Abstract
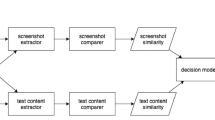
Many visual similarity-based phishing page detectors have been developed to detect phishing webpages, however, scammers now create polymorphic phishing pages to breach the defense of those detectors. We call this kind of countermeasure phishing page polymorphism. Polymorphic pages are visually similar to genuine pages they try to mimic, but they use different representation techniques. It increases the level of difficulty to detect phishing pages. In this paper, we propose an effective detection mechanism to detect polymorphic phishing pages. In contrast to existing approaches, we analyze the layout of webpages rather than the HTML codes, colors, or content. Specifically, we compute the similarity degree of a suspect page and an authentic page through image processing techniques. Then, the degrees of similarity are ranked by a classifier trained to detect phishing pages. To verify the efficacy of our phishing detection mechanism, we collected 6,750 phishing pages and 312 mimicked targets for the performance evaluation. The results show that our method achieves an excellent detection rate of 99.6%.
Preview
Unable to display preview. Download preview PDF.
Similar content being viewed by others
References
Chen, K.-T., Chen, J.-Y., Huang, C.-R., Chen, C.-S.: Fighting Phishing with Discriminative Keypoint Features of Webpages. IEEE Internet Computing (2009)
Dhamija, R., Tygar, J.D., Hearst, M.: Why phishing works. In: Proceedings of the SIGCHI Conference on Human Factors in Computing Systems, pp. 581–590 (2006)
Szor, P.: The Art of Computer Virus Research and Defense. Addison-Wesley Professional, Reading (2005)
Halderman, J.A., Waters, B., Felten, E.W.: A convenient method for securely managing passwords. In: Proceedings of the 14th International Conference on World Wide Web, pp. 471–479 (2005)
Tan, C.H., Teo, J.C.M.: Protection AgainstWeb-based Password Phishing. In: Proceedings of the International Conference on Information Technology, pp. 754–759. IEEE Computer Society, Washington (2007)
Zhang, Y., Hong, J.I., Cranor, L.F.: Cantina: a content-based approach to detecting phishing web sites. In: Proceedings of the 16th International Conference on World Wide Web, pp. 639–648 (2007)
Liu, W., Deng, X., Huang, G., Fu, A.Y.: An Antiphishing Strategy Based on Visual Similarity Assessment. IEEE Internet Computing, 58–65 (2006)
Fu, A.Y., Wenyin, L., Deng, X.: Detecting Phishing Web Pages with Vi- sual Similarity Assessment Based on Earth Mover’s Distance (EMD). IEEE Transactions on Dependable and Secure Computing, 301–311 (2006)
Otsu, N., et al.: A threshold selection method from gray-level histograms. IEEE Transactions on Systems, Man, and Cybernetics 9(1), 62–66 (1979)
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2009 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Lam, IF., Xiao, WC., Wang, SC., Chen, KT. (2009). Counteracting Phishing Page Polymorphism: An Image Layout Analysis Approach. In: Park, J.H., Chen, HH., Atiquzzaman, M., Lee, C., Kim, Th., Yeo, SS. (eds) Advances in Information Security and Assurance. ISA 2009. Lecture Notes in Computer Science, vol 5576. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-642-02617-1_28
Download citation
DOI: https://doi.org/10.1007/978-3-642-02617-1_28
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-642-02616-4
Online ISBN: 978-3-642-02617-1
eBook Packages: Computer ScienceComputer Science (R0)