Abstract
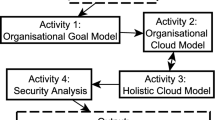
In this paper we present the main steps of a process for the systematic development of security critical inter-organizational applications. We employ models of the functional aspects of the system at different layers of abstraction for analyzing security requirements, risks and controls and for generating executable security services.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Preview
Unable to display preview. Download preview PDF.
Similar content being viewed by others
References
SHVT Manual, Fraunhofer Institute for Secure Telecooperation (2004)
Business Process Modeling Notation (BPMN) Information (2006), Available online: http://www.bpmn.org
IHE.net: IT Infrastructure Technical Framework (2006), Available online: http://www.ihe.net
Alberts, C.J., Dorofee, A.J.: Managing information security risks: the OCTAVE approach. Pearson Education, London (2002)
Basin, D., Doser, J., Lodderstedt, T.: Model driven security for process-oriented systems. In: Proc. 8th ACM Symposium on Access Control Models and Technologies, ACM Press, New York (2003)
Breu, R., Popp, G., Alam, M.: Model-based development of access policies. Journal for Software Tools and Technology Transfer (STTT) 9, 457–470 (2007)
Datta, A., Derek, A., Mitchell, J.C., Pavlovic, D.: A derivation system and compositional logic for security protocols. Journal of Computer Security 13, 423–482 (2005)
Giorgini, P., et al.: ST-Tool: A CASE Tool for Modeling and Analyzing Trust Requirements. In: Herrmann, P., Issarny, V., Shiu, S.C.K. (eds.) iTrust 2005. LNCS, vol. 3477, Springer, Heidelberg (2005)
Federal Office for Information Security (BSI). IT Baseline Protection Manual (2003), Available online: http://www.bsi.bund.de/english/gshb/manual/index.htm
Gutierrez, C., Fernandez-Medina, E., Piattini, M.: Security risk analysis in web services systems. In: Proc. SECRYPT 2006, pp. 425–430 (2006)
Hafner, M., Agreiter, B., Breu, R., Nowak, A.: SECTET — An Extensible Framework for the Realization of Secure Inter-Organizational Workflows. Journal of Internet Research (2006)
Hailey, C., Laney, R., Moffett, J., Nuseibeh, B.: Security requirements engineering, a framework for representation and analysis. IEEE Transactions on Software Engineering (to appear, 2007)
Jürjens, J.: Secure Systems Development with UML. Springer, Heidelberg (2004)
Lodderstedt, T., Basin, D., Doser, J.: SecureUML: A UML-Based Modeling Language for Model-Driven Security. In: Jézéquel, J.-M., Hussmann, H., Cook, S. (eds.) UML 2002. LNCS, vol. 2460, pp. 426–441. Springer, Heidelberg (2002)
Peltier, T.R.: Risk analysis and risk management. Information Systems Security 13(4), 44–56 (2004)
Innerhofer-Oberperfler, F., Breu, R., Yautsiukhin, A.: Quantitative assessment of enterprise security systems (submitted)
Raptis, D., Dimitrakos, T., Gran, B.A., Stølen, K.: The CORAS Approach for Model-based Risk Management applied to e-Commerce Domain. In: Proc. CMS-2002, pp. 169–181 (2002)
Rodriguez, A., Fernandez-Medina, E., Piattini, M.: Capturing Security Requirements in Business Processes Through a UML 2.0 Activity Diagrams Profile. In: Roddick, J.F., Benjamins, V.R., Si-said Cherfi, S., Chiang, R., Claramunt, C., Elmasri, R.A., Grandi, F., Han, H., Hepp, M., Lytras, M., Mišić, V.B., Poels, G., Song, I.-Y., Trujillo, J., Vangenot, C. (eds.) ER Workshops 2006. LNCS, vol. 4231, pp. 32–42. Springer, Heidelberg (2006)
Schabetsberger, T., Ammenwerth,, Breu, R., Hoerbst, A., Goebel, G., Penz, R., Schindelwig, K., Toth, H., Vogl, R., Wozak, F.: E-Health Approach to Link-up Actors in the Health Care System of Austria. Stud. Health Technol. Inform. 124
Service Central de la Securite des Systemes d’Information. Expression of needs and identification of safety objectives (EBIOS) (online, 1997)
Wozak, F., Ammenwerth, E., Breu, M., Penz, R., Schabetsberger, T., Vogl, R., Wurz, M.: Medical Data GRIDs as approach towards secure cross enterprise document sharing (based on IHE XDS). In: Proc. MIE 2006, pp. 377–383 (2006)
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2008 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Breu, R., Hafner, M., Innerhofer-Oberperfler, F., Wozak, F. (2008). Model-Driven Security Engineering of Service Oriented Systems. In: Kaschek, R., Kop, C., Steinberger, C., Fliedl, G. (eds) Information Systems and e-Business Technologies. UNISCON 2008. Lecture Notes in Business Information Processing, vol 5. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-540-78942-0_8
Download citation
DOI: https://doi.org/10.1007/978-3-540-78942-0_8
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-540-78941-3
Online ISBN: 978-3-540-78942-0
eBook Packages: Computer ScienceComputer Science (R0)