Abstract
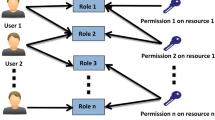
Access control between multi-user and multi-object is the key technique in security management of distributed workflow systems, and the mechanism of the role-based authorization and access control is an effective way to solve the problem. Both RBAC96 and NRBAC are better models of role-based access control. After introducing authorization constraints, a new model of role-based access control, ARBAC, is presented to mend the above models’ shortcomings. After this, an example is given to explain the execution of the role assignment algorithm. Finally, ARBAC model is applied to workflow system architecture and the new architecture is also explained in this paper. In practice, the model ARBAC with the authorization mechanism is flexible, and it also simplifies the task complexity of security administrator.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Preview
Unable to display preview. Download preview PDF.
Similar content being viewed by others
References
Sandhu, R., Coyne, E., Feinstein, H., et al.: Role-Based Access Control Model. IEEE Computer 29(2), 38–47 (1996)
Qiao, Y., Xu, D., Dai, G.: A New Role-based Access Control Model and It’s Implement Mechanism. Journal of Computer Research& Development 37(1), 37–44 (2000)
Bertino, E., Ferrari, E., Atluri, V.: The Specification and Enforcement Of Authorization Constraints in Workflow Management Systems. ACM Transactions on Information and System Security 2(1), 65–104 (1999)
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2004 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Wang, B., Zhang, S., Xia, X. (2004). The Application Research of Role-Based Access Control Model in Workflow Management System. In: Li, M., Sun, XH., Deng, Q., Ni, J. (eds) Grid and Cooperative Computing. GCC 2003. Lecture Notes in Computer Science, vol 3033. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-540-24680-0_162
Download citation
DOI: https://doi.org/10.1007/978-3-540-24680-0_162
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-540-21993-4
Online ISBN: 978-3-540-24680-0
eBook Packages: Springer Book Archive