Abstract
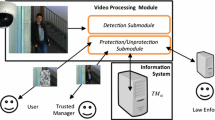
Even more than in our physical world, in our digital world we need systems that meet the security objective of service providers and users in equal measure. This paper investigates the requirements of secure authorizations with respect to accountability and privacy in the context of surveillance for misuse detection during service utilization. We develop a model of system architectures for secure and privacy-respecting authorizations that allows to derive and compare the properties of available technology. It is shown how the model maps to existing authorization architectures.
Preview
Unable to display preview. Download preview PDF.
Similar content being viewed by others
References
Biskup, J., Karabulut, Y.: A hybrid PKI model with an application for secure meditation. In: Shenoi, S. (ed.) Proceedings of the 16th Annual IFIP WG 11.3 Working Conference on Data and Application Security, Cambridge, England, July 2002, pp. 271–282. Kluwer, Dordrecht (2002)
Flegel, U.: Pseudonymizing Unix log files. In: Davida, G.I., Frankel, Y., Rees, O. (eds.) InfraSec 2002. LNCS, vol. 2437, pp. 162–179. Springer, Heidelberg (2002)
Camenisch, J., Lysyanskaya, A.: An efficient system for non-transferable anonymous credentials with optional anonymity revocation. In: Pfitzmann, B. (ed.) EUROCRYPT 2001. LNCS, vol. 2045, pp. 93–118. Springer, Heidelberg (2001)
Gollmann, D.: 10.2.1: Kerberos. In: Computer Security, pp. 168–171. John Wiley & Sons, Inc, West Sussex (1999)
Flegel, U.: Pseudonymizing Audit Data for Privacy Respecting Misuse Detection. PhD thesis, University of Dortmund, Dept. of Computer Science (January 2006)
Pfitzmann, A.: Multilateral security: Enabling technologies and their evaluation. In: Wilhelm, R. (ed.) Informatics. LNCS, vol. 2000, pp. 50–62. Springer, Heidelberg (2001)
Pfitzmann, A., Hansen, M.: Anonymity, unlinkability, unobservability, pseudonymity, and identity management - a consolidated proposal for terminology (May 2006), dud.inf.tu-dresden.de/literatur/Anon_Terminology_v0.28.pdf
van Rossum, H., Gardeniers, H., Borking, J., et al.: Privacy-enhancing technologies: The path to anonymity, vol. ii, Technical report, Registratiekamer Netherlands and Information and Privacy Commissioner Ontario, Canada, Achtergrondstudies en Verkenningen 5B, Rijswijk, Netherlands (August 1995)
Bundestag, D.D.: Gesetz über Rahmenbedingungen für elektronische Signaturen (SIGG) (in German). Bundesgesetzblatt, Teil I(1) (January 2005), 2, http://bundesrecht.juris.de/bundesrecht/sigg_2001/
Gabber, E., Gibbons, P.B., Kristol, D.M., Matias, Y., Mayer, A.: On secure and pseudonymous client-relationships with multiple servers. ACM Transactions on Information and System Security 2(3), 390–415 (1999)
Cranor, L.F.: Agents of choice: Tools that facilitate notice and choice about web site data practices. In: Proceedings of the 21st International Conference on Privacy and Personal Data Protection, Hong Kong SAR, China, September 1999, pp. 19–25 (1999)
Clauß, S., Köhntopp, M.: Identity management and its support of multilateral security. Computer Networks 37(2), 205–219 (2001)
Köhntopp, M., Berthold, O.: Identity management based on P3P. In: Federrath, H. (ed.) Designing Privacy Enhancing Technologies. LNCS, vol. 2009, pp. 141–160. Springer, Heidelberg (2001)
Köpsell, S., Wendolsky, R., Federrath, H.: Revocable anonymity. In: Müller, G. (ed.) ETRICS 2006. LNCS, vol. 3995, pp. 206–220. Springer, Heidelberg (2006)
Federrath, H.: Privacy enhanced technologies: Methods – markets – misuse. In: Katsikas, S.K., Lopez, J., Pernul, G. (eds.) TrustBus 2005. LNCS, vol. 3592, pp. 1–9. Springer, Heidelberg (2005)
Fischer-Hübner, S.: IT-Security and Privacy: Design and Use of Privacy-Enhancing Security Mechanisms. LNCS, vol. 1958. Springer, Heidelberg (2001)
Seys, S., Díaz, C., De Win, B., Naessens, V., Goemans, C., Claessens, J., Moreau, W., De Decker, B., Dumortier, J., Preneel, B.: Anonymity and privacy in electronic services (APES) Deliverable 2 – Requirement study of different applications. Technical report, K. U. Leuven (May 2001)
Goldberg, I.: Privacy-enhancing technologies for the internet, II: Five years later. In: Dingledine, R., Syverson, P.F. (eds.) PET 2002. LNCS, vol. 2482, pp. 1–12. Springer, Heidelberg (2003)
Goldberg, I., Wagner, D., Brewer, E.: Privacy enhancing technologies for the internet. In: Proceedings of the COMPCON’97, San Jose, California, USA, February 1997, IEEE (1997), http://www.cs.berkeley.edu/~daw/privacy-compcon97-www/privacy-html.html
Chaum, D.: Showing credentials without identification: Transferring signatures between unconditionally unlinkable pseudonyms. In: Seberry, J., Pieprzyk, J.P. (eds.) AUSCRYPT 1990. LNCS, vol. 453, pp. 246–264. Springer, Heidelberg (1990)
Van Herreweghen, E.: Secure anonymous signature-based transactions. In: Goos, G., Hartmanis, J., van Leeuwen, J. (eds.) ESORICS 2000. LNCS, vol. 1895, pp. 55–71. Springer, Heidelberg (2000)
Brands, S.A.: Rethinking Public Key Infrastructures and Digital Certificates: Building in Privacy. MIT Press, Cambridge, Massachusetts, USA (2000)
Glenn, A., Goldberg, I., Légaré, F., Stiglic, A.: A description of protocols for private credentials (October 2001), http://eprint.iacr.org/2001
Stubblebine, S.G., Syverson, P.F.: Authentic attributes with fine-grained anonymity protection. In: Frankel, Y. (ed.) FC 2000. LNCS, vol. 1962, pp. 276–294. Springer, Heidelberg (2001)
Lysyanskaya, A., Rivest, R.L., Sahai, A., Wolf, S.: Pseudonym systems. In: Heys, H.M., Adams, C.M. (eds.) SAC 1999. LNCS, vol. 1758, pp. 184–199. Springer, Heidelberg (2000)
Schechter, S., Parnell, T., Hartemink, A.: Anonymous authentication of membership in dynamic groups. In: Franklin, M.K. (ed.) FC 1999. LNCS, vol. 1648, pp. 184–195. Springer, Heidelberg (1999)
Gritzalis, D., Moulinos, K., Iliadis, J., Lambrinoudakis, C., Xarhoulakos, S.: Pythia: Towards anonymity in authentication. In: Dupuy, M., Paradinas, P. (eds.) Proceedings of the IFIP TC11 16th International Conference on Information Security (Sec 2001), Paris, France, IFIP, June 2001, pp. 1–17. Kluwer Academic Publishers, Dordrecht (2001)
Hirose, S., Yoshida, S.: A user authentication scheme with identity and location privacy. In: Varadharajan, V., Mu, Y. (eds.) ACISP 2001. LNCS, vol. 2119, pp. 235–246. Springer, Heidelberg (2001)
Handley, B.: Resource-efficient anonymous group identification. In: Frankel, Y. (ed.) FC 2000. LNCS, vol. 1962, pp. 295–312. Springer, Heidelberg (2001)
Davida, G., Frankel, Y., Tsiounis, Y., Yung, M.: Anonymity control in e-cash systems. In: Hirschfeld, R. (ed.) FC 1997. LNCS, vol. 1318, pp. 1–16. Springer, Heidelberg (1997)
Camenisch, J., Maurer, U., Stadler, M.: Digital payment systems with passive anonymity-revoking trustees. In: Martella, G., Kurth, H., Montolivo, E., Bertino, E. (eds.) Computer Security - ESORICS 1996. LNCS, vol. 1146, pp. 33–43. Springer, Heidelberg (1996)
Claessens, J., Preneel, B., Vandewalle, J.: Anonymity controlled electronic payment systems. In: Proceedings of the 20th Symposium on Information Theory in the Benelux, Haasrode, Belgium, May 1999, pp. 109–116 (1999)
Pointcheval, D.: Self-scrambling anonymizers. In: Frankel, Y. (ed.) FC 2000. LNCS, vol. 1962, pp. 259–275. Springer, Heidelberg (2001)
Nakanishi, T., Haruna, N., Sugiyama, Y.: Unlinkable electronic coupon protocol with anonymity control. In: Zheng, Y., Mambo, M. (eds.) ISW 1999. LNCS, vol. 1729, pp. 37–46. Springer, Heidelberg (1999)
Büschkes, R., Kesdogan, D.: Privacy enhanced intrusion detection. In: Müller, G., Rannenberg, K. (eds.) Multilateral Security in Communications. Information Security, pp. 187–204. Addison Wesley, Reading (1999)
Chaum, D., Fiat, A., Naor, M.: Untraceable electronic cash. In: Goldwasser, S. (ed.) CRYPTO 1988. LNCS, vol. 403, pp. 319–327. Springer, Heidelberg (1990)
Chan, Y.Y.: On privacy issues of internet access services via proxy servers. In: Baumgart, R. (ed.) Secure Networking - CQRE (Secure) 1999. LNCS, vol. 1740, pp. 183–191. Springer, Heidelberg (1999)
Groß, S., Lein, S., Steinbrecher, S.: A multilateral secure payment system for wireless LAN hotspots. In: Katsikas, S.K., Lopez, J., Pernul, G. (eds.) TrustBus 2005. LNCS, vol. 3592, pp. 80–89. Springer, Heidelberg (2005)
Stubblebine, S.G., Syverson, P.F., Goldschlag, D.M.: Unlinkable serial transactions: Protocols and applications. ACM Transactions on Information and System Security 2(4), 354–389 (1999)
Fischer-Hübner, S., Brunnstein, K.: Opportunities and risks of intrusion detection expert systems. In: Proceedings of the International IFIP-GI-Conference Opportunities and Risks of Artificial Intelligence Systems (ORAIS 1989), July 1989, Hamburg, Germany, IFIP (1989)
IDA (Intrusion Detection and Avoidance System): Ein einbruchsentdeckendes und einbruchsvermeidendes System (in German). Reihe Informatik. Shaker (1993)
Sobirey, M., Richter, B., König, H.: The intrusion detection system AID – Architecture and experiences in automated audit trail analysis. In: Horster, P. (ed.) Proceedings of the IFIP TC6/TC11 International Conference on Communications and Multimedia Security, Essen, Germany, IFIP, September 1996, pp. 278–290. Chapman & Hall, London (1996)
Lundin, E., Jonsson, E.: Anomaly-based intrusion detection: privacy concerns and other problems. Computer Networks 34(4), 623–640 (2000)
Eckert, C., Pircher, A.: Internet anonymity: Problems and solutions. In: Dupuy, M., Paradinas, P. (eds.) Proceedings of the IFIP TC11 16th International Conference on Information Security (Sec 2001), Paris, France, IFIP, June 2001, pp. 35–50. Kluwer Academic Publishers, Dordrecht (2001)
Pang, R., Paxson, V.: A high-level programming environment for packet trace anonymization and transformation. In: Proceedings of the 2003 Conference on Applications, Technologies, Architectures, and Protocols for Computer Communications, Karlsruhe, Germany, ACM SIGCOMM, August 2003, pp. 339–351. ACM Press, New York (2003)
Alamäki, T., Björksen, M., Dornbach, P., Gripenberg, C., Gyórbíró, N., Márton, G., Németh, Z., Skyttä, T., Tarkiainen, M.: Privacy enhancing service architectures. In: Dingledine, R., Syverson, P.F. (eds.) PET 2002. LNCS, vol. 2482, pp. 99–109. Springer, Heidelberg (2003)
Author information
Authors and Affiliations
Editor information
Rights and permissions
Copyright information
© 2007 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Flegel, U., Meier, M. (2007). Authorization Architectures for Privacy-Respecting Surveillance . In: Lopez, J., Samarati, P., Ferrer, J.L. (eds) Public Key Infrastructure. EuroPKI 2007. Lecture Notes in Computer Science, vol 4582. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-540-73408-6_1
Download citation
DOI: https://doi.org/10.1007/978-3-540-73408-6_1
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-540-73407-9
Online ISBN: 978-3-540-73408-6
eBook Packages: Computer ScienceComputer Science (R0)