10.1007/s00145-004-0312-y
Kang, B.G., Lee, M.S., Park, J.H.: Efficient delegation of pairing computation (2005)
Koblitz, N., Menezes, A.: Pairing-based cryptography at high security levels. In: Smart, N.P. (ed.) Cryptography and Coding 2005. LNCS, vol. 3796, pp. 13–36. Springer, Heidelberg (2005). https://doi.org/10.1007/11586821_2
Kumar, K., Liu, J., Lu, Y.H., Bhargava, B.: A survey of computation offloading for mobile systems. Mob. Netw. Appl. 18(1), 129–140 (2013). https://doi.org/10.1007/s11036-012-0368-0
Lin, X.J., Qu, H., Zhang, X.: New efficient and flexible algorithms for secure outsourcing of bilinear pairings. Cryptology ePrint Archive, Report 2016/076 (2016). http://eprint.iacr.org/2016/076
Luo, Y., Fu, S., Huang, K., Wang, D., Xu, M.: Securely outsourcing of bilinear pairings with untrusted servers for cloud storage. In: Trustcom/BigDataSE/ISPA (2016)
Mell, P., Grance, T.: The NIST definition of cloud computing. NIST Special Publication, pp. 800–145 (2011)
Nguyen, P.Q., Shparlinski, I.E., Stern, J.: Distribution of modular sums and the security of the server aided exponentiation (2000)
Ren, Y., Ding, N., Wang, T., Lu, H., Gu, D.: New algorithms for verifiable outsourcing of bilinear pairings. Sci. China Inf. Sci. 59(9), 99103 (2016)
Shacham, H.: New paradigms in signature schemes. Ph.D. thesis, Stanford, CA, USA (2006)
Tian, H., Zhang, F., Ren, K.: Secure bilinear pairing outsourcing made more efficient and flexible. In: Proceedings of the 10th ACM Symposium on Information, Computer and Communications Security, ASIA CCS 2015, pp. 417–426. ACM, New York (2015). https://doi.org/10.1145/2714576.2714615
Wang, Y., Wu, Q., Wong, D.S., Qin, B., Chow, S.S.M., Liu, Z., Tan, X.: Securely outsourcing exponentiations with single untrusted program for cloud storage. In: Kutyłowski, M., Vaidya, J. (eds.) ESORICS 2014. LNCS, vol. 8712, pp. 326–343. Springer, Cham (2014). https://doi.org/10.1007/978-3-319-11203-9_19
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2018 IFIP International Federation for Information Processing
About this paper
Cite this paper
Kalkar, Ö., Kiraz, M.S., Sertkaya, İ., Uzunkol, O. (2018). A More Efficient 1–Checkable Secure Outsourcing Algorithm for Bilinear Maps. In: Hancke, G., Damiani, E. (eds) Information Security Theory and Practice. WISTP 2017. Lecture Notes in Computer Science(), vol 10741. Springer, Cham. https://doi.org/10.1007/978-3-319-93524-9_10
Download citation
DOI: https://doi.org/10.1007/978-3-319-93524-9_10
Published:
Publisher Name: Springer, Cham
Print ISBN: 978-3-319-93523-2
Online ISBN: 978-3-319-93524-9
eBook Packages: Computer ScienceComputer Science (R0)