Abstract
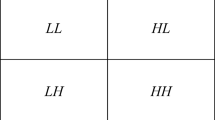
In this paper, we propose a block SVD-based fragile watermarking technique for image authentication. Using this technique, we can detect any modification made to the image and indicate the specific locations where the modification was made. We utilize the singular value of image block as the authentication data. The image is divided into same size blocks, and authentication data is inserted into the LSB plane of each block. Authentication data is produced from XOR operation between watermark image and binary bits obtained from singular value of one block image. Singular value is converted to binary bits using modular arithmetic. Security of this technique resides on two keys, so in the case where the keys are incorrect, the extraction process will return an image that resembles noise, the same case as if the image is not watermarked, or the watermarked image is modified. If the unmodified watermarked image is used, the extraction process will return the correct watermark image.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Preview
Unable to display preview. Download preview PDF.
Similar content being viewed by others
References
Yeung, M., Mintzer, F.: An Invisible Watermarking Technique for Image Verification. In: Proc. ICIP, Santa Barbara, CA, vol. 2, pp. 680–683 (1997)
Memon, N., Shende, S., Wong, P.: On the Security of the Yeung-Mintzer Authentication Watermark. In: Proc. of the IS and TPICS Symposium, Savannah, Georgia (2000)
Wong, P., Memon, N.: Secret and Public Key Image Watermarking Schemes for Image Authentication and Ownership Verification. IEEE Trans. on Image Processing 10, 1593–1601 (2001)
Byun, S., Lee, S., Tewfik, A., Ahn, B.: A SVD-Based Fragile Watermarking Scheme for Image Authentication. In: Petitcolas, F.A.P., Kim, H.-J. (eds.) IWDW 2002. LNCS, vol. 2613, pp. 170–178. Springer, Heidelberg (2003)
Liu, R., Tan, T.: An SVD-based Watermarking Scheme for Protecting Rightful Ownership. IEEE Trans. on Multimedia 4, 121–128 (2002)
Andrews, H., Patterson, C.: Singular Value Decomposition (SVD) Image Coding. IEEE Trans. Commun. COM-24, 425–432 (1976)
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2004 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Oktavia, V., Lee, WH. (2004). A Fragile Watermarking Technique for Image Authentication Using Singular Value Decomposition. In: Aizawa, K., Nakamura, Y., Satoh, S. (eds) Advances in Multimedia Information Processing - PCM 2004. PCM 2004. Lecture Notes in Computer Science, vol 3332. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-540-30542-2_6
Download citation
DOI: https://doi.org/10.1007/978-3-540-30542-2_6
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-540-23977-2
Online ISBN: 978-3-540-30542-2
eBook Packages: Computer ScienceComputer Science (R0)