Abstract
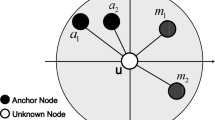
Recently, Zhang et al. proposed a location-based threshold-endorsement scheme (LTE) to thwart bogus data injection attacks. This scheme exhibits much greater filtering power than earlier symmetric schemes and results in enhanced energy savings. In this paper, we show that LTE has a significant vulnerability. We also propose an improved scheme that mitigates this weakness and thereby achieves the original claims of Zhang et al. without lessening LTE’s remarkable filtering power.
“This research was supported by the MIC(Ministry of Information and Communication), Korea, under the ITRC(Information Technology Research Center) support program supervised by the IITA(Institute of Information Technology Advancement)” (IITA-2006-(C1090-0603-0025)).
Preview
Unable to display preview. Download preview PDF.
Similar content being viewed by others
References
Boneh, D., Lynn, B., Shacham, H.: Short signatures from the Weil pairing. In: Boyd, C. (ed.) ASIACRYPT 2001. LNCS, vol. 2248, pp. 514–532. Springer, Heidelberg (2001)
Baek, J., Zheng, Y.: Identity-based threshold signature from the bilinear pairings. In: Proc. Int. Conf. Inf. Tech.: Coding Comput., pp. 124–128 (April 2004)
Ye, F., Luo, H., Lu, S., Zhang, L.: Statistical en-route filtering of injected false data in sensor networks. IEEE JSAC, Special Issue on Self-Orgazing Distributed Collaborative Sensor Networks 23(4), 839–850 (2005)
Zhang, Y., Liu, W., Lou, W., Fang, Y.: Location-based compromise-tolerant security mechanisms for wireless sensor networks. IEEE JSAC, Special Issue on Security in Wireless Ad Hoc Networks 24(2), 247–260 (2006)
Zhu, S., Setia, S., Jajodia, S., Ning, P.: An interleaved hop-by-hop authentication scheme for filtering of injected false data in sensor networks. In: Proc. IEEE Symp. Security Privacy, pp. 259–271 (May 2004)
Author information
Authors and Affiliations
Editor information
Rights and permissions
Copyright information
© 2007 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Kim, Y.H., Park, J.H., Lee, D.H., Lim, J. (2007). Bogus Data Filtering in Sensor Networks. In: Washio, T., et al. Emerging Technologies in Knowledge Discovery and Data Mining. PAKDD 2007. Lecture Notes in Computer Science(), vol 4819. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-540-77018-3_62
Download citation
DOI: https://doi.org/10.1007/978-3-540-77018-3_62
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-540-77016-9
Online ISBN: 978-3-540-77018-3
eBook Packages: Computer ScienceComputer Science (R0)